- Wiz is a greenfield CNAPP built from scratch in 2020 around an agentless Security Graph; Prisma Cloud is an acquisition stack assembled by Palo Alto Networks from Evident.io, RedLock, PureSec, Twistlock, and Bridgecrew between 2018 and 2021.
- Wiz scans cloud environments agentlessly by default and adds optional eBPF-based runtime via Wiz Defend; Prisma Cloud mixes agentless scanning with the Twistlock-derived Defender agent for container, host, and serverless runtime protection.
- Prisma Cloud's code security module is built on open-source Checkov (from the Bridgecrew acquisition), scanning Terraform, CloudFormation, Kubernetes, Helm, and ARM; Wiz Code ships native IaC and secrets scanning tied into the same Security Graph used by Wiz Cloud.
- Neither vendor publishes list pricing — both require a sales quote, with Prisma Cloud sold in credit-based modules and Wiz typically priced per workload.
- Prisma Cloud is being merged into Cortex Cloud (announced February 2025) as Palo Alto Networks' unified SOC-plus-cloud platform; Google completed its $32B acquisition of Wiz in March 2026.
Which Is Better: Wiz or Prisma Cloud?
Both Wiz and Prisma Cloud are top-tier Cloud Native Application Protection Platforms (CNAPPs). They cover the same broad surface — CSPM, CWPP, CIEM, DSPM, and code security — but they arrive there from opposite directions.
Wiz is a purpose-built CNAPP that started from a blank sheet in 2020, anchored on an agentless Security Graph. Prisma Cloud is a Palo Alto Networks platform assembled from a series of acquisitions between 2018 and 2021, now being folded into Cortex Cloud.
