Between January and April 2026, I added 56 new application security tools to the AppSec Santa database across 9 categories, tracked week by week through the AppSec Tool Radar newsletter. The latest 2026 launches lean heavily toward AI Security, with notable arrivals like Noma Security, Mindgard, WitnessAI, Cisco DefenseClaw, Corgea, OpenGrep, Endor Labs, Socket, Chainguard, and Apiiro.
What counts as a “new” AppSec tool? A tool earns the
new: trueflag when I add it to the database in 2026, whether it is a brand new company, a product from an existing vendor I had not covered yet, a material rebrand, or a tool that changed enough to warrant fresh coverage. Pure version bumps and minor feature updates do not qualify.
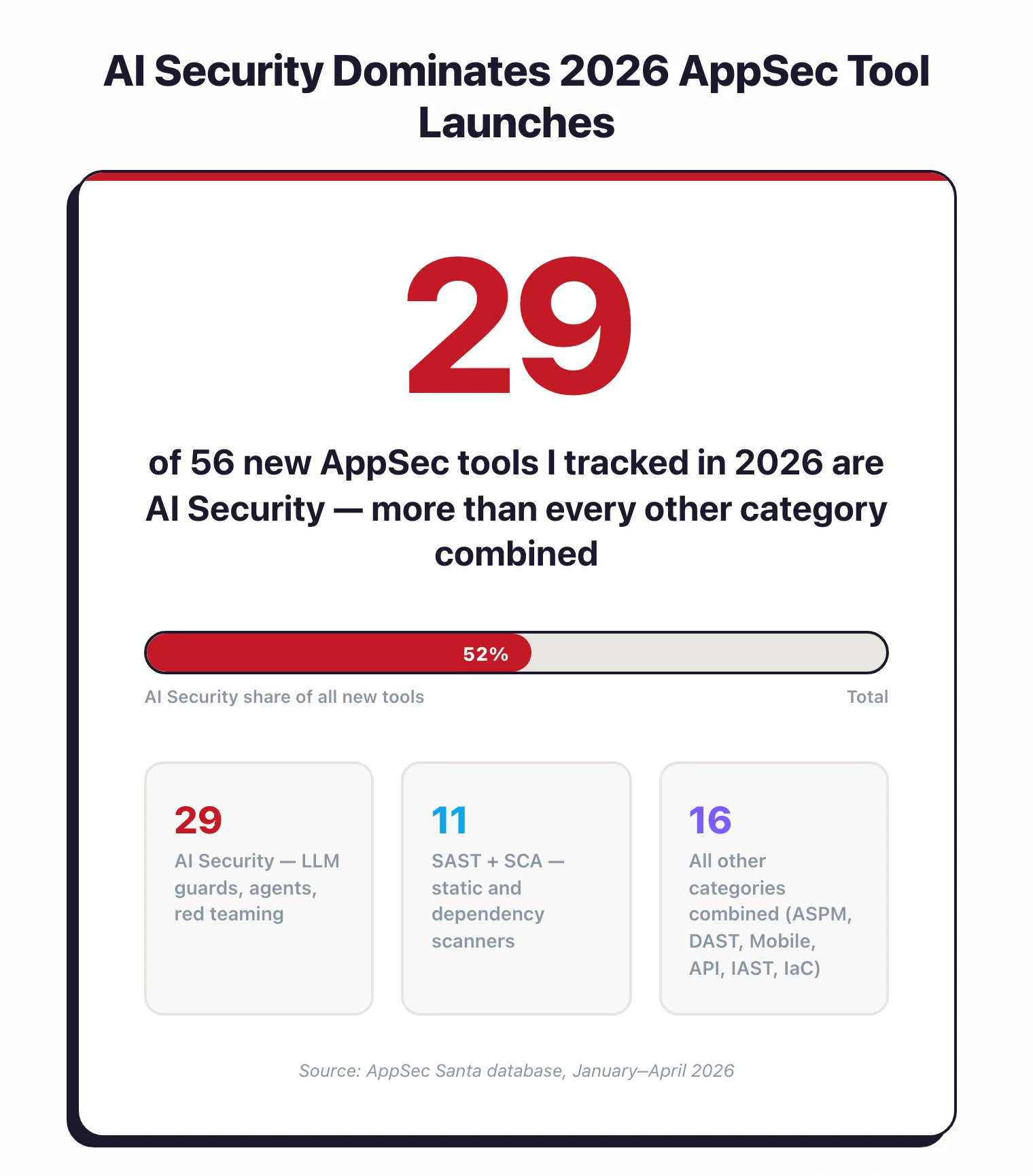
The mix is lopsided. AI Security alone accounts for 29 of the 56, which reflects where money and attention are going. SAST, SCA, DAST, ASPM, and mobile round out the rest.
