Fortify WebInspect Agent adds IAST capabilities to the Fortify WebInspect DAST scanner. It instruments Java and .NET applications during dynamic scans to provide file names, line numbers, and stack traces for each vulnerability.
The agent is included free with WebInspect and WebInspect Enterprise licenses. It is also available through Fortify on Demand SaaS.
What is Fortify WebInspect Agent?
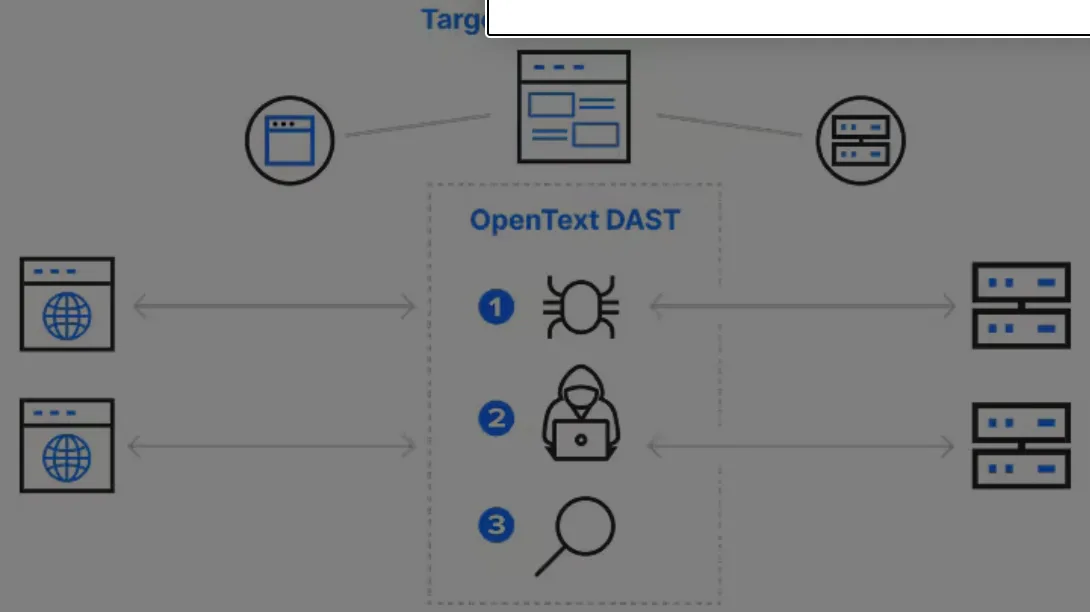
The WebInspect Agent transforms Fortify WebInspect from a pure DAST scanner into a hybrid DAST+IAST solution. While WebInspect attacks the application externally, the agent monitors code execution internally.
This combination means developers get specific file-and-line references rather than generic HTTP-level descriptions.
Key Features
| Feature | Details |
|---|---|
| Supported Languages | Java, .NET |
| Licensing | Included with WebInspect and WebInspect Enterprise |
| SaaS Option | Available through Fortify on Demand |
| Java Deployment | JVM agent argument |
| .NET Deployment | IIS module or Windows installer |
| Attack Validation | Confirms payloads reach vulnerable code paths |
| CAPTCHA Handling | Bypasses CAPTCHA at application level |
| Cross-Tool Correlation | Integrates with Fortify SCA static findings |
Code-Level Vulnerability Reporting
When the agent detects a vulnerability during a scan, it captures the complete execution context: source file name and path, line number where the vulnerability occurs, full stack trace showing the call chain, and variable values at the point of exploitation.
This detail eliminates the guesswork that typically follows DAST-only scans.
Attack Validation
The agent validates that attacks launched by WebInspect actually reach vulnerable code paths. If a potential vulnerability is blocked by a web application firewall, input validation, or other defensive layer before it reaches vulnerable code, the agent confirms the finding is a false positive.
Integration with Fortify Ecosystem
Fortify is now part of OpenText, following the acquisition of Micro Focus in 2023. The agent works within the broader OpenText Fortify ecosystem:
- Fortify WebInspect — DAST scanning with IAST enhancement
- Fortify SCA — static analysis correlation
- Fortify Software Security Center — centralized reporting
- Fortify on Demand — SaaS delivery option
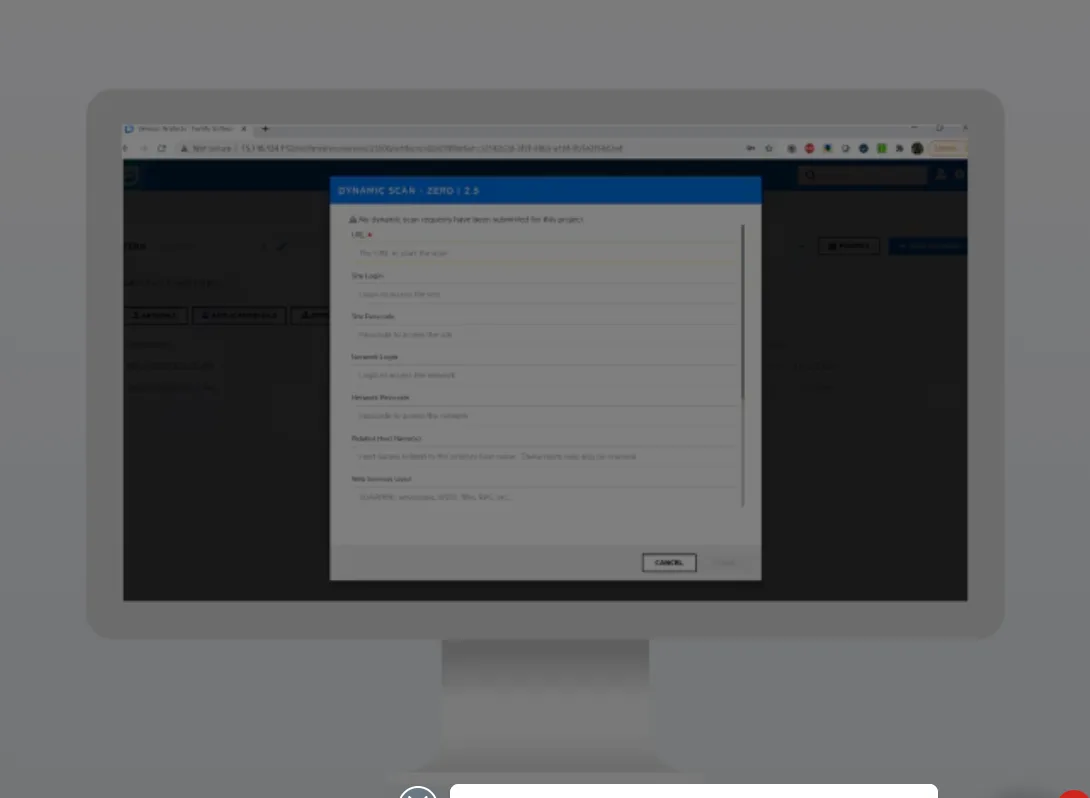
Getting Started
-javaagent JVM argument. For .NET, install the IIS module via the provided Windows installer. No source code changes needed.When to Use Fortify WebInspect Agent
The WebInspect Agent makes sense whenever you already run Fortify WebInspect scans and want more actionable results. There is no extra licensing cost.
The agent is particularly valuable for Java and .NET enterprise applications where WebInspect is already part of the security testing strategy. If you need IAST for languages beyond Java and .NET, consider Contrast Assess or Seeker IAST.