This page compares the two head-to-head. For a broader list, see the IaC security tools category and the related comparison Wiz vs Orca Security .
In my experience evaluating CNAPPs, Wiz tends to win on time-to-value and graph-based prioritization, especially for greenfield or multi-cloud environments. Prisma Cloud tends to win when you already live inside the Palo Alto Networks ecosystem and want cloud signals correlated with network and endpoint telemetry.
Architecture and Origin Story
Key Insight
The two platforms look similar on a feature matrix but come from very different engineering histories — one built as a single graph from day one, the other assembled from five separate acquisitions over four years.
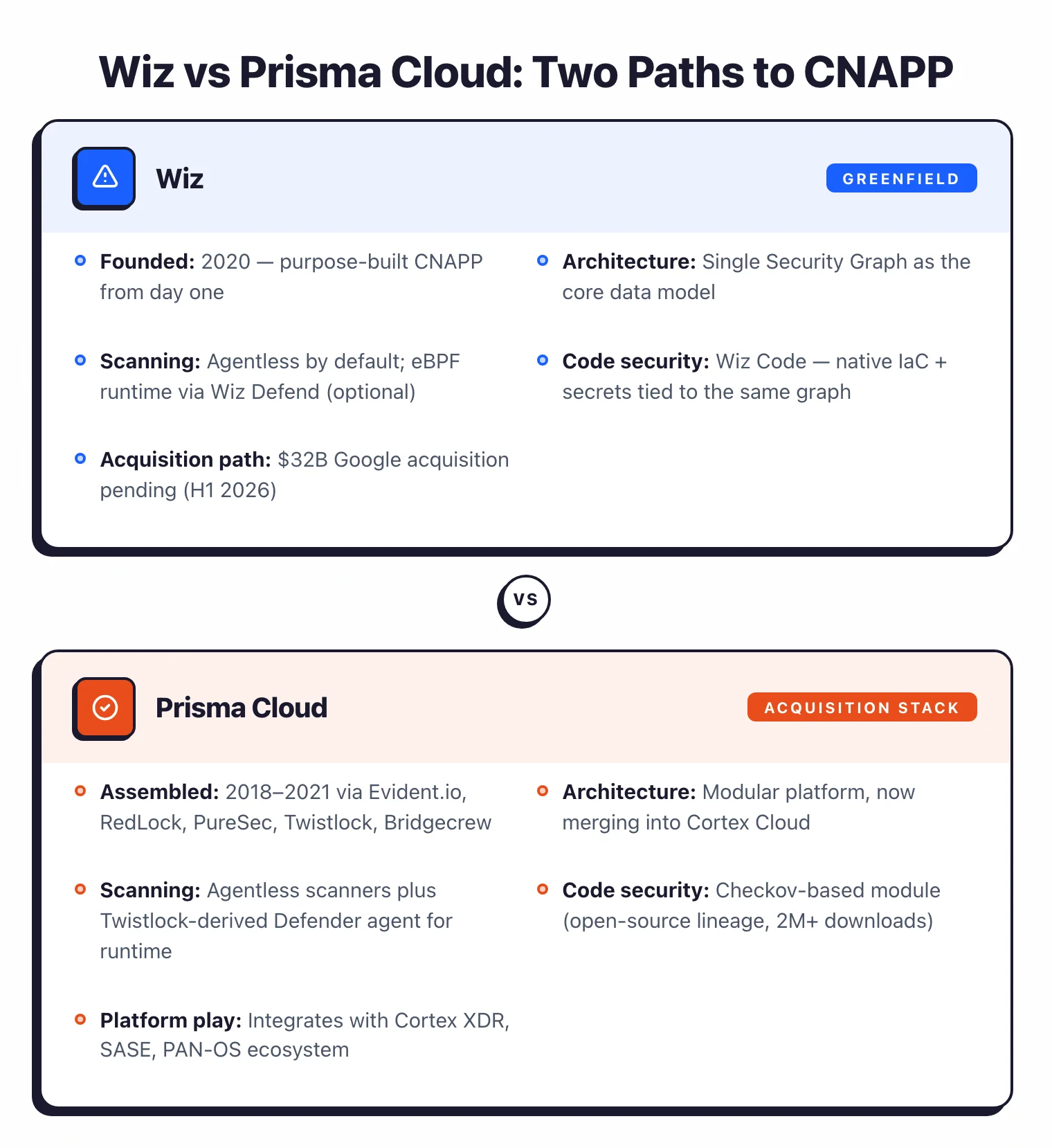
Prisma Cloud is an acquisition stack. Palo Alto Networks bought Evident.io (CSPM) in March 2018 , then RedLock (cloud threat defense) in October 2018 , then Twistlock (container runtime) and PureSec (serverless) in 2019 , and finally Bridgecrew (Checkov-based IaC scanning) in February 2021 .
Each of those products became a module inside Prisma Cloud, and integration work has been ongoing ever since. That history is visible in how agents, data models, and consoles align across modules.
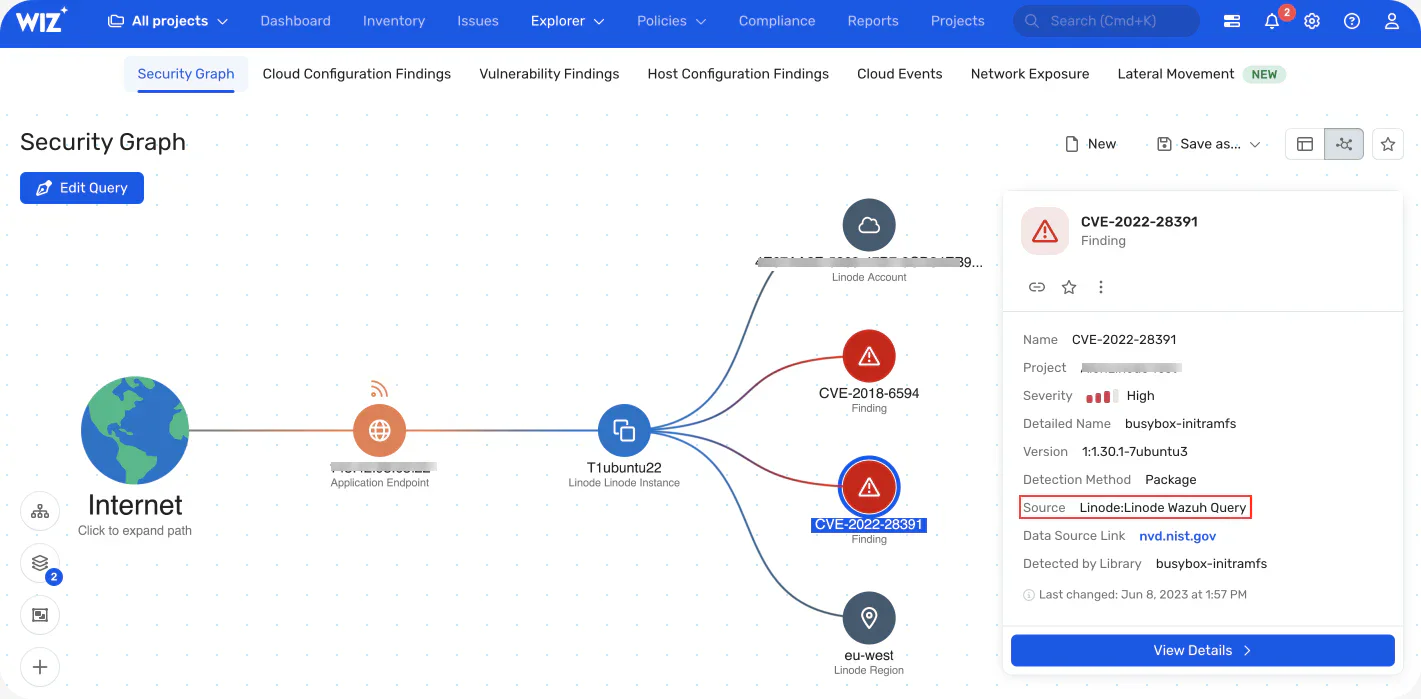
Wiz was founded in 2020 by former Microsoft Cloud Security Group engineers and built as a single platform from day one. The core data model is the Security Graph — a normalized view of cloud resources, identities, network paths, vulnerabilities, secrets, and data classifications linked together so attack paths can be computed directly.
