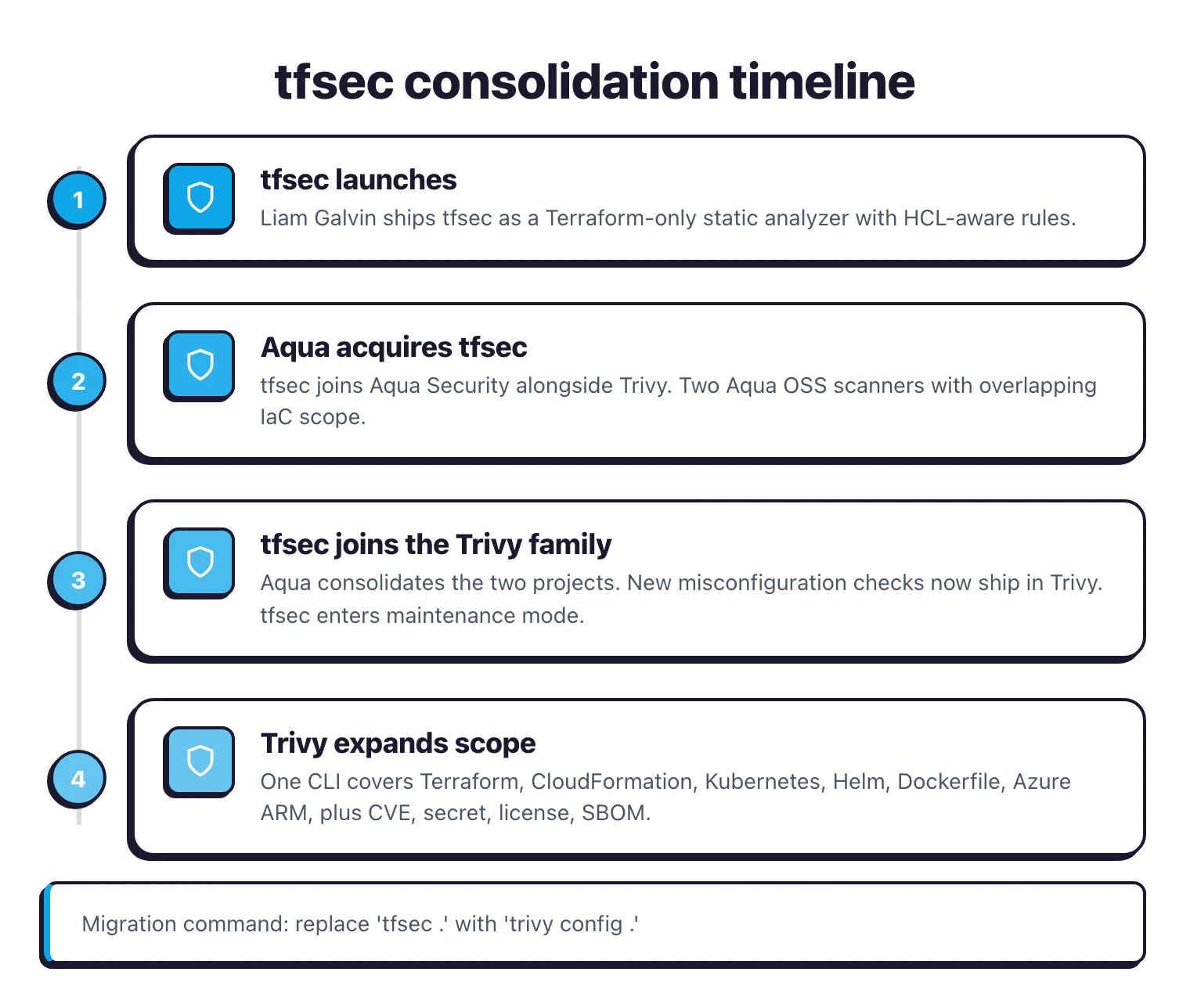
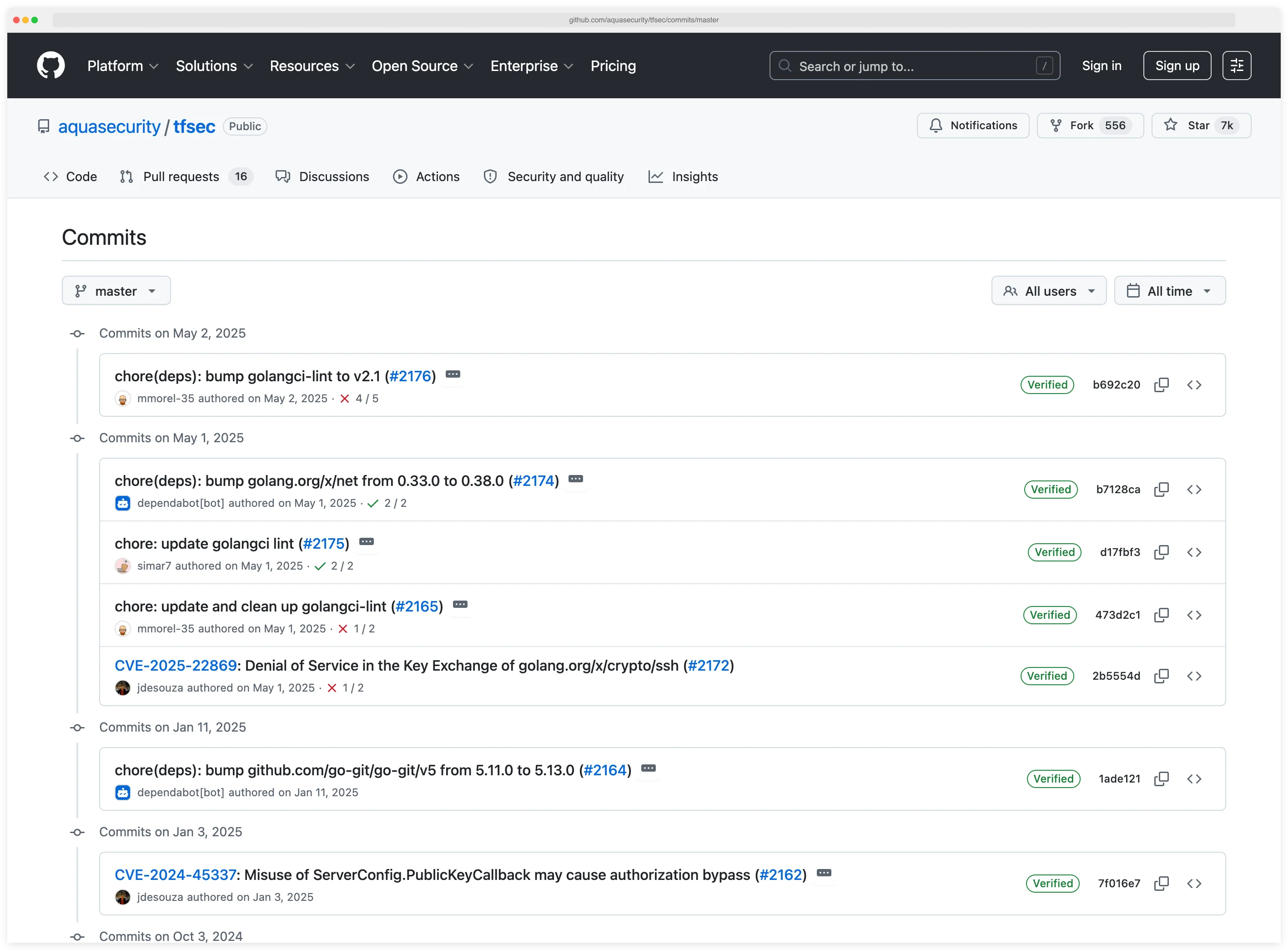
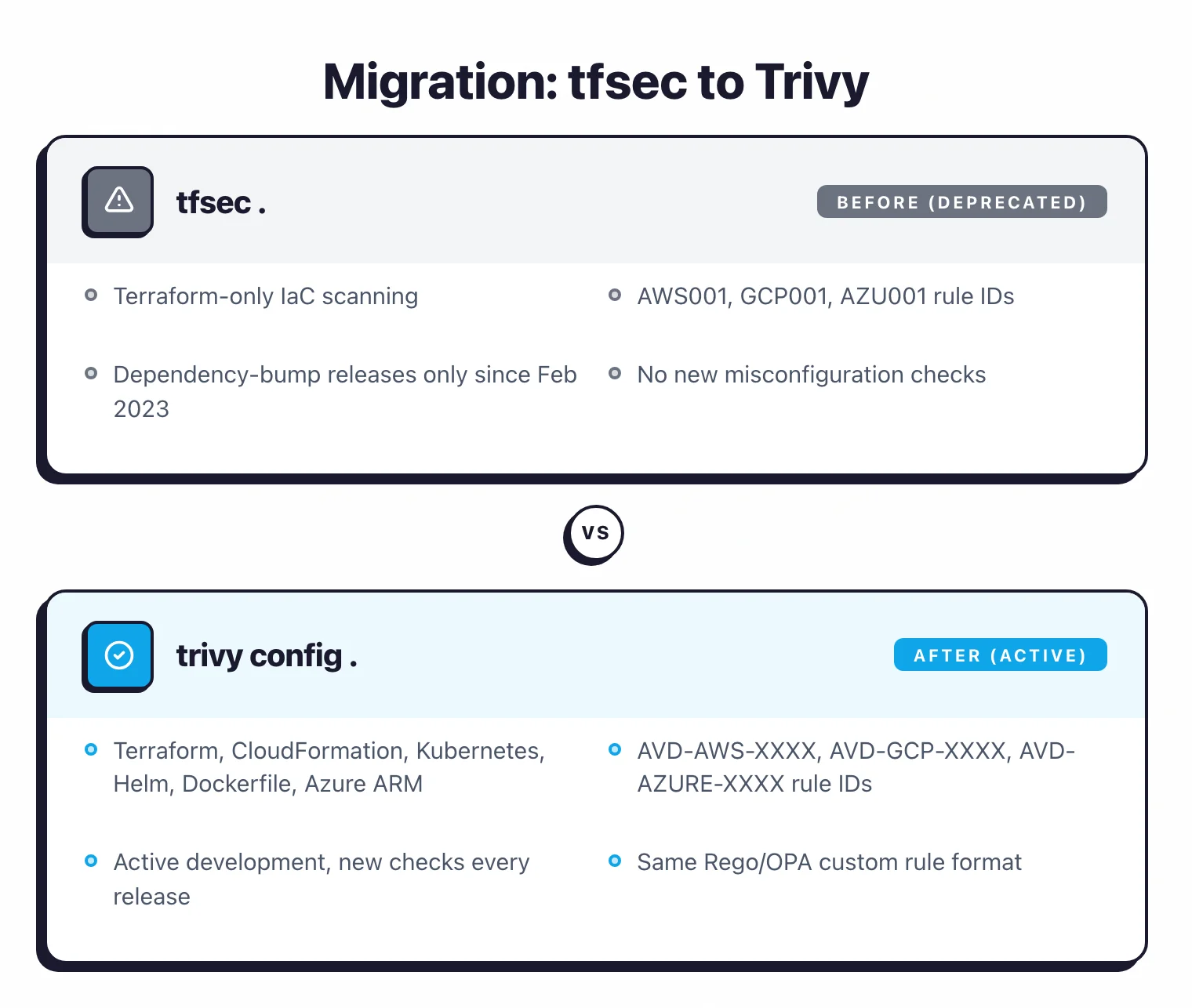
- Aqua Security announced in February 2023 that tfsec is joining the Trivy family. The tfsec repo still ships dependency bumps but no new checks; misconfiguration rule work now happens in Trivy.
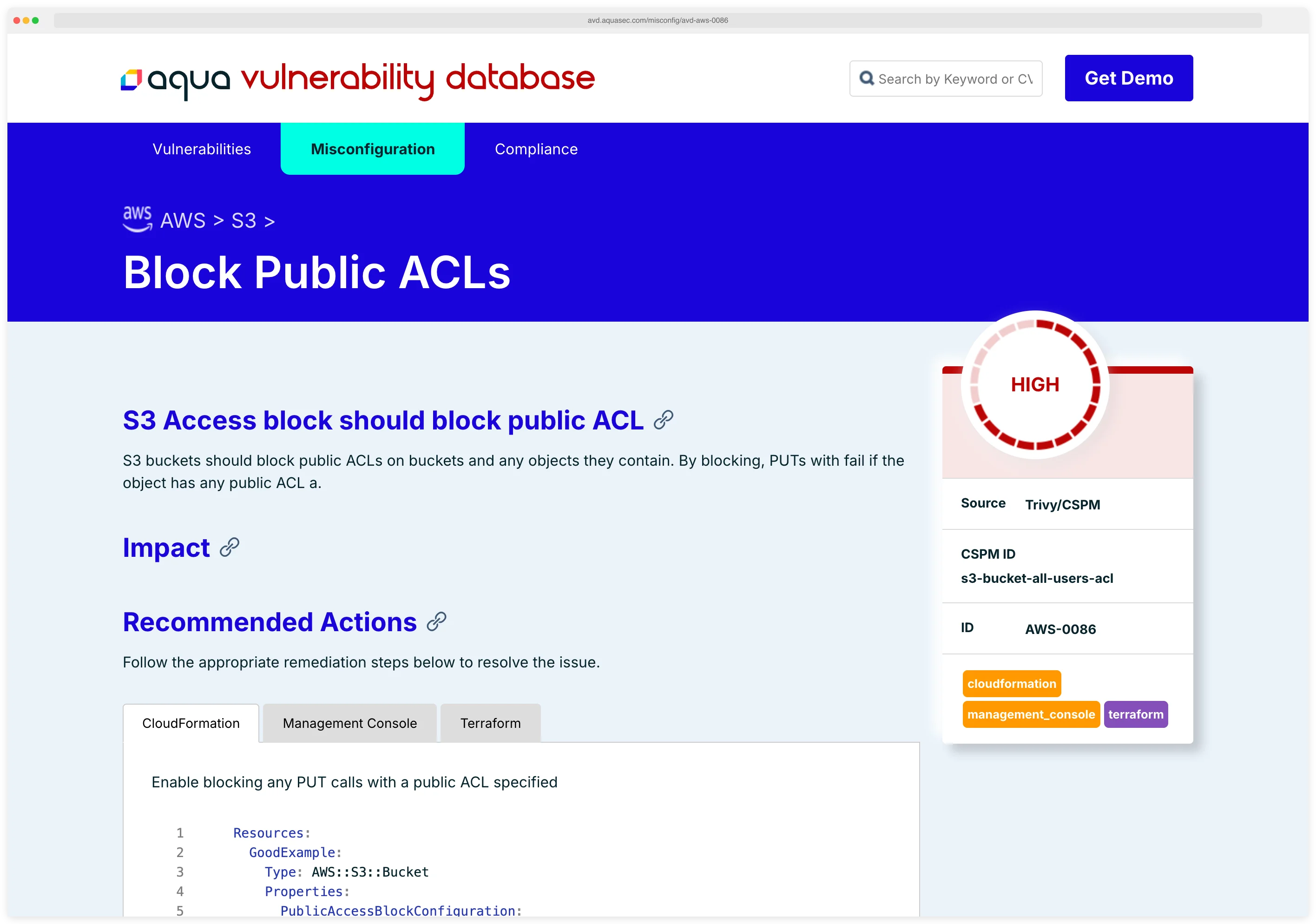
- Trivy is the active project. One scanner covers misconfiguration (formerly tfsec), vulnerability (CVE), license, secret, and SBOM scanning across containers, IaC, and source code.
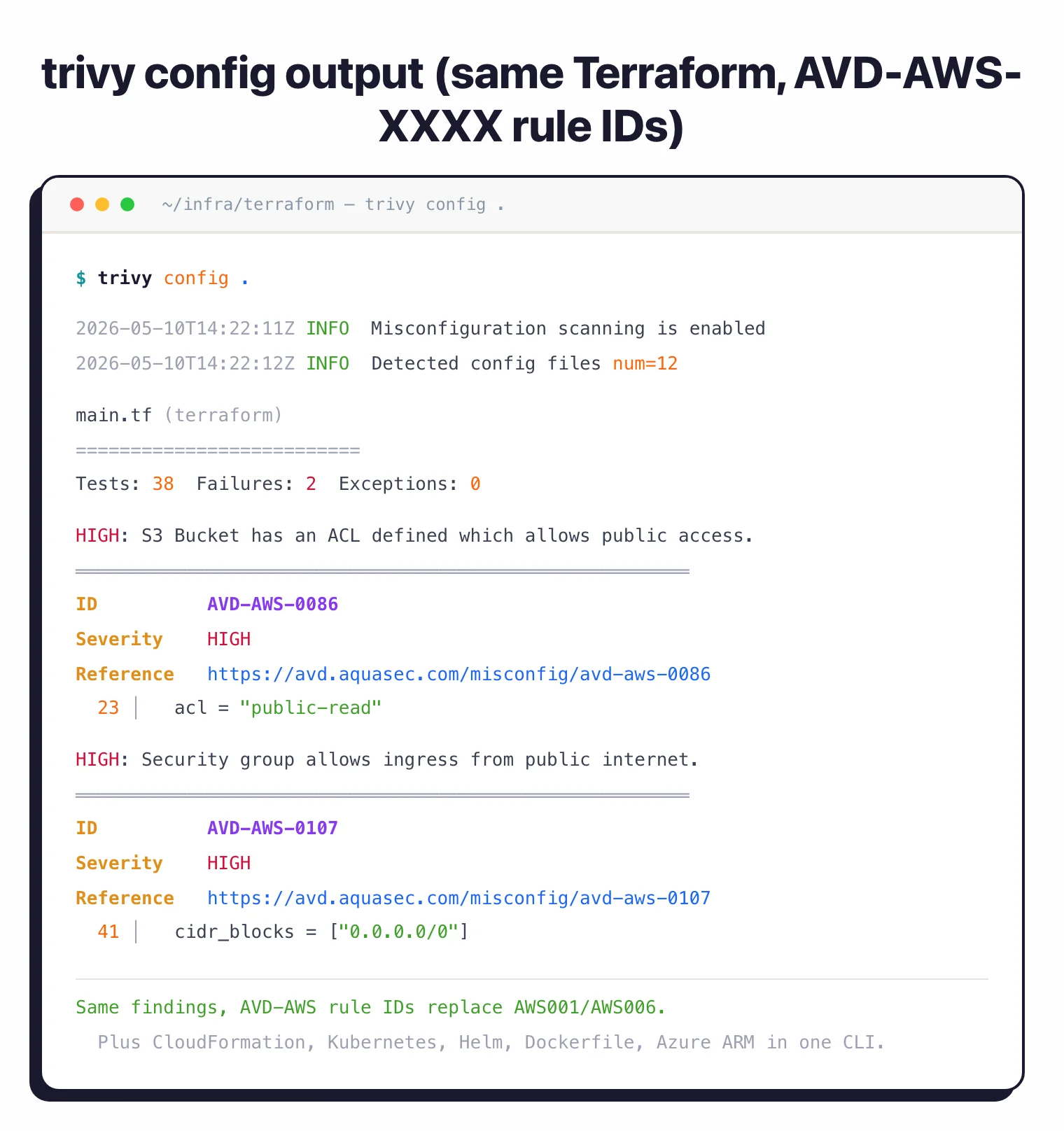
