Best Open-Source IaC Security Tools
The best open-source IaC security scanners for Terraform, Kubernetes, CloudFormation, and Helm in 2026. Checkov, Trivy, KICS, Terrascan, Conftest, and Kubescape compared by policy depth, platform coverage, and CI/CD fit.
- Checkov leads the open-source IaC field with 1,000+ policies including 800 graph-based cross-resource checks, covering Terraform, CloudFormation, Kubernetes, Helm, Dockerfiles, Ansible, ARM, and Bicep.
- Trivy absorbed tfsec in 2023 and now delivers IaC misconfiguration scanning alongside container image, SBOM, secret, and license scanning from a single Apache-2.0 binary.
- KICS ships 2,400+ queries from Checkmarx and targets Terraform, Kubernetes, Helm, CloudFormation, Ansible, OpenAPI, and Google Deployment Manager under Apache 2.0.
- Terrascan (Tenable, Apache 2.0) wraps Open Policy Agent for Rego-based policy, so teams already using OPA can write policies once and apply them across IaC and runtime K8s admission.
- Every tool listed is free (Apache 2.0 or AGPL equivalent); the commercial platforms built on top of these engines (Prisma Cloud, Aqua, Tenable Cloud Security) add dashboards, policy packs, and central reporting, but the scanning itself stays free.
The best open-source IaC security tools in 2026 are Checkov, Trivy, KICS, Terrascan, Conftest, and Kubescape. Each is Apache 2.0 (or AGPL equivalent), runs in CI/CD with minimal setup, and catches the same misconfigurations that the paid CNAPPs charge you for.
Why Choose Open-Source IaC Security Tools?
Three reasons teams pick open-source over commercial CNAPPs for IaC scanning.
The first is cost. Commercial cloud security platforms price on a per-asset, per-account, or per-workload basis, and IaC scanning is rarely the product they’re selling.
You often pay for runtime CSPM, CWPP, and CIEM features you don’t need yet, with IaC thrown in. A pure open-source stack gives you the scanning depth without the rest of the platform.
The second is CI/CD fit. Every tool in this list runs as a single binary or container, fits in a GitHub Actions workflow in under 10 lines of YAML, and outputs SARIF for GitHub code scanning or JSON for custom pipelines.
Commercial products add a web UI and a centralized policy engine, but the scanning contract is the same.
The third is transparency. You can read the policies. When Checkov flags CKV_AWS_20 on an S3 bucket, the check definition is a Python file on GitHub you can open and understand.
That transparency matters for organizations that need to justify which rules gate deploys and which are advisory.
The trade-offs are real. Open-source IaC scanners don’t give you central reporting across orgs and business units, they don’t map findings to a shared inventory, and remediation is on you.
For small-to-midsize engineering orgs running CI/CD-gated deploys, that’s a fair trade. For regulated enterprises with compliance teams needing audit trails, the commercial platforms usually win on operational features.
Top Open-Source IaC Security Tools
Checkov
Bridgecrew built Checkov before Palo Alto Networks acquired Bridgecrew and folded it into Prisma Cloud in 2021. The project remains Apache 2.0 and actively maintained by the Prisma Cloud team.
Checkov ships 1,000+ policies across Terraform, CloudFormation, Kubernetes, Helm, Dockerfiles, ARM, Bicep, Ansible, Kustomize, Serverless Framework, and OpenTofu.
The standout capability is graph-based policy: 800 checks model relationships between resources (an S3 bucket whose ACL is private but whose bucket policy grants Principal: * is a graph-level finding no single-file scanner catches).
Secrets detection includes verification against live APIs so confirmed credentials are marked differently from regex-matched guesses. IaC cost estimation is there for Terraform. Coverage maps explicitly to CIS, SOC 2, HIPAA, and PCI DSS.
