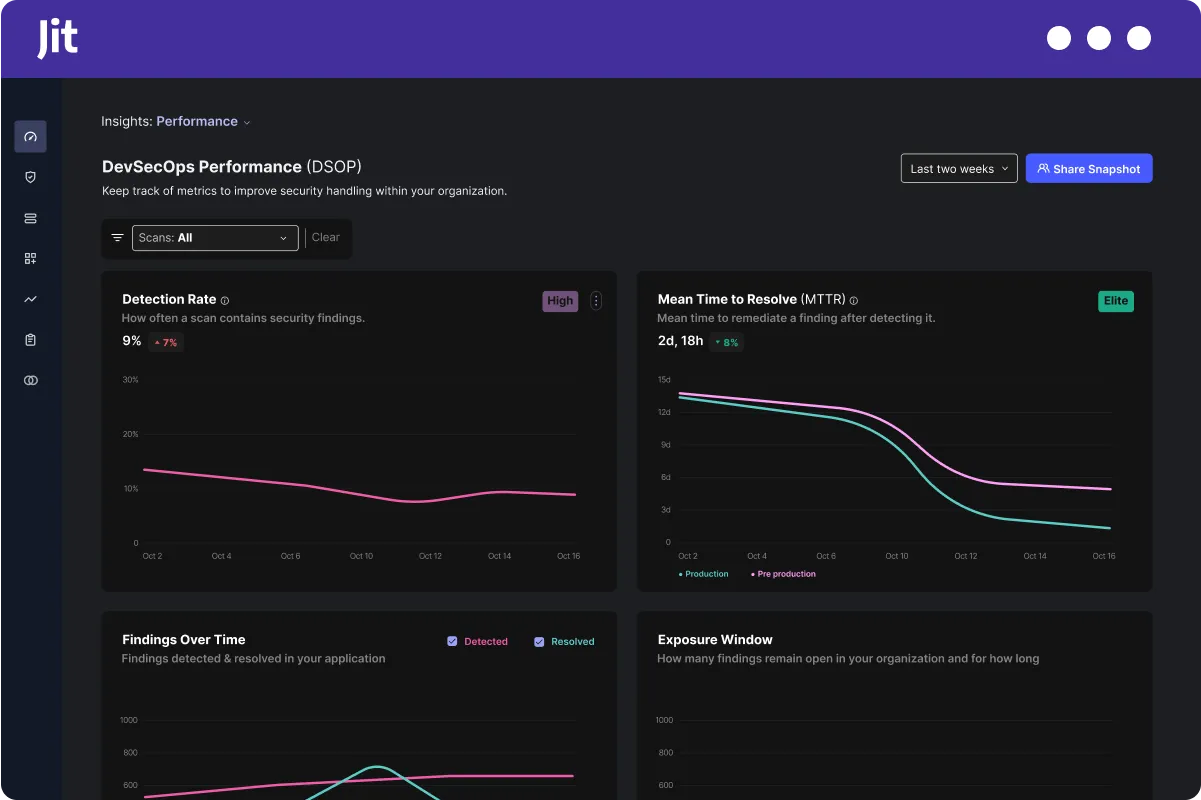
Jit is an AI agent ASPM platform for product security teams. It bundles its own SAST, SCA, secrets detection, IaC, CSPM, DAST, and container scanning with AI agents that automate triage, remediation, and compliance work.
