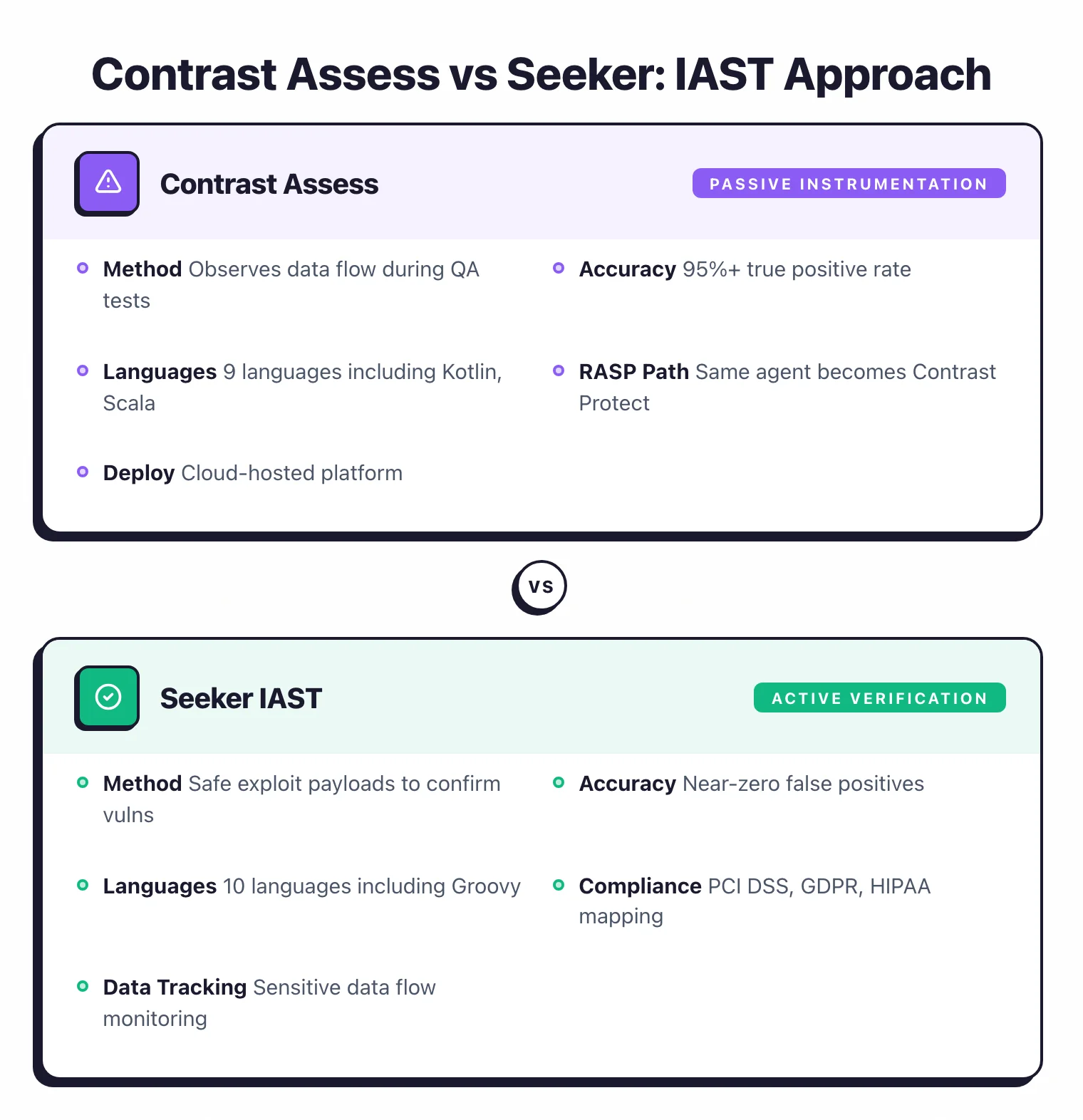
- Contrast Assess uses passive instrumentation with a 95%+ true positive rate; Seeker uses active verification with safe exploit payloads for near-zero false positives.
- Seeker supports 10 languages including Groovy; Contrast Assess covers 9 languages (Java, .NET, Node.js, Python, Go, Ruby, PHP, Kotlin, Scala).
- Seeker maps findings to PCI DSS, GDPR, HIPAA, OWASP Top 10, and CWE/SANS Top 25 with sensitive data flow tracking; Contrast covers OWASP Top 10 only.
- Contrast Community Edition reached end-of-life in June 2025; both tools are now commercial-only with no free tier.
- Contrast Assess shares its agent with Contrast Protect (RASP) for seamless testing-to-production defense; Seeker has no RASP equivalent in the Black Duck portfolio.
