Frida is a dynamic instrumentation toolkit developed by Ole André Vadla Ravnås. With over 19,700 GitHub stars, it is widely used for runtime mobile application security testing and reverse engineering — see my mobile app pentesting guide for the broader workflow Frida slots into, and pair it with Objection when you want a higher-level CLI on top.
The framework works by injecting the QuickJS JavaScript engine into running processes, enabling powerful inspection and manipulation capabilities.
Security researchers rely on Frida for mobile pentesting because it provides deep visibility into app internals. You can hook any function, spy on cryptographic operations, trace private application code, and bypass security controls—all without needing the app’s source code.
What is Frida?
Frida is a free and open source dynamic code instrumentation framework that allows developers, reverse engineers, and security researchers to analyze and modify the behavior of running applications. At its core, Frida injects a JavaScript engine into the target process, letting you write scripts that interact with the app at runtime.
The toolkit supports multiple platforms including Android, iOS, Windows, macOS, Linux, FreeBSD, and even embedded systems like QNX. This cross-platform capability makes it an essential tool for mobile security professionals who need to test apps across different operating systems.
Function hooking is one of Frida’s most powerful features. You can intercept calls to specific functions, examine or modify their arguments, change return values, or completely replace the function’s behavior by rewriting machine code at runtime.
This enables techniques like bypassing root detection, intercepting encrypted API calls, and manipulating memory to expose hidden functionality.
Key features
Dynamic Analysis Capabilities
Frida excels at runtime manipulation, letting you observe live application behavior that static analysis cannot reveal. You can trace function calls as they happen, monitor API interactions, and identify vulnerabilities that only surface during execution.
This includes uncovering insecure data storage, weak encryption implementations, and authentication bypasses.
