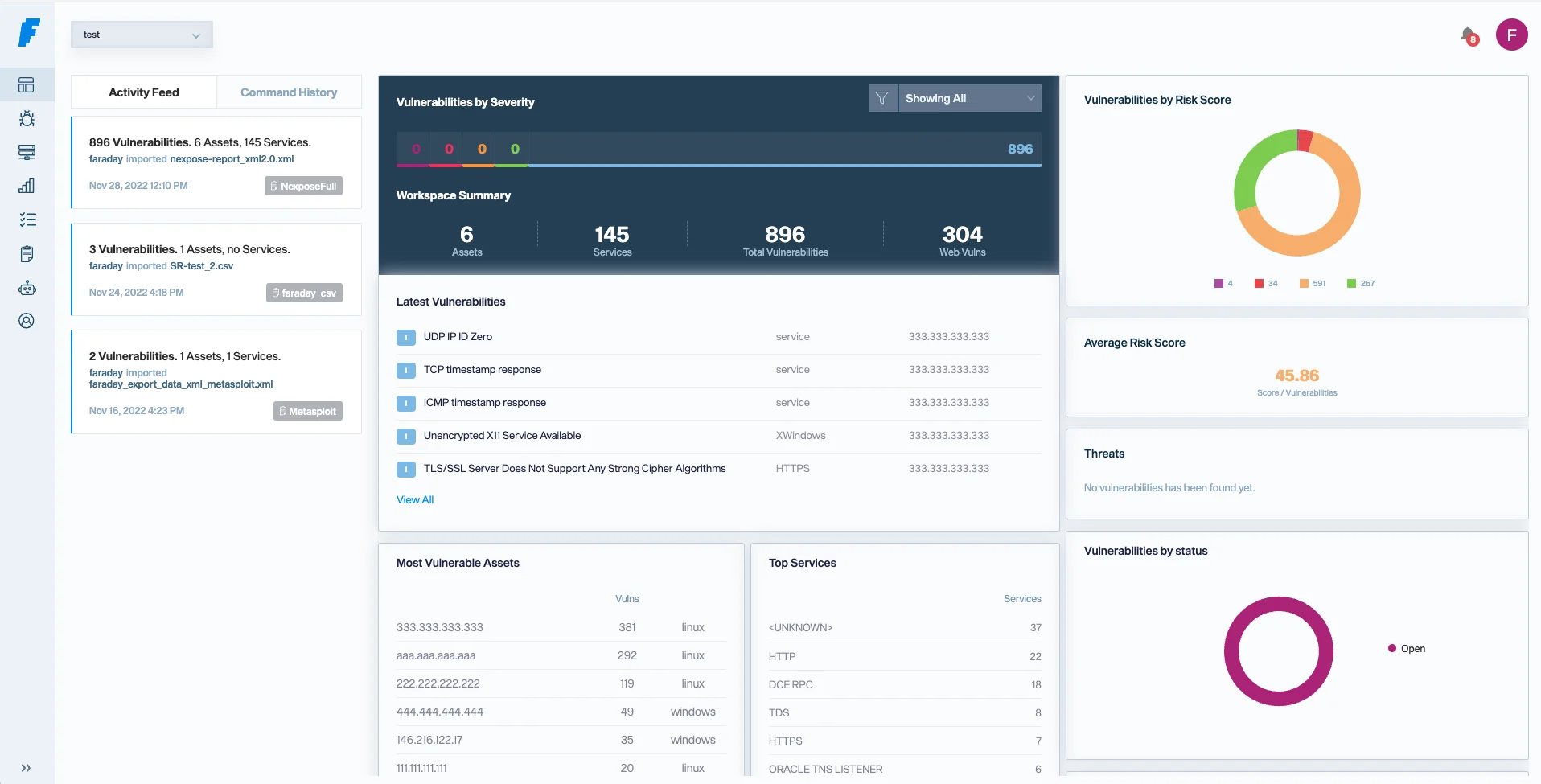
Faraday is an open-source vulnerability management platform with 6.2k GitHub stars and 1k forks. It orchestrates 80+ security tools, normalizes their output, and deduplicates findings into a single management interface.
