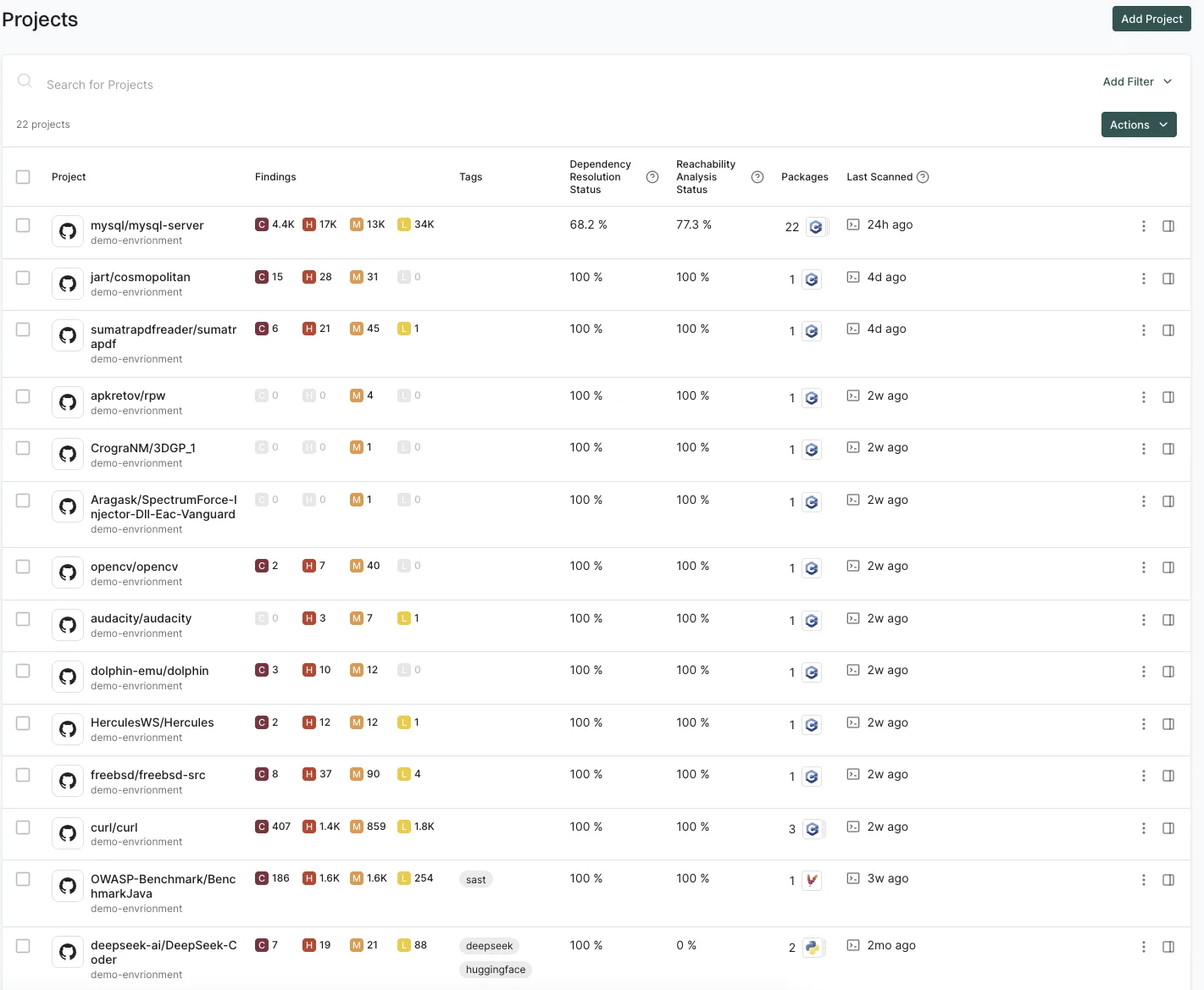
Endor Labs is an AI-native SCA platform that uses function-level reachability analysis to cut through alert noise.