- Migrate from tfsec to Trivy with `trivy config <path>`. The same Terraform, CloudFormation, Kubernetes manifests, and Helm charts get scanned, and legacy tfsec rule IDs map to Trivy AVD rule IDs.
- Trivy's IaC scope reaches beyond Terraform to CloudFormation, Kubernetes manifests, Helm charts, Dockerfile, and Azure ARM templates. tfsec was Terraform-only at the time of the announcement.
- If you are still on tfsec in CI, the migration is small. Replace `tfsec .` with `trivy config .` and map any AWS001 / GCP001 / AZU001 allowlist entries to Trivy's AVD-AWS-XXXX naming.
What Happened: tfsec Joined the Trivy Family
Short answer for tfsec vs Trivy: Use Trivy. Aqua Security consolidated tfsec into the Trivy family in February 2023, and the tfsec repo gets no new misconfiguration checks.
Switch CI to trivy config <path> and the same Terraform rules keep running, plus CloudFormation, Kubernetes, Helm, Dockerfile, and Azure ARM coverage.
Both tools are maintained by Aqua Security. By 2023, tfsec’s Terraform-focused IaC scanner and Trivy’s broader IaC + containers + source code scanner had overlapping scope.
Aqua decided to consolidate. Engineering attention moved to Trivy, and tfsec’s Terraform check depth was folded into Trivy’s misconfiguration scanner.
The practical impact: if you are searching “tfsec vs Trivy” in 2026, the comparison is a migration question, not a tool selection. Switch CI to trivy config <path> and the same Terraform rules continue to run, plus a wider set covering CloudFormation, Kubernetes, Helm, Dockerfile, and Azure ARM templates.
Key Differences
| Dimension | tfsec (deprecated focus) | Trivy (active) |
|---|---|---|
| Status | Maintenance only; joined Trivy family Feb 2023 | Active, primary Aqua OSS scanner |
| Scope | Terraform-only IaC | Misconfig (IaC), vulnerability (CVE), license, secret, SBOM |
| IaC formats | Terraform | Terraform, CloudFormation, Kubernetes, Helm, Dockerfile, Azure ARM |
| Languages / runtimes | Terraform HCL | Container images, source repos, Git history, K8s clusters |
| Rule format | Custom + Rego (OPA) | Rego (OPA), the same format tfsec used |
| Output | tfsec text + JSON + JUnit + SARIF | Trivy table, JSON, SARIF, SBOM (CycloneDX/SPDX via convert), JUnit/HTML/ASFF via templates |
| CI integration | Standalone tfsec CLI, GitHub Actions | trivy CLI, GitHub Actions, GitLab template, Jenkins, Azure DevOps |
| Best for | Legacy CI not yet migrated | All current IaC + container scanning needs |
Migration Story
Why Aqua consolidated the two
By 2023, tfsec and Trivy were both Aqua-maintained open-source scanners with overlapping IaC scope. tfsec was Terraform-only. Trivy already had a misconfiguration scanner that handled Terraform, CloudFormation, Kubernetes, and more.
