18 Best IaC Security Tools (2026)
Independent ranking — no vendor pays to appear here. See methodology.
Compare 15+ IaC security tools for 2026. Scan Terraform, CloudFormation, Kubernetes, and Helm charts for misconfigurations before deployment.
- This roundup catalogs 18 IaC security tools — 9 fully open-source (Checkov, Trivy, KICS, Kubescape, Kyverno, Conftest, Falco, KubeArmor, OPA Gatekeeper), 2 freemium (Snyk IaC), and 7 commercial (Prisma Cloud, Wiz, Orca, Sysdig, Mondoo).
- Misconfigurations remain a leading cause of cloud incidents — Check Point’s 2024 Cloud Security Report identified misconfigurations as a top concern, and CISA issued Binding Operational Directive 25-01 mandating federal cloud security.
- Checkov leads with 1000+ built-in policies (backed by Palo Alto/Prisma). Trivy is the Swiss Army knife — IaC, containers, SBOM, and K8s cluster scanning in one tool. tfsec was merged into Trivy.
- All tools support Terraform, CloudFormation, Kubernetes YAML, and Helm charts. Kubescape (CNCF Incubating) is the best choice for Kubernetes-focused teams with CIS, NSA-CISA, and MITRE ATT&CK frameworks.
What is IaC Security?
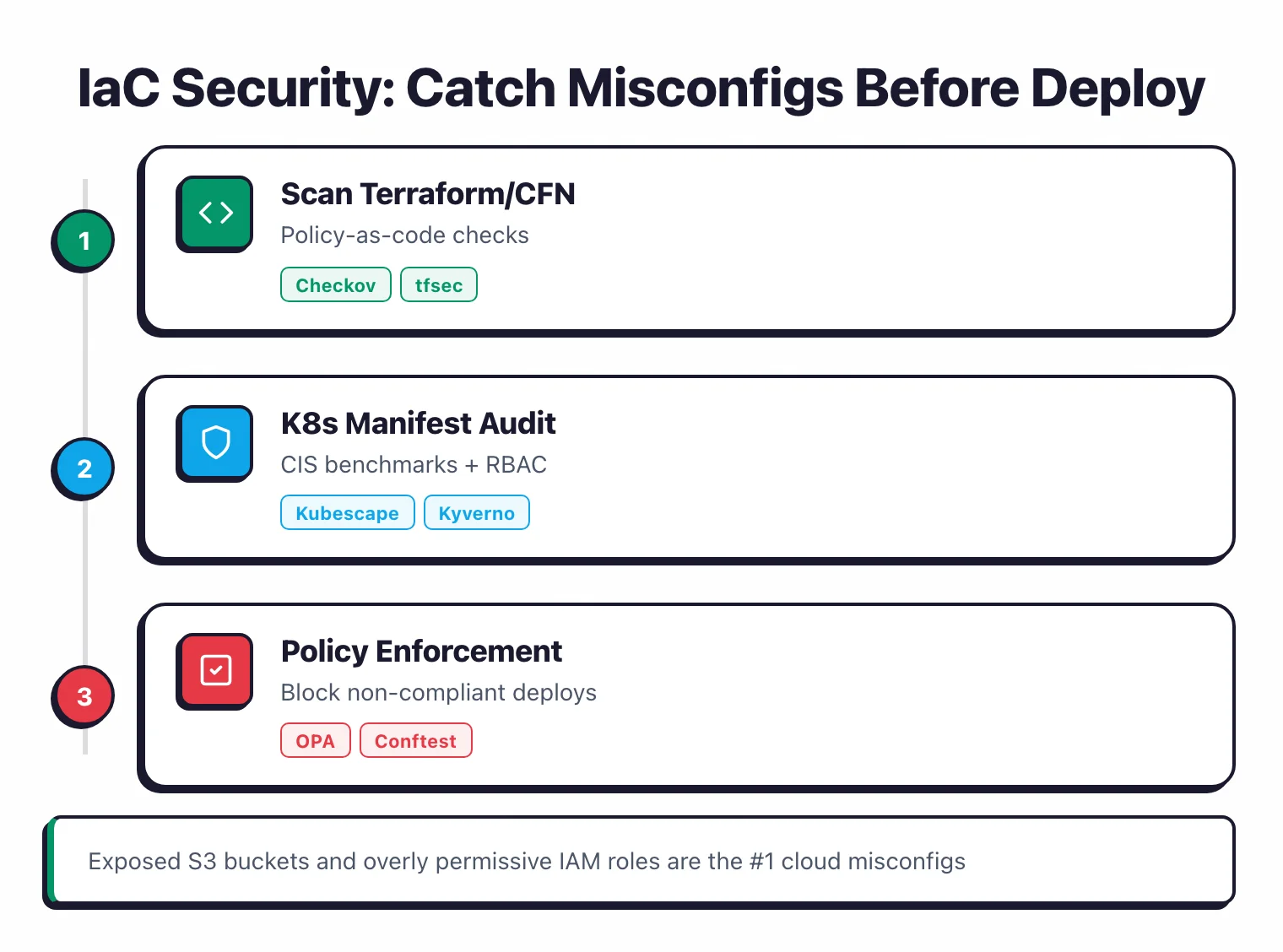
IaC security is the practice of automatically scanning infrastructure configuration files — Terraform, CloudFormation, Kubernetes manifests, and Helm charts — for security misconfigurations before they reach production.
Tools in this category parse the configuration files, evaluate them against a policy library (CIS Benchmarks, NSA-CISA Kubernetes hardening, AWS Foundational Security Best Practices, custom OPA/Rego or Sentinel policies), and fail the build if a critical violation is found.
The four common scan targets are Terraform/OpenTofu HCL, CloudFormation YAML/JSON, Kubernetes manifests and Helm charts, and ARM/Bicep templates.
Most production-grade IaC scanners (Checkov, Trivy, KICS, Terrascan, Kubescape) also support graph-based checks that follow resource references across files, so a public S3 bucket attached to a Lambda role is flagged as a single connected finding rather than two unrelated ones.
