Imperva API Security is a commercial API security platform that uses machine learning to automatically discover, classify, and protect APIs across cloud and on-premises environments. It combines API discovery, schema enforcement, runtime BOLA detection, and bot protection in a single platform.
Thales Group acquired Imperva in December 2023 for $3.6 billion. The combined operation now has 5,800+ security experts across 68 countries. The Imperva brand and product line continue under Thales’s cybersecurity division, with active API security development.
Unlike tools that only monitor API traffic at the gateway level, Imperva analyzes traffic patterns using ML to find shadow and zombie APIs that organizations did not know existed.
Key Features at a Glance
| Feature | Details |
|---|---|
| API Discovery | ML-powered continuous discovery of shadow, zombie, internal, and third-party APIs across cloud and on-prem |
| Data Classification | Automatic identification of PII, payment data, and credentials flowing through each endpoint |
| Schema Enforcement | Security gap analysis of OpenAPI/Swagger definitions with runtime enforcement |
| BOLA Detection | Behavioral baselining and ML-driven Broken Object Level Authorization detection in real time |
| Bot Protection | Native integration with Imperva Advanced Bot Protection for credential stuffing and API abuse |
| OWASP API Top 10 | Coverage across all OWASP API Security Top 10 threat categories |
| Deployment Options | Cloud-managed, self-managed, agent-based, and agentless deployment models |
| Compliance | Sensitive data flow auditing for GDPR, PCI DSS, and CCPA requirements |
Overview
Imperva API Security bundles discovery, risk assessment, and runtime defense in a single platform, sitting in the broader API security tools landscape. Compared to point solutions that require stitching together separate discovery, testing, and protection tools, Imperva covers the full API security lifecycle in one product, and I have compared it head-to-head with Salt Security for buyers weighing the WAF-extension model against pure-play API behavioral runtime.
The platform handles four stages: discovering all APIs (including shadow and zombie endpoints), classifying the data flowing through them, assessing schemas for security gaps, and blocking threats in real time.
Key Features
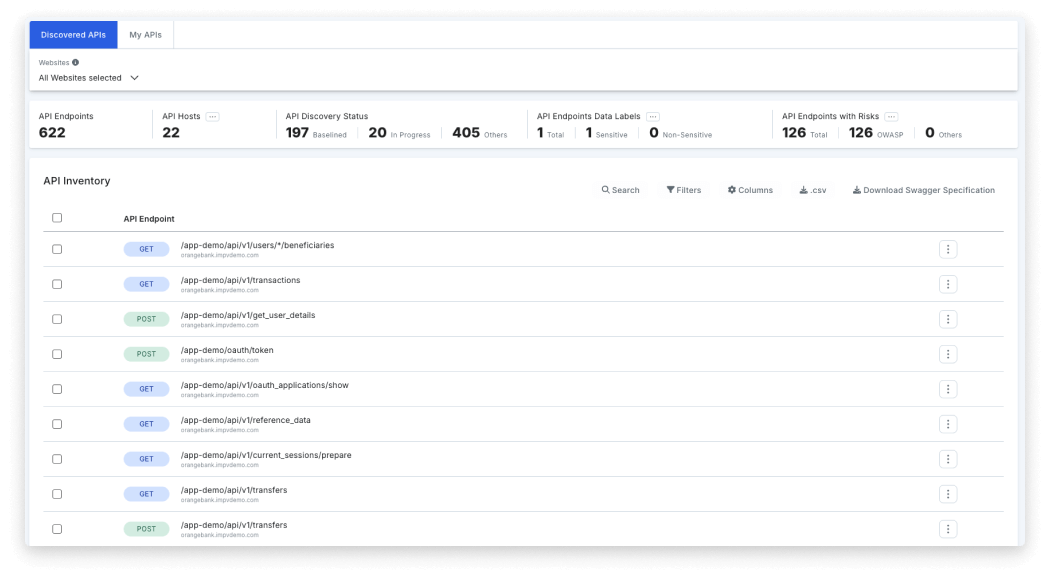
API Discovery and Classification
The ML-powered discovery engine finds APIs that traditional inventories miss:
- Shadow APIs — Endpoints deployed without security team awareness
- Zombie APIs — Deprecated APIs still accessible and potentially vulnerable
- Internal APIs — Service-to-service communication within microservices
- Third-party APIs — External integrations and partner endpoints
Each discovered API is automatically classified by risk level. The platform identifies sensitive data types (PII, payment data, credentials) flowing through each endpoint without retaining the raw data itself.