In 2026, AI Security accounted for 29 of 56 new AppSec tools I tracked — more than every other category combined.
Most of the tools here launched, rebranded, or closed funding in the last 12 months. A handful are older companies that I simply had not covered on the site before 2026, and I flag those explicitly in the description. I added this page because every competitor list I found was either a static roundup from 2023 or a sales page for one vendor.
How I track new AppSec tools
Every week I ship the AppSec Tool Radar newsletter, which is where most of these tools surface first. I read vendor blogs, funding announcements, OWASP and RSA conference lists, and raw GitHub activity. When something passes the bar, I add it to the database and flag it with new: true.
My bar for “new” is loose on purpose. A newly founded company qualifies, but so does an established vendor I had not covered yet.
Rebrands count if the product materially changed. Pure version bumps do not.
Every tool on this page went through the same quick intake: I read the vendor site, check funding and GitHub activity, and look for independent coverage. If something smells like pure marketing without a product, I drop it.
Which 2026 AppSec tool launches are worth a first look?
Below are the 15 new 2026 tools I think deserve a first look, picked for diversity across categories and for how much they actually change the conversation in their space. The full list of 56 sits further down the page.
Noma Security (AI Security)
Noma bundles AI asset discovery, posture management, red teaming, and runtime protection into one platform. The Agentic Risk Map is the differentiator: it maps every agent’s connections, tools, identities, and data sources so you can see the blast radius before anything breaks.
The company raised $132M total and reports 1,300% ARR growth. I am watching this one closely because the “unified AI security platform” pitch is crowded, and Noma has the budget to outrun most of it.
Native integrations with Microsoft Copilot Studio, Salesforce AgentForce, ServiceNow, and AWS Security Hub are the proof points I weight most heavily here. Those partnerships are hard to fake.
Mindgard (AI Security)
Mindgard is a DAST-AI platform that runs automated red teaming against LLMs, agents, and multimodal models. It spun out of Lancaster University and has 11 PhDs on staff, which shows in the attack library quality.

I like that Mindgard only needs an inference or API endpoint to test, with no access to model internals. The MITRE ATLAS alignment also makes reports easier to defend in front of a security committee.
Funding sits at $11.6M total, including an $8M round led by .406 Ventures in December 2024. Small compared to Noma, but Mindgard is narrower in scope and does not need to fund a full posture-management platform.
WitnessAI (AI Security)
WitnessAI is a runtime AI security platform with intent-based behavioral controls, shadow AI discovery, and policy enforcement at the network layer. It operates between users and AI models instead of modifying the models themselves.
The intent detection angle is what caught my eye. Instead of pattern matching against known bad strings, WitnessAI analyzes the meaning behind each prompt to catch multi-turn jailbreaks that evade keyword filters.
Funding sits at $58M as of January 2026, led by Sound Ventures, on the back of 500% ARR growth in the prior year. Single-tenant deployment with full data sovereignty is the enterprise hook for regulated buyers.
Cisco DefenseClaw (AI Security)
Cisco DefenseClaw is an open-source governance framework for agentic AI that Cisco shipped at RSA 2026. The core rule is strict: nothing runs until it has been scanned, and anything flagged as dangerous is blocked automatically.
