Intruder is a cloud-based continuous vulnerability scanner that monitors your external attack surface for security weaknesses. It runs 140,000+ checks against web applications, APIs, cloud infrastructure, and network services.
Founded in 2015 and selected for the GCHQ Cyber Accelerator, Intruder now serves 3,000+ customers. It has a 4.8/5 rating on G2 from 154 reviews.
| Feature | Details |
|---|---|
| Deployment | Cloud-only SaaS |
| Security checks | 140,000+ |
| Cloud connectors | AWS, Azure, GCP |
| AI analyst | GregAI |
| Compliance | SOC 2, ISO 27001, PCI DSS, HIPAA, DORA |
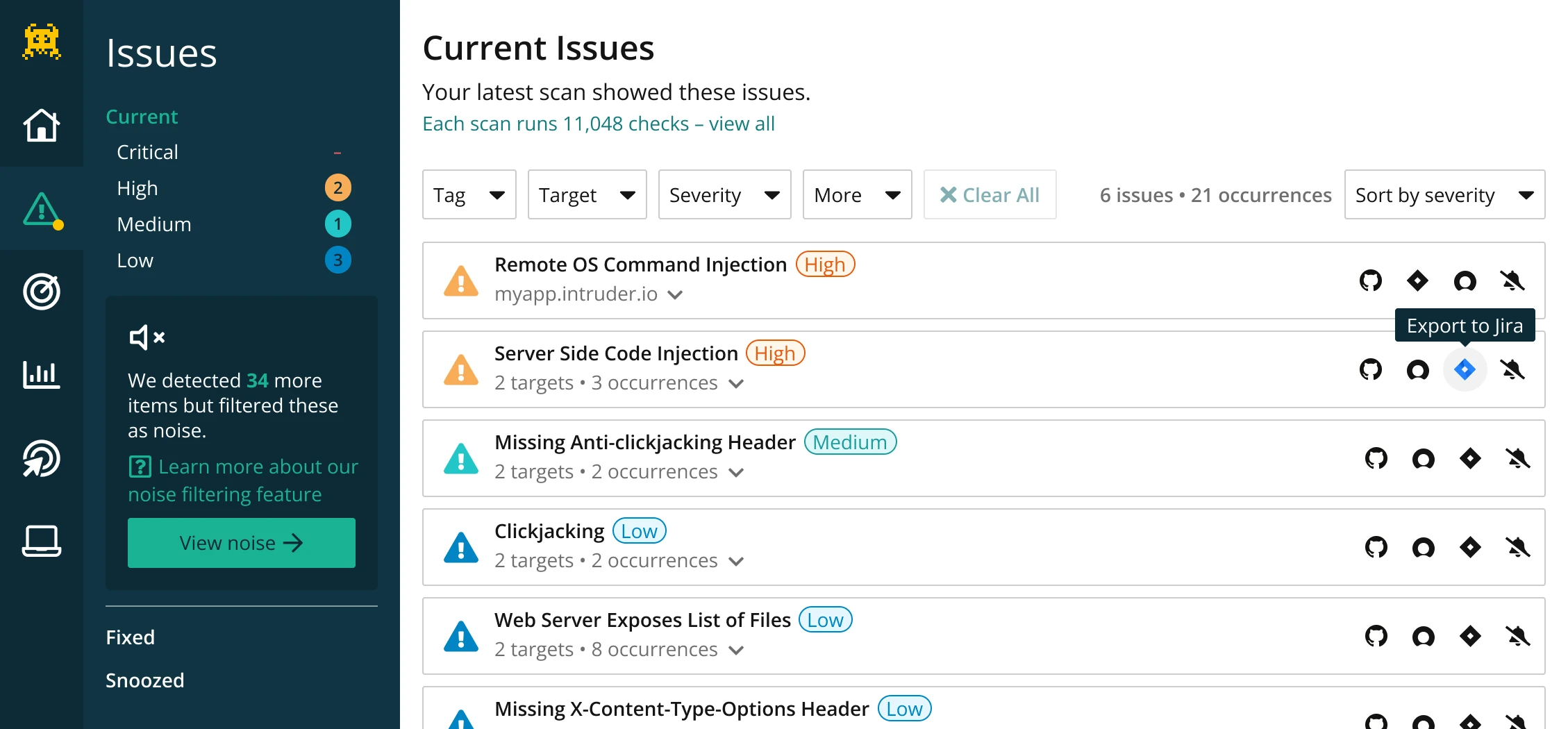
| Integrations | 15+ (Jira, Slack, GitHub, etc.) |
| API access | Pro, Premium, and Vanguard plans |
| Free trial | 14 days (Cloud plan features) |
| Starting price | See intruder.io/pricing |
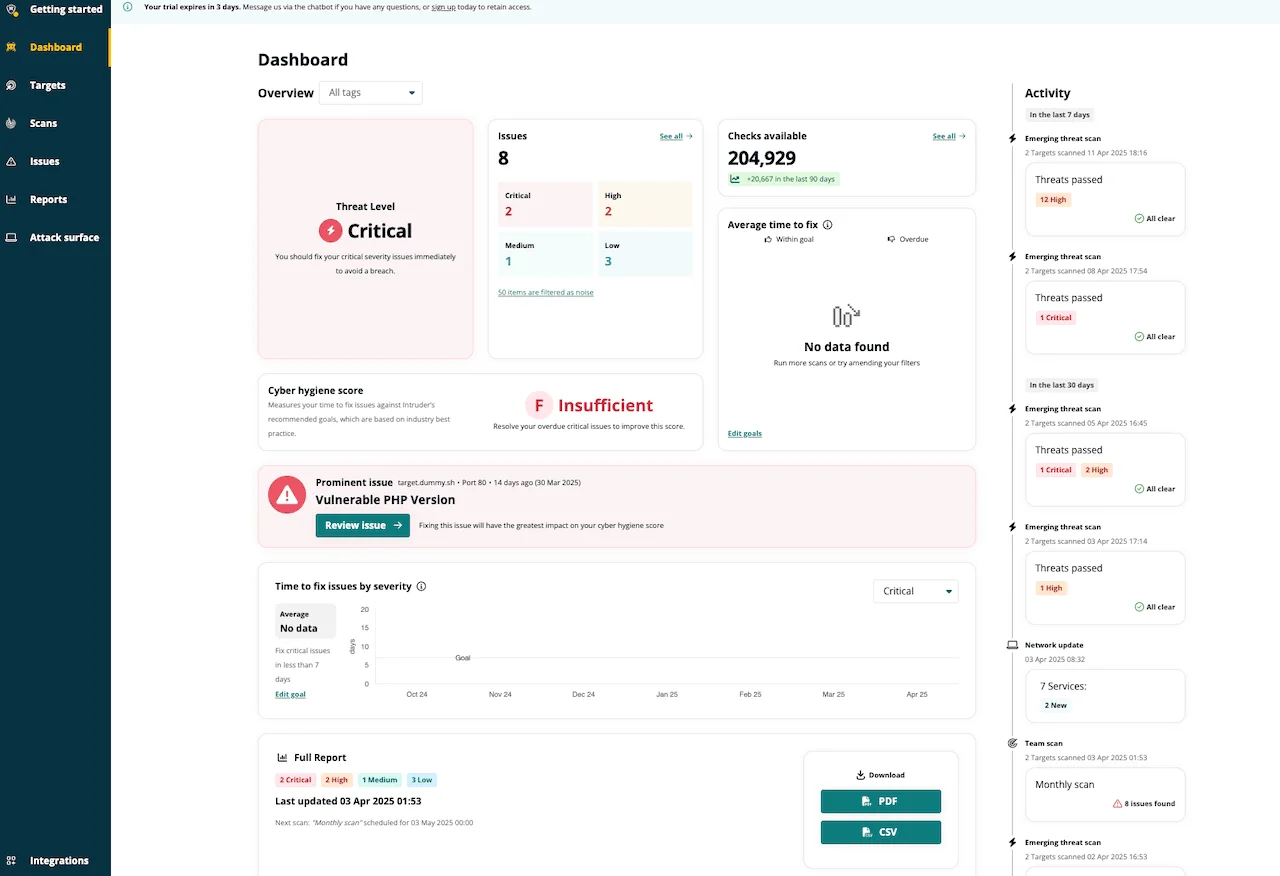
What is Intruder?
Intruder scans internet-facing systems for vulnerabilities on a continuous basis. When your infrastructure changes or a new threat emerges, it triggers scans automatically.
No manual scheduling required.
The Verizon 2024 Data Breach Investigations Report found that vulnerability exploitation as an initial access vector grew significantly year over year, reinforcing the need for continuous scanning of internet-facing assets.
The platform differs from traditional DAST tools in scope. Where most DAST scanners focus on web application logic (XSS, SQLi, authentication flaws), Intruder covers the broader attack surface: exposed ports, misconfigured services, outdated software, and cloud misconfigurations alongside web application vulnerabilities.
Intruder is an attack surface management platform with vulnerability scanning, not a deep application security tester. It finds exposed services and known CVEs across your entire perimeter.
For detailed web app testing of authenticated flows and business logic, pair it with a dedicated DAST scanner like ZAP or Burp Suite.
Key Features
Native connectors for AWS, Azure, and GCP. Runs daily misconfiguration checks and automatically imports cloud assets.
