Mayhem is an AI-driven security testing platform that uses coverage-guided fuzzing and symbolic execution to find vulnerabilities in APIs, compiled binaries, and containerized applications. Built by Carnegie Mellon University researchers who won the 2016 DARPA Cyber Grand Challenge, Mayhem takes a fundamentally different approach to dynamic application security testing (DAST) than traditional scanners.
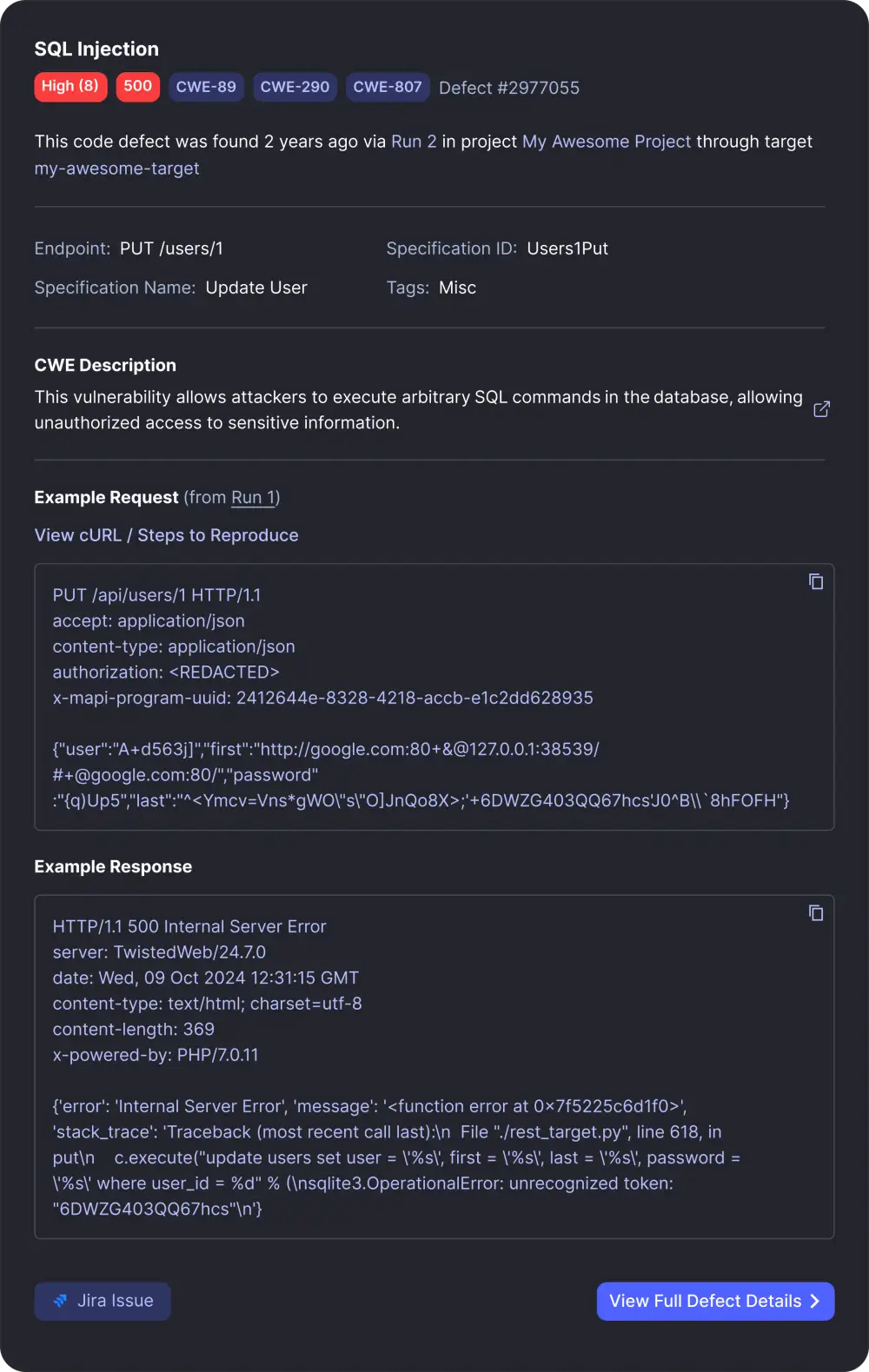
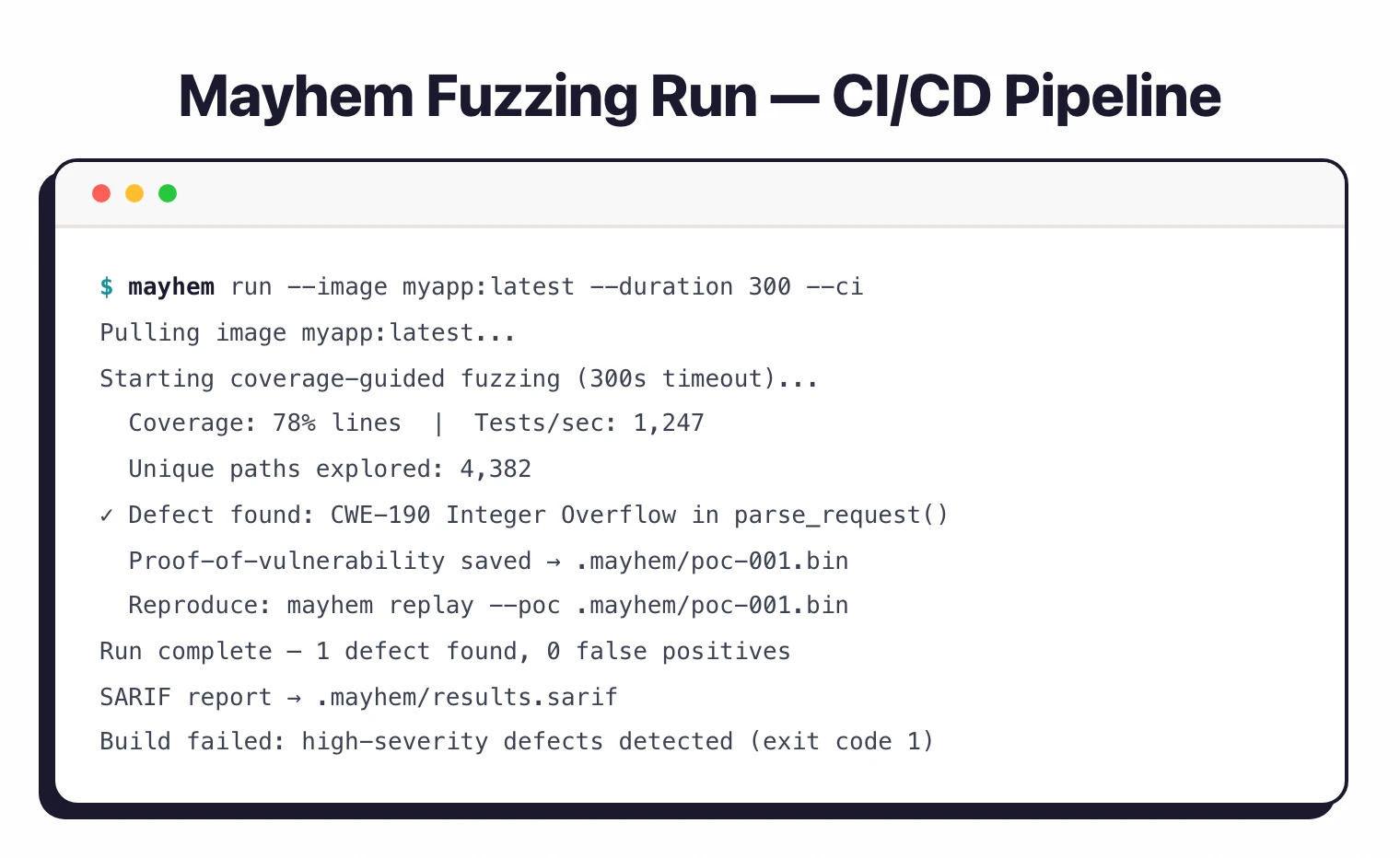
It generates thousands of targeted inputs per minute using code coverage feedback, and every reported finding includes a proof-of-vulnerability with zero false positives.