Maintaining two codebases for the same checks was duplicated engineering. Aqua announced the consolidation in February 2023 in the tfsec is joining the Trivy family post. Engineering attention shifted to Trivy, and the Terraform rule depth was folded in.
For users, the result was one CLI instead of two and one set of release notes instead of two.
What changed for tfsec users
The tfsec binary still works for existing CI pipelines. The repository ships dependency-bump releases (latest v1.28.14, May 2025), but no new misconfiguration rules and no new format support.
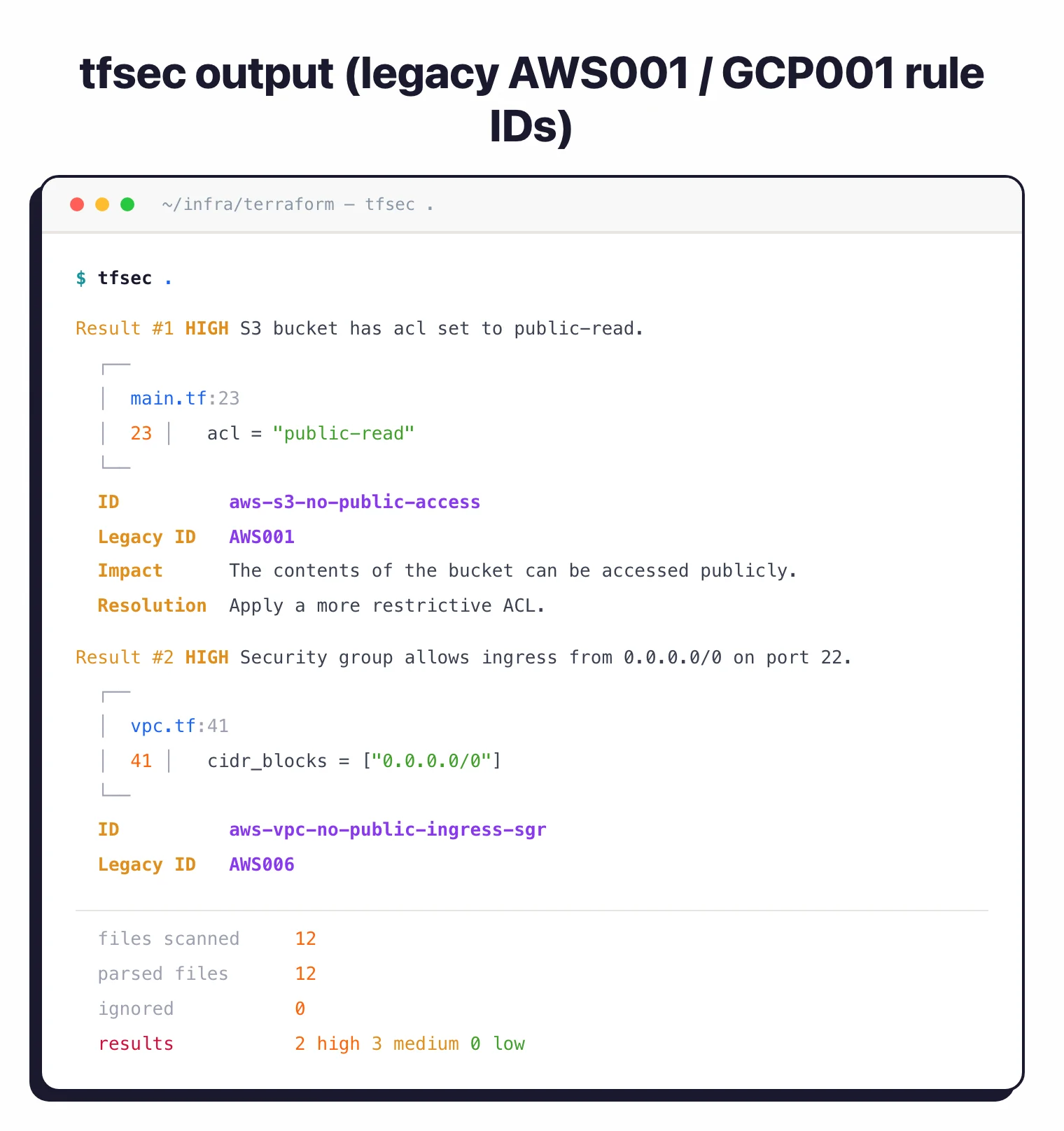
The tfsec rule IDs (AWS001, AWS002, GCP001, AZU001, and so on) map to Trivy’s Aqua Vulnerability Database format: AVD-AWS-XXXX, AVD-GCP-XXXX, AVD-AZURE-XXXX. The official tfsec-to-trivy-migration-guide.md in the tfsec repo documents the flag-by-flag CLI mapping.
