FOSSA is an enterprise SCA platform that treats license compliance as a first-class concern, not an afterthought.
While most SCA tools focus on vulnerability detection and tack on license checking, FOSSA was built around the compliance workflow from the start.
The platform scans 17+ languages across 20+ build systems and claims 99.8% accuracy on license detection. Its policy engine was designed with Heather Meeker, one of the leading open-source licensing attorneys.
Companies like Uber, Verizon, and Atlassian use it to manage open-source risk across their portfolios.
FOSSA also handles vulnerability scanning, SBOM generation, binary composition analysis, and reachability-based prioritization. The CLI is open-source (written in Haskell) with over 5.8 million downloads.
What is FOSSA?
FOSSA sits between your codebase and your legal/compliance team. It scans dependencies, detects licenses, flags conflicts, generates attribution reports, and enforces policies.
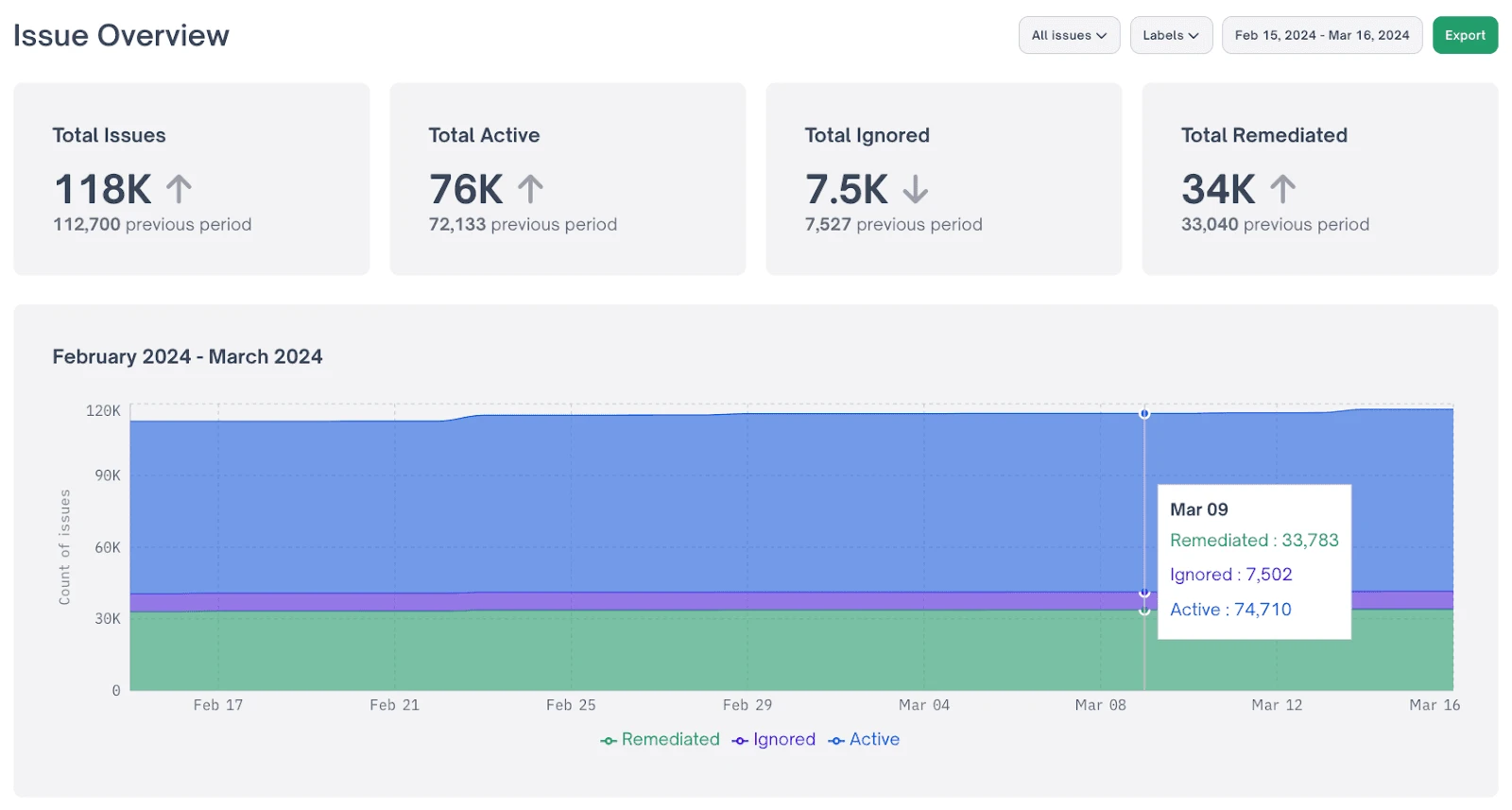
The vulnerability scanning layer adds reachability analysis and multi-source intelligence (NVD, GitHub Advisories, OSV, plus FOSSA’s own database).