Overview
The story behind Mayhem starts at Carnegie Mellon’s CyLab. In 2012, professor David Brumley and graduate students Thanassis Avgerinos and Alex Rebert founded ForAllSecure to turn their research on automated vulnerability discovery into a product.
In 2016, their system won the DARPA Cyber Grand Challenge, a competition where autonomous machines had to find, diagnose, and patch software vulnerabilities in real time with no human intervention. Mayhem became the first non-human competitor to earn a DEF CON Black Badge and was exhibited at the Smithsonian National Museum of American History.
The technology moved from defense research to commercial product in 2019 when ForAllSecure launched Mayhem as a SaaS platform. In October 2024, the company rebranded from ForAllSecure to Mayhem Security to align with its product identity.
In November 2025, Bugcrowd acquired Mayhem Security. All 11 employees joined Bugcrowd, and David Brumley became Bugcrowd’s Chief AI and Science Officer.
The Mayhem platform is being integrated into Bugcrowd’s crowdsourced security testing platform to combine autonomous AI testing with human hacker expertise.
Product Screenshots
Key Features
| Feature | Details |
|---|---|
| Fuzzing Engine | Coverage-guided fuzzing with symbolic execution |
| False Positives | Zero: every finding includes a proof-of-vulnerability |
| API Testing | REST (OpenAPI), gRPC, Postman collections |
| Code Testing | Linux, Windows, ARM, MIPS, PPC binaries |
| SBOM Analysis | Dynamic reachability analysis, CycloneDX and SPDX support |
| Performance | P50/P90/P99 latency metrics for API endpoints |
| CI/CD | GitHub, GitLab, Jenkins, Azure DevOps, CircleCI, Travis CI |
| Reporting | SARIF format, CWE labeling, predictive CVSS scoring |
| Container Support | Docker and Kubernetes cluster analysis |
Use Cases
Mayhem serves teams that need deeper vulnerability discovery than signature-based DAST scanners provide, especially in environments where false positives are expensive to triage.
- API security testing for teams building REST or gRPC services. Mayhem parses OpenAPI specs and Postman collections, generates intelligent test cases, and verifies both positive behavior (API does what it should) and negative behavior (API rejects what it should not accept). Supports OWASP API Top 10 coverage.
- Embedded systems and IoT firmware testing. Mayhem’s support for ARM, MIPS, and PowerPC binaries makes it one of the few DAST tools that can fuzz native firmware without recompilation. Unlike traditional web-focused DAST scanners like Burp Suite, Mayhem can test compiled binaries directly.
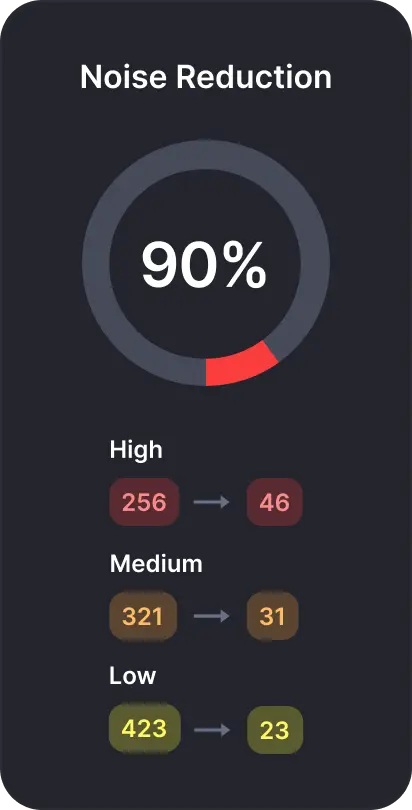
- SBOM noise reduction for organizations drowning in SCA alerts. Dynamic SBOM shows only vulnerabilities reachable during runtime, reducing noise by up to 80% compared to traditional SCA tools like Snyk or Grype.