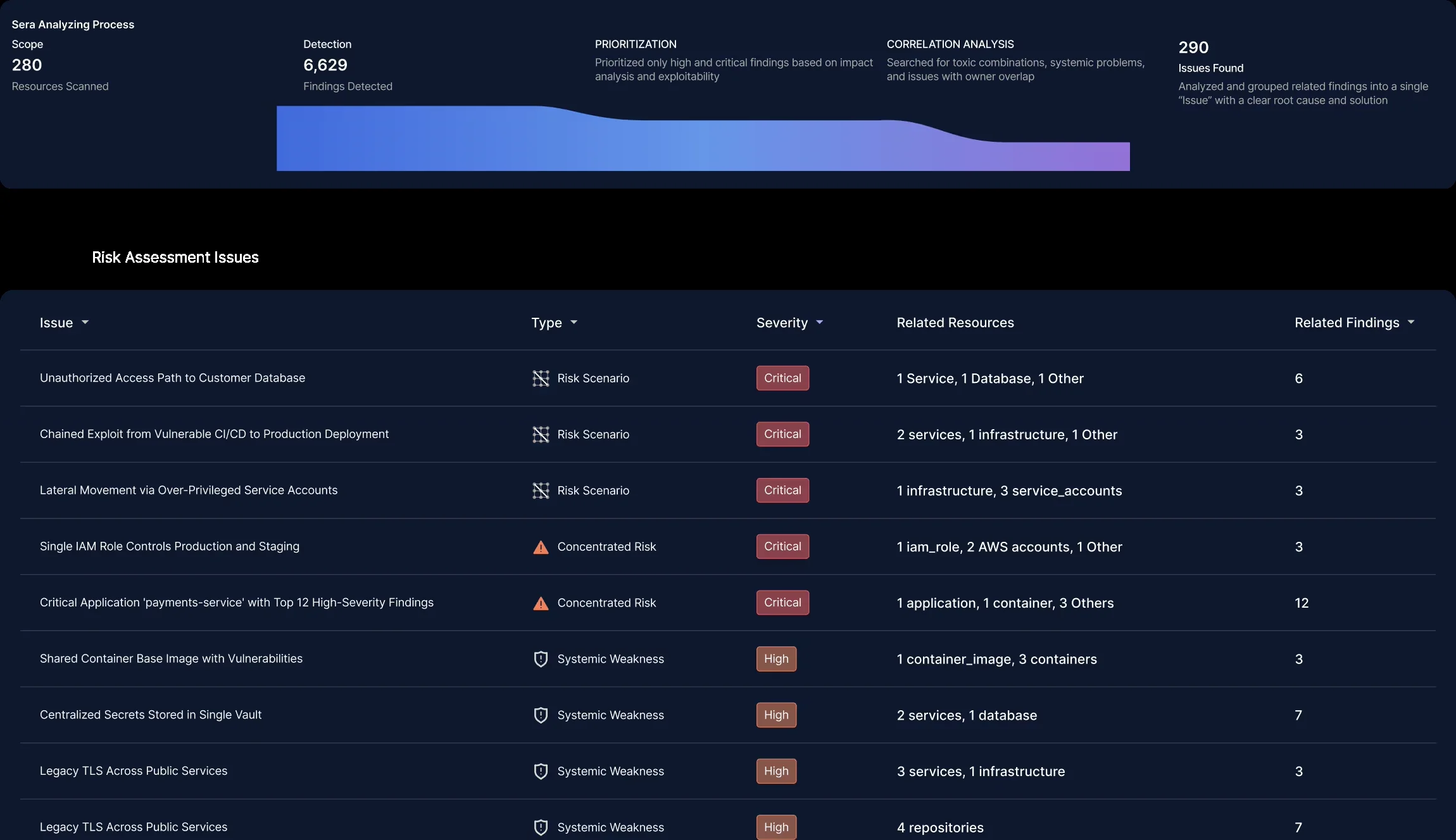
Everything runs through what Jit calls the Company Context Graph, a knowledge graph that maps code repositories to cloud infrastructure, team ownership, and business context. Agents use this graph when analyzing and prioritizing findings.
The company is headquartered in Boston, backed by Tiger Global, Insight Partners, Boldstart Ventures, FXP, and TechAviv. SOC 2 Type 2 certified and an AWS Partner.
What is Jit?
Jit started as a developer-first ASPM platform and has since repositioned around AI agents. Unlike aggregation-focused ASPM tools that expect you to bring your own scanners, Jit ships its own scanning engines and puts AI agents on top to handle analysis, triage, and remediation.