Key features
License compliance
This is where FOSSA stands apart. The platform does full-text license analysis, not just filename matching.
It detects modified licenses, dual-licensed components, and non-standard terms that simpler tools miss. The claimed accuracy rate is 99.8%.
You can define organizational policies around which licenses are acceptable. The policy engine supports three rule types:
- Deny – Block the build if a dependency uses this license
- Flag for Review – Pause for manual approval
- Approve – Allow automatically
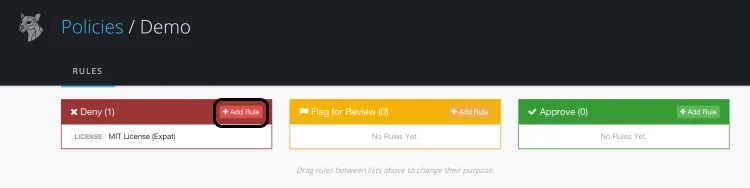
FOSSA ships with pre-built standard policies and lets you create custom ones. Rules can target specific licenses, projects, or the entire organization.
If you distribute commercial software that includes GPL-licensed components, you may be obligated to release your source code. FOSSA catches these conflicts before they become legal problems.
The policy engine was co-designed with Heather Meeker, a partner at Tech Law Partners and one of the most cited open-source licensing attorneys.
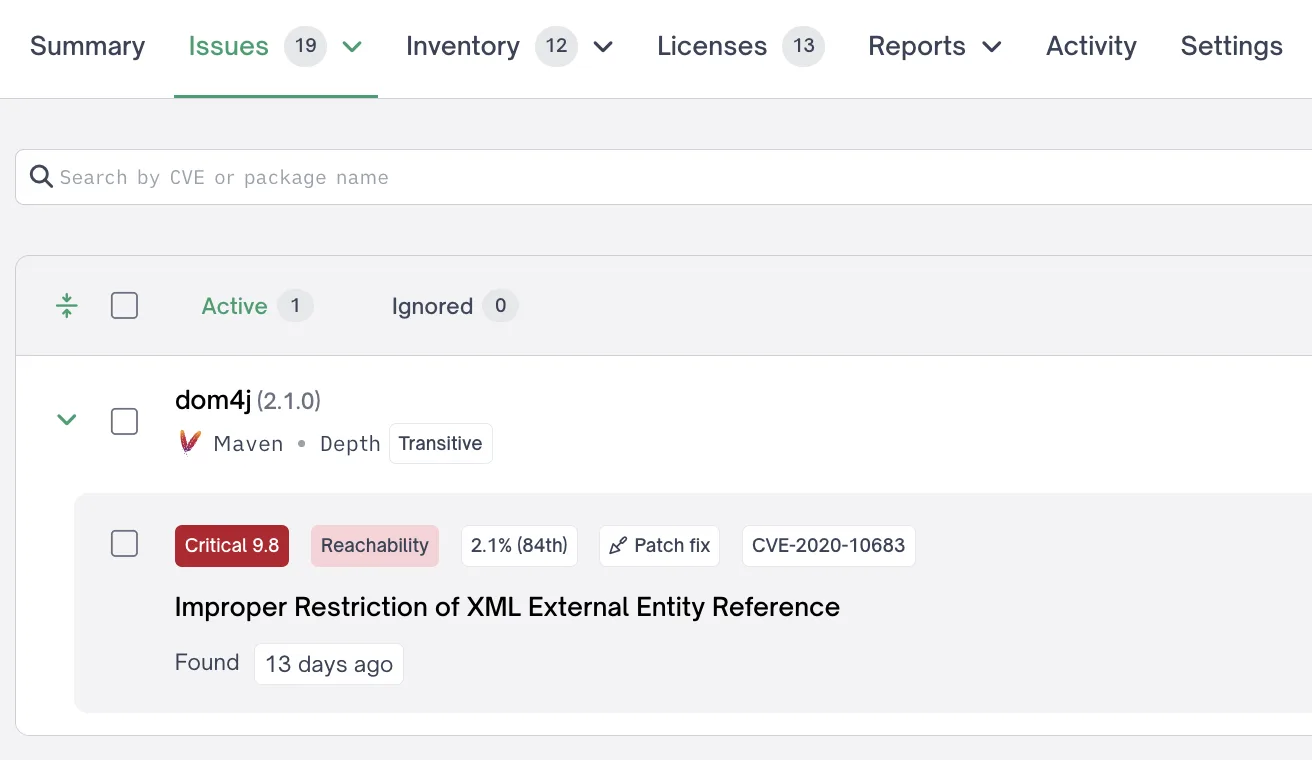
Vulnerability scanning with reachability
FOSSA’s vulnerability scanning pulls from NVD, GitHub Security Advisories, OSV, and a proprietary database.
