Invicti Shark is an IAST sensor that pairs with the Invicti DAST scanner. The scanner attacks from outside; Shark watches from inside the runtime and catches vulnerabilities and hidden assets that external-only scanning misses.
The team behind Shark built one of the first commercial IAST implementations (AcuSensor). Shark plugs directly into Invicti’s Proof-Based Scanning, so reported vulnerabilities come with both exploitation proof and exact code locations.
What is Invicti Shark?
Shark sits inside your application while the scanner sends requests. It observes how those requests move through backend code.
You get file names, line numbers (for PHP), and stack traces (for Java and .NET) for each finding.
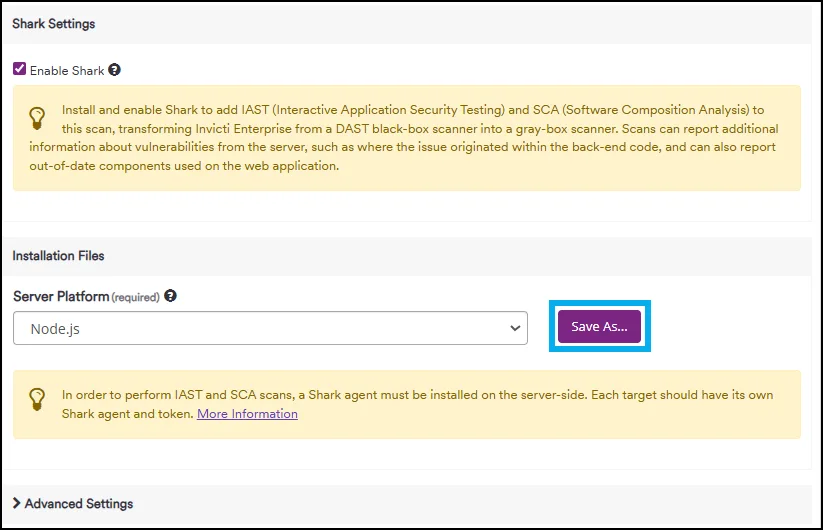
Each Shark Token is generated uniquely per target from the Target configuration panel in Invicti. The default bridge URL is https://iast.invicti.com, which needs to be whitelisted. Bridge URL and port are configurable per target.
Key Features
| Feature | Details |
|---|---|
| Supported Languages | PHP, Java, .NET, Node.js |
| Scanning Approach | IAST sensor paired with DAST scanner |
| Vulnerability Proof | Combined Proof-Based Scanning + runtime observation |
| Code Location | File names, line numbers (PHP), stack traces (Java/.NET) |
| API Coverage | OWASP API Top 10 (BOLA, IDOR, BFLA) |
| Asset Discovery | Hidden endpoints, admin panels, backup files, form parameters |
| Bridge URL | https://iast.invicti.com (configurable per target) |
| Deployment | Staging/test environments only |
Hidden asset discovery
DAST crawlers only find pages and endpoints linked from other pages. Shark sees everything inside the application directory:
- Admin panels with no public navigation links
- API endpoints missing from documentation
- Backup files and development artifacts
- Hidden GET and POST parameters the crawler never encounters
So the attack surface Invicti actually tests goes well beyond what crawling alone covers.
Proof-Based Scanning integration
