GitLab DAST is the built-in dynamic application security testing tool for GitLab Ultimate. It runs as a CI/CD pipeline job, scans your deployed application for vulnerabilities, and shows results directly in merge requests.
No external tool to configure. No separate dashboard to manage.
Add a CI template, set a target URL, and DAST runs alongside your existing pipeline.
Requires GitLab Ultimate. Not available on Free or Premium tiers.
Key features at a glance
| Feature | Detail |
|---|---|
| GitLab Tier | Ultimate only (GitLab.com, Self-Managed, Dedicated) |
| Analyzer Version | DAST v5 (browser-based, unified) |
| Legacy Analyzer | Proxy-based removed in GitLab 17.3 |
| Web Scanning | Browser-based for SPAs (React, Vue, Angular) |
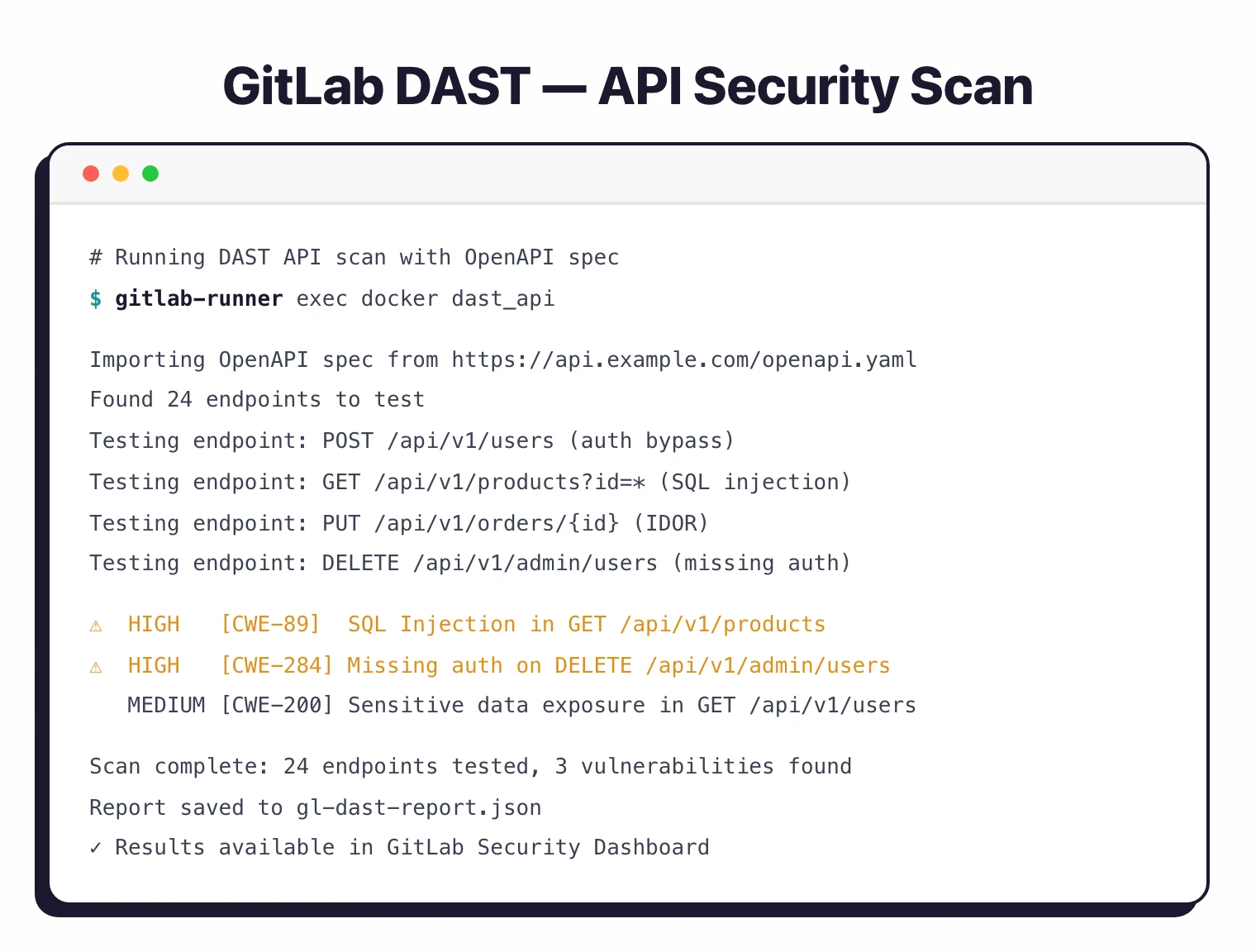
| API Scanning | REST (OpenAPI/Swagger), GraphQL, SOAP |
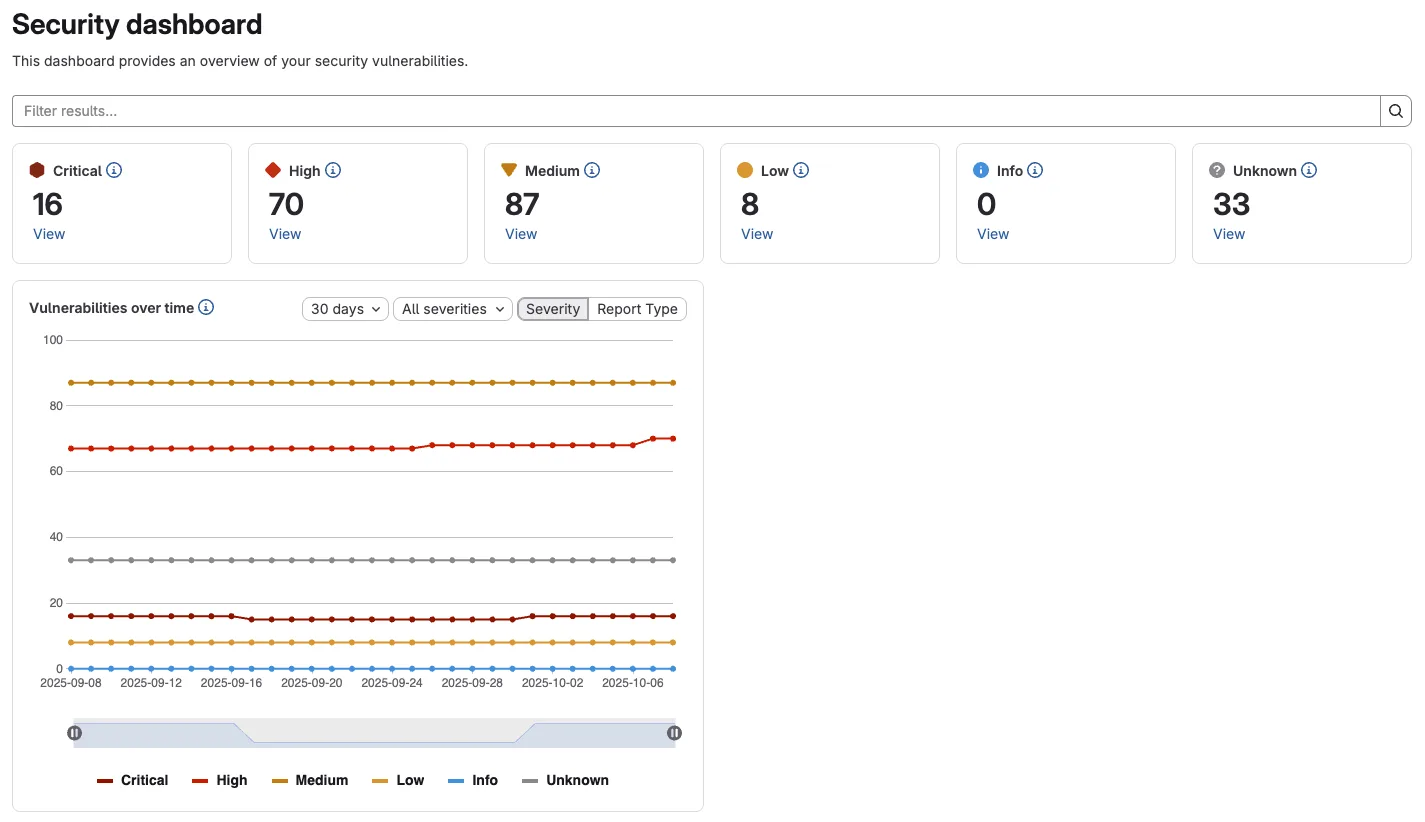
| Results Location | Merge request widget, pipeline security tab, security dashboard |
| Authentication | Form-based login, token/header auth, OAuth |
| On-Demand Scans | Yes — via UI or API, outside CI/CD pipelines |
| Scan Modes | Quick scan and full scan |
| Output | DAST report artifact (JSON) |
What is GitLab DAST?
