Wiz Alternatives
Evaluating alternatives to Wiz? Compare top CNAPP and cloud security competitors including Orca Security, Prisma Cloud, Lacework, Aqua Security, and Sysdig Secure.
- Wiz's agentless scanning covers 100% of your cloud environment within minutes, but its pricing scales with cloud workload spend and can become significant for large environments.
- Orca Security uses the same agentless SideScanning approach as Wiz and is often positioned as a direct price-competitive alternative for AWS, Azure, and GCP deployments.
- Prisma Cloud from Palo Alto Networks offers the broadest feature set in the CNAPP market — code security, cloud posture, workload protection, and identity — though complexity scales with scope.
- Lacework uses behavioral ML to surface anomalies in cloud activity, which catches configuration drift and unusual runtime behavior that signature-based tools miss.
- Aqua Security covers the full container and Kubernetes lifecycle from image scanning through runtime protection, with agent-based depth that agentless-only tools cannot match.
The best Wiz alternatives in 2026 are Orca Security, Prisma Cloud, Lacework, Aqua Security, and Sysdig Secure — each offering distinct strengths in cloud posture management, container security, or runtime protection.
Why Look for Wiz Alternatives?
Wiz is one of the fastest-growing security companies in history. Its agentless deployment model, security graph visualization , and ability to show cross-cloud attack paths changed how the market thinks about CNAPP.
For cloud security teams that previously needed weeks of agent rollout, Wiz delivers value within hours of connecting a cloud account.
The reality is that Wiz is not the right fit for every organization. The most common trigger for evaluating alternatives is cost.
Wiz’s pricing is based on cloud workload spend or seat count depending on the contract structure. For organizations running significant cloud infrastructure, the numbers can become material quickly.
Procurement teams entering first negotiations often emerge looking for leverage — or an alternative that delivers comparable posture management at lower cost.
The second consideration is scope. Wiz is an agentless platform. Agentless scanning sees cloud resource configurations, stored data, installed packages, and cross-account relationships.
It does not see live process execution, syscall-level activity, or network connections at the kernel level. For runtime security requirements — detecting an active container escape, a cryptominer spawning a child process, or lateral movement inside a compromised pod — agentless tools have fundamental limits.
Teams with strong container and Kubernetes security requirements often find they need an agent-based tool like Aqua or Sysdig alongside Wiz, or instead of it.
A third factor is platform investment. Organizations already running Palo Alto Networks firewalls have natural pull toward Prisma Cloud, which integrates deeply with that ecosystem. Similarly, teams embedded in the AWS marketplace may evaluate a different set of vendors than those running multi-cloud.
Top Wiz Alternatives
1. Orca Security
Orca Security is the most direct Wiz alternative in the market. Both tools use agentless cloud scanning, both provide a security graph for visualizing attack paths, and both compete in the same CNAPP deals.
Orca uses its own SideScanning technology , which connects to cloud accounts through read-only APIs and cloud snapshots rather than deploying agents. Coverage reaches cloud misconfigurations, vulnerabilities in workloads, exposed sensitive data, and identity risks across AWS, Azure, and GCP.