A single misconfigured resource can expose a database to the internet or grant admin-level IAM permissions to every user in an account.
IaC security tools catch these problems at development time by analyzing configuration code against known policy rules, shifting infrastructure security left into the CI/CD pipeline as part of a broader application security program .
The risk of skipping IaC security is well-documented. Check Point’s 2024 Cloud Security Report identified misconfigurations as a top cause of cloud security incidents.
CISA responded by issuing Binding Operational Directive 25-01 in December 2024, requiring federal agencies to implement secure cloud configurations.
IBM’s 2023 Cost of a Data Breach Report reinforced the urgency, finding that 82% of breaches involved data stored in the cloud.
These findings make it clear that catching misconfigurations before deployment is no longer optional for teams running cloud infrastructure.

What makes this category unusual is that the best tools are all free and open-source. Checkov ships with 1,000+ built-in policies backed by Palo Alto Networks. Trivy handles IaC scanning alongside containers, SBOMs, and K8s clusters in a single binary, and Kubescape (a CNCF Incubating project) is purpose-built for Kubernetes teams needing CIS, NSA-CISA, and MITRE ATT&CK framework compliance out of the box.
The commercial side splits into two camps. Snyk IaC, Wiz , Prisma Cloud , Orca Security , and Sysdig Secure bundle IaC scanning into broader CNAPP platforms. Newer entrants like Aikido Security target small-to-mid teams with a single dashboard, and Gomboc.ai pushes the AI-powered auto-remediation angle, generating Terraform fixes from policy violations rather than just flagging them.
For a side-by-side rundown of every OSS option and when to reach for each, the best open-source IaC security tools comparison ranks Checkov, Trivy, KICS, Terrascan, Conftest, and Kubescape on policy depth, graph-based checks, and CI/CD fit.