Up to 3 accounts on Cloud plan, 10 on Pro, unlimited on Enterprise.
Pricing
Intruder offers four tiers, all with 5 infrastructure licenses included:
- Essential — 1 scheduled scan, unlimited ad hoc scans, enhanced risk data, unlimited users
- Cloud — Unlimited scheduled scans, emerging threat scans, GregAI analyst, up to 3 cloud accounts, advanced analytics, role-based access, 15+ integrations
- Pro — Internal target scanning, up to 10 cloud accounts, mass deployment options
- Enterprise — Unlimited cloud accounts, 1000+ checks, attack surface visibility, advanced access control
Pricing is based on a base fee plus a per-target fee, calculated dynamically on Intruder’s pricing page.
All plans include a 14-day free trial with Cloud plan features.
Integrations
Getting Started
API Access
The Intruder API lets you manage targets, trigger scans, and retrieve results programmatically. Available on Pro, Premium, and Vanguard plans.
# Trigger a scan via the Intruder API
curl -X POST "https://api.intruder.io/v1/scans" \
-H "Authorization: Bearer YOUR_API_KEY" \
-H "Content-Type: application/json" \
-d '{"target_id": "target_123"}'
When to Use Intruder
Intruder works well for small to mid-sized organizations that need continuous attack surface monitoring without a dedicated security team. The cloud connectors and automated scanning mean less manual work for teams with cloud-native infrastructure.
It covers the gap between traditional vulnerability management (Qualys, Nessus) and application-specific DAST tools. If your primary concern is “what’s exposed on the internet and is it vulnerable,” Intruder answers that question.
For deep web application security testing of complex SPAs, authenticated workflows, or API business logic, you will need a complementary tool like Acunetix or Invicti.
Intruder itself acknowledges this positioning: it scans your perimeter, not the inner workings of your applications. For help choosing the right approach, see the what is DAST guide.