- CI/CD pipeline integration for teams that want continuous fuzz testing on every code change. Mayhem links findings to specific commits and runs regression tests against previously discovered issues.
Bugcrowd acquired Mayhem Security in November 2025. The Mayhem platform continues to operate and is being integrated into Bugcrowd’s crowdsourced security testing platform.
If you are evaluating Mayhem, check with Bugcrowd for the latest licensing and availability information, as the product roadmap may evolve as integration progresses.
Strengths & Limitations
Strengths:
- Proven technology with DARPA Cyber Grand Challenge pedigree and real-world CVE discoveries at companies like Cloudflare and Roblox
- Zero false positives through proof-of-vulnerability for every finding — unlike traditional DAST scanners where 20-40% of findings may be false alarms
- Coverage-guided fuzzing finds 2x more bugs than fuzzing alone, detecting vulnerability classes that signature-based DAST scanners structurally cannot detect
- Dynamic SBOM reachability analysis cuts SCA noise by up to 80%, showing only runtime-reachable vulnerabilities
- Native binary testing supports Linux, Windows, ARM, MIPS, and PPC without recompilation or source code access
- Strong CI/CD integration with SARIF output for interoperability with GitHub Code Scanning, VS Code, and other tools
- Built-in ZAP integration for API testing provides supplementary DAST coverage alongside fuzzing
Limitations:
- Acquisition by Bugcrowd creates uncertainty about future standalone availability and pricing
- Fuzzing requires more setup than traditional DAST scanners: you need to provide build artifacts or container images, not just a URL
- Not a traditional web application crawler; it does not spider HTML pages looking for forms and links like Burp Suite or Acunetix
- Small team (11 employees at acquisition) means the platform’s future now depends on Bugcrowd’s integration priorities
- API fuzzing requires an OpenAPI spec or Postman collection; cannot test undocumented API endpoints without a specification
- No built-in WAF, DDoS protection, or runtime shielding. Mayhem is purely an offensive testing tool
Getting Started
Mayhem pricing
Mayhem does not publish list prices. Pricing depends on the testing modes you need (Code Security, API Security, Dynamic SBOM), the number of fuzz targets, and CI/CD integration scope.
To get a quote, contact Bugcrowd through mayhem.security or bugcrowd.com — Mayhem joined Bugcrowd in November 2025 and licensing now sits under the Bugcrowd platform contract.
Per AppSec Santa policy, I do not publish dollar amounts unless the vendor displays them publicly. Bugcrowd has historically used custom enterprise pricing for Mayhem. A free trial has been available for the API Security mode in the past — check the current sign-up flow.
For free fuzzing alternatives, OSS-Fuzz (Google) covers open-source projects. For commercial fuzzing peers, evaluate Code Intelligence and ForAllSecure’s pre-acquisition documentation as historical reference.
How Mayhem Compares
Mayhem sits in a distinct spot among DAST tools as a fuzzing-first platform rather than a traditional web scanner.
Against conventional DAST tools like Burp Suite, Acunetix, or Invicti, Mayhem trades breadth for depth. It does not crawl websites or fill out HTML forms.
Instead, it generates thousands of targeted inputs per minute using code coverage feedback, finding memory corruption, crashes, and logic errors that signature-based scanners miss. The tradeoff: it requires compiled artifacts or API specs as input, not just a URL.
Compared to other API testing tools like StackHawk or Escape, Mayhem’s coverage-guided approach provides deeper testing but requires more initial setup. StackHawk is faster to configure for OpenAPI-based scanning; Mayhem finds more nuanced issues but demands build pipeline integration.
For teams that need both traditional web DAST and fuzzing, running Mayhem alongside a crawler-based scanner like ZAP or Nuclei covers both dimensions. Mayhem’s built-in ZAP integration for API testing already follows this complementary approach.
The Dynamic SBOM capability competes with SCA tools rather than DAST tools. Its runtime reachability analysis reduces noise from tools like Snyk, Dependabot, or Grype.