The company behind Faraday, Infobyte, has been around since 2004. Headquartered in Miami with a research lab in Buenos Aires.
Customers include Accenture, Volkswagen, Telefonica, Santander, BBVA, HSBC, KPMG, Lufthansa, AT&T, and Vercel.
GitHub: infobyte/faraday | Latest Release: v5.19.0 (January 2026)
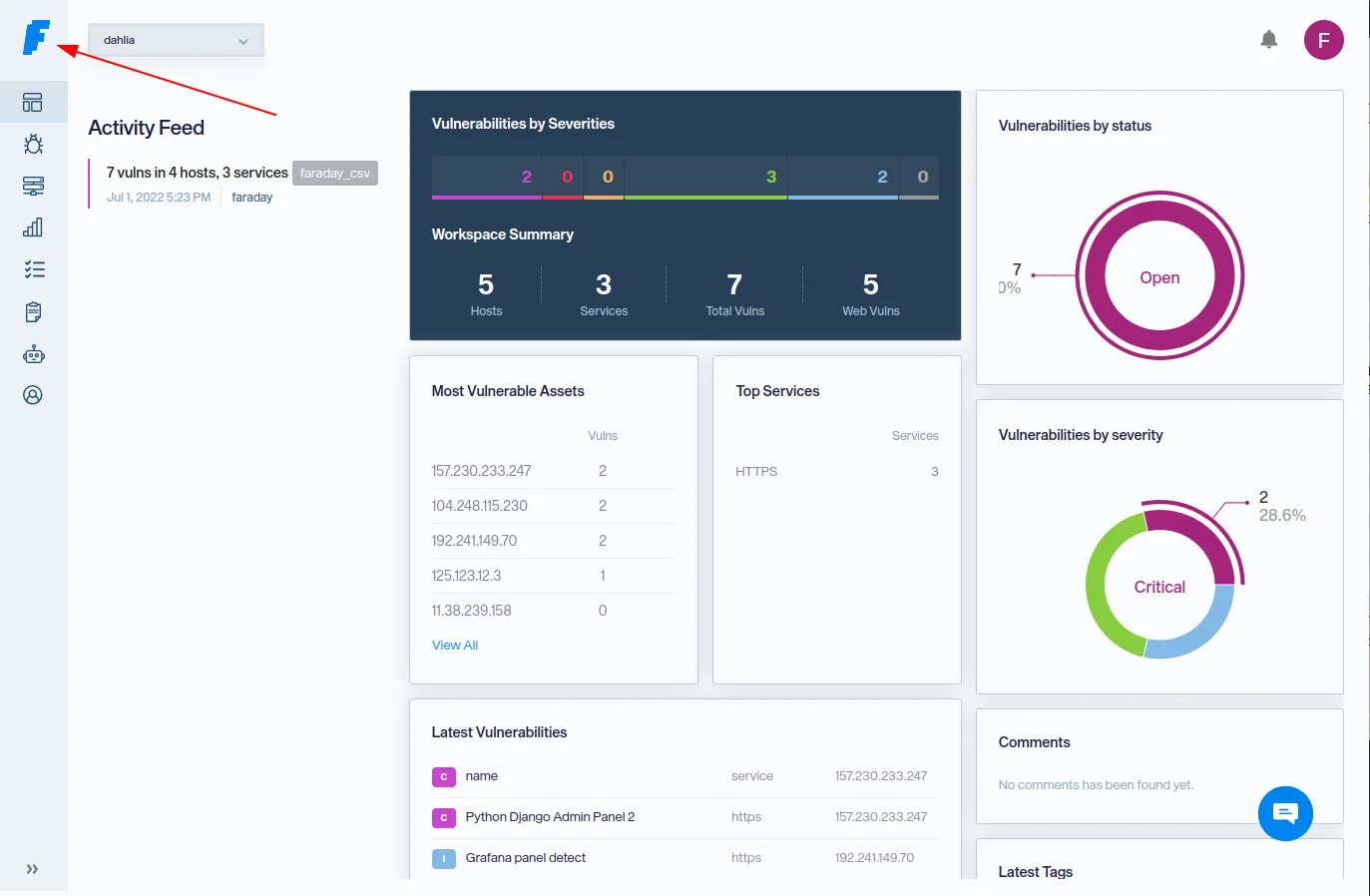
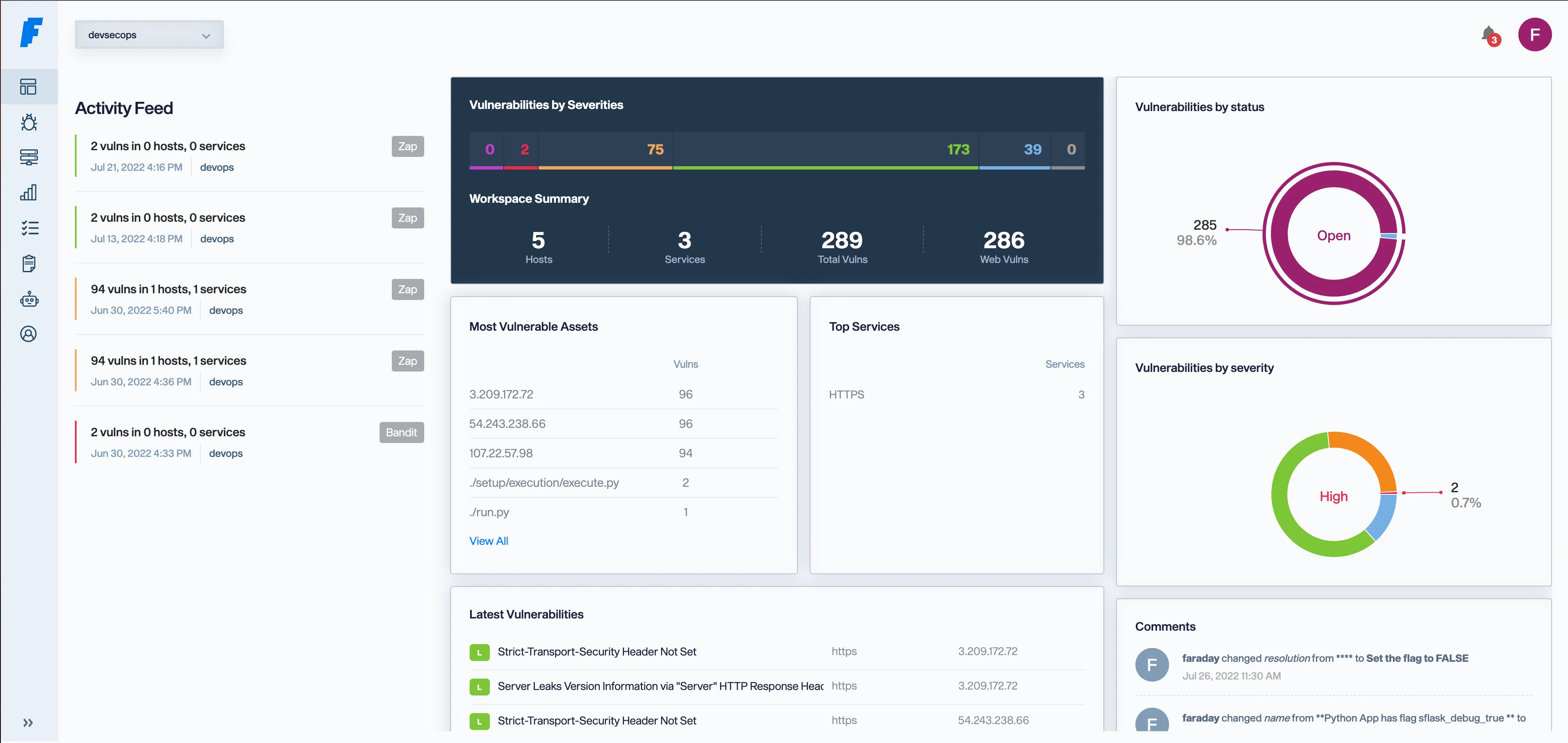
I open Faraday when I am running a multi-tool pentest and need one shared workspace. It ingests output from Nmap, Nessus, Burp, and a few dozen other scanners, deduplicates findings, and lets the team collaborate on the same target list. The community edition is free and self-hosted, which is the main reason it stays in my rotation for internal engagements.