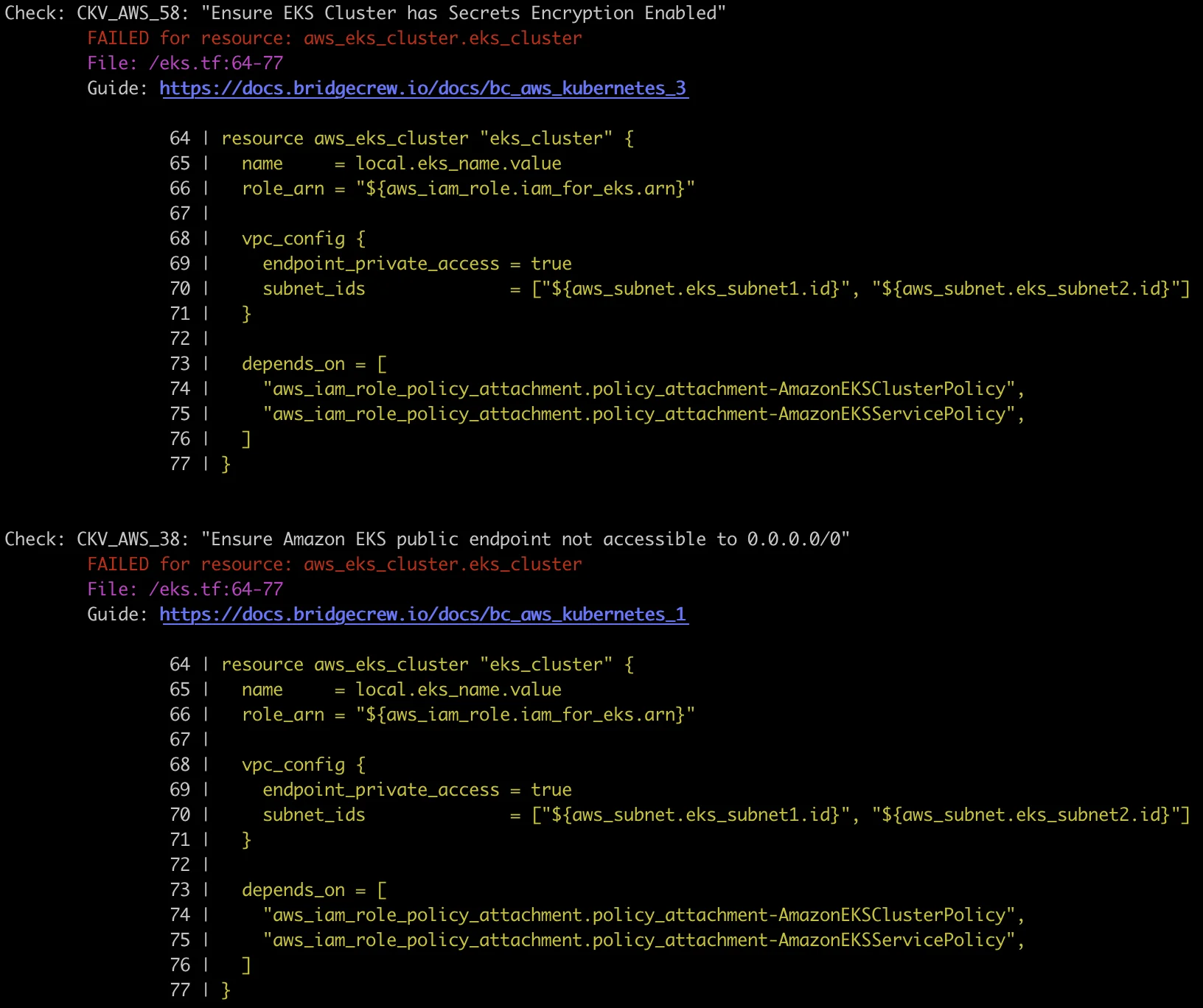
Use Checkov if you want the deepest IaC policy library of any open-source scanner and graph-based cross-resource checks matter to you.
Trivy
Aqua Security’s universal scanner . Trivy is Apache 2.0 with over 31,000 GitHub stars and covers containers, filesystems, dependencies, secrets, licenses, Kubernetes clusters, and IaC from a single binary.