Custom rules written for tfsec (in the Rego / OPA format) port to Trivy with minimal changes. The rule format is the same.
How to migrate
The smallest change is replacing the CLI invocation:
# Before (deprecated)
tfsec .
# After (active)
trivy config .
For more involved CI scripts:
- Replace
tfsec <path>withtrivy config <path>. - If you parse JSON output, the structure has changed. Switch to
trivy config -f json <path>and update any field accessors. - If you allowlist specific rule IDs, map old
AWS001 → AVD-AWS-XXXXusing Trivy’s documentation. - If you want CloudFormation, Kubernetes, Helm, Dockerfile, or Azure ARM scanning at the same time, drop them into the same
trivy configcall. No extra steps. - To unify with vulnerability scanning, run
trivy fs <path>for source-code SCA + secret scanning alongside.
Trivy’s broader scope
Beyond replacing tfsec, Trivy covers:
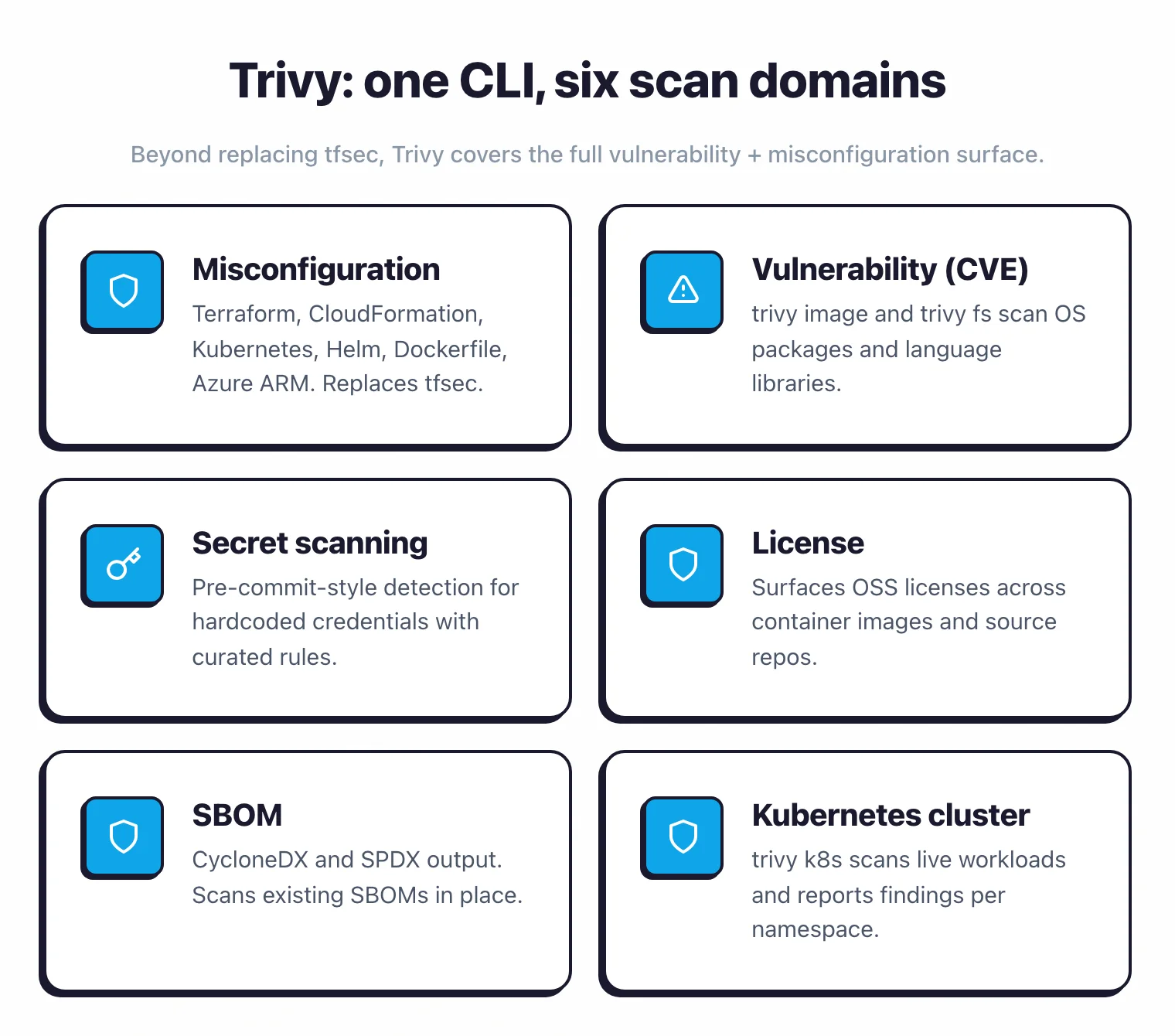
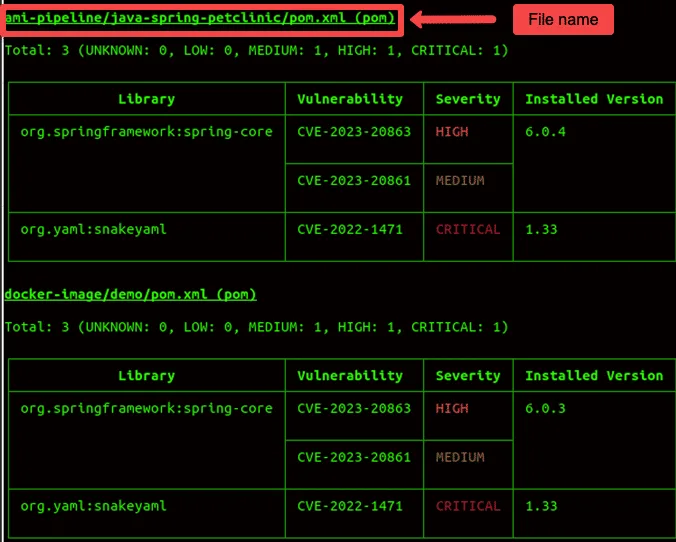
- Container image vulnerability scanning:
trivy image <image>finds CVEs in OS packages and language libraries. - SBOM generation and scanning: CycloneDX and SPDX output, plus the ability to scan an existing SBOM.
- Secret scanning: pre-commit-style detection for hardcoded credentials, with Aqua’s curated rules.
- License scanning: surfaces OSS licenses across container images and source repos.
- Filesystem scanning:
trivy fs <path>runs the full set against any directory or repo. - Kubernetes cluster scanning:
trivy k8s <cluster>scans live workloads.
Teams that adopted tfsec for Terraform pick up the rest of these capabilities by switching the CLI to Trivy. No license cost, no new vendor.
What To Do Now
If you are on tfsec in CI today
- Plan a migration sprint. Replace
tfsecinvocations withtrivy config. - Map any allowlisted rule IDs from the AWS001 / GCP001 / AZU001 naming to Trivy’s AVD-AWS-XXXX.