What is Faraday?
Faraday started as a tool for penetration testers who needed a single place to collect results from multiple scanners. It has since grown into a vulnerability management platform used by security operations teams, red teams, and managed security service providers.
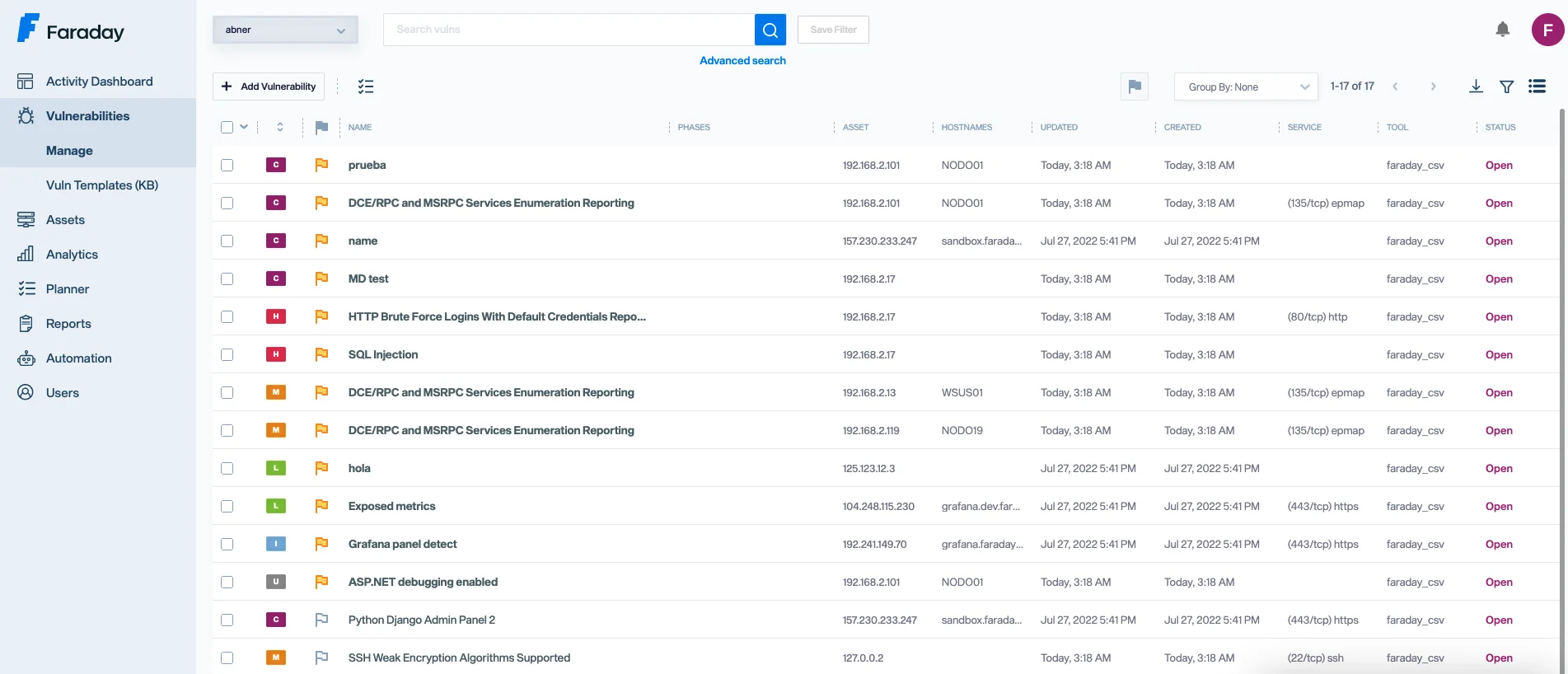
What are Faraday’s key features?