Three ideas hold the platform together:
Key Features
AI security agents
Jit’s agent system is the main differentiator from traditional ASPM tools:
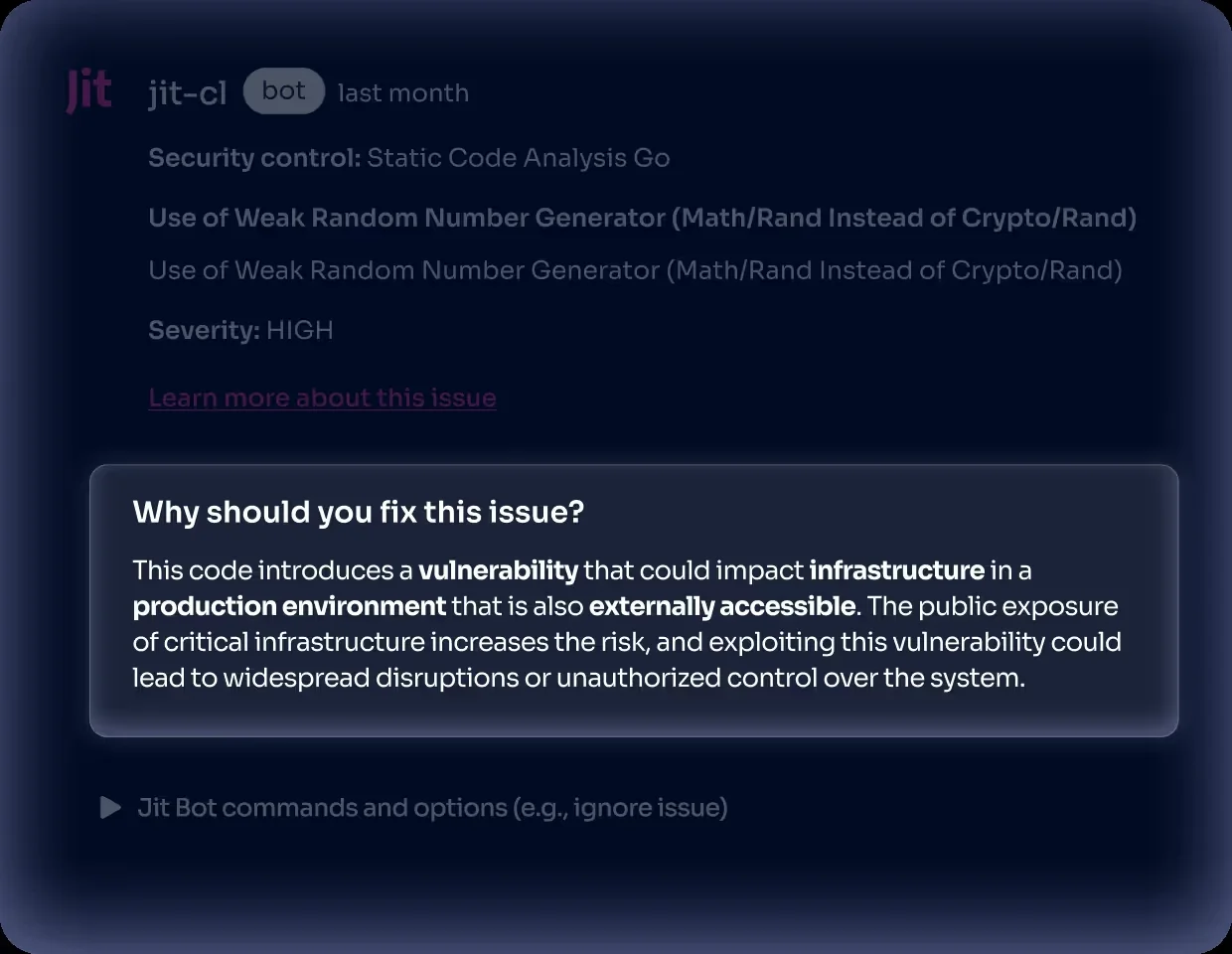
- Core Agents analyze findings, prioritize by context, and correlate issues across code and cloud using the Company Context Graph
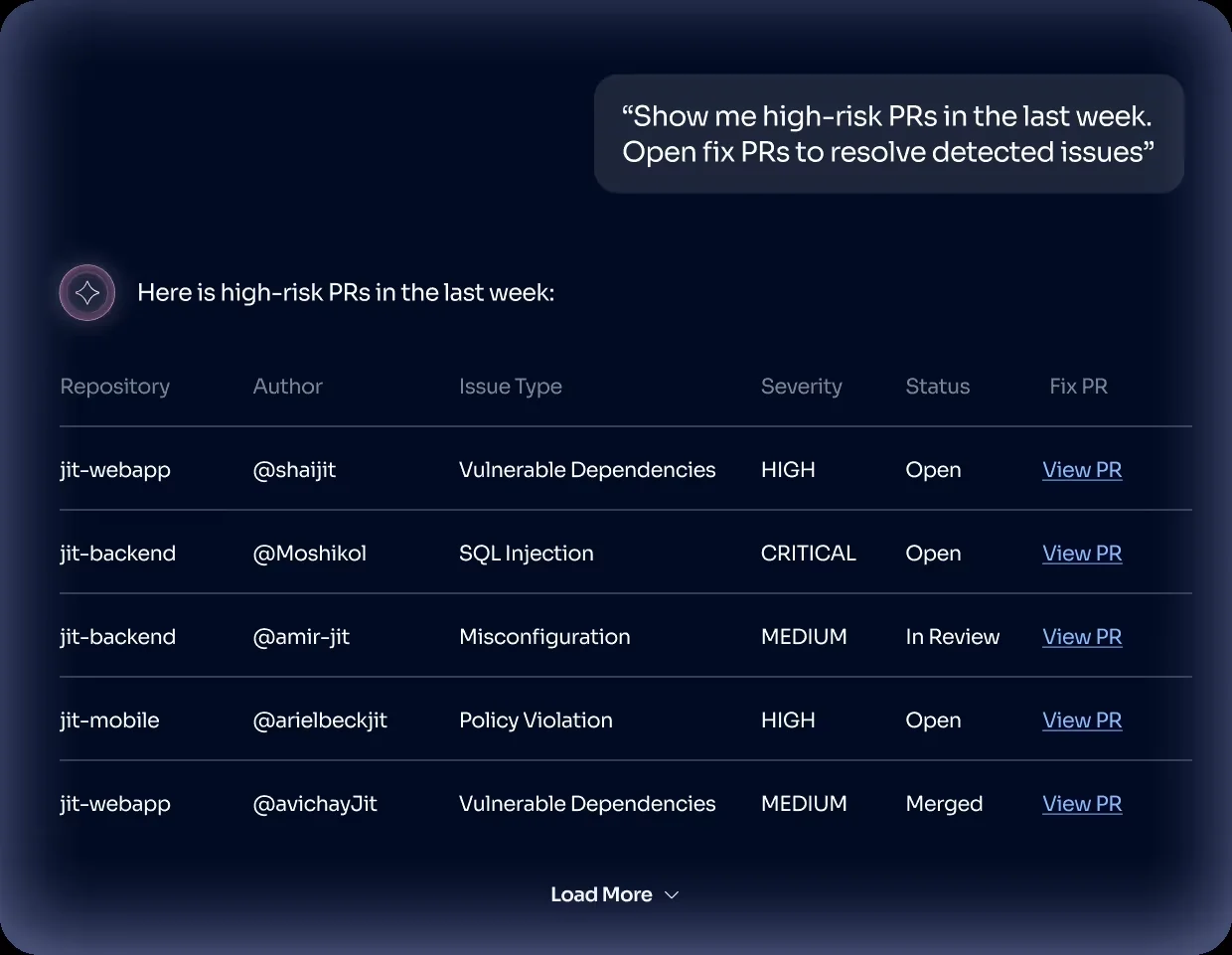
- Pre-Built Agents handle common jobs: triaging vulnerabilities, opening fix PRs, collecting compliance evidence
- Custom Agents let teams build their own agents for organization-specific security workflows
- All agents follow a four-step loop: Plan (break the task down), Execute (take actions), Reflect (check the results), Respond (deliver output)
Built-in security scanning
Jit runs its own scanners rather than wrapping third-party tools. All scans execute in Jit’s managed infrastructure, not in your CI/CD pipelines.