Mobile Pentesting Applications
For Android testing, Frida is most powerful on rooted devices where it can instrument any app and system service. On non-rooted devices, you can still use frida-gadget by embedding it in debuggable applications. The framework supports all Android versions from 4.4 onwards.
On iOS, Frida works in both jailed and jailbroken modes. Jailbroken devices offer the most comprehensive access, enabling you to instrument system services and apps with minimal effort.
The tool is extensively documented in the OWASP Mobile Application Security Testing Guide (MASTG).
OWASP MASTG Dynamic Analysis
Frida is the canonical tool the OWASP MASTG cites for dynamic instrumentation tests. It maps directly to the MASTG-TEST-0023 / 0024 / 0050 series — runtime hooking, dynamic analysis of authentication and crypto, and the resilience tests that need to observe a running process.
If your assessment plan references those test IDs, Frida is usually what you reach for to execute them, paired with a rooted Android device, a jailbroken iOS test phone, or — on stock devices — frida-gadget injected into a debuggable build.
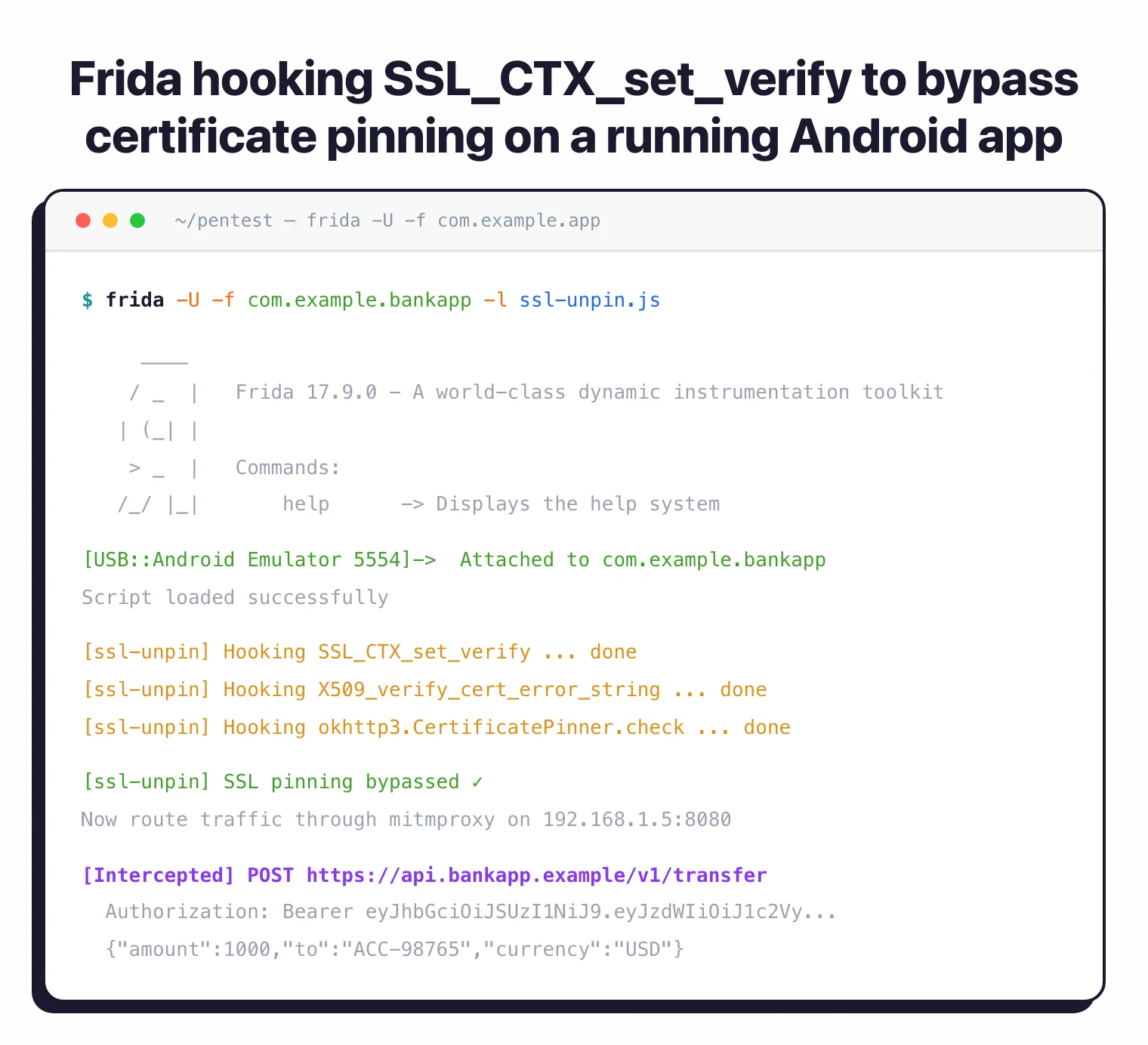
SSL Pinning Bypass Workflow
The most-used Frida pattern in the wild is SSL pinning bypass. The flow: attach Frida to the target app, load a community pinning-bypass script (objection’s android sslpinning disable or one of the curated frida-scripts equivalents), and replace the OS or library-level pinning checks at runtime so an upstream proxy like mitmproxy or Burp can decrypt traffic.
This is the same loop that powers most banking-app pentests today. Pair it with frida-gadget when you cannot root the device, and with Objection when you want a higher-level wrapper around the same primitives.
Community and Ecosystem
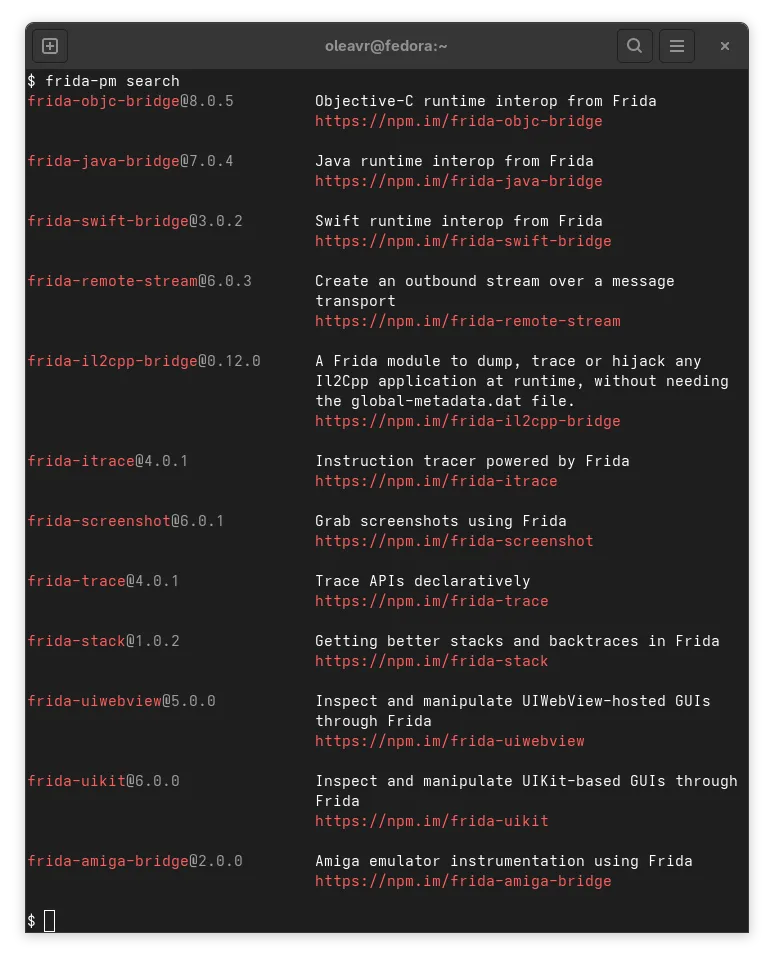
The Frida ecosystem includes thousands of ready-made scripts for common tasks like bypassing root detection, SSL unpinning, and extracting data from popular apps. Projects like frida-tools provide command-line utilities, while frameworks like Objection build higher-level capabilities on top of Frida’s core functionality.