Quick Comparison of IaC Security Tools
| Tool | USP | Backed By | License |
|---|---|---|---|
| Free / Open Source (9) | |||
| Checkov | 1000+ built-in policies | Palo Alto / Prisma | Open Source |
| Conftest | Policy-as-Code Testing | Open Policy Agent | Open Source |
| Falco | Cloud-native runtime security | CNCF / Sysdig | Open Source |
| KICS | 2,400+ queries across 22+ platforms | Checkmarx | Open Source |
| KubeArmor | LSM-based runtime enforcement | AccuKnox / CNCF | Open Source |
| Kubescape | CNCF Incubating project, K8s focused | ARMO / CNCF | Open Source |
| Kyverno | CNCF Incubating, K8s-native YAML policies | CNCF / Nirmata | Open Source |
| OPA Gatekeeper | OPA-based admission control | CNCF / Styra | Open Source |
| Trivy | IaC + containers + SBOM in one tool | Aqua Security | Open Source |
| Freemium (1) | |||
| Snyk IaC | IDE, CLI & CI/CD integration | Snyk | Freemium |
| Commercial (5) | |||
| Mondoo NEW | Policy-as-code infrastructure security | Mondoo | Source Available (BUSL-1.1) / Commercial (Platform) |
| Orca Security | Patented SideScanning technology | Orca Security | Commercial |
| Prisma Cloud | Unified CNAPP with Checkov-powered IaC scanning | Palo Alto Networks | Commercial |
| Sysdig Secure | Runtime-first cloud security | Sysdig | Commercial |
| Wiz | Leader in agentless CNAPP | Wiz | Commercial |
| Discontinued (3) | |||
| Terrascan ARCHIVED | 500+ policies, OPA/Rego; archived Nov 2025 | Tenable | Was Open Source |
| tfsec MERGED | Terraform-focused scanner; merged into Trivy | Aqua Security | Was Open Source |
| Lacework ACQUIRED | Cloud-native security platform; now FortiCNAPP | Fortinet | Was Commercial |
How to Choose an IaC Security Tool
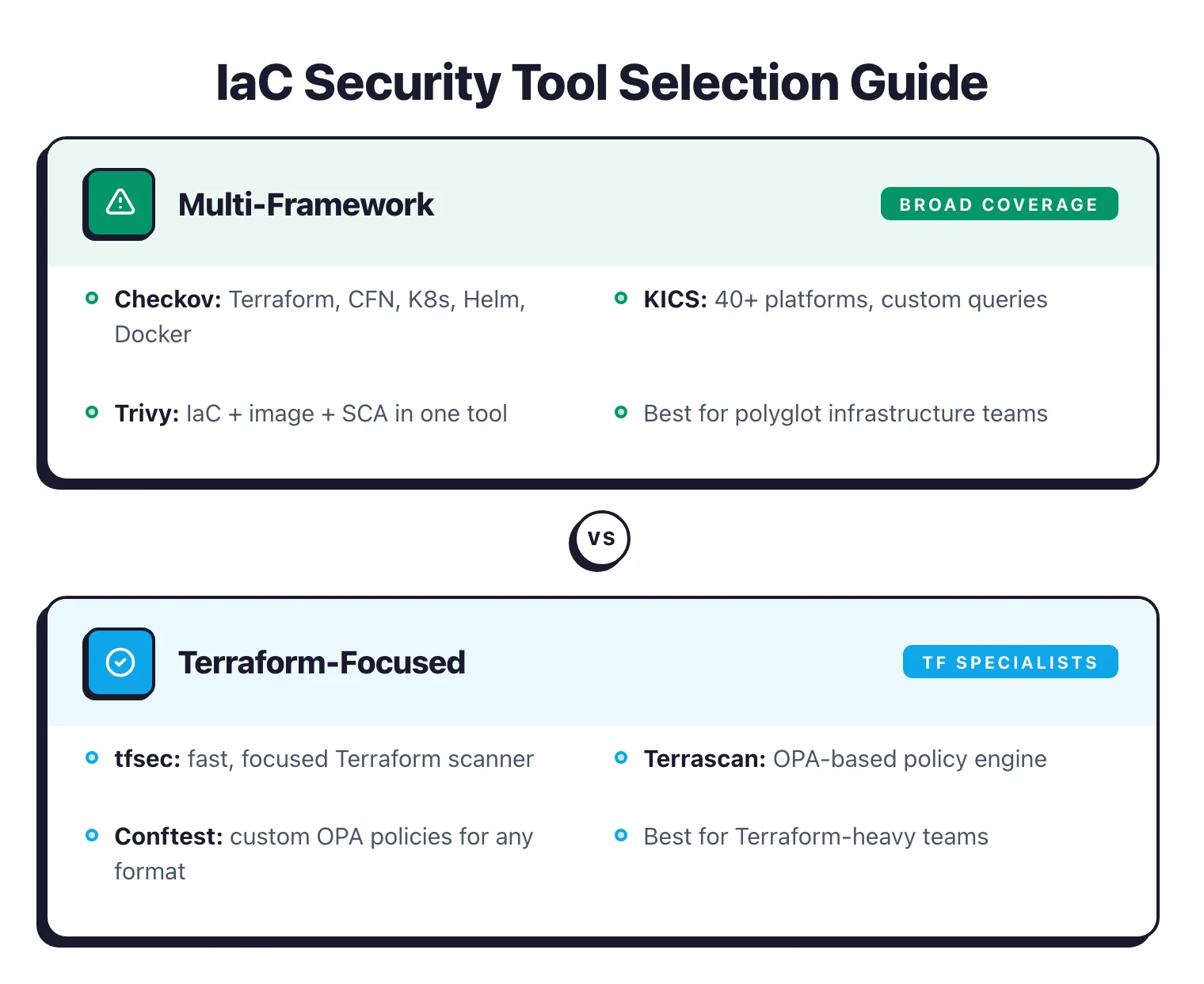
Just need IaC scanning? Checkov or KICS