Both vendors now describe themselves as CNAPPs. The difference is that Prisma Cloud’s CNAPP is a marketing umbrella over several once-separate products, while Wiz’s CNAPP is one product with one graph underneath.
How Each Scans Cloud Environments
Scanning strategy is the clearest technical divide between these two tools.
Wiz uses an agentless, snapshot-based approach . It attaches to cloud account APIs, takes read-only snapshots of workloads (VMs, containers, serverless functions), analyzes them out-of-band, and feeds the results into the Security Graph. A full risk profile is typically available within 24 hours of connecting an account.
For deeper runtime detection, Wiz Defend adds an eBPF-based sensor, but it is optional and not the primary scanning path.
Prisma Cloud supports agentless scanning for posture, vulnerability assessment, and data discovery. But its runtime story for containers, hosts, and serverless functions still leans heavily on the Twistlock-derived Defender agent , which provides process monitoring, drift detection, WAAS-style web protection, and compliance enforcement at runtime.
The practical consequence shows up in deployment timelines. Turning on Wiz is an API-key exercise; turning on Prisma Cloud Compute at scale usually involves rolling Defender agents to every node or serverless function you want protected at runtime.
Note: Neither approach is wrong. Agents see syscalls and process trees that snapshots miss, while snapshots avoid the operational cost of running security software inside every workload.
Coverage Compared
Both tools cover the five canonical CNAPP pillars, with different strengths in each.