- SAST - Static analysis of source code for security vulnerabilities
- SCA - Dependency vulnerability detection and analysis
- Secrets Detection - Scanning for exposed credentials and API keys
- IaC Security - Infrastructure-as-code misconfiguration detection (Terraform, CloudFormation, Kubernetes)
- CSPM - Cloud security posture management for AWS, Azure, and GCP
- DAST - Dynamic application security testing
- Container Scanning - Vulnerability detection in container images
- SBOM Generation - Software bill of materials creation
- License Detection - Open source license compliance checking
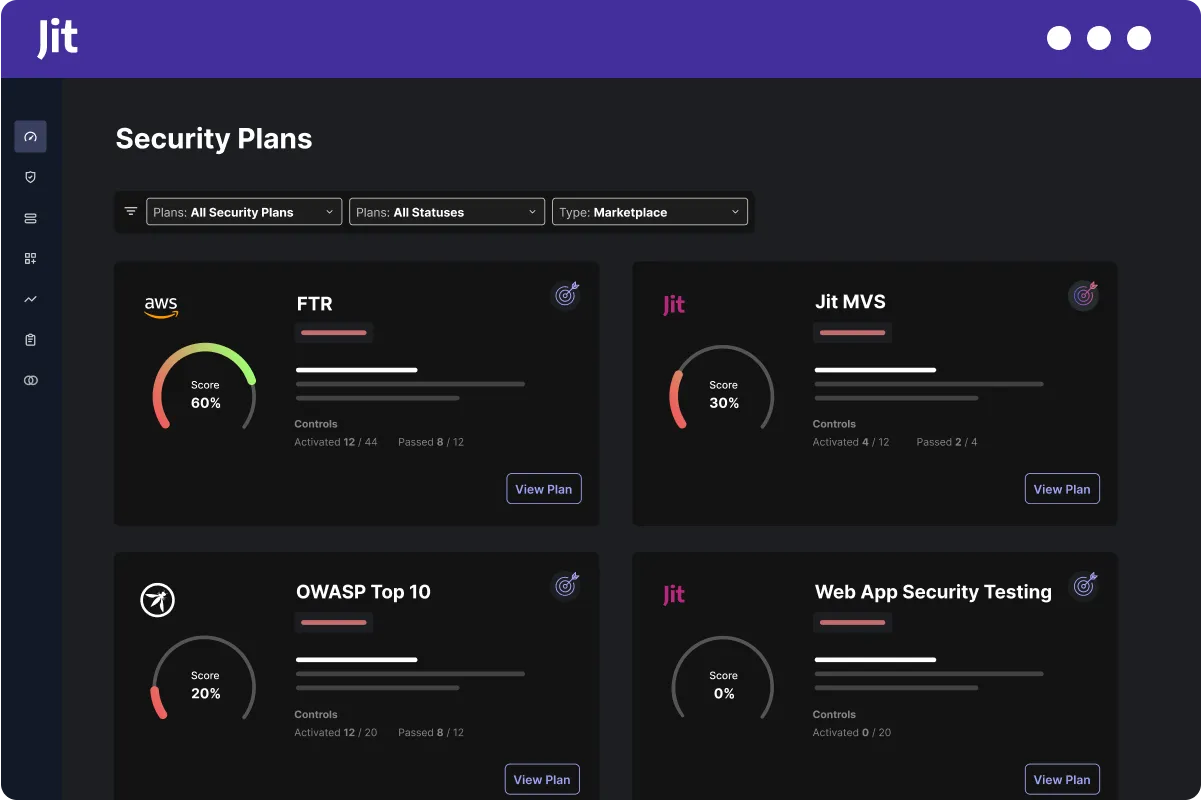
Security Plans
Each plan bundles the scanners and policies you need for a particular goal:
- MVS for AppSec - A starter set of scanning and controls for teams that want baseline coverage without configuration overhead
- AWS Foundational Technical Review - Controls aligned to AWS FTR requirements
- GitHub Security Best Practices - Security configuration tuned for GitHub-based workflows
- SOC 2 Compliance - Controls mapped to SOC 2 certification requirements
- Maximum Security - Turns on everything Jit offers
IDE plugins
Jit has plugins for three IDEs:
- VS Code
- IntelliJ
- Cursor
Integrations
Jit integrates across 12 categories. Here are the main ones:
Getting started
Jit also offers what it calls Velocity Engineers, staff who help with onboarding and initial configuration.