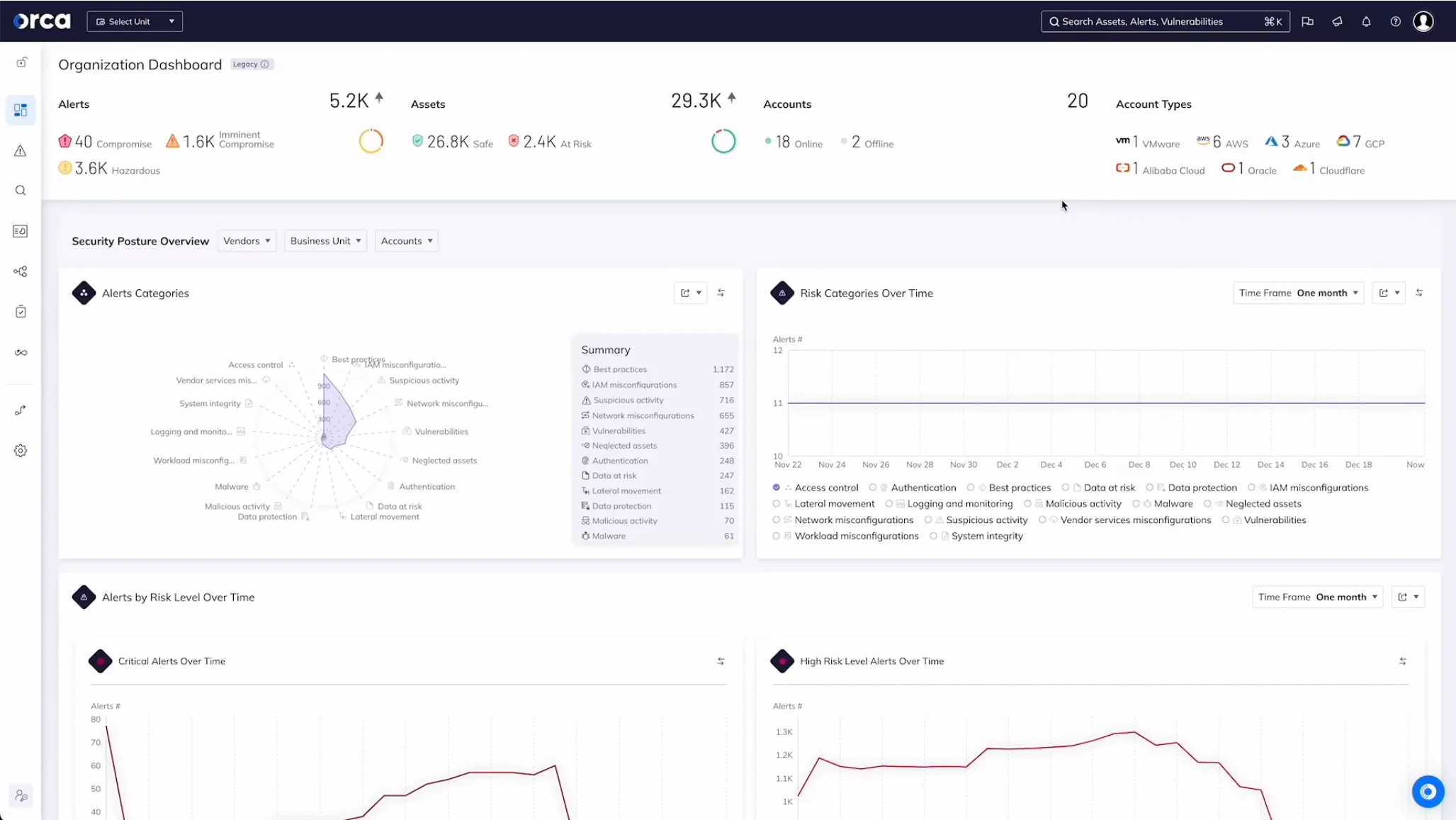
Where Orca differentiates is risk prioritization. Its Attack Path Analysis maps how a combination of vulnerabilities, identities, and network exposures could be chained together to reach a critical asset. This is similar to Wiz’s security graph but implemented with different scoring and visualization choices that some teams prefer.
Orca is consistently positioned as price-competitive with Wiz. For organizations entering procurement, having Orca as a credible alternative strengthens negotiating position regardless of which tool ultimately wins.
For a detailed comparison, see the Wiz vs Orca Security analysis.
Best for: Teams wanting agentless CNAPP coverage as a direct Wiz alternative. License: Commercial Key difference: SideScanning approach with competitive CNAPP feature set. Often positioned as the primary price-competitive Wiz alternative.
2. Prisma Cloud
Prisma Cloud from Palo Alto Networks is the broadest CNAPP platform in the market in terms of feature scope. It spans code security (IaC scanning, SCA, secrets), cloud security posture management, workload runtime protection , network security, and identity threat detection.
No single vendor covers as many of the CNAPP subcategories in a single product license.