- Update any JSON parsers that consume tfsec output.
- Add
trivy fsandtrivy imageto your pipeline if you want vulnerability and secret scanning alongside.
If you are evaluating tfsec for a new project
- Skip tfsec. The project joined the Trivy family in 2023 and gets no new checks. Start with Trivy directly.
- For Terraform-only projects,
trivy configcovers what tfsec did. - For broader IaC scope (CloudFormation, Kubernetes, Helm, Azure ARM), Trivy handles all of it in one CLI.
If you want alternatives to Trivy
- Checkov : focused IaC-only scanner with strong rule curation.
- KICS : broad cloud-provider coverage from Checkmarx.
- See the Checkov vs Trivy and Checkov vs KICS comparisons for the live IaC tooling decisions.
Related comparisons
- Checkov vs Trivy : two active IaC scanners head-to-head.
- Checkov vs KICS : IaC-only alternatives to Trivy.
- Trivy alternatives : wider field of container and IaC scanners.
- Trivy vs Snyk : open-source Trivy vs commercial Snyk Container.
Frequently Asked Questions
Is tfsec still maintained?
trivy config <path>.What replaced tfsec?
How do I migrate from tfsec to Trivy?
tfsec <path> with trivy config <path> in your CI scripts. The default Terraform ruleset is the same; Trivy ships with the AWS, GCP, Azure, and Kubernetes checksets that tfsec used. If you allowlist specific tfsec rule IDs (AWS001, GCP002, etc), map them to Trivy’s AVD-AWS-XXXX naming. The official tfsec-to-trivy-migration-guide.md in the tfsec repo walks through flag-by-flag equivalents.Why did Aqua decide to consolidate tfsec into Trivy?
Should I use Trivy's IaC scanning or a different tool?

Founder, AppSec Santa
9+ years in application security. Reviews and compares 201 AppSec tools across 12 categories to help teams pick the right solution. More about me →