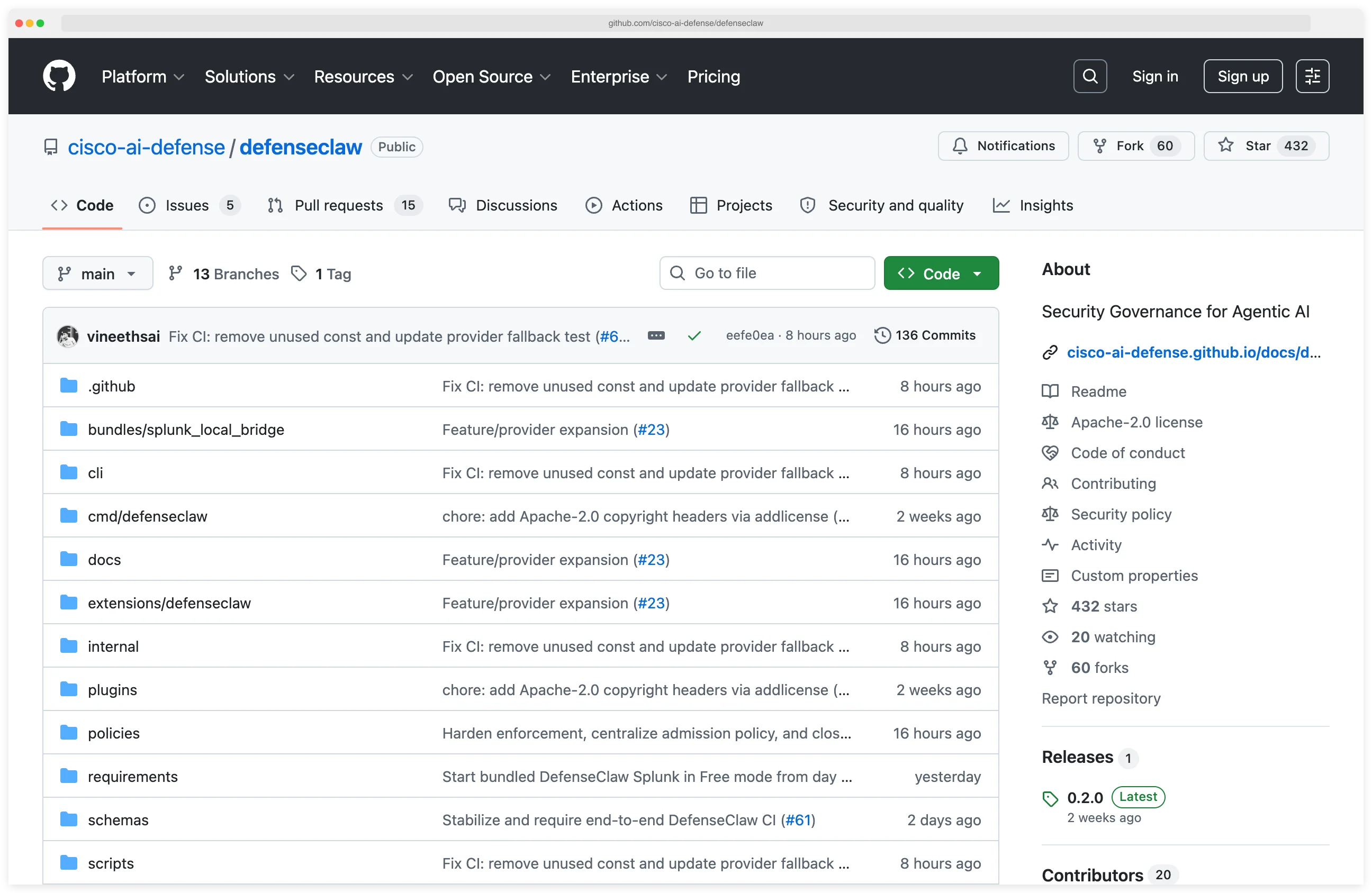
It ships four scanners for agent skills, MCP servers, static code (CodeGuard), and AI Bill of Materials generation. Sandbox isolation uses Landlock LSM and seccomp-BPF, a nice touch for anyone running agents in multi-tenant environments.