| Capability | Wiz | Prisma Cloud |
|---|---|---|
| License | Commercial | Commercial |
| Deployment model | Agentless by default; optional eBPF via Wiz Defend | Agentless scanners plus Twistlock-derived Defender agent |
| Data model | Security Graph (resources, identities, paths, risks) | Multi-module platform, trending toward Cortex Cloud |
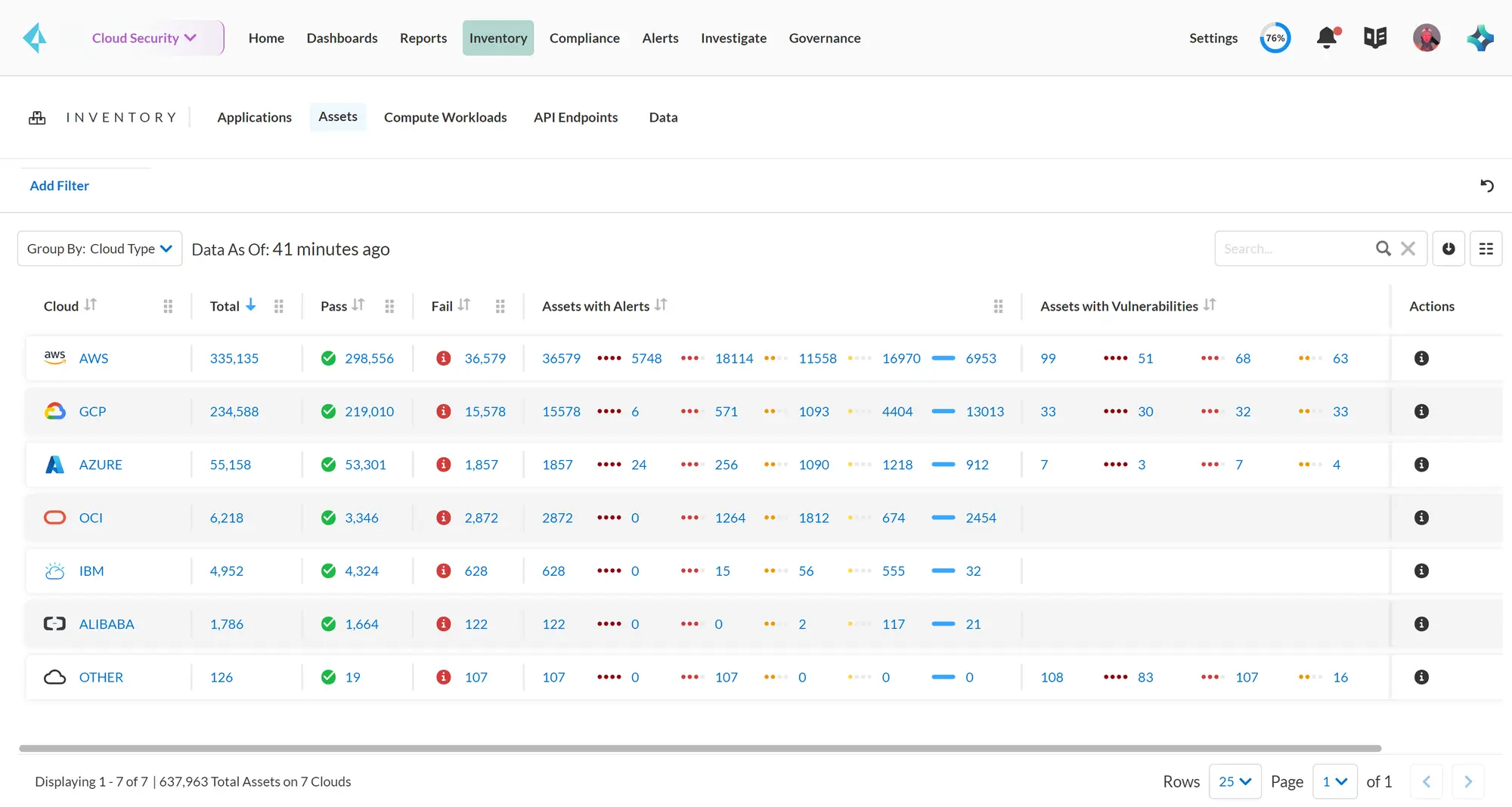
| Clouds | AWS, Azure, GCP, OCI, Alibaba, VMware vSphere, Kubernetes | AWS, Azure, GCP, OCI, Alibaba, IBM Cloud |
| CSPM | Yes, built-in | Yes, originally Evident.io + RedLock |
| CWPP | Yes, agentless (vulns, malware, secrets) | Yes, Twistlock-derived (containers, hosts, serverless) |
| CIEM | Yes | Yes |
| DSPM | Yes, native | Yes, native |
| Code / IaC | Wiz Code (native IaC, secrets, containers) | Code security module built on Checkov |
| Runtime detection | Wiz Defend (eBPF) | Defender agent + WAAS |
| Compliance frameworks | CIS, PCI, HIPAA, SOC 2, NIST, ISO | 100+ frameworks including CIS, PCI, HIPAA, GDPR, SOC 2, NIST 800-53 |
| Integrations | 200+ via WIN partner program | Palo Alto platform, Cortex XDR/CDR, third parties |
| Notable context | Now part of Google Cloud (deal closed March 2026) | Merging into Cortex Cloud as of Q3 FY25 (announced Feb 2025) |
Both platforms support the same big-five hyperscalers. Prisma Cloud adds IBM Cloud, which matters for a small but real set of regulated workloads. Wiz adds Alibaba and VMware vSphere as first-class citizens for customers with APAC or hybrid footprints.