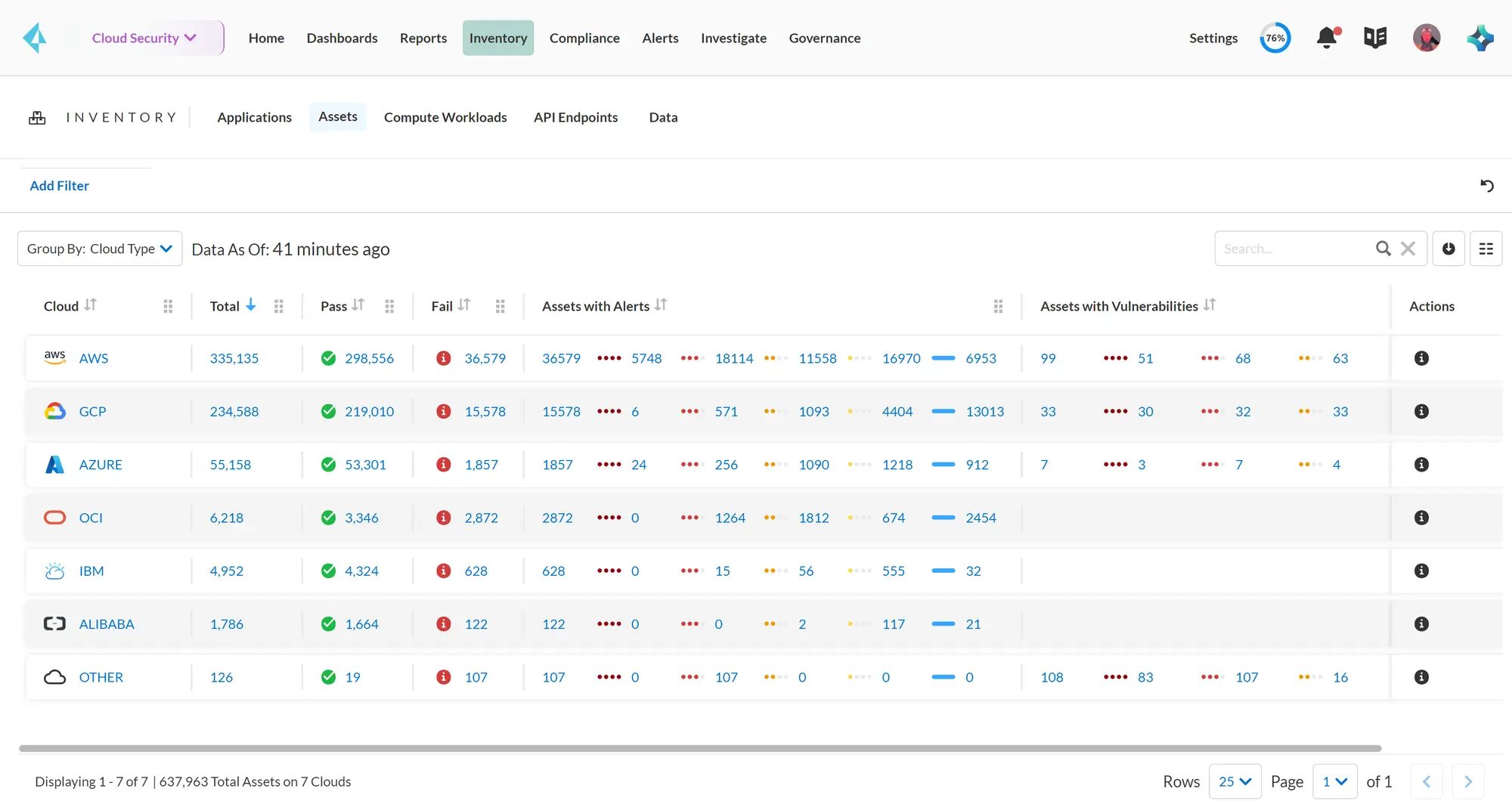
The tradeoff for breadth is complexity. Prisma Cloud is not a tool you deploy and get value from in an afternoon. Configuration, policy tuning, and integration work take time.
Teams that successfully operationalize Prisma Cloud typically have a dedicated cloud security engineering function. The payoff for that investment is deep integration across the Palo Alto Networks ecosystem, including Cortex XSOAR for automation and Next-Generation Firewalls for network context.
For a detailed comparison, see the Wiz vs Prisma Cloud analysis.