Contrast Assess and Seeker are the two leading commercial IAST tools that instrument running applications to detect vulnerabilities during testing.
Which Is Better: Contrast Assess or Seeker?
Contrast Assess and Seeker are both agent-based IAST tools that instrument running applications to find vulnerabilities from inside the runtime. They share the same fundamental approach but differ in how they validate findings, what they do beyond vulnerability detection, and how they fit into the broader security toolchain.
Contrast Assess is the better fit for development teams that want always-on security testing baked into their existing QA workflow. The passive instrumentation catches vulnerabilities as tests run, the upgrade path to Contrast Protect (RASP) means the same agent can move from testing to production defense.
Seeker is the stronger choice for organizations where compliance reporting drives security investment. The active verification approach confirms every finding is exploitable before it hits your backlog.
The sensitive data tracking maps how personal and financial information flows through your code, which is directly useful for PCI DSS, GDPR, and HIPAA audits.
What Are the Key Differences?
| Feature | Contrast Assess | Seeker |
|---|---|---|
| Vendor | Contrast Security | Black Duck (formerly Synopsys) |
| License | Commercial (CE discontinued June 2025) | Commercial |
| Core Languages | Java, .NET, Node.js, Python, Go, Ruby, PHP | Java, .NET, Node.js, Python, Go, Ruby, PHP |
| Additional Languages | Kotlin, Scala | Scala, Kotlin, Groovy |
| Detection Approach | Passive runtime instrumentation | Active verification with safe exploit payloads |
| Claimed Accuracy | 95%+ true positive rate (OWASP Top 10) | Near-zero false positives (verified findings only) |
| API Protocol Support | REST | REST, SOAP, GraphQL, gRPC |
| Sensitive Data Tracking | No | Yes (PCI DSS, GDPR, HIPAA) |
| Compliance Mapping | OWASP Top 10 | OWASP Top 10, CWE/SANS Top 25, PCI DSS, GDPR, HIPAA |
| RASP Upgrade Path | Yes (Contrast Protect, same agent) | No |
| SCA Integration | Contrast SCA (same platform) | Black Duck SCA |
| SAST Integration | Contrast Scan (same platform) | Coverity (same portfolio) |
| SIEM Integration | Limited | Splunk, IBM QRadar |
| Microservices Tracing | Architecture visualization | Cross-service request tracing |
| CI/CD Integration | CI/CD plugins, IDE integration | REST API for automation |
| Free Tier | None (CE discontinued June 2025) | None |
| Deployment | Agent-based, cloud-hosted platform | Agent-based, requires on-premises enterprise server |
| Platform Ecosystem | Contrast Platform (Assess + Scan + SCA + Protect) | Black Duck portfolio (Seeker + Coverity + Black Duck SCA) |
Contrast Assess vs Seeker: How Do They Compare?
Detection Approach: Passive Instrumentation vs Active Verification
This is the main technical difference between the two tools.