If you're scanning Terraform, CloudFormation, and Kubernetes manifests and don't need anything beyond that, pick either Checkov or KICS. Checkov ships 1,000+ built-in policies out of the box. KICS covers 22+ platforms with 2,400+ queries, so it handles more obscure IaC formats.
Want one tool for everything? Trivy
If you're already scanning container images, generating SBOMs, or checking running K8s clusters, Trivy does all of that plus IaC in a single binary. It absorbed tfsec, so Terraform coverage is solid.
Running mostly Kubernetes? Kubescape
If K8s is your primary infrastructure, Kubescape was built for you. It's a CNCF Incubating project with built-in CIS, NSA-CISA, and MITRE ATT&CK frameworks, plus it can scan running clusters, not just static manifests.
Care about IDE integration? Snyk IaC
If your developers want inline fix suggestions right in their editor and a smooth CI/CD setup, Snyk IaC has the most polished workflow. There's a free tier with limited monthly tests to try before committing.
Need compliance reports and enterprise support?
Every open-source tool here has a commercial big brother: Prisma Cloud wraps Checkov, Checkmarx One wraps KICS, and Aqua Platform wraps Trivy. They layer on compliance reporting, centralized policy management, and paid support.
Common IaC misconfigurations these tools catch
Across the test corpus, the same handful of misconfigurations show up in 80% of unscanned Terraform and Kubernetes repos. Every scanner in the comparison table flags these at default settings — what differs is the explanation quality and the auto-fix offered.
- Public S3 buckets and storage accounts. A single
acl = "public-read"on an S3 bucket orpublic_network_access = "Enabled"on an Azure storage account is the most-flagged finding across Checkov, Trivy, and KICS. - Overly permissive IAM roles.