This is the first time I have seen a big network security vendor drop something meaningful into the open source AI security space. DefenseClaw is Apache 2.0, integrates with Splunk HEC and OTLP collectors, and pushes Cisco’s AI Defense agenda beyond their closed enterprise stack.
Guardrails AI (AI Security)
Guardrails AI is an open-source Python framework (Apache 2.0, 6.7k GitHub stars) for validating LLM inputs and outputs. The Guardrails Hub ships pre-built validators for toxicity, PII, hallucination, and bias.
This is the tool I recommend to teams that want to self-host and do not need a managed control plane. The composition model, where you chain multiple validators into one guard, is the most flexible I have seen in open source.
There is also a commercial Guardrails Pro managed service for teams that want hosted validation, dashboards, and enterprise support. I have only tested the open-source core, which is already enough for most production use cases.
Corgea (SAST)
Corgea is an AI-native SAST scanner that combines LLM analysis with AST-based static analysis, then auto-generates code fixes for developer approval. The company is a Y Combinator S23 grad with $2.6M in seed funding.
What caught my eye is the integration model. Corgea can run as a standalone SAST scanner or bolt onto existing Snyk, Semgrep, Checkmarx, Fortify, or CodeQL findings and generate fixes on top.
Corgea reports false positive rates below 5%, compared to 20%+ with traditional pattern-matching SAST. I have not verified that number on my own code, but the direction matches what I see with other LLM-assisted scanners.
OpenGrep (SAST)
OpenGrep is the community fork of Semgrep CE that restores taint analysis, inter-procedural scanning, and Windows support, all features Semgrep Inc. removed from the open-source edition. It is LGPL-2.1 licensed and backward compatible with Semgrep rules.
The interesting bit is the consortium behind it. Ten or more appsec companies (Aikido, Endor Labs, Jit, Orca Security, and others) fund a full-time OCaml development team. I am cautiously optimistic this model holds.
OpenGrep supports 30+ languages with taint tracking across 12 of them, and Visual Basic support is exclusive to OpenGrep at the moment. Existing Semgrep rules, JSON output, and SARIF output all work without modification, so switching over is mostly a binary swap.
Endor Labs (SCA)
Endor Labs runs function-level reachability analysis across 40+ languages and claims a 97% reduction in SCA alert noise. The platform also covers SAST, container scanning, secrets, and malware detection.
Customers include OpenAI, Cursor, Snowflake, and Atlassian, which is not a bad customer list for a company founded in 2021. Reachability is the feature that finally makes SCA dashboards tolerable, and Endor is one of the best I have tested.
Endor is also one of the backers of the OpenGrep consortium, which signals where the company thinks the commoditized parts of SAST are heading. The strategy is to own reachability and leave pattern matching to the community fork.
Socket (SCA)
Socket detects supply chain attacks by analyzing package behavior (network calls, filesystem access, shell execution, obfuscated code) instead of waiting for a CVE. It is free for open source projects and covers 10+ ecosystems.
I run Socket alongside a traditional SCA tool on my own projects. The two find different things: Snyk catches known CVEs, Socket catches the malicious npm package that was published 40 minutes ago.
Pro tip: Pair Socket with a CVE-based scanner like Snyk. The two find genuinely different things — CVE scanners catch known vulnerabilities, behavioral scanners catch the malicious npm package that was published 40 minutes ago. Running only one of them leaves a gap.
The GitHub App integration is the best-in-class part. Every PR with a dependency change gets a security report as a comment, and bad packages get blocked before they ever enter main.