For IaC security tools teams already running Palo Alto Networks infrastructure, Prisma Cloud is worth serious evaluation. For teams without that ecosystem investment, the complexity overhead may outweigh the breadth advantage.
Best for: Palo Alto Networks customers wanting an integrated cloud security platform. License: Commercial Key difference: Broadest feature set in the CNAPP market — code, cloud, workload, network, identity — with deep Palo Alto Networks integration.
3. Lacework
Lacework takes a behavioral ML approach to cloud security that differs from Wiz’s posture-focused model. Where Wiz shows you what your cloud environment looks like at a point in time, Lacework monitors how it behaves over time.
Its machine learning engine builds a baseline of normal activity for each environment — API calls, user behaviors, network flows, process execution patterns — and surfaces anomalies that deviate from that baseline.
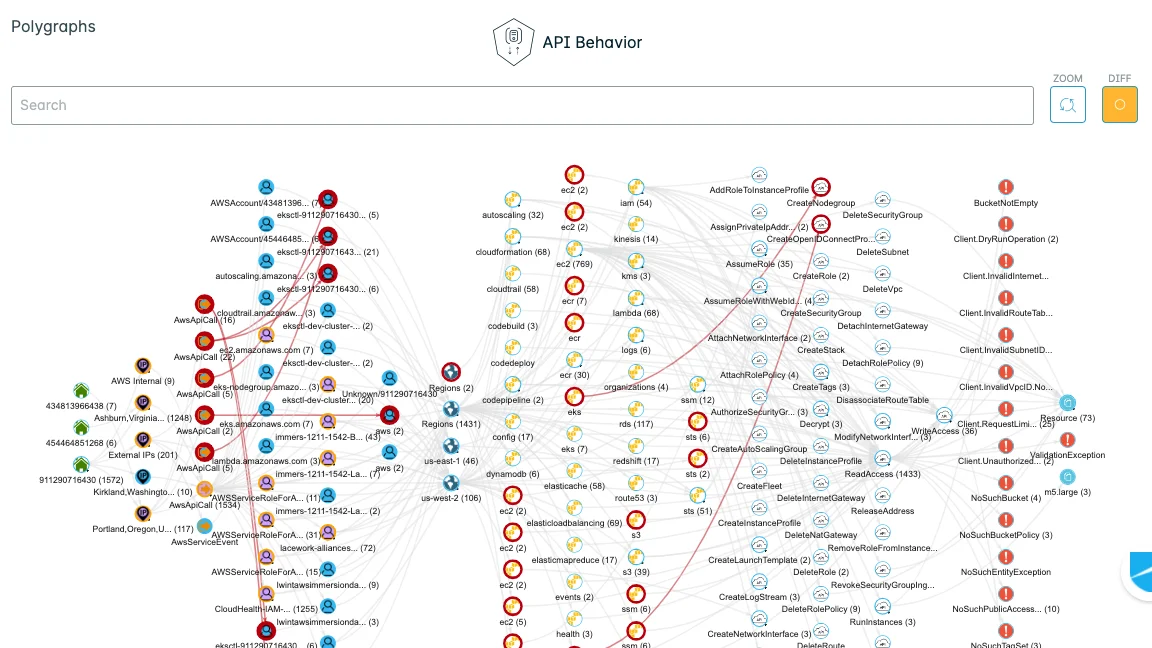
This catches configuration drift, insider threats, and novel attack techniques that rule-based systems miss. A legitimate service calling an unusual AWS API for the first time, or an EC2 instance communicating with a new external IP range, surfaces as an anomaly even without a matching CVE or misconfiguration signature.
Lacework also provides CSPM for cloud configuration posture and vulnerability assessment for container workloads. The platform covers AWS, Azure, GCP, and Kubernetes.
The behavioral approach requires time to build accurate baselines, which means value accumulates over weeks rather than hours. For teams that need immediate posture visibility, this ramp-up period can be frustrating.
But for organizations with mature cloud security programs that have solved basic posture hygiene and need to detect active threats, Lacework’s anomaly detection fills a gap that posture-only tools like Wiz do not address.