Compliance-framework counts are marketing numbers on both sides and should be validated against your own audit scope. The real question is how cleanly the tool maps your production environment to the frameworks you actually have to report against.
Deployment Footprint
Deployment is where the architectural difference becomes operational.
A typical Wiz rollout: connect each cloud account via a CloudFormation, Terraform, or native role-based template, wait for the first scan to populate the Security Graph, then tune policies and attack-path alerts. Runtime sensors for Wiz Defend are added later if needed.
A typical Prisma Cloud rollout involves enabling the relevant modules (CSPM, CWPP, CIEM, DSPM, code, network) on licensed credits, pointing cloud accounts at the tenant, and then — for runtime — orchestrating Defender agents through DaemonSets, host packages, or serverless layers. Teams that already run Palo Alto agents elsewhere are comfortable with this; teams that do not often cite it as the biggest integration cost.
Both Wiz Code and Prisma Cloud’s code security module plug into CI pipelines and version control. Prisma Cloud leans on Checkov’s existing open-source footprint, which many platform teams already use locally. Wiz Code unifies results with the same Security Graph that ingests cloud runtime data.
Neither tool is plug-and-play at enterprise scale. Both require identity integration, policy tuning, and ownership mapping before they stop generating noise.
Pricing Reality
Neither Wiz nor Prisma Cloud publishes pricing on its website. Both require a sales conversation, and both adjust pricing by cloud footprint, module mix, and negotiating leverage.
From public RFPs and procurement disclosures, Prisma Cloud is typically sold in a credit-based model where each module (CSPM, CWPP, CIEM, DSPM, code, network) consumes credits per workload per month. Wiz is typically sold per workload across connected cloud accounts, with add-ons for Wiz Code and Wiz Defend.
Any specific dollar figure you see in a comparison article is anecdotal until you have a quote scoped to your own environment. Per my content rules , I do not publish vendor pricing when the vendor itself does not.
What you can reliably compare is the shape of a deal, not the absolute number. Both vendors price aggressively against each other at the enterprise tier, and both offer multi-year and platform-bundle discounts.
Which to Pick
I recommend Wiz when agentless time-to-value, graph-based prioritization, or a single pane of glass across AWS, Azure, GCP, OCI, and Alibaba is the deciding factor. It also tends to win when the buyer wants a focused CNAPP rather than a platform play tied to a broader SOC vendor.
I recommend Prisma Cloud when you are already standardized on Palo Alto Networks for firewall, SASE, or XDR and want cloud signals correlated with that telemetry in Cortex Cloud. It also wins for teams that already run Checkov locally and want a managed, policy-governed version of the same engine with enterprise SLA backing.
For a broader view, browse the IaC security tools and ASPM tools categories, or compare against Wiz vs Orca Security .
Both tools solve the same problem from different starting points. Wiz bets that a single graph built from day one beats a best-of-breed stack stitched together. Prisma Cloud bets that integration inside a bigger security platform beats a standalone CNAPP — a bet that now extends to the Cortex data lake and Google Cloud’s infrastructure , respectively.
Frequently Asked Questions
Is Wiz or Prisma Cloud fully agentless?
Which platform is better for Palo Alto Networks customers?
How does the code security story compare?
Do Wiz and Prisma Cloud publish pricing?
What about Cortex Cloud — does that change the comparison?

Founder, AppSec Santa
Years in application security. Reviews and compares 215 AppSec tools across 12 categories to help teams pick the right solution. More about me →