Chainguard (SCA)
Chainguard ships 2,000+ hardened container images built on Wolfi, most with zero known CVEs. Every image includes a build-time SBOM and Sigstore signature, with SLSA Build Level 2 provenance.
The team came from Google and built Sigstore before starting Chainguard. Reported ARR hit $40M in 2025, which is unusually strong for a container-focused vendor. The free tier gives you about 50 :latest images without a login.
Chainguard is also the clearest example of how 2026 SCA is shifting. Instead of scanning broken images, you start from hardened ones, so security work moves to build time instead of runtime alerts.
Escape (DAST)
Escape is an API-native DAST platform that specializes in business logic bugs like BOLA, IDOR, and broken access control, which classic web scanners were never designed to find. It runs 140+ attack scenarios against REST and GraphQL APIs.
I tested Escape against a small GraphQL API of mine and it generated smarter authorization probes than any legacy DAST tool I have used. The open-source GraphQL Armor middleware is a useful side bet for teams not ready to buy.
Escape is Y Combinator backed, SOC 2 Type II compliant, and claims roughly 2,000 security teams as customers. The agentless model needs no proxy or traffic capture, which is the main edge over Burp-style tools that require heavier setup.
AppTrana (DAST)
AppTrana by Indusface combines DAST scanning, WAF, DDoS protection, bot mitigation, and API security into one fully managed WAAP subscription. The 24/7 SOC handles false positive tuning at no extra cost.
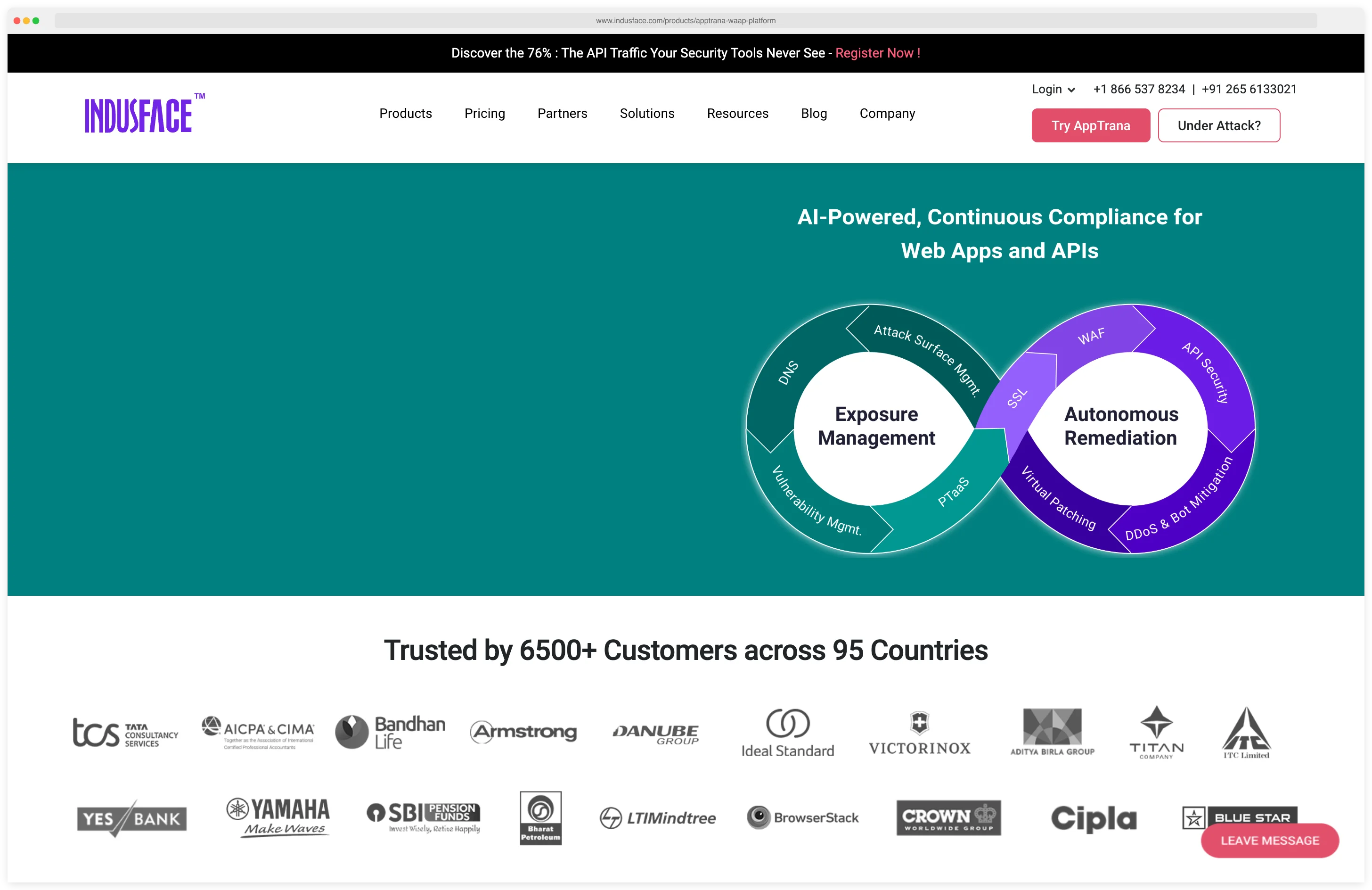
I added it because the “find a vuln and virtually patch it within 72 hours” SwyftComply workflow is genuinely useful for compliance-driven teams. Advanced plan pricing starts at $99 per app per month on a published page.
Indusface, the parent company, is headquartered in India and backed by Tata Capital. The managed SOC, false positive monitoring, and custom rule creation are included at no extra cost, which is unusual in the WAAP space.
Apiiro (ASPM)
Apiiro has emerged as one of the strongest ASPM platforms, with customers including USAA, BlackRock, Shell, SoFi, and Equinix. The platform uses Deep Code Analysis and a Risk Graph to tie code changes to runtime impact.