When to use Jit
Jit makes sense when you’d rather have one platform with its own scanners than stitch together separate SAST, SCA, secrets, and IaC tools yourself.
It’s a good fit if:
- You don’t have a large existing security toolchain and want scanning built in from day one
- You want AI agents doing triage and remediation instead of manual review cycles
- Compliance (SOC 2, AWS FTR) is driving your security program and you’d rather pick a plan than configure controls one by one
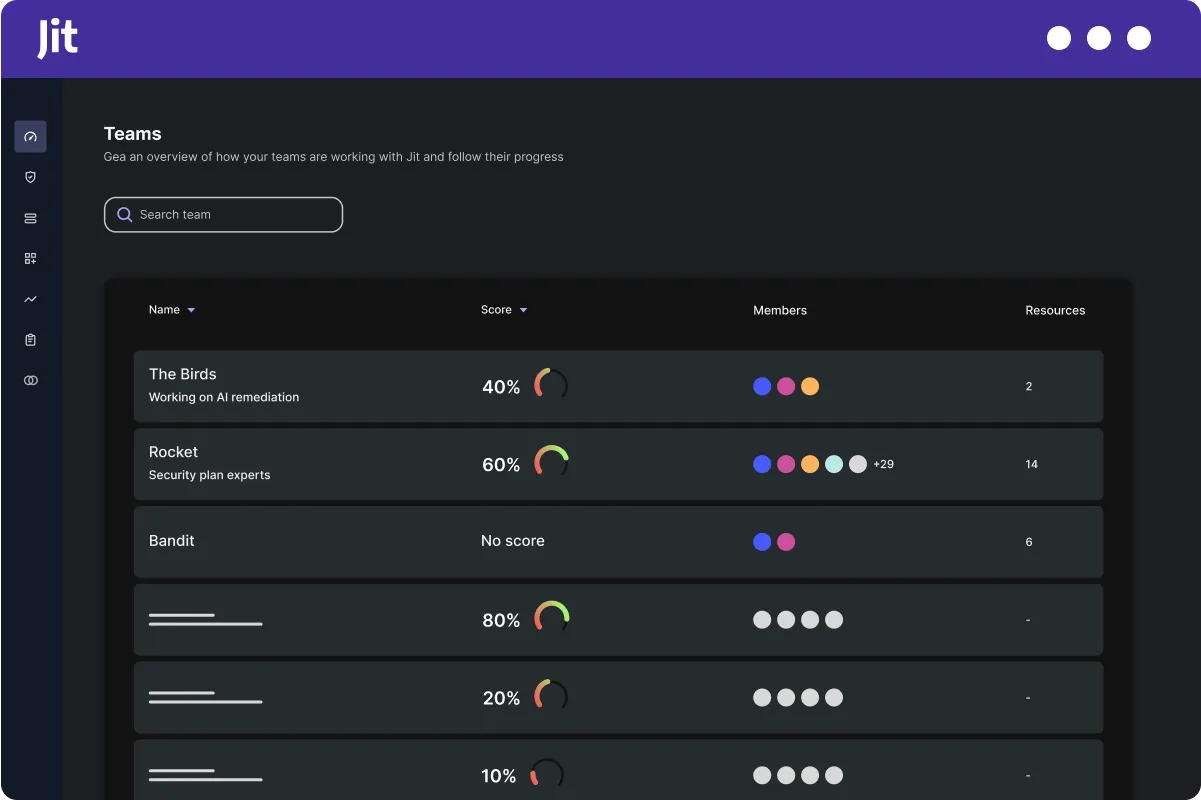
- Your developers are expected to own security outcomes, not hand them off to a separate AppSec team
- You’d rather scans run on Jit’s infrastructure than eat into your CI/CD minutes
It’s probably not the right pick if:
- You already have security tools you like and just need something to aggregate their findings
- You need fine-grained control over individual scanning engines
- All your tooling must run on-premises or in your own cloud accounts
The founding team includes CEO Shai Horovitz, CTO David Melamed (PhD), and Co-Founder Aviram Shmueli.