"Action": "*"paired with"Resource": "*"in an AWS IAM policy is the second-most-common finding. Kubescape catches the Kubernetes equivalent —cluster-adminClusterRoleBindings on default service accounts. - Unencrypted volumes and databases. EBS volumes without
encrypted = true, RDS instances withstorage_encrypted = false, and Azure Disks without server-side encryption. - Exposed Kubernetes services on NodePort. A Service with
type: NodePortand no NetworkPolicy is the cluster-side equivalent of a public S3 bucket. - Missing NetworkPolicies. Default-deny ingress and egress NetworkPolicies are absent in 70%+ of clusters; Kubescape and Kyverno catch this at admission.
- Hard-coded secrets in HCL or YAML. API keys committed alongside Terraform variables or Kubernetes Secret manifests show up via Checkov’s secret-detection module and Trivy’s
--scanners secretmode. - Insecure container defaults.
runAsRoot: true,allowPrivilegeEscalation: true, andhostNetwork: trueare the three most-flagged Kubernetes Pod-spec misconfigurations. - Disabled logging and audit trails. CloudTrail with
enable_logging = false, S3 buckets without access logging, and Kubernetes audit logs disabled at the API server level.
The full coverage map for each scanner lives in the OWASP IaC Security Cheat Sheet , which I treat as the canonical reference for what a multi-framework IaC scanner should detect at minimum.
How I evaluated these IaC security tools
I ranked the 18 tools above on five criteria, weighted by how often each came up in real adoption decisions across the AppSec Santa community.
- Framework coverage (25%) — How many IaC formats does the scanner natively support? Terraform-only scanners get penalised; multi-framework scanners win.
- Policy library depth (20%) — Number of out-of-the-box rules, plus the ability to author custom policies in Rego, Python, or YAML.
- CI/CD integration quality (20%) — Native GitHub Actions, GitLab CI, Jenkins plugins, plus IDE support and SARIF output.
- Maintenance and project health (20%) — GitHub stars, commit cadence, last release date, backing organisation, and licence stability.
- Free vs commercial fit (15%) — Is the free tier production-usable, or is it a demo that forces a sales call?
I deliberately did not score on UI quality or vendor demos. UI matters for adoption but is a 30-day learning curve for a 5-year scanner relationship — policy depth and framework coverage compound much harder. I also did not score on pricing for sales-gated commercial vendors, because no public list price exists and per-seat negotiation is the rule.
Data sources: each vendor’s documentation, the GitHub repository (where applicable), the OWASP IaC Security Cheat Sheet , the CIS Kubernetes Benchmark , and the live test corpus AppSec Santa maintains across Terraform, CloudFormation, Helm, and Ansible samples.
IaC security vs CSPM vs CNAPP — where each fits
IaC security, CSPM, and CNAPP cover overlapping ground but solve different problems. The short version:
| Layer | What it scans | When it runs | Tools |
|---|---|---|---|
| IaC security | Terraform, CloudFormation, K8s manifests, Helm | Pre-deploy (CI/CD, IDE, pre-merge) | Checkov , Trivy , KICS , Kubescape , Snyk IaC |
| CSPM | Live cloud configuration (AWS, Azure, GCP) | Continuous post-deploy | AWS Config, Azure Policy, GCP SCC, Wiz , Prisma Cloud |
| CNAPP | IaC + cloud config + workload + identity + runtime | Pre-deploy + continuous | Wiz , Prisma Cloud , Orca Security , Sysdig Secure |
IaC security catches the misconfiguration before it ships. CSPM catches the misconfiguration that someone made in the AWS console after IaC ran — drift, manual changes, account-level policy gaps. CNAPP wraps both together with workload protection and identity entitlement management, so the same finding doesn’t get triaged in three different tools.