I am still forming an opinion on Apiiro. The Risk Graph demo is impressive and the customer list is serious (USAA, BlackRock, Shell), but Deep Code Analysis is a broad claim and I want to run it against my own codebase before I fully buy in.
The Guardian Agent feature specifically targets AI-generated code from Copilot and Cursor. That is a useful angle given that empirical studies put Copilot suggestions in roughly the same vulnerability range as human developers (Asare et al., 2022). Every ASPM vendor is now scrambling to say something about AI code, and this study is part of why.
Legit Security (ASPM)
Legit Security is an AI-native ASPM platform with native SAST, SCA, and secrets scanning, not just aggregation from other tools. It has 120+ integrations and specific guardrails for Cursor, GitHub Copilot, and Windsurf.
The AI code assistant guardrails are the interesting wrinkle. Most ASPM tools still treat AI-generated code like any other commit, but Legit routes it through a separate review path. The company has raised $70M.
Legit serves Fortune 500 enterprises with complex pipelines and thousands of developers, which is a harder sell than a tool aimed at mid-market. I expect the next 12 months will clarify whether Legit or Apiiro wins the “heavy ASPM” category.
Appdome (Mobile)
Appdome protects Android and iOS apps with 400+ no-code defenses injected directly into compiled binaries via CI/CD. ONEShield RASP handles anti-tampering, anti-debugging, and anti-emulator protection.
The no-code angle is the pitch. Your mobile developers do not need to integrate an SDK or ship new source code; you hand Appdome your APK or IPA and get a hardened build back. Pricing is custom enterprise.
Customers cluster in financial services, gaming, streaming, and retail. Those verticals ship on aggressive release cycles where waiting for dev teams to integrate SDKs is a nonstarter. ThreatScope, the real-time threat intelligence and analytics layer, is the piece I find most useful for ongoing monitoring.
How are the 56 new 2026 AppSec tools split by category?