For IaC specifically, Trivy absorbed tfsec in 2023
and now runs the full tfsec check library under trivy config. Coverage includes Terraform, CloudFormation, Kubernetes, Helm, and Dockerfiles. The check library is smaller than Checkov’s (it inherits tfsec’s roughly 150 checks rather than Checkov’s 1,000+), but it covers the most common misconfigurations and the detection quality is solid.
What makes Trivy worth adopting for IaC is consolidation. One tool scans your Terraform, your container images, your Kubernetes cluster, and your dependency manifests. For a team that wants one binary in CI instead of three, Trivy wins the tooling argument even if Checkov’s policy count is higher.

KICS
Keeping Infrastructure as Code Secure, from Checkmarx . Apache 2.0, 2,400+ queries, covering Terraform, Kubernetes, Helm, CloudFormation, Ansible, OpenAPI, Google Deployment Manager, Docker, and Pulumi.
KICS has the largest raw policy count in the open-source IaC space. The query language is its own DSL (JSON Schema plus Rego-style logic) so writing custom queries has a learning curve. Checkmarx provides commercial support via Checkmarx One, which bundles KICS with the broader Checkmarx platform.
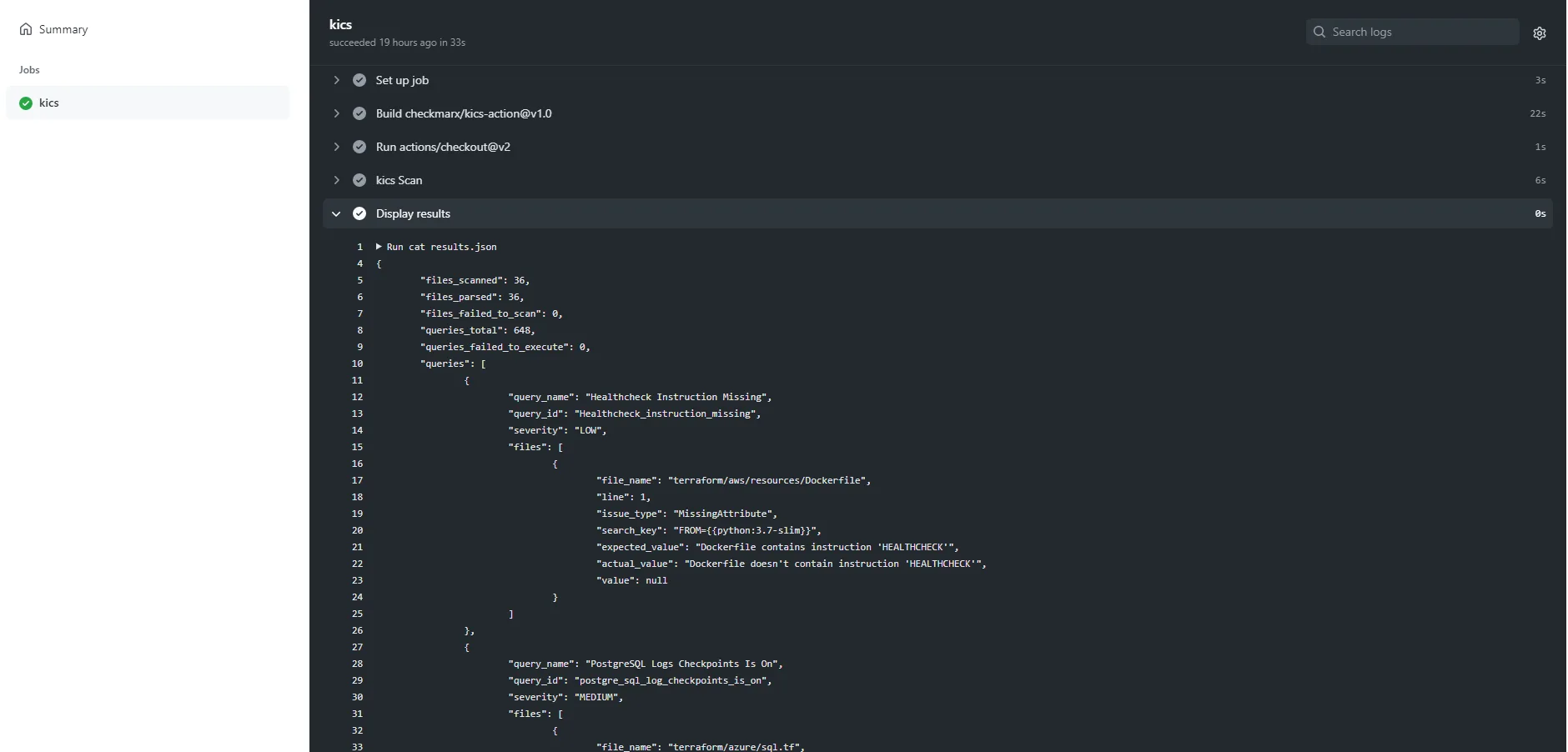
Use KICS when you want the broadest out-of-the-box query coverage, especially across Pulumi and Google Deployment Manager where other scanners are thinner.