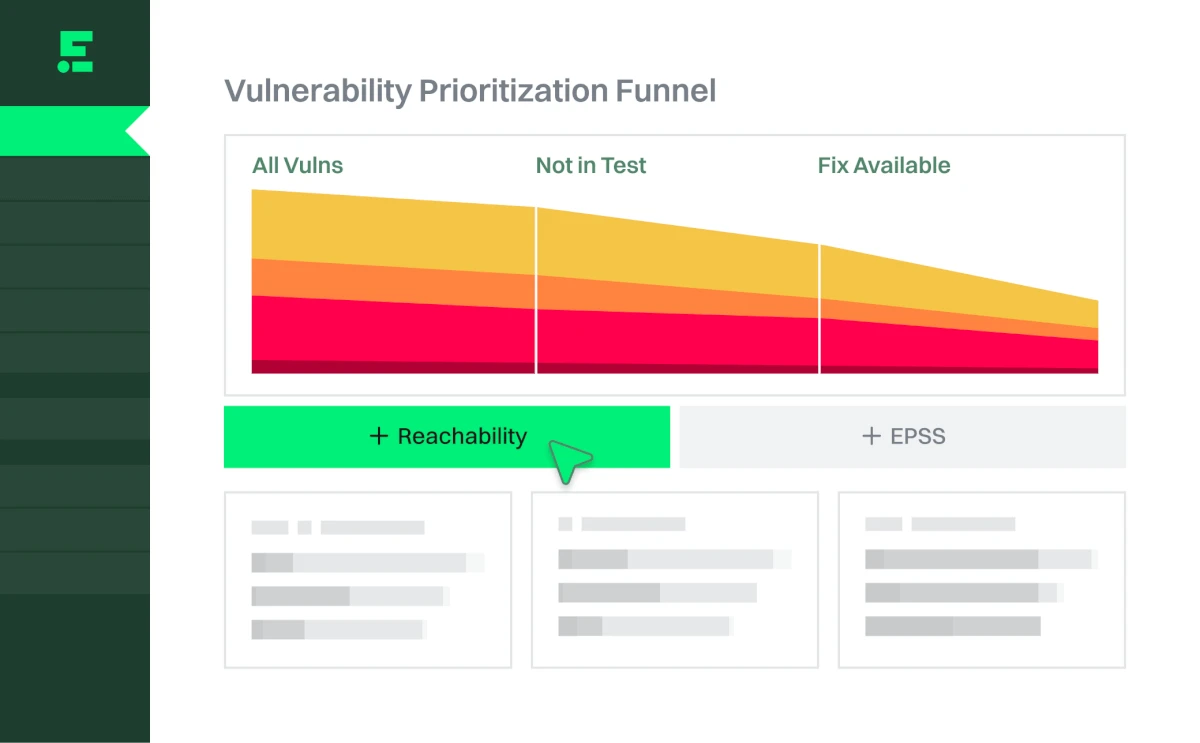
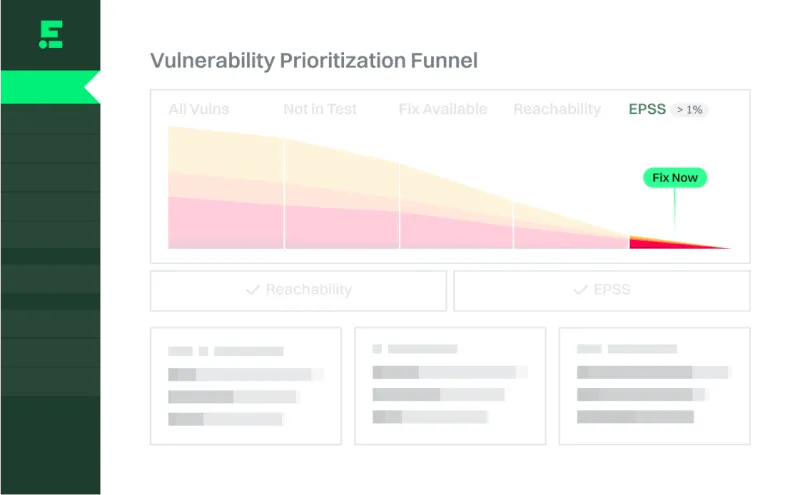
The platform reports up to 97% reduction in SCA alerts by filtering out vulnerabilities in code paths your application never calls.
It covers SAST, SCA, container scanning, secrets detection, and malware detection across 40+ languages.
