Fluid Attacks combines DAST, SAST, SCA, and penetration testing in a single platform. Automated scanners find the bugs.
Their team of ethical hackers confirms the critical ones are real.
This two-layer approach — machine scanning plus human verification — is the main selling point. False positive rates stay very low because a person has actually validated exploitability before the finding reaches your dashboard.
The company is based in Colombia, became a CVE Numbering Authority in 2021, and their CLI tool is CASA tier 2 approved for Google Play compliance.
Key features at a glance
| Feature | Detail |
|---|---|
| Testing Methods | DAST, SAST, SCA, PTaaS, secure code review |
| SAST Languages | Java, Python, JS, TS, Go, Ruby, PHP, C#, C/C++, Kotlin, Swift, Scala |
| False Positive Approach | Deterministic detection + human expert verification |
| CVE Authority | CNA status since 2021 — can assign CVE identifiers |
| CASA Compliance | Tier 2 approved for Google Play requirements |
| AI Fix Suggestions | Language and framework-aware remediation guidance |
| API | GraphQL-based API for programmatic access |
| IDE Plugins | VS Code, IntelliJ, Cursor |
| Connectivity | Cloud (HTTPS/SSH), Egress (static IP), Connector (Cloudflare ZTNA) |
| Severity Scoring | CVSSF (proprietary metric beyond standard CVSS) |
What is Fluid Attacks?
Most DAST tools are fully automated — you point them at a target, they scan, they report. Fluid Attacks takes a different approach by adding human verification on top of automated scanning.
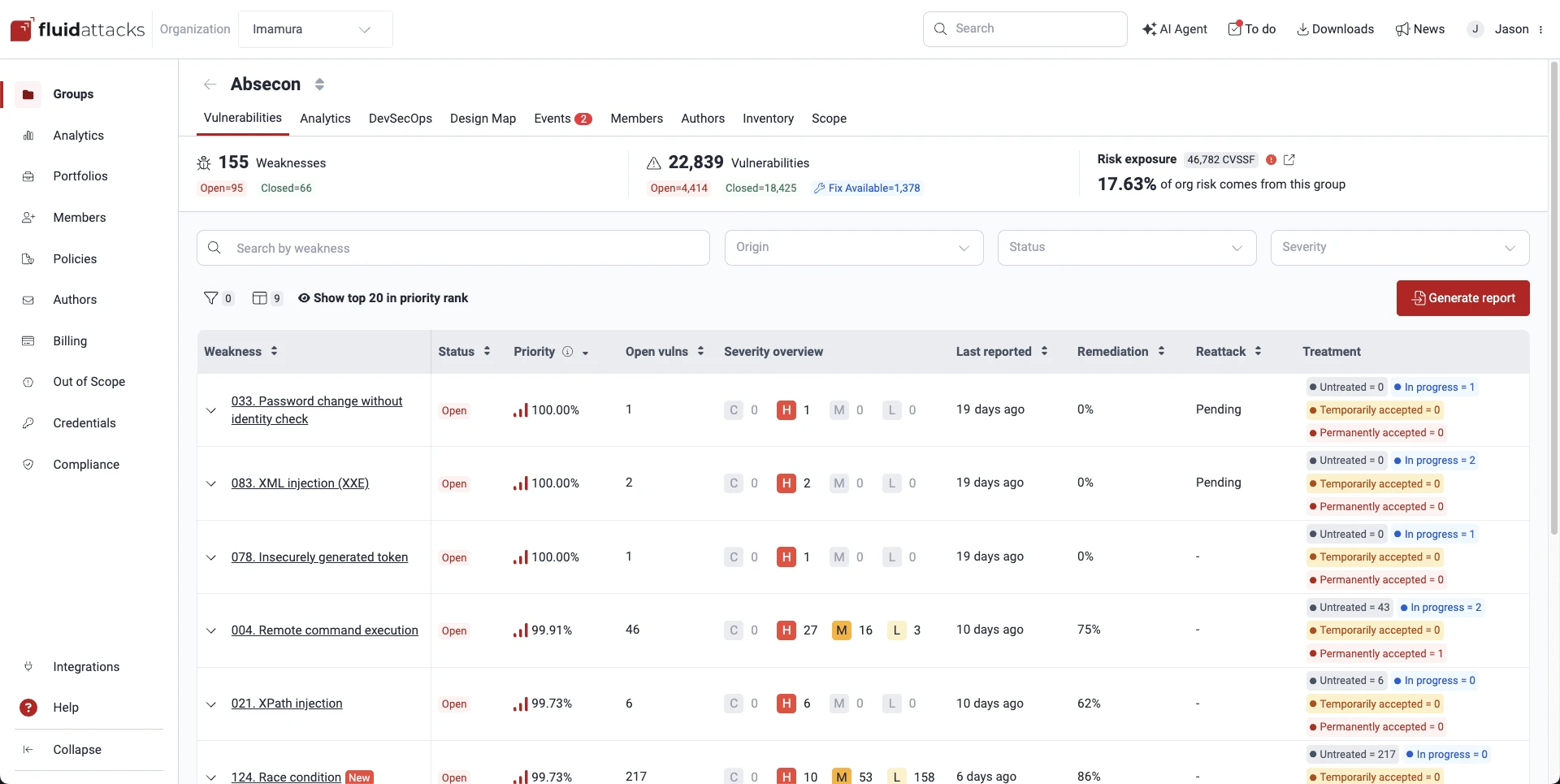
The automated layer runs DAST against running applications, SAST against source code in 13 languages, and SCA against your dependency tree. Findings from all three scanners land in one dashboard with deduplication built in.
The human layer is where it gets interesting. Fluid Attacks’ team of certified ethical hackers reviews critical findings, confirms exploitability, and weeds out false positives.
They also run continuous penetration testing alongside the automated scans.
Deterministic detection patterns trigger only on confirmed vulnerabilities. Human verification adds a second filter.
When a finding hits your dashboard, it’s almost certainly real.
Multi-methodology testing
All scan types run through one platform. DAST probes running applications with targeted attack patterns.
SAST reviews source code in 13 languages. SCA checks open-source dependencies for known vulnerabilities and license issues.