Terrascan
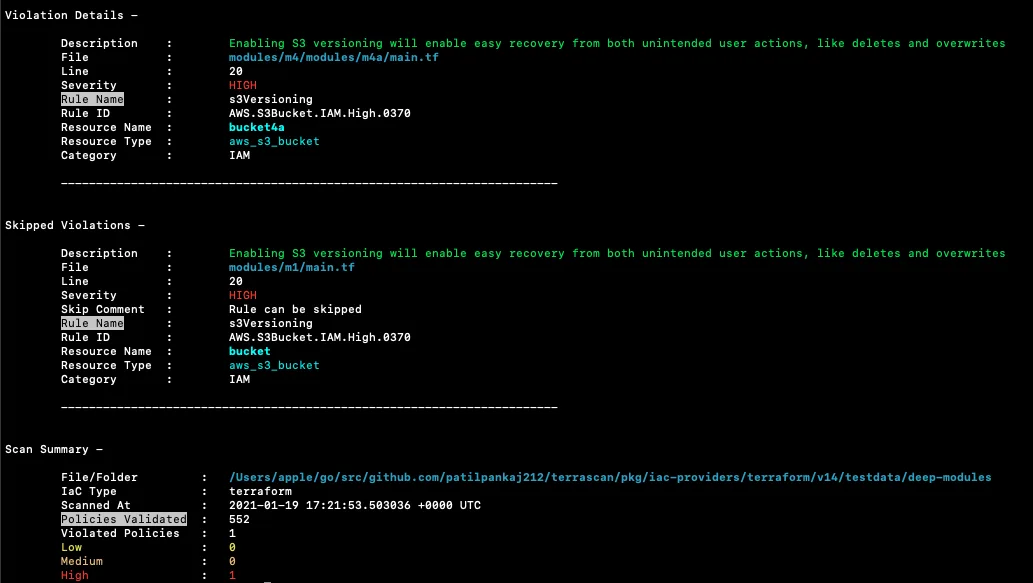
Terrascan was built by Accurics , then acquired by Tenable in 2021 and folded into the Tenable Cloud Security (formerly Accurics/Tenable.cs) platform. The open-source project remains Apache 2.0.
The differentiator is policy architecture. Terrascan uses Open Policy Agent (OPA) and Rego , so policies written for Terrascan run unchanged against OPA Gatekeeper in Kubernetes admission control. Teams already invested in OPA for runtime policy get policy reuse out of Terrascan for free.
Coverage is Terraform, CloudFormation, Kubernetes manifests, Helm, and Kustomize. Policy count is smaller than KICS or Checkov, but the OPA alignment is meaningful for platform teams running OPA everywhere.