The platform is used by OpenAI, Cursor, Snowflake, Netskope, and Atlassian.
What is Endor Labs?
Most SCA tools report every vulnerability in every dependency. Endor Labs analyzes which vulnerable code paths are actually reachable from your application.
A dependency might have a known CVE, but if your code never calls the affected function, it gets deprioritized.
Key features
Scan capabilities
| Capability | Coverage |
|---|---|
| SCA | 40+ languages, function-level reachability |
| SAST | AI-native static analysis |
| Secrets detection | API keys, credentials, tokens |
| Container scanning | Docker, OCI images |
| Malware detection | Typosquatting, dependency confusion |
| SBOM | CycloneDX, SPDX generation |
Reachability analysis
Endor Labs builds call graphs from your application code and traces data flow to vulnerable methods in dependencies.
If a vulnerable function is buried in dead code or behind a code path your application never exercises, the finding gets deprioritized. This is function-level analysis, not just package-level.
Dependency lifecycle management
Beyond vulnerabilities, Endor Labs tracks version freshness, maintainer activity, license compliance, and security posture scoring for each dependency. This helps teams make informed decisions about which packages to trust.
SBOM management
Generates SBOMs in CycloneDX and SPDX formats with continuous updates. The dependency graph visualization shows direct and transitive dependencies and their risk status.
Malware detection
Endor Labs scans for malicious packages in addition to vulnerable ones, catching supply chain attacks like typosquatting and dependency confusion.
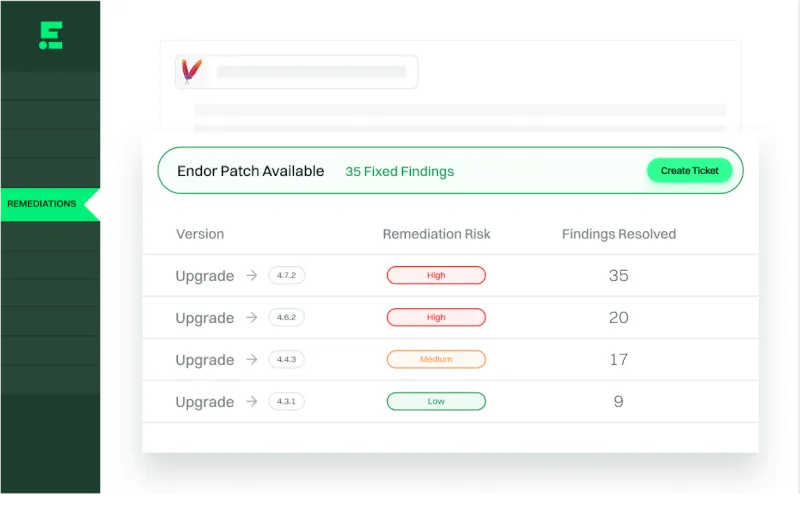
Dependency update automation and Endor Patches
On top of alert prioritization, Endor Labs ships automated remediation in two shapes. For vulnerabilities where an upgrade exists, the platform opens automated fix pull requests with the minimum safe version bump for direct and transitive dependencies, the same pattern as Snyk or Mend. Where no upstream upgrade is available, Endor Patches provide backported fixes — binary-compatible patched artifacts for common Java and Python libraries — so teams can resolve critical findings without waiting for maintainer releases.
These two paths handle dependency update automation with a narrower scope than Renovate’s continuous refresh loop. Endor’s PRs are security-triggered rather than cadence-driven, so most teams pair it with Renovate or Dependabot when they want general dependency hygiene alongside security remediation.
Setup
endorctl from the Endor Labs documentation for your platform.endorctl scan --path . to analyze dependencies with reachability analysis.endorlabs/github-action@v1 action for automatic PR scanning.# Scan project
endorctl scan --path .
GitHub Actions
- name: Endor Labs Scan
uses: endorlabs/github-action@v1
with:
api_key: ${{ secrets.ENDOR_API_KEY }}
api_secret: ${{ secrets.ENDOR_API_SECRET }}
enable_pr_comments: true
endorctl install and first scan
Install the CLI with the official curl script:
curl https://api.endorlabs.com/download/latest/endorctl_linux_amd64 -o