Best for: Organizations with mature cloud security posture that need behavioral anomaly detection for active threats. License: Commercial Key difference: ML-based behavioral analysis detects anomalies over time. Catches drift and novel threats beyond configuration posture snapshots.
4. Aqua Security
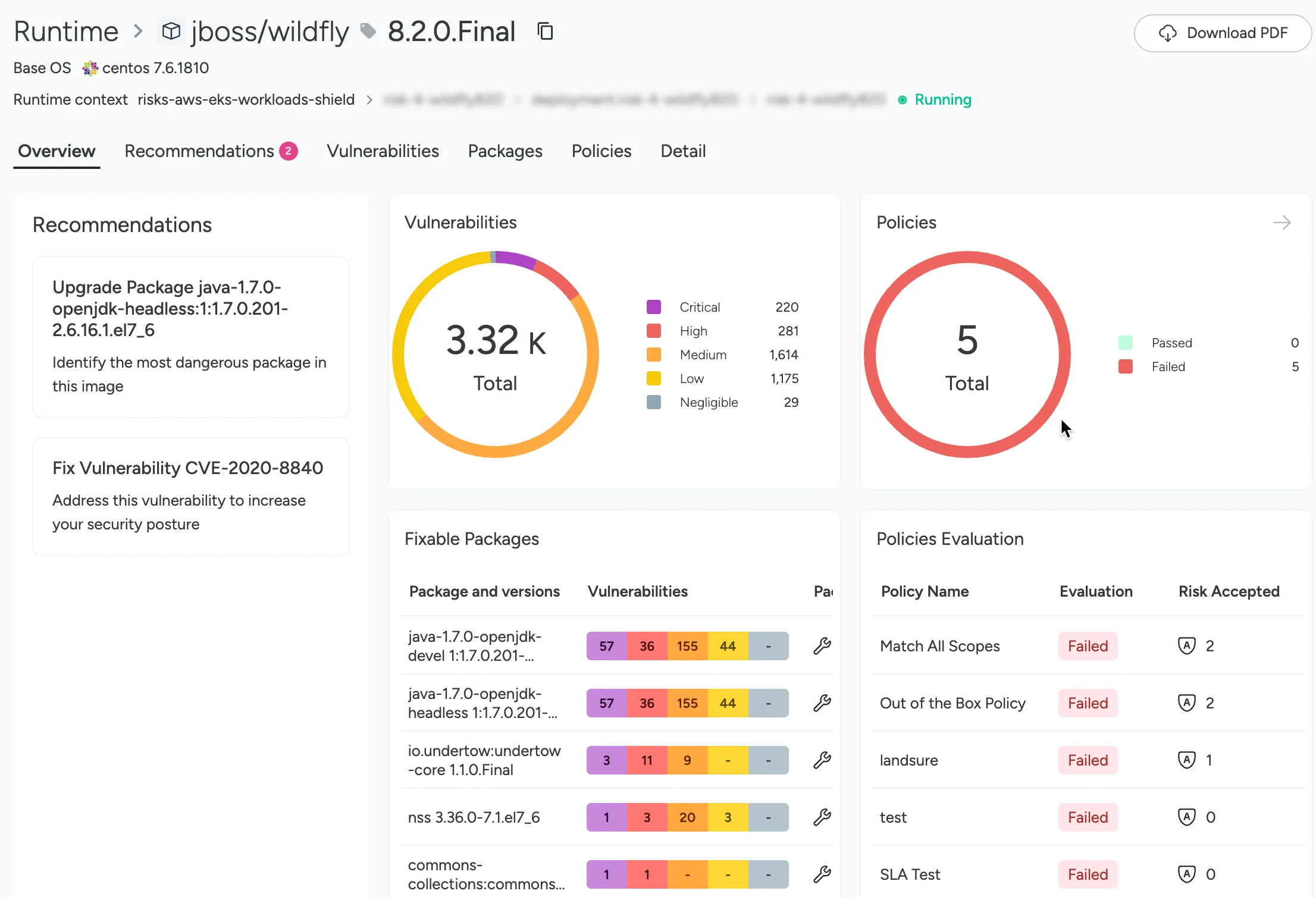
Aqua Security focuses on containers, Kubernetes, and the software supply chain. It is the strongest option on this list for teams whose primary concern is workload and container runtime security rather than broad cloud posture.