Schema Assessment and Enforcement
Imperva goes beyond simple schema validation:
- Security gap analysis — Checks API definitions (OpenAPI/Swagger) for missing authentication parameters, weak validation rules, and other security anti-patterns
- Runtime enforcement — Applies schema protection at runtime to block malformed requests
- Selective enforcement — Lets teams apply schema protection only to well-defined, stable APIs to reduce false positives during development cycles
API Detection and Response
The ADR capability targets business logic attacks that signature-based tools miss:
- Behavioral baselining — Learns normal API usage patterns per endpoint
- BOLA detection — Identifies when users attempt to access objects belonging to other users
- Anomaly correlation — ML-based incident correlation groups noisy events into prioritized incidents
- Automated policy suggestions — Recommends protection policies based on observed traffic patterns
Bot Protection Integration
Imperva API Security works alongside Imperva’s bot protection to defend against automated threats:
- Credential stuffing and account takeover attempts
- API scraping and data harvesting
- Business logic abuse from automated scripts
- Rate limit evasion through distributed attack patterns
Use Cases
Microservices environments — Discover and protect the full mesh of service-to-service APIs that perimeter tools cannot see.
Regulated industries — Automatic PII and payment data classification helps meet compliance requirements for GDPR, PCI DSS, and CCPA.
API-first businesses — Organizations exposing APIs to partners and customers need continuous discovery and schema enforcement as APIs evolve.
Bot-targeted APIs — APIs facing automated abuse benefit from the integrated bot protection and behavioral analysis.
Strengths & Limitations
Strengths:
- ML-based discovery catches shadow and zombie APIs that manual inventories miss
- Single platform removes the need to stitch together separate discovery, testing, and protection tools
- Native bot protection integration provides defense against automated API abuse
- Flexible deployment (cloud-managed, self-managed, agent-based, agentless) fits diverse architectures
- Part of a large cybersecurity platform with shared threat intelligence across WAF, RASP, and DDoS products
Limitations:
- Enterprise-focused product with enterprise pricing — less suited for small teams or startups
- Full platform benefits require broader Imperva/Thales product adoption
- Self-managed deployments require infrastructure investment and operational expertise
- ML-based detection needs a baseline traffic period before it can effectively identify anomalies
Getting Started
Imperva API Security alternatives
Imperva API Security competes in the enterprise API security market alongside several pure-play and platform-extension peers. The buying signal that usually decides the choice is whether you already operate behind an Imperva WAF, want a behavioral pure-play, or need a different edge story.
- Salt Security is the pure-play API behavioral runtime alternative. It runs continuous behavioral detection without a WAF dependency and is the canonical comparison for buyers who want behavioral runtime as a standalone discipline rather than a WAF extension.
- Akamai API Security, formerly Noname Security before the June 2024 acquisition, pairs the Noname engine with Akamai’s edge. It is the closest direct equivalent to Imperva on the WAF-platform-extension axis but lives on Akamai’s edge instead of Imperva/Thales infrastructure.
- 42Crunch takes the contract-first stance. Every check ties back to the OpenAPI spec and a runtime micro API firewall enforces the same contract in production, which is the right pick when the security model has to live and die with the spec.
- Wallarm bundles WAAP heritage with developer-focused API discovery and runtime detection. It overlaps with Imperva’s WAAP positioning but with a stronger appeal to product engineering teams owning the API estate end-to-end.
- Cequence leads with a unified API protection platform tuned for bot abuse and business-logic attacks, closer to Imperva on bot defense but sold as a dedicated API + bot product rather than a full WAF/CDN suite.
- Traceable AI, acquired by Harness in 2025, sits at the API security plus observability boundary and competes for distributed-tracing-heavy environments.