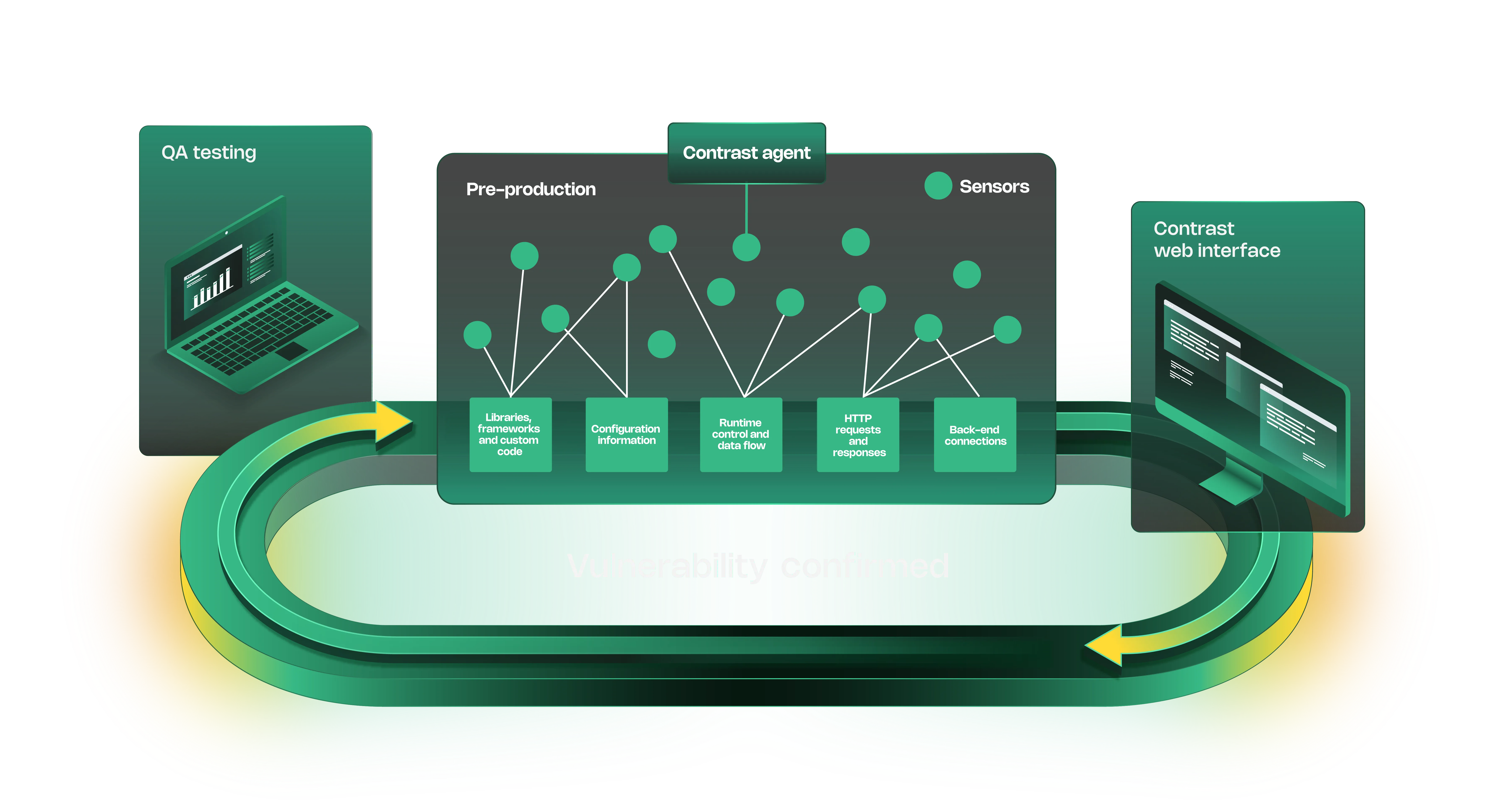
Contrast Assess uses passive instrumentation. Sensors embed into the application at startup and observe how data flows through the runtime during normal test execution.
When tainted input reaches a dangerous operation — a SQL query, an HTML output, a file path — without proper sanitization, Contrast flags the vulnerability with the exact code location and data flow trace. The sensors watch continuously without modifying application behavior.
Contrast reports a 95%+ true positive rate for OWASP Top 10 vulnerabilities using this approach.
Seeker adds an active verification step on top of runtime observation. When Seeker detects a potential vulnerability, it generates safe exploit payloads and sends them through the application to confirm the issue is genuinely exploitable.
If the payload does not reach the vulnerable sink or gets blocked by existing defenses, the finding is dropped. Only verified vulnerabilities make it into the final report.
This patented approach means Seeker’s output is a list of confirmed, exploitable issues rather than probable vulnerabilities.
The practical difference shows up in triage. Contrast Assess reports more findings because passive observation catches everything that looks vulnerable, even if some issues are mitigated by environmental factors.
Seeker reports fewer findings but each one has been confirmed exploitable. Teams that are drowning in triage backlogs will appreciate Seeker’s approach.
Teams that want maximum visibility into potential risk, even if some findings need manual validation, get more from Contrast.
Language and Protocol Coverage
Seeker supports Java, .NET, Node.js, Go, Python, Ruby, PHP, and JVM languages including Scala, Kotlin, and Groovy. That adds up to roughly ten languages, which matters for organizations running polyglot environments.
Contrast Assess now supports Java, .NET, Node.js, Python, Go, Ruby, PHP, Kotlin, and Scala — nine languages with broad framework coverage within each. The remaining gap is Groovy, which only Seeker covers.
The language difference between these two tools has narrowed considerably.
On API protocols, Seeker supports REST, SOAP, GraphQL, and gRPC. It also discovers API endpoints exercised during testing, which helps maintain accurate API inventories.
Contrast Assess handles REST APIs well but does not list the same breadth of protocol support.
Compliance and Sensitive Data Tracking

Seeker has a meaningful advantage for compliance-driven organizations. The sensitive data tracking feature monitors how personal information, credentials, and financial data flow through your application — where it enters, which code processes it, and where it ends up.
This produces audit-ready documentation for PCI DSS (cardholder data flows), GDPR (personal data processing), and HIPAA (protected health information handling).