GitLab DAST is part of GitLab’s DevSecOps platform. The scanner runs as a standard CI/CD job, testing deployed applications for SQL injection, XSS, CSRF, security misconfigurations, and other runtime flaws.
According to the OWASP Testing Guide , dynamic testing against a running application is essential for catching vulnerabilities that static analysis cannot reach, such as authentication and session management issues.
The tool is language-agnostic — it examines applications externally, so it doesn’t matter what language or framework the app is built with.
Note: The legacy proxy-based analyzer was deprecated in GitLab 16.9 and removed in 17.3. DAST version 5 uses a unified browser-based approach for all scanning. If you're on an older version, GitLab provides migration guides for both proxy-based and browser-based v4 analyzers.
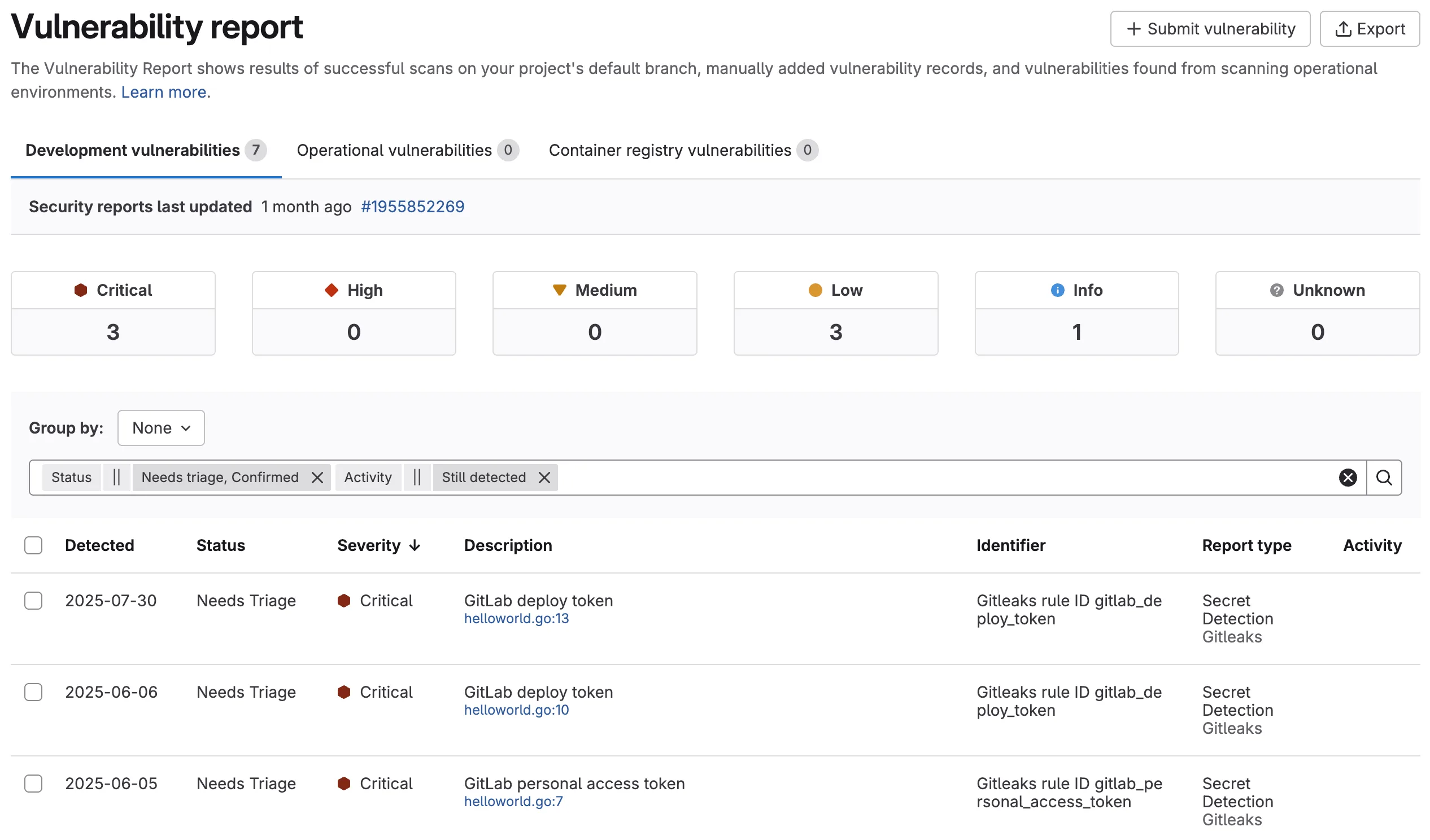
Results flow into GitLab’s security features automatically. Vulnerabilities appear in the merge request widget (highlighting new issues introduced by the MR), the pipeline security tab, and the project-level security dashboard.
Developers can review, dismiss, or create issues for findings without leaving GitLab.
Browser-based scanning
The browser-based scanner handles modern SPAs that render content via JavaScript. It executes JS, interacts with client-side routing, handles OAuth and token-based authentication, and tests API calls made by the frontend.
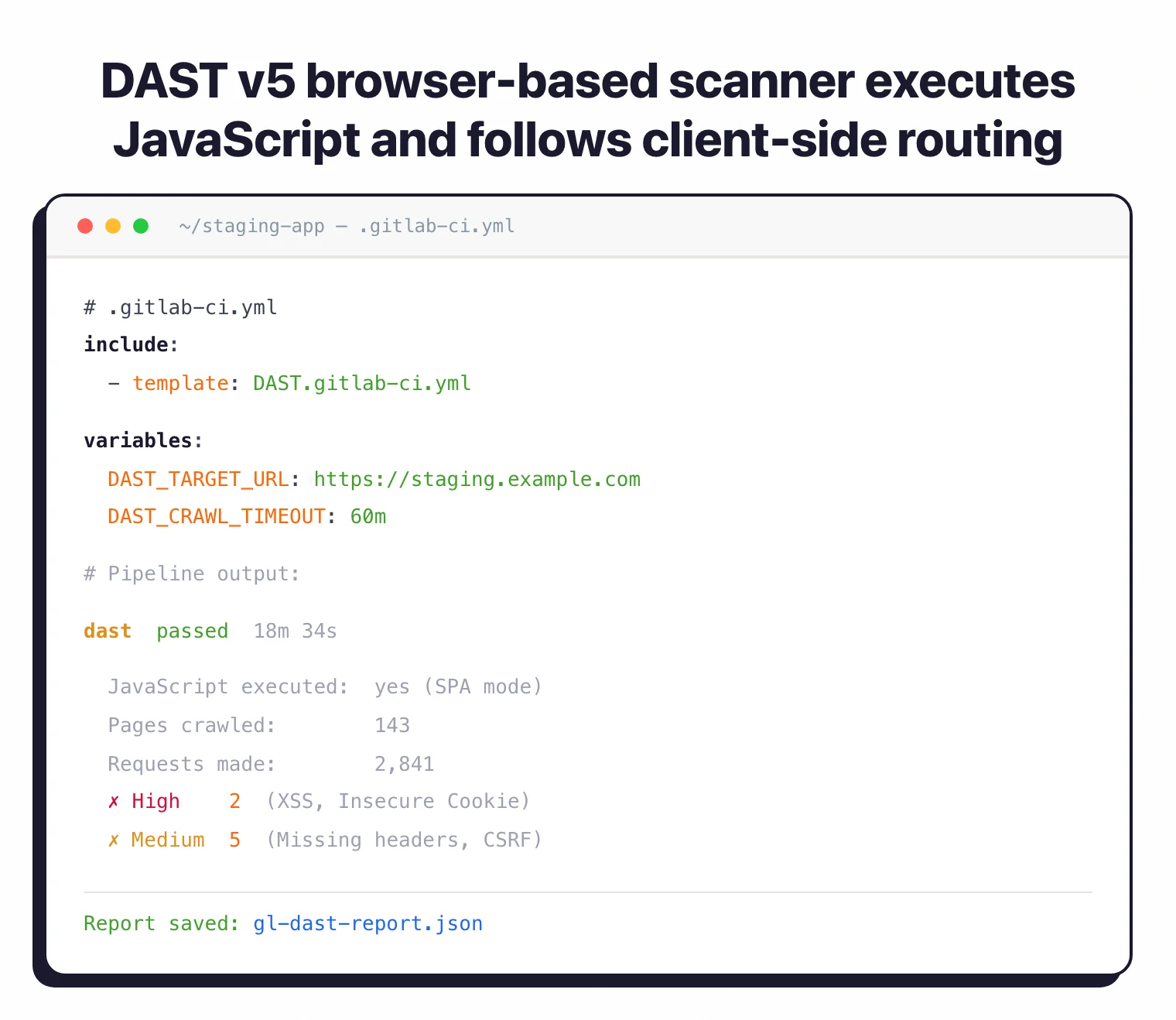
include:
- template: DAST.gitlab-ci.yml
variables:
DAST_TARGET_URL: https://staging.example.com
DAST_CRAWL_TIMEOUT: 60m
API scanning
For REST APIs, point the analyzer at your OpenAPI/Swagger spec. For GraphQL, provide the endpoint URL. SOAP is also supported.
include:
- template: DAST-API.gitlab-ci.yml
variables:
DAST_API_OPENAPI: https://api.example.com/openapi.yaml
DAST_TARGET_URL: https://api.example.com
Authenticated scanning
GitLab DAST supports form-based login, bearer tokens, and header-based auth for scanning protected pages.
variables:
DAST_TARGET_URL: https://staging.example.com
DAST_AUTH_URL: https://staging.example.com/login
DAST_AUTH_USERNAME: $DAST_USER
DAST_AUTH_PASSWORD: $DAST_PASS
DAST_AUTH_USERNAME_FIELD: username
DAST_AUTH_PASSWORD_FIELD: password
DAST_AUTH_FIRST_SUBMIT_FIELD: submit
DAST_AUTH_SUCCESS_IF_AT_URL: https://staging.example.com/dashboard
Pro tip: Run DAST scans outside your CI/CD pipeline through the GitLab UI or API — useful for ad-hoc testing of production URLs or scheduling scans without touching .gitlab-ci.yml.