Aqua’s approach is agent-based. A lightweight agent — deployed as a DaemonSet in Kubernetes or as a sidecar — instruments container activity at the kernel level using eBPF. This provides runtime enforcement capabilities that no agentless tool can match: blocking a container escape as it happens, preventing a malicious process from spawning, or terminating network connections that violate policy.
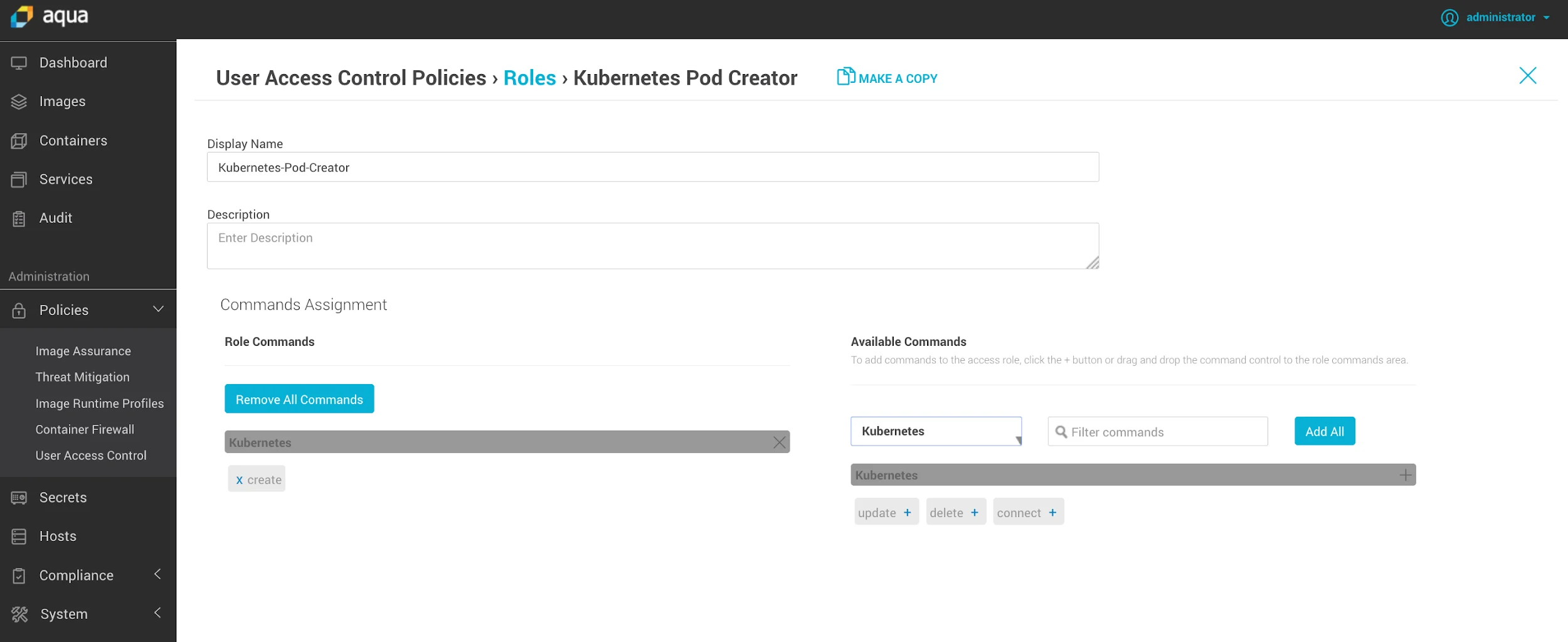
The platform also covers the development lifecycle, scanning container images in CI/CD pipelines, enforcing SBOM policies, and detecting secrets in image layers.
Aqua’s Supply Chain Security module tracks artifacts from source code through build to registry, providing attestation and provenance data that satisfies software supply chain security requirements.
For teams whose cloud security risk is concentrated in Kubernetes workloads rather than cloud account misconfigurations, Aqua’s depth justifies the agent deployment overhead.
Best for: Teams running container-heavy infrastructure that need runtime enforcement in Kubernetes. License: Commercial Key difference: Agent-based runtime enforcement at the kernel level. Full container lifecycle security from CI/CD through production.