It includes EPSS scoring and reachability analysis that traces whether your code actually calls the vulnerable function in a dependency.
Build-level reachability is generally available; function-level reachability is in beta for Maven projects.
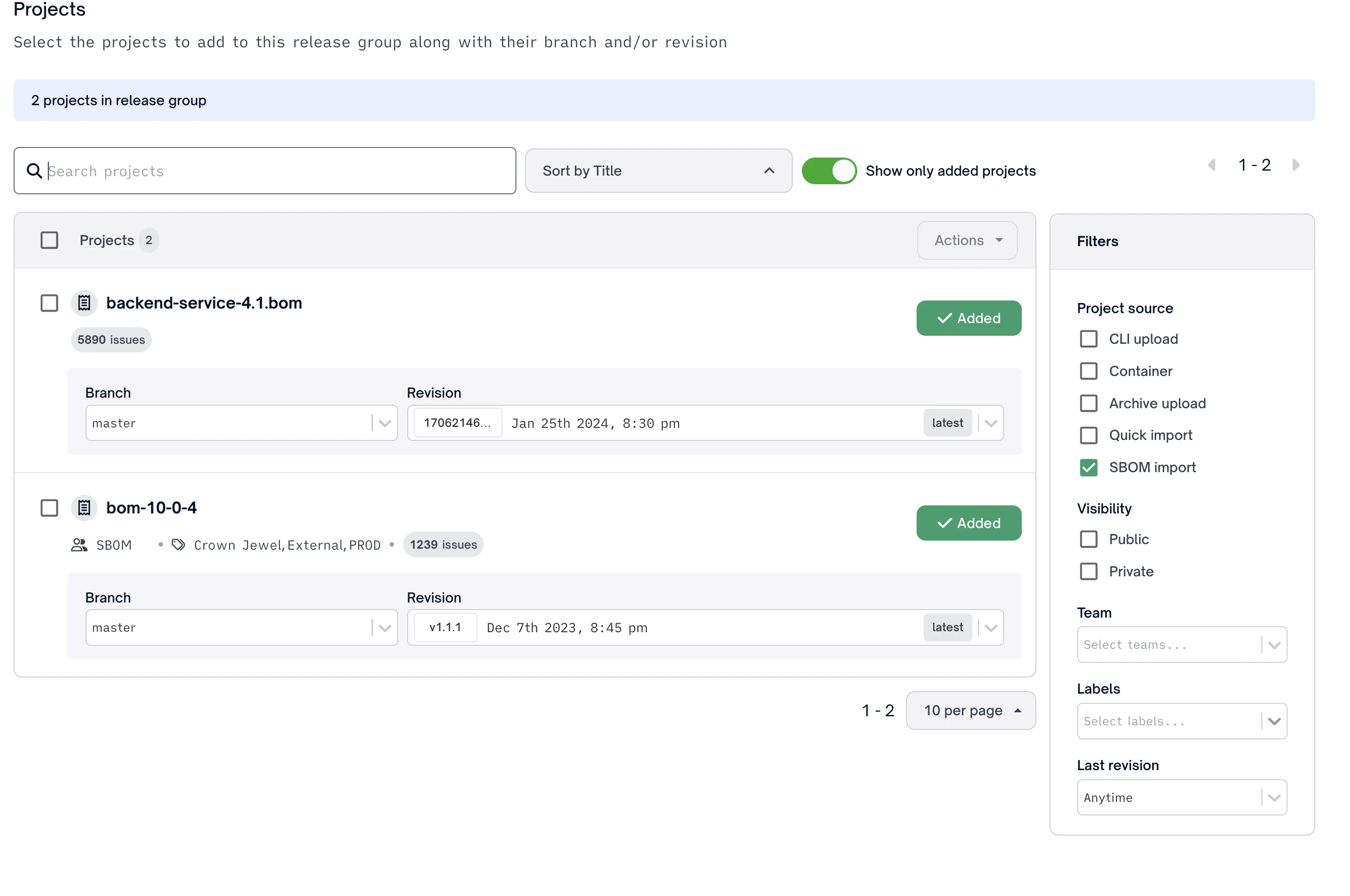
SBOM generation and portal
FOSSA generates SBOMs in SPDX and CycloneDX formats with complete dependency reporting to unlimited nesting depth.
The SBOM Portal is a hosted distribution point where you share SBOMs with customers, auditors, or partners using access tokens. You can import third-party SBOMs and track versions over time.
Binary composition analysis
For situations where you don’t have source code access, FOSSA can scan compiled binaries (JAR files, DLLs, EXEs) using fingerprinting. This is useful for third-party vendor assessments and supply chain verification.
fossabot AI agent
FOSSA recently added an AI agent called fossabot that handles strategic dependency updates. It analyzes upgrade paths, considers CI signals, and plans updates that minimize breakage.