How to use GitLab DAST
include: - template: DAST.gitlab-ci.yml to your .gitlab-ci.yml and set the DAST_TARGET_URL variable to your staging URL.DAST_AUTH_URL, DAST_AUTH_USERNAME, DAST_AUTH_PASSWORD, and field name variables so the scanner can test authenticated areas.What are GitLab DAST’s limitations?
A few things to know before choosing GitLab DAST:
- Ultimate only — requires the most expensive GitLab tier
- Pipeline dependency — if any concurrent security job fails, DAST results won’t appear in the pipeline security dashboard
- Limited customization — fewer tuning options than dedicated DAST tools
- No advanced features — no AI-powered testing, no business logic testing, no proof-based scanning
What does GitLab DAST integrate with?
GitLab DAST is tightly scoped to the GitLab ecosystem itself — see the DAST tools landscape when you need third-party CI/CD integration, or Invicti when you want vendor-neutral pipeline support.
When to use GitLab DAST
GitLab DAST is the obvious choice if you’re already on GitLab Ultimate. Zero integration friction — it’s a CI template and a few variables. Results show up where developers already work.
Good fit when you need:
- DAST integrated directly into GitLab CI/CD pipelines
- Vulnerability findings in merge request reviews
- Browser-based scanning for SPAs
- API security testing for REST, GraphQL, and SOAP
- Centralized security dashboard across multiple projects
- On-demand scanning for ad-hoc testing
If you’re on GitLab Free or Premium, you’ll need a standalone DAST tool . For a breakdown of how dynamic testing compares to other approaches, see the SAST vs DAST vs IAST guide.
And even on Ultimate, teams that need advanced features like business logic testing, AI-powered scanning, or proof-based verification should look at dedicated platforms like Escape or Invicti alongside or instead of GitLab DAST.
Teams on a budget might also consider Dastardly , a free CI/CD DAST scanner from PortSwigger.
Works best when combined with GitLab’s other security scanners (SAST, SCA, Container Scanning) for full pipeline coverage.
How much does GitLab DAST cost?
GitLab DAST is bundled inside GitLab Ultimate, and GitLab publishes Ultimate pricing publicly on about.gitlab.com/pricing . I’d verify the current per-seat list price there before any budgeting conversation, since GitLab updates tiering periodically.
What drives cost is the GitLab tier itself. There is no à la carte DAST license — you cannot buy DAST without Ultimate, and Free or Premium tiers do not include it at all. A 30-day Ultimate trial is available, which is the no-cost path to evaluate DAST against your own apps.
I treat GitLab DAST as a tier-bundled feature rather than a standalone DAST line item — the question is whether Ultimate makes sense across your full set of GitLab features (Compliance, Vulnerability Management, Audit Events, Free Guest Users), not just DAST in isolation. If you only need DAST and you’re on Free or Premium, a standalone tool from the DAST tools landscape will be cheaper.
What are alternatives to GitLab DAST?
If GitLab Ultimate’s per-seat pricing or the DAST scope does not fit, these are the alternatives I’d weigh in the DAST tools landscape :
- ZAP — The OWASP scanner that GitLab DAST is built on. Free and open source, supports authenticated scans and API testing. Best when you want the underlying engine without the GitLab tier overhead.
- Invicti — Enterprise DAST with proof-based scanning that integrates into GitLab CI/CD via REST API. Better fit when you need broader vulnerability coverage and ASPM-style rollups across many repositories.
- Burp Suite Enterprise — Scaled DAST around the Burp engine with PR-blocking gates. Verify pricing on portswigger.net before budgeting. Pairs well with developer-led GitLab pipelines.
- StackHawk — CI-native DAST around the ZAP engine with stronger developer ergonomics than vanilla GitLab DAST. Better when engineering wants more control over scan tuning and PR-blocking gates.
- Bright Security — Developer-first DAST with low-false-positive scanning. Worth evaluating when you want richer API and SPA coverage than GitLab DAST currently delivers.