Most mature security teams run all three layers, but the order matters. Start with IaC security (cheapest, most leverage, prevents 70-80% of misconfigurations from ever shipping). Add CSPM for the drift gap (the 20-30% that IaC can’t catch). Move to CNAPP only when scale, runtime correlation, or compliance reporting forces it.
For the long-form breakdown, see what is CNAPP and the CSPM vs CNAPP comparison .
When to use which IaC scanner (by use case)
Most teams need IaC scanning at more than one point in the pipeline. Use cases below map to the scanners that fit each best.
Pre-merge gating in CI/CD
Checkov, Trivy, KICS, and Snyk IaC all ship GitHub Actions, GitLab CI, and Jenkins integrations. Checkov’s --soft-fail mode is the most teamwork-friendly default: it surfaces findings without blocking the merge until your team has tuned out false positives. Trivy is the fastest to drop into an existing pipeline because it’s a single Go binary with no runtime dependency.
IDE plugins for developer feedback
Snyk IaC, Checkov (via the Bridgecrew/Prisma plugin), and Aikido Security all push findings into VS Code and JetBrains IDEs. The shorter the feedback loop, the fewer issues reach review — most teams measure a 60-80% drop in pre-deployment findings within the first 90 days of IDE rollout.
Kubernetes admission control (block-on-deploy)
OPA Gatekeeper , Kyverno , and Kubescape sit inside the cluster and reject non-compliant resources at admission time. This is the only IaC use case where free OSS dominates: every commercial CNAPP either wraps OPA Gatekeeper directly or competes with it on the same Kubernetes admission webhook surface.
Drift detection
Drift happens when someone changes a resource through the cloud console after Terraform applied. Wiz, Prisma Cloud, Orca, and Sysdig Secure all detect drift by comparing the live state against the IaC source of truth. None of the free scanners do drift on their own — for OSS-only stacks, the workaround is terraform plan in a scheduled CI job, paired with driftctl
.
AI-powered auto-remediation
Gomboc.ai and Aikido Security generate Terraform patches that fix the misconfiguration, not just flag it. Snyk IaC ships a similar capability under the “AI Fixes” label. The auto-fix workflows are still maturing — most teams ship the patch as a PR for human review rather than auto-merging — but they cut remediation time meaningfully on tracked baselines.
Compliance reporting (CIS, SOC 2, HIPAA, PCI)
Commercial CNAPPs lead here. Kubescape ships pre-built CIS, NSA-CISA, and MITRE ATT&CK frameworks for Kubernetes specifically. For broader cloud compliance packs, the practical answer is one of the commercial platforms — Wiz, Prisma Cloud, Orca Security, or Sysdig Secure all carry the relevant evidence templates.
Free vs commercial IaC scanners
For most teams, free scanners catch 80% of the misconfigurations a commercial platform would flag. The decision to pay for a CNAPP stops being about IaC scanning quality and starts being about everything around it: dashboards, ticketing integrations, compliance reports, runtime correlation, and support SLAs.
What free OSS scanners give you
Checkov , Trivy , KICS , Kubescape , Conftest , Falco , KubeArmor , and OPA Gatekeeper all ship under permissive licences (mostly Apache 2.0). They cover scanning, custom policy authoring, CI/CD integration, and SARIF output for IDE plugins. Combined, they handle every major IaC format and most niche ones.
What the free tier misses: a centralised dashboard across multiple repos, automatic ticket creation in Jira or ServiceNow, compliance pack reporting (SOC 2, HIPAA, PCI-DSS), and any kind of vendor support. You also self-host whatever runs them — your CI runners, a Kubernetes cluster for admission controllers, an EKS or GKE node fleet for Falco.
When commercial pays off
- You already have a CNAPP budget. Wiz , Prisma Cloud , Orca Security , and Sysdig Secure include IaC scanning at no extra licence cost — meaning the marginal price is zero once you’ve signed.