Here is how the 56 new tools distribute across categories. AI Security dominates, and the next four categories together barely match it.
The 56 new tools split as 29 AI Security, 6 SCA, 5 SAST, 5 ASPM, 4 DAST, 3 Mobile, 2 API Security, 1 IAST, and 1 IaC Security.
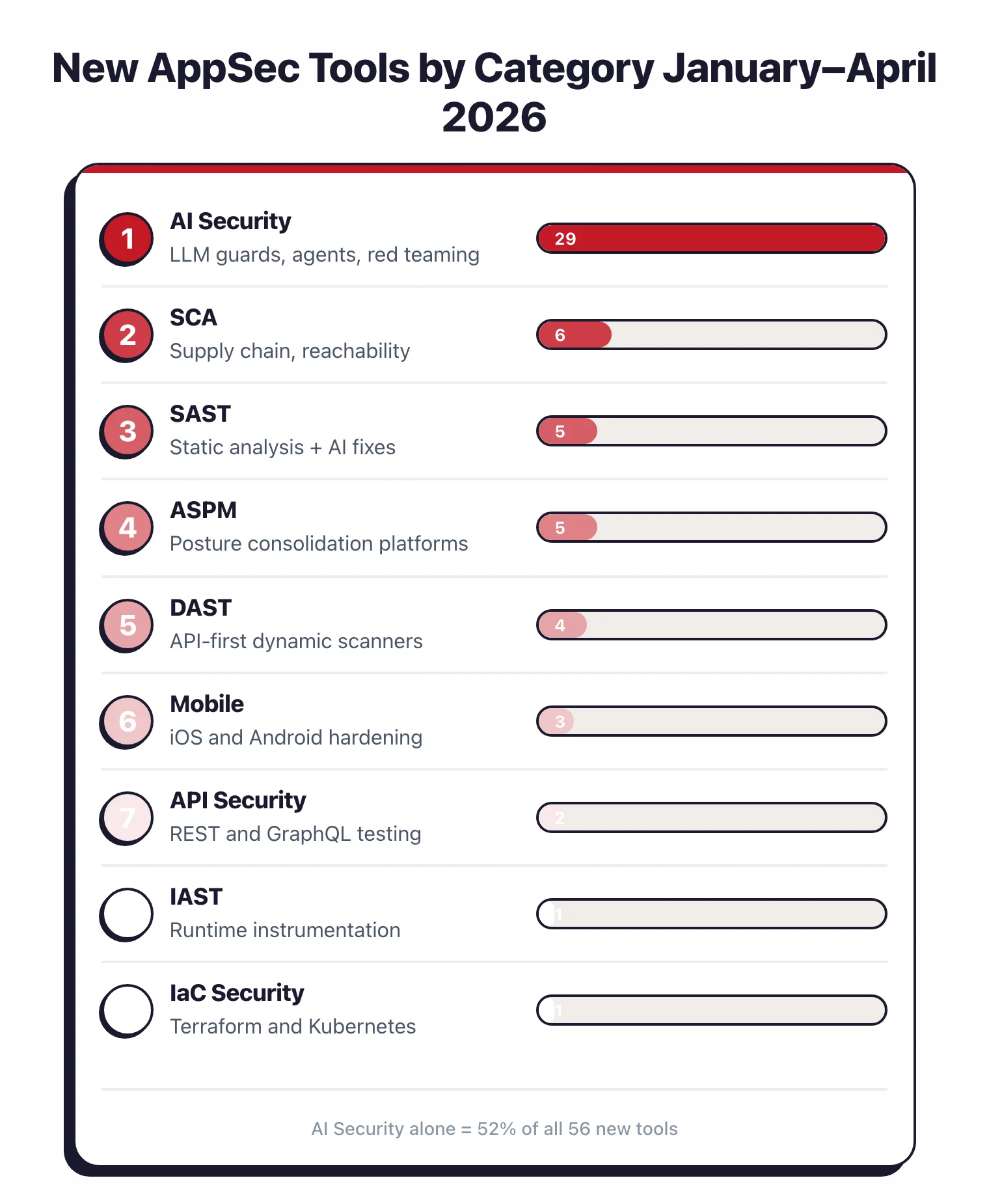
The AI Security bucket of 29 tools splits further. Roughly half are runtime guards and firewalls (Noma, WitnessAI, Protecto, NeuralTrust, Lasso Security), a third are red teaming and evaluation tools (Mindgard, Garak, PyRIT, FuzzyAI), and the rest cover niche angles like MCP scanning, RAG protection, and agent observability.