The OWASP Testing Guide recommends combining multiple testing methodologies because each catches different vulnerability classes — DAST finds runtime issues, SAST catches code-level flaws, and SCA surfaces vulnerable dependencies.
Results from all three appear in a single dashboard. Duplicate findings across methodologies get merged automatically, so you don’t waste time triaging the same bug reported by two different scanners.
Connectivity options
Fluid Attacks supports three ways to reach your applications:
- Cloud: HTTPS/SSH encrypted connections with OAuth, SSH, or HTTPS authentication
- Egress: Cloudflare-based static IP whitelisting for firewall rules
- Connector: Zero Trust Network Access via Cloudflare Tunnel for private network testing
The Connector option is worth noting — it lets Fluid Attacks scan internal applications without opening inbound firewall ports.
How to use Fluid Attacks
CI/CD integration
Fluid Attacks integrates with GitLab, Azure DevOps, and other CI/CD platforms. The pipeline can break builds when findings exceed your severity threshold.
# Using the Fluid Attacks Docker image
docker run --rm -v $(pwd):/code fluidattacks/cli:latest \
skims scan /code/config.yaml
Fluid Attacks primarily works through their platform for continuous scanning and human verification. The CLI tool (skims) takes a YAML configuration file that defines scan targets and rules.
For CI/CD integration, connect your repositories directly through the Fluid Attacks platform, which handles build-breaking policies and finding deduplication across scan types.
Integrations
When to use Fluid Attacks
Fluid Attacks makes sense when you want automated scanning verified by actual humans. The combination eliminates most false positives, but it costs more than pure-automation tools and the human review adds time to the triage cycle.
Good fit when you need:
- Multi-methodology testing (DAST + SAST + SCA) in one place
- Human expert verification of critical findings
- Very low false positive rates
- Continuous penetration testing alongside automated scanning
- CASA tier 2 compliance for Google Play
- CVE-level vulnerability research support
Teams that prioritize speed over accuracy, or those on a tight budget, may prefer fully automated DAST tools like StackHawk or ZAP.
For a comparison of testing approaches, see the guide on SAST vs DAST vs IAST. Fluid Attacks is for organizations willing to pay more for higher confidence in findings.
Teams focused purely on API security might also consider Escape, which specializes in business logic and BOLA detection.