Tool integrations
Faraday normalizes data from 80+ security tools:
| Category | Tools |
|---|---|
| Vulnerability scanners | Nessus, OpenVAS, Qualys |
| SAST/DAST | OWASP ZAP, Burp Suite, Semgrep |
| Network | Nmap, Masscan |
| Pentesting | Metasploit, Nuclei |
| Cloud/containers | Trivy, AWS tools |
All findings get normalized into a common format with automatic deduplication.
Agents Dispatcher
For large or distributed environments, Agents Dispatcher runs remote scans without installing the full Faraday stack on every machine:
- Lightweight agents for scheduled or on-demand scanning
- Horizontal scaling across multiple environments
- Automatic result import back to the central instance
- Works with any supported scanner
Note: Unlike most ASPM tools that focus on development pipeline security, Faraday comes from the offensive security world. It's built for pentesting teams, red teams, and vulnerability assessors who need to manage findings from hands-on security testing alongside automated scanning.
Ticketing integration
| System | Integration type |
|---|---|
| Jira | Direct ticket sync with bidirectional updates |
| ServiceNow | Vulnerability ticket creation |
| GitLab | Issue creation from findings |
| SolarWinds | Integration available |
Additional products
Beyond the open-source core, Faraday offers several commercial products:
| Product | What it does |
|---|---|
| Faraday Enrichment | Smart scoring that prioritizes vulnerabilities using contextual data |
| Faraday CART | Continuous automated attack testing |
| Faraday OPS | External attack surface mapping and monitoring |
| Faraday Labs | Offensive security research services |
| Red Team Services | Application, network, hardware, and physical security assessments |
Authentication and deployment
| Feature | Options |
|---|---|
| Authentication | 2FA, LDAP, SAML |
| Deployment | Cloud or on-premises |
| API | RESTful API for automation |
| CLI | faraday-cli for terminal workflows |
What does Faraday integrate with?
How do I get started with Faraday?
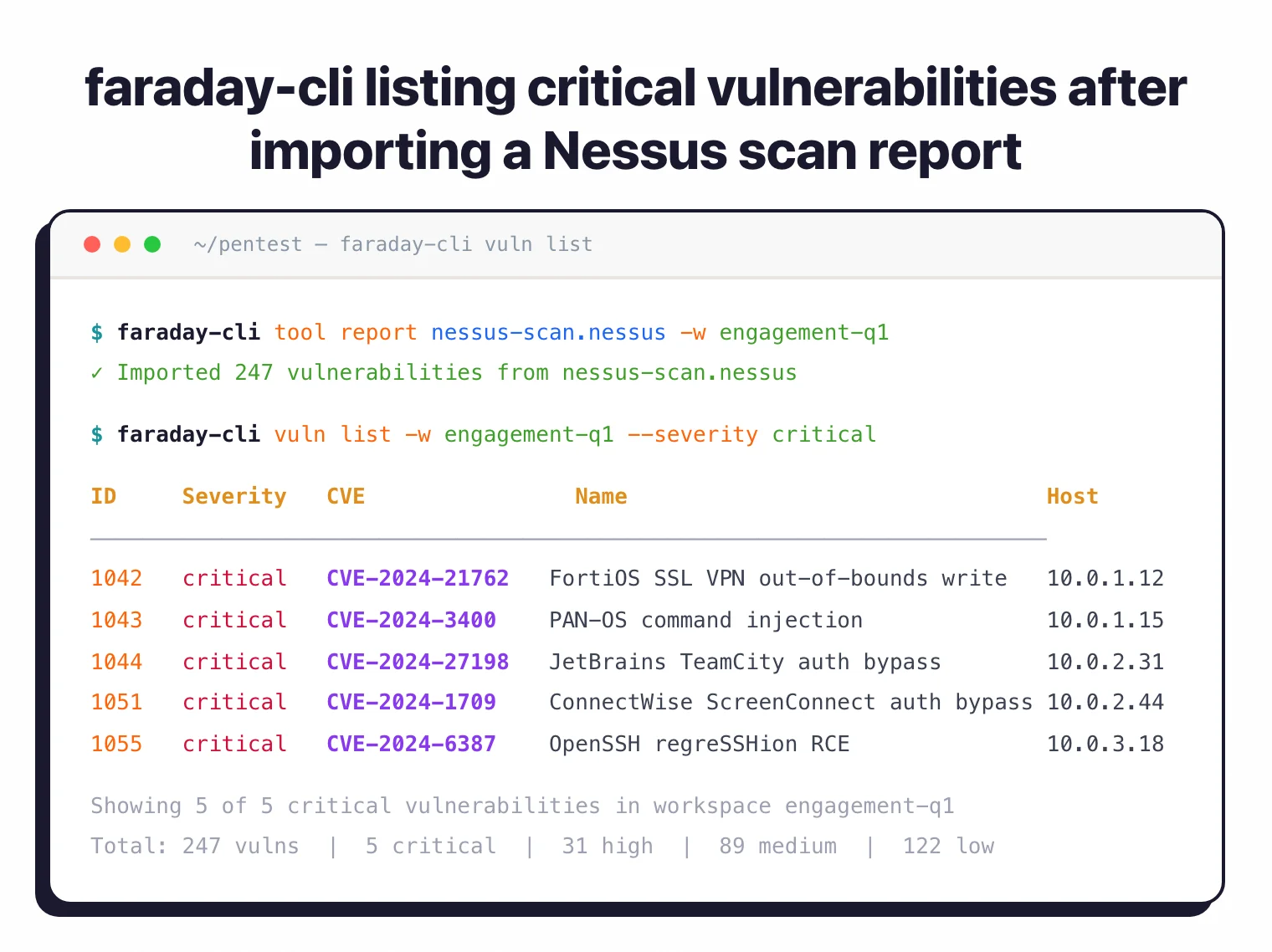
docker compose up -d from the Faraday repository. The web UI launches on port 5985 with PostgreSQL as the backend.CLI usage
# Install Faraday CLI
pip install faraday-cli
# Connect to your Faraday instance
faraday-cli auth -f https://your-faraday-instance -u admin