Seeker also maps vulnerability findings to compliance frameworks: OWASP Top 10, CWE/SANS Top 25, PCI DSS, GDPR, and HIPAA. Compliance teams can run a report showing exactly which regulatory requirements are affected by detected vulnerabilities.
That is directly useful during audits and saves the manual work of mapping security findings to regulatory controls.
Contrast Assess reports against OWASP Top 10 and standard vulnerability classifications. The Contrast Platform provides risk-level dashboards and trend reporting.
However, Contrast does not offer the same dedicated sensitive data tracking or the breadth of regulatory compliance mapping that Seeker provides.
If your security program is driven by PCI DSS, GDPR, or HIPAA requirements, Seeker addresses those needs more directly.
Platform Ecosystem and Upgrade Paths
Both tools sit within larger security platforms, but the ecosystems are structured differently.
Contrast Assess is part of the Contrast Platform, which includes Contrast Scan (SAST), Contrast SCA (software composition analysis), and Contrast Protect (RASP). The key selling point is the shared agent architecture.
The same agent that runs Assess during testing can run Protect in production to block attacks at runtime. You do not need to deploy a separate tool or re-instrument your application.
For teams that want to move from finding vulnerabilities to blocking exploits, this continuity is a meaningful advantage.
Seeker sits within the Black Duck portfolio alongside Coverity (SAST) and Black Duck SCA.
Following the October 2024 acquisition by Clearlake Capital and Francisco Partners, these tools now operate as the independent Black Duck Software company.
Seeker integrates with Black Duck SCA to correlate IAST findings with open-source vulnerabilities. It also feeds data into Splunk and IBM QRadar for centralized security monitoring.
However, there is no RASP equivalent in the Black Duck portfolio — Seeker is focused on testing, not production defense.
The ecosystem choice often depends on what you already run. If you use Contrast Scan or Contrast SCA, adding Assess keeps everything in one platform.
If you use Coverity or Black Duck SCA, Seeker slots in alongside your existing tools.
Deployment and CI/CD Integration
The deployment models differ in a meaningful way. Contrast Assess uses a cloud-hosted platform.
You deploy agents to your application, and findings report back to Contrast’s cloud. Setup is relatively quick — Contrast claims you can instrument an application within an hour.
The platform provides IDE integration so developers see findings directly in Visual Studio and other editors.
Seeker requires a separate on-premises enterprise server (Windows or Linux) before you can deploy agents. This adds infrastructure overhead and setup time compared to Contrast’s cloud model.
For organizations that require on-premises control over security data, this is actually a benefit. For teams that want fast deployment without managing server infrastructure, it is a hurdle.
For CI/CD, Contrast offers plugins and an API for pipeline integration. Seeker provides a REST API for automation that can be wired into any CI/CD system.
Neither tool has the same level of out-of-the-box pipeline tooling (official GitHub Actions, Docker images) that you see with SAST or DAST tools.
In both cases, integration requires some configuration work with the vendor’s API.
When Should You Choose Contrast Assess?
Choose Contrast Assess if:
- You want always-on IAST that runs passively during your existing tests with no separate scan phase
- You need a path from vulnerability detection (Assess) to runtime attack blocking (Protect) using the same agent
- Your stack uses Java, .NET, Node.js, Python, Go, Ruby, PHP, Kotlin, or Scala
- Cloud-hosted deployment with fast setup time is preferred over managing on-premises infrastructure
- You already use or plan to use Contrast Scan (SAST) or Contrast SCA for a unified platform
When Should You Choose Seeker?
Choose Seeker if:
- Compliance reporting for PCI DSS, GDPR, or HIPAA is a primary driver for your security program
- Active verification that confirms exploitability before reporting is worth more to you than maximum finding volume
- Your stack includes Groovy, which Contrast does not support
- Sensitive data tracking — knowing exactly where personal and financial data flows through your code — is a requirement
- You need SIEM integration with Splunk or IBM QRadar for centralized vulnerability monitoring
- You already use Black Duck SCA or Coverity and want correlated findings across IAST, SCA, and SAST
Both tools represent the top tier of commercial IAST. The choice usually comes down to whether your priority is developer workflow integration and platform breadth (Contrast) or compliance depth and verified-only findings (Seeker).
See more AppSec Santa tool reviews in our IAST tools category.
Frequently Asked Questions
Is Contrast Assess or Seeker IAST better for reducing false positives?
Does Contrast Assess or Seeker have better language support?
Is there a free version of Contrast Assess or Seeker?
Which IAST tool is better for compliance reporting?
Can I use Contrast Assess and Seeker together?

Founder, AppSec Santa
Years in application security. Reviews and compares 215 AppSec tools across 11 categories to help teams pick the right solution. More about me →