5. Sysdig Secure
Sysdig Secure is built on the open-source Falco runtime security project, which Sysdig created and maintains. It uses eBPF-based instrumentation to capture syscall-level activity across every container and host in your Kubernetes environment.
The runtime detection layer maps findings to MITRE ATT&CK tactics , giving security teams actionable context for triaging alerts. Unlike agentless tools that see snapshots, Sysdig sees live process execution, file system access, network connections, and container escapes as they happen.
Sysdig also includes CSPM, vulnerability management, and cloud configuration scanning in a unified platform. But the runtime security capability is what distinguishes it from most competitors.
For organizations with compliance requirements that mandate runtime protection (PCI-DSS, FedRAMP, SOC 2), Sysdig’s depth in that dimension is a practical necessity. Agentless platforms like Wiz document what was configured, not what is actively executing.
The operational model requires managing a Falco-based agent across your cluster nodes. This is manageable with Kubernetes DaemonSet deployment, but it is a different commitment than Wiz’s API-only approach.
Best for: Teams with runtime security requirements in Kubernetes who need MITRE-mapped threat detection. License: Commercial (Falco is open-source) Key difference: eBPF-based runtime enforcement with MITRE ATT&CK mapping. Detects active threats in real time rather than configuration snapshots.
Feature Comparison
| Feature | Wiz | Orca Security | Prisma Cloud | Lacework | Aqua Security | Sysdig Secure |
|---|---|---|---|---|---|---|
| License | Commercial | Commercial | Commercial | Commercial | Commercial | Commercial |
| Deployment | Agentless | Agentless | Agentless + agent | Agent + agentless | Agent-based | Agent (eBPF) |
| CSPM | Yes | Yes | Yes | Yes | Yes | Yes |
| Vulnerability scanning | Yes | Yes | Yes | Yes | Yes | Yes |
| Runtime security | Limited | Limited | Yes | Behavioral | Yes | Core feature |
| Container/Kubernetes | Yes | Yes | Yes | Yes | Core feature | Core feature |
| IaC scanning | Yes | Yes | Yes | No | Limited | No |
| Identity security (CIEM) | Yes | Yes | Yes | Yes | Limited | No |
| Behavioral ML | No | No | No | Core feature | No | No |
| Supply chain security | No | No | Yes | No | Yes | No |
| Cloud providers | AWS, Azure, GCP | AWS, Azure, GCP | AWS, Azure, GCP | AWS, Azure, GCP | Multi-cloud | Multi-cloud |
When to Stay with Wiz
Wiz remains the right choice in several scenarios:
- Speed of deployment matters. No other platform delivers full cloud account coverage as quickly as Wiz. If your priority is going from zero visibility to full posture coverage in hours rather than weeks, Wiz’s agentless model is unmatched.
- Your team needs a security graph. Wiz’s visualization of attack paths connecting misconfigurations, identities, network exposures, and sensitive data is genuinely useful for explaining cloud risk to engineering and executive audiences. It is a differentiated capability.
- You need multi-cloud posture in a single tool. Wiz’s consistent cross-cloud data model and unified inventory across AWS, Azure, and GCP reduces the context-switching of managing separate tools per provider.
- Runtime security is not the primary requirement. If your cloud security program is focused on posture, misconfigurations, and vulnerability management rather than active threat detection, Wiz’s agentless model covers the essential use cases without agent complexity.
- You are already in contract. The switching cost of replacing Wiz — re-training teams, rebuilding integrations, re-establishing baselines — is substantial. Unless a specific capability gap is blocking security program goals, the operational cost of migration often outweighs the benefit.
For more AppSec Santa comparisons, see the full IaC security tools category.
Frequently Asked Questions
What is the best alternative to Wiz for smaller teams?
Is Orca Security better than Wiz?
Does Prisma Cloud replace Wiz?
What is the difference between Wiz and Aqua Security?
Which CNAPP tool has the best Kubernetes security?

Founder, AppSec Santa
Years in application security. Reviews and compares 215 AppSec tools across 12 categories to help teams pick the right solution. More about me →