# Import scan results
faraday-cli tool report /path/to/nessus-report.nessus -w my-workspace
# List vulnerabilities
faraday-cli vuln list -w my-workspace --severity critical
System requirements
Per docs.faradaysec.com/requirements , the floor for a community-edition install is 2 GHz quad-core / 8 GB RAM, with 8-core / 16 GB recommended for large networks running Agents Dispatcher across multiple environments.
How Faraday compares to other vulnerability managers
If Faraday does not fit your team, four adjacent tools cover overlapping territory.
- DefectDojo — The closest direct OSS peer. DefectDojo leans DevSecOps and pulls from 200+ parsers including SAST/DAST/SCA in CI/CD pipelines; Faraday leans offensive security and pentest collaboration. If your scanners are CI-driven, DefectDojo fits better.
- ArmorCode — Better fit if you need commercial enterprise ASPM with 320+ scanner integrations, AI-powered prioritization, and managed SaaS rather than self-hosting Faraday.
- Plextrac — The closest commercial peer for Faraday’s pentest-collaboration shape. Plextrac centralizes engagement data, lets red and blue teams collaborate on findings, and ships strong client-deliverable reporting. Faraday is the open-source angle on the same job; Plextrac wins on polish, paid templates, and enterprise reporting features.
- Dradis — Pentest reporting peer with similar offensive-security DNA. Dradis is stronger on report templating and client deliverables; Faraday is stronger on orchestration and Agents Dispatcher remote scanning.
For a wider sweep, the ASPM hub lists every active platform.
When to use Faraday
Faraday is the go-to choice for offensive security teams, pentesting firms, and MSSPs that need centralized vulnerability management from hands-on testing alongside automated scanning. Its roots in the pentesting world show — the interface and workflows are designed around how security assessors actually work.
Pro tip: Penetration testing teams, red teams, and MSSPs that need to aggregate findings from 80+ security tools with remote scanning agents and ticketing integration.
If your focus is purely on development pipeline security (SAST/SCA in CI/CD), tools like DefectDojo or Jit are a better fit. Faraday shines when offensive security testing is a big part of your program.