- For teams looking for open-source API security testing, Akto offers API discovery and testing with a community edition; for API-first security testing in CI/CD pipelines, APIsec covers the automated-pentest niche.
The signal that consistently favors Imperva is an existing Imperva WAF/Bot/RASP footprint, since the API Security module joins the same Cloud Application Security platform and inherits shared threat intelligence without integration work.
How to use Imperva API Security
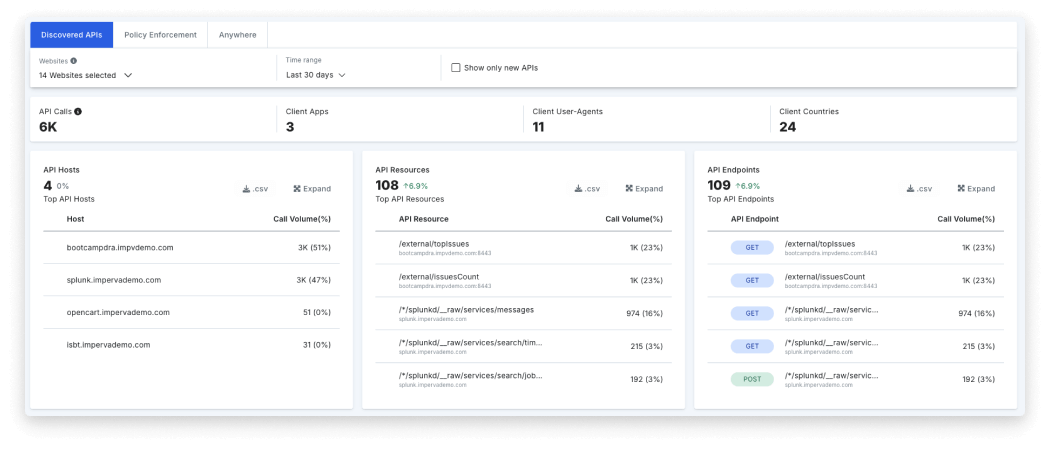
Imperva API Security follows a discover-classify-protect cycle that maps cleanly onto an existing Imperva or Thales deployment.
- Connect APIs through the Imperva Cloud WAF, the on-prem WAF Gateway, or a hybrid agent. Cloud-managed deployments inherit Imperva’s edge; self-managed deployments run inside the customer’s infrastructure for full data-residency control.
- Run discovery and inventory. The ML engine analyzes traffic across the connected entry points and surfaces shadow APIs, zombie APIs, third-party integrations, and the data classes (PII, payment data, credentials) flowing through each endpoint, usually within the first scan cycle.
- Configure protection rules and rate limits. Schema enforcement applies to stable APIs first, runtime BOLA detection runs against per-endpoint behavioral baselines, and bot protection inherits from Imperva Advanced Bot Protection without a second deployment.
- Tune behavioral analytics against your traffic baseline. The platform recommends policies based on observed patterns, and the API Detection and Response (ADR) module groups noisy events into prioritized incidents instead of raw alerts.
- Push findings into Splunk, Datadog, or the wider SIEM/SOAR stack so the security and platform teams act on the same incident view that drives Imperva’s blocking decisions.
Imperva API Security pricing
Imperva does not publish pricing for the API Security module. The product follows the standard Imperva enterprise commercial model — contact sales for a quote, with the API Security tier typically purchased alongside Imperva Cloud WAF or the broader Cloud Application Security suite rather than as a standalone line item.
Three signals consistently move the price: API call volume across the protected estate, the number of monitored entry points (Cloud WAF, hybrid agent, self-managed gateway), and whether bot protection, RASP, or DDoS modules are bundled. Existing Imperva WAF customers usually see lower incremental pricing for API Security than greenfield buyers because the module attaches to the existing contract rather than introducing a new platform agreement. Following the December 2023 Thales acquisition, procurement still runs through Imperva’s enterprise sales motion, with no public Thales-branded rate card replacing the Imperva pricing engagement.
For a broader overview of API security tools and how they compare, see the API security tools category page.