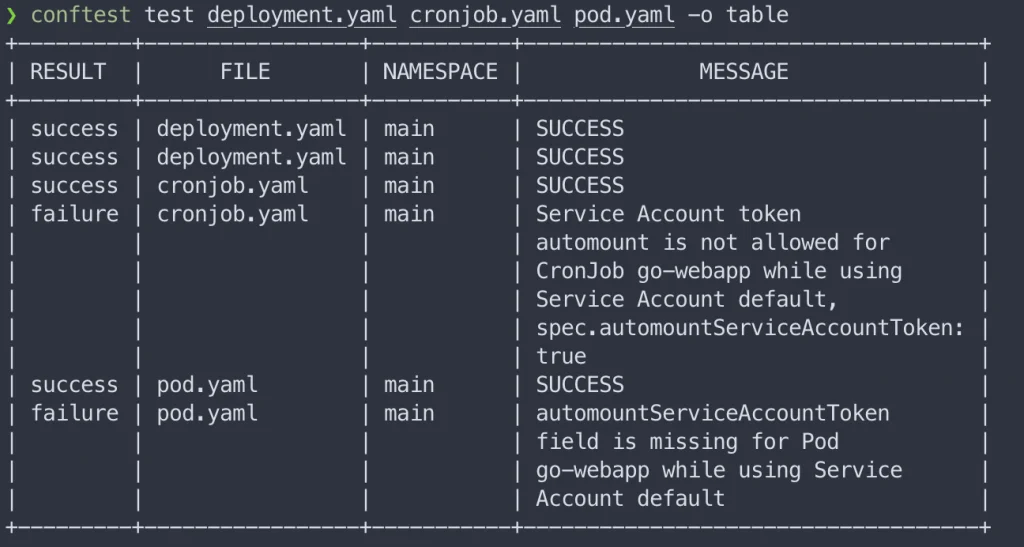
Conftest
Conftest is by the Open Policy Agent project itself . Apache 2.0, part of CNCF .
It doesn’t ship policies out of the box, you write Rego rules that validate structured configuration files (Terraform plan JSON, Kubernetes YAML, Dockerfile AST, Helm output). This is policy-as-code in the most literal sense: the tool is infrastructure, you bring the checks.
Use Conftest when your organization already uses OPA for other concerns (admission control, authorization, microservice policy) and you want a unified policy language across all of them. Don’t use it if you want out-of-the-box coverage of common CIS or CIS-like benchmarks; reach for Checkov or KICS instead.
Kubescape
Kubernetes-specific posture scanner from ARMO , now a CNCF sandbox project. Apache 2.0.
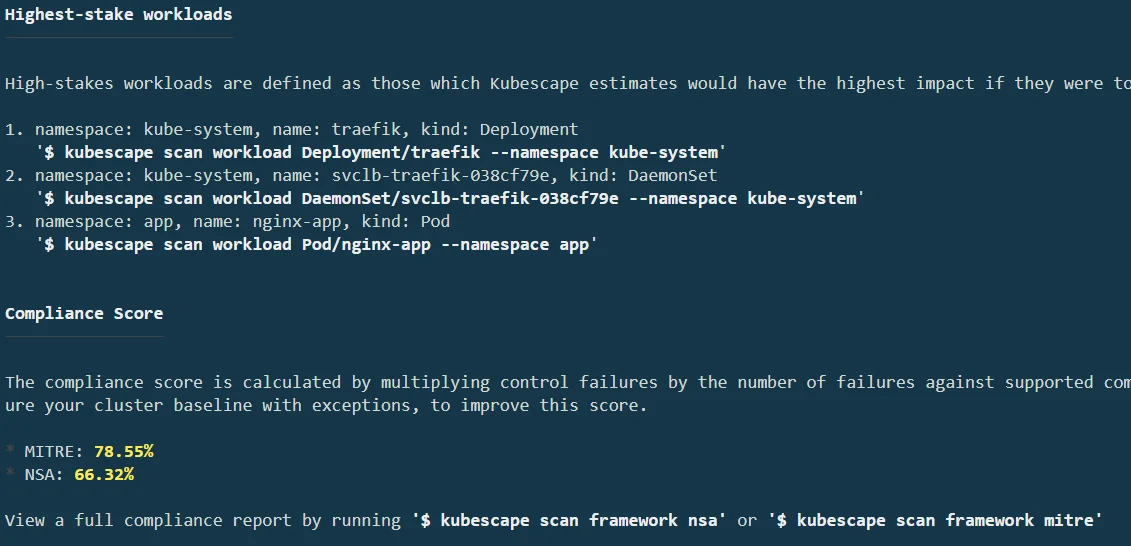
Ships NSA-CISA , MITRE ATT&CK, CIS, SOC 2, and NIST framework packs out of the box. Runs as a CLI, a GitHub Action, an admission controller, and a runtime agent. The compliance reporting is the strongest in the open-source K8s space, you get a score per control framework with remediation guidance.