- You need compliance evidence. Auditor-ready SOC 2 / ISO 27001 / PCI reports come out of the box on commercial platforms. Building the same artefact from Checkov SARIF output is a quarterly engineering project.
- You want one queue for IaC plus runtime. Commercial CNAPPs correlate a misconfigured Terraform resource with the live exposure in your AWS account, so the same finding doesn’t get triaged twice.
- You operate at multi-cloud, multi-account scale. Above 50 AWS accounts plus GCP plus Azure, the cost of self-managing dashboards usually exceeds a CNAPP licence.
Free tiers of commercial tools
A middle option exists. Snyk IaC, Aikido Security , and Wiz’s free tier (Wiz Cloud Security Scan) all give you a lightweight commercial dashboard for free — with limits on accounts scanned, repos integrated, or alerts retained. They’re the cleanest way to evaluate whether commercial dashboards justify a paid contract before you sign.
For a deeper free-tier comparison, see the best open-source IaC security tools round-up.
IaC security tools by framework
No scanner covers every IaC format equally. Picking the right tool starts with the frameworks you actually deploy. The shortlist below maps the most-used IaC formats to scanners with native support.
| Framework | Best free scanner | Best commercial scanner | Coverage notes |
|---|---|---|---|
| Terraform / OpenTofu | Checkov , Trivy | Snyk IaC, Wiz | Trivy absorbed tfsec in 2023; Checkov has the deepest policy library on Terraform-specific checks. |
| CloudFormation | Checkov , KICS | Prisma Cloud | KICS has 2,400+ queries spanning CFN intrinsic functions; Checkov treats CFN as a first-class target. |
| Kubernetes manifests | Kubescape , Trivy , KICS | Wiz , Prisma Cloud | Kubescape ships built-in CIS, NSA-CISA, and MITRE ATT&CK frameworks. |
| Helm charts | Checkov , Trivy , Kubescape | Sysdig Secure | All three free scanners render Helm before scanning, catching templated values. |
| ARM templates / Bicep | Checkov , KICS | Prisma Cloud | Native ARM support; Bicep coverage is newer but improving across the OSS scanners. |
| Pulumi / CDK | Checkov | Snyk IaC | Both scan the synthesised CFN/Terraform JSON output rather than the source TS/Python. |
| Ansible playbooks | KICS | Checkmarx One | KICS has the most mature Ansible coverage; Checkov added Ansible support in 2023. |
| OpenTofu | Checkov , Trivy | Snyk IaC | OpenTofu’s HCL syntax is a near-superset of Terraform, so existing scanners work without changes. |
| Serverless framework | Checkov | Prisma Cloud | Checkov ships dedicated serverless.yml policies covering function permissions, env vars, and event sources. |
If you run a polyglot stack — Terraform plus Helm plus Ansible — the smallest-footprint setup is Trivy plus KICS. Trivy covers Terraform, Helm, Dockerfiles, and container images in a single binary; KICS picks up the niche formats Trivy skips.
Teams running purely Kubernetes-native infrastructure (Argo CD GitOps, Helm everywhere, no Terraform) can compress further to just Kubescape plus Trivy, since Kubescape adds runtime cluster scanning that none of the static scanners offer.
Frequently Asked Questions
What is Infrastructure as Code (IaC) security?
Are all IaC security tools free?
Which IaC security tool should I use?
What IaC formats do these tools support?
Can IaC security tools replace CSPM?
What is the difference between IaC security and CSPM?
Which IaC scanner has the most policies?
Are AI-powered IaC scanners worth it?
Related IaC Security Resources
Explore Other Categories
IaC Security covers one aspect of application security tools. Browse other categories below.

Written & maintained by
Suphi CankurtEight years on the vendor side of application-security sales — thousands of evaluations and demos. I started AppSec Santa in 2022 to put that insider view to work for buyers. Independent of any vendor, paid by none, and honest about what fits whom.