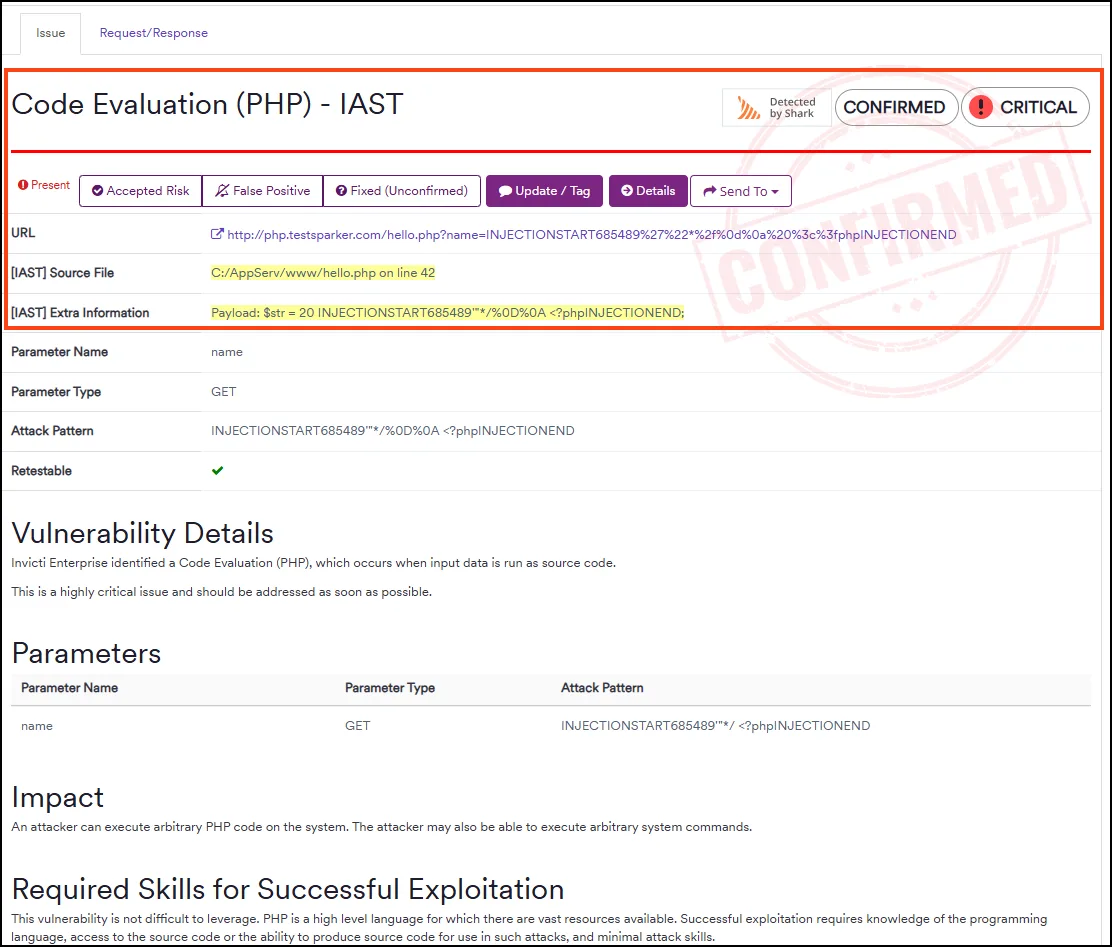
Invicti’s Proof-Based Scanning confirms vulnerabilities by safely exploiting them and producing evidence. Shark adds the internal view: it confirms that payloads actually reached vulnerable code, provides the call chain showing the attack path, and verifies that input bypassed sanitization.
You end up with vulnerability reports that are both verified as exploitable and pinned to specific code locations.
SQL injection tracing
For SQL injection findings, Shark traces the full path from user input to database query. You see which sanitization functions were called (if any), whether they worked, and how the final query was constructed.
Instead of a generic “SQL injection found” report, developers get the specific data flow that needs fixing.
API security flaw detection
Shark also monitors for API vulnerabilities that need runtime context to identify:
- BOLA — detects when user input directly accesses objects without authorization checks
- IDOR — identifies direct references to internal implementation objects
- BFLA — finds missing authorization on administrative functions
These are nearly impossible to catch from outside the application.
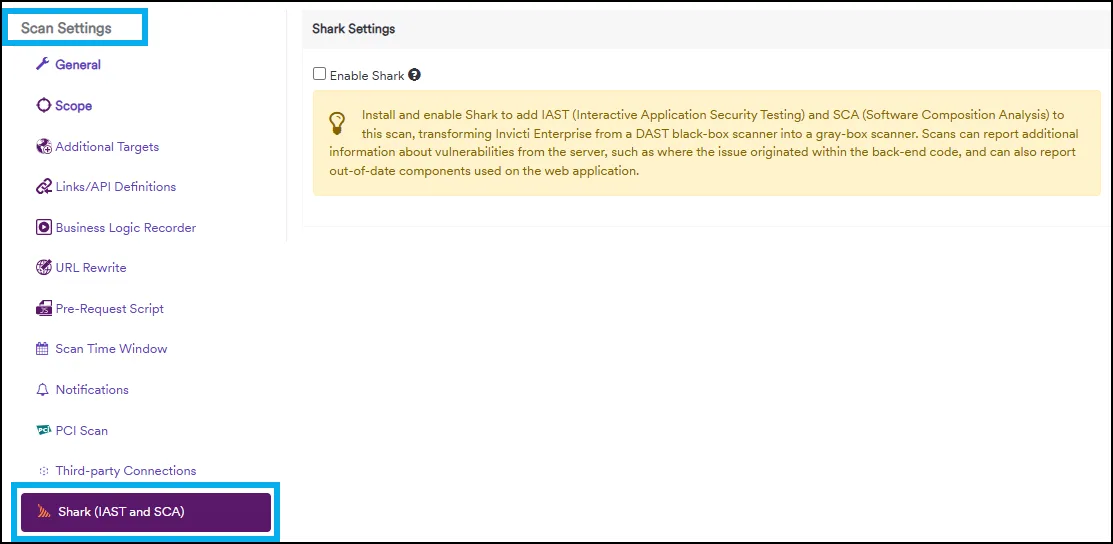
Getting Started
Deploy the sensor — Install Shark on your staging or test environment. PHP uses an extension, Java uses a JVM agent argument, .NET uses a package. No source code changes needed.
When to use Invicti Shark
If you already run Invicti for DAST and want more actionable results, Shark is worth a look. The IAST layer adds code locations and hidden asset discovery without changing your scanning workflow.
Deploy it on staging servers or in virtual machines as part of CI/CD pipelines. Not recommended for production since active sensors consume resources.
If you need standalone IAST without a paired DAST scanner, consider Contrast Assess or Seeker IAST. If you use Datadog for observability, Datadog IAST integrates directly with APM tracing.