Recent developments include IL2CPP bridges for Unity game hacking, FridaContainer for modular script management, and integrations with popular security testing frameworks. The community actively maintains scripts and tools through 2026.
Frida 17.9.0 (March 2026) introduced an eBPF-based spawn gater for Linux, improving process spawn monitoring without kernel module dependencies. The same release added override_option() for host sessions, giving researchers finer control over session configuration. A quick follow-up in 17.9.1 fixed a semver pre-release overflow bug.
Integration with Testing Workflows
Frida integrates seamlessly into mobile security testing workflows. You can combine it with mitmproxy for traffic inspection, use it alongside Objection for automated testing, and integrate scripts into CI/CD pipelines for continuous security validation.
When to use Frida
Strengths:
- Widely used tool with extensive documentation and community support
- Flexible runtime code manipulation and instrumentation
- Cross-platform support covers virtually all mobile testing scenarios
- JavaScript API is accessible to testers without deep assembly knowledge
- Active development with regular updates and new features
- Free and open source with permissive licensing
- Extensive script library accelerates common testing tasks
Limitations:
- Requires root/jailbreak access for full system-level testing capabilities
- Learning curve for understanding hooking concepts and JavaScript API
- Apps with anti-tampering protections may detect Frida’s presence
- Performance overhead when instrumenting complex applications
- Some advanced techniques require low-level knowledge of process internals
Best for: Frida is ideal for security researchers and pentesters who need comprehensive runtime analysis of mobile applications, especially when testing authentication mechanisms, encryption implementations, and bypassing client-side security controls.
Frida Alternatives
Frida is the de-facto standard, but a handful of tools cover adjacent or complementary scope. The closest alternatives:
- Objection . Built on top of Frida, exposes the most-used hooks (root detection bypass, SSL pinning, keystore dump, jailbreak detection) as one-line commands. Use Objection when you want speed and Frida directly when you need custom JavaScript.
- Xposed Framework. Android-only, requires root. Hooks at the Zygote level so it survives across app restarts and reaches deeper system services than Frida’s per-process injection. The trade-off is no iOS support and a heavier device-side footprint.
- Cydia Substrate. Historical iOS hooking framework. Largely superseded by Frida on modern iOS, but still referenced in legacy jailbreak research and older MASTG-style runbooks.
- QBDI. Quarkslab’s low-level dynamic binary instrumentation library. More C/C++-oriented than Frida’s JavaScript API; useful when you need fine-grained instruction-level instrumentation rather than function hooking.
- Brida + Burp. Bridges Frida’s runtime hooks into Burp Suite. Useful when the question is API-level rather than process-level — Brida lets Burp invoke Frida hooks during proxying without writing a standalone Frida client.
For a wider view, see my mobile security tools hub and mobile app pentesting guide .
Frida Pricing and Licensing
Frida is fully free and open source. The project is released under the wxWindows Library Licence — an OSI-approved, BSD-style permissive license — which means you can use Frida in commercial pentesting engagements, internal security tooling, or research without paying license fees or sharing modifications.
There is no paid tier, no enterprise SKU, and no commercial fork from the maintainers. Some training providers and consultancies sell paid courses that teach Frida, but those are not Frida itself. The only ongoing cost is your time learning the JavaScript API and writing or curating hook scripts.
Getting started
pip3 install frida-tools to install the CLI utilities and Python bindings./data/local/tmp/, and run it as root. On iOS, install Frida via Cydia on jailbroken devices.frida -U -n com.example.app to attach to a process over USB, or frida -U -f com.example.app to spawn and instrument it from launch.frida -U -l hook.js -n com.example.app to inject your script into the running process.Combine Frida with Ghidra for static analysis, Jadx for decompiling Android apps, and Objection for automated mobile security testing.