Getting started
curl -H 'Cache-Control: no-cache' https://raw.githubusercontent.com/fossas/fossa-cli/master/install-latest.sh | bashexport FOSSA_API_KEY=<your-key> && fossa analyze scans your project. fossa test checks it against your policies.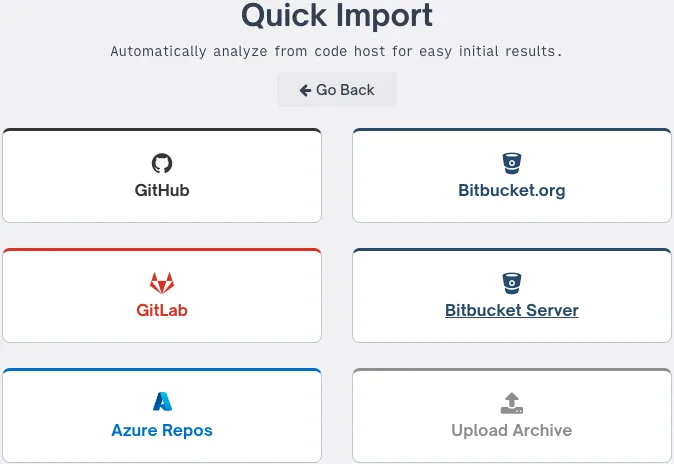
# Install FOSSA CLI (macOS/Linux)
curl -H 'Cache-Control: no-cache' https://raw.githubusercontent.com/fossas/fossa-cli/master/install-latest.sh | bash
# Install via Homebrew
brew install --cask fossa
# Set API key
export FOSSA_API_KEY=<your-key>
# Analyze project
fossa analyze
# Run compliance tests
fossa test
CI/CD integration
GitHub Actions
- name: FOSSA Scan
uses: fossas/fossa-action@main
with:
api-key: ${{ secrets.FOSSA_API_KEY }}
GitLab CI
fossa-scan:
stage: security
script:
- curl -H 'Cache-Control: no-cache' https://raw.githubusercontent.com/fossas/fossa-cli/master/install-latest.sh | bash
- fossa analyze
- fossa test
variables:
FOSSA_API_KEY: $FOSSA_API_KEY
rules:
- if: $CI_PIPELINE_SOURCE == "merge_request_event"
- if: $CI_COMMIT_BRANCH == $CI_DEFAULT_BRANCH
Supported languages
| Language | Package Managers |
|---|---|
| JavaScript | npm, yarn, pnpm, Bower |
| Java/Kotlin/Scala | Maven, Gradle, sbt |
| Python | pip, Poetry, Pipenv, Conda |
| .NET (C#/F#/VB) | NuGet, Paket |
| Go | Go modules, Glide, Godeps |
| Ruby | Bundler |
| PHP | Composer |
| Rust | Cargo |
| Swift | CocoaPods, Swift PM, Carthage |
| Elixir | Mix |
| Erlang | Rebar3 |
| Haskell | Stack, Cabal |
| Clojure | Leiningen |
| Dart | Pub |
| Perl | CPAN |
| Fortran | fpm |
| C/C++ | Various |
Integrations
When to use FOSSA
FOSSA is the right choice when license compliance is a hard requirement, not a nice-to-have.
That typically means companies that distribute commercial software containing open-source components, sell to enterprise customers with SBOM requirements, or operate in regulated industries.
Strengths:
- 99.8% license detection accuracy with full-text analysis
- Policy engine built with leading OSS attorneys
- SBOM Portal for centralized distribution and sharing
- Binary composition analysis for vendor assessments
- Broad language coverage: 17+ languages, 20+ build systems
Limitations:
- License compliance features are the main differentiator; vulnerability scanning is solid but not as deep as Snyk’s
- Enterprise features require paid plans; median annual contract: $25,500 (range: $13,800–$67,300)
- CLI is Haskell-based, which can make custom integrations harder to contribute to
How it compares:
| vs. | Key difference |
|---|---|
| Snyk Open Source | Snyk is stronger on vulnerability detection and automated fix PRs. FOSSA is stronger on license compliance and attribution reports. |
| Black Duck | Both are enterprise-grade with strong license compliance. Black Duck has a larger knowledge base (6M+ projects) but FOSSA has a more modern UX and SBOM Portal. |
| Dependabot | Dependabot is free and GitHub-native but has no license compliance features. FOSSA fills the compliance gap. |
Learn more in our guides: What is SCA?, What is an SBOM?, and open-source license compliance.
Frequently Asked Questions
What is FOSSA used for?
Does FOSSA have a free tier?
How does FOSSA compare to Snyk Open Source?
What makes FOSSA different from other SCA tools?
What SBOM formats does FOSSA support?
* Pricing data from Vendr — anonymized contract values from real buyer transactions.