For IaC specifically, Kubescape scans Kubernetes manifests, Helm charts, and Kustomize configurations. For runtime Kubernetes posture, it runs in-cluster. The scope is narrower than Checkov’s or Trivy’s, it does K8s only, but for K8s-first teams the depth is worth it.
Honorable mentions
trivy config. If your CI still invokes tfsec, migrate to Trivy for continued updates.Trivy’s predecessor, tfsec, is now archived and merged into Trivy. If your CI still invokes tfsec, migrate to trivy config, same check IDs, active development.
Datree was an open-source K8s manifest validator, but the company was acquired in late 2022 and the project is effectively unmaintained. Use Kubescape instead for K8s manifest scanning.
OPA Gatekeeper is the runtime admission-controller sibling of Conftest, same Rego policies, different deployment model. Use it when you want to enforce IaC-equivalent policies at the point of resource creation in a cluster.
Feature Comparison
| Tool | License | Focus | Policies | Best For |
|---|---|---|---|---|
| Checkov | Apache 2.0 | IaC (broad) | 1,000+ (800 graph-based) | Deepest out-of-box coverage, cross-resource checks |
| Trivy | Apache 2.0 | All-in-one (IaC + containers + SBOM + secrets) | ~150 IaC (inherited from tfsec) | Tool consolidation across IaC and containers |
| KICS | Apache 2.0 | IaC (broad) | 2,400+ | Widest out-of-box query count |
| Terrascan | Apache 2.0 | IaC (Rego-based) | ~500 | OPA-aligned orgs, runtime reuse |
| Conftest | Apache 2.0 | Policy-as-code | Zero OOTB | Custom Rego policies, full flexibility |
| Kubescape | Apache 2.0 | Kubernetes specific | ~200 K8s controls | Kubernetes-first teams, compliance reporting |
When Should You Use a Commercial Tool Instead?
Open-source IaC scanning is enough for most teams. Move to a commercial CNAPP when you need:
- Central reporting across many orgs, accounts, and business units, with role-based access and audit logs
- Correlation between IaC findings and runtime cloud posture, so a misconfig flagged in Terraform maps to the actual deployed resource
- Compliance attestation reports ready to hand to auditors, not just SARIF output
- SLA-backed support with a vendor contract
- Integration with identity providers, SIEMs, and the rest of a security operations stack
For those needs, Wiz vs Orca Security and Wiz vs Prisma Cloud cover the top CNAPP options. If you’re evaluating whether a CNAPP adds enough over open-source, the CSPM vs CNAPP explainer helps frame the decision.
For the full IaC category, see IaC security tools . For deeper container-focused comparisons, Checkov vs Trivy and Checkov vs KICS cover the two most common head-to-heads.
Frequently Asked Questions
Which open-source IaC scanner has the most policies?
Is tfsec still maintained?
trivy config, and the tfsec repo redirects to Trivy. If you see guides recommending tfsec, treat them as recommending Trivy’s IaC misconfiguration scanner.Can I use Checkov and Trivy together?
Which tool is best for Kubernetes manifest scanning specifically?
trivy k8s.How do open-source tools compare with Prisma Cloud or Wiz on IaC?

Founder, AppSec Santa
9+ years in application security. Reviews and compares 201 AppSec tools across 12 categories to help teams pick the right solution. More about me →