Most of these tools exist because of a single class of attack: indirect prompt injection, formalized in the AISec@CCS paper that showed LLM-integrated applications can be hijacked through untrusted data sources at scale (Greshake et al., 2023).
SCA looks traditional on paper with 6 new entries, but the focus has shifted. Reachability analysis (Endor Labs), supply chain attack detection (Socket), and hardened base images (Chainguard) now drive most of the conversation. Classic CVE scanners are not where new money is flowing.
SAST has 5 new tools with very different approaches. Corgea leans on LLMs for detection and auto-remediation. Qodana ports JetBrains IDE inspections into CI, Parasoft keeps its compliance-first rule engine for automotive and medical, Betterleaks is a Gitleaks successor for secrets, and OpenGrep is the community fork of Semgrep CE.
ASPM added 5 new entries: Apiiro, Legit Security, Aikido, Jit, and Seemplicity. This is a consolidation category. ASPM platforms are starting to ingest findings from SAST, SCA, DAST, cloud, and now AI into one dashboard.
Mobile, API Security, IAST, and IaC Security together account for 7 tools. These are the quiet categories where new launches are rare and usually meaningful. Appdome, Levo.ai, Invicti Shark, and Mondoo are the standouts.
A few themes repeat across the 56 tools that are worth calling out.

First, the word “agent” shows up in nearly every new AI Security tool. The industry is now designing for autonomous AI agents and MCP servers instead of just LLM prompts.
Second, reachability analysis is no longer a luxury feature in SCA. Endor, Aikido, and several others treat it as table stakes. Third, AI-powered auto-remediation has crossed into SAST as a real product instead of a demo.
The acquisition pattern is also hard to miss. Check Point bought Lakera, F5 bought CalypsoAI, and Cisco rolled out DefenseClaw after its earlier Robust Intelligence acquisition. Large network security vendors are clearly buying their way into AI security rather than building from scratch.
Key Insight
Large network security vendors are not building AI security from scratch — they are buying their way in. Check Point + Lakera, F5 + CalypsoAI, Cisco + Robust Intelligence (now DefenseClaw). If you are tracking where AI security consolidates next, watch which independent vendor has the customer list a network giant cannot replicate in 18 months.
Funding still flows freely into AI Security specifically. Noma ($132M), Apiiro ($135M), and WitnessAI ($58M in January 2026) all show investors are willing to write big checks at the top of the market. Meanwhile, open-source projects like Garak, PyRIT, Guardrails AI, and now Cisco DefenseClaw keep improving without any commercial pressure.
The complete 56-tool list
The full list of new 2026 tools renders below, grouped by category and pulled live from the database. Any tool I flag as new: true this year shows up automatically, so the list stays current without me editing this page.
Methodology
I run AppSec Santa as a one-person project and track new tools through a weekly cadence tied to the AppSec Tool Radar newsletter. Primary sources are vendor announcements, funding news, OWASP and conference speaker lists, GitHub release feeds, and reader tips. Every tool on this list has a full review page on the site with its own features, pricing notes (when published publicly), and FAQ.
I do not accept paid placements. A tool either makes the list because it exists and I can verify it, or it does not. If a vendor sends me a press release, I check the claims against their documentation before adding anything.
If you know of a new AppSec tool I should add, reply to any newsletter issue and I will take a look. I add roughly one to three tools per week on average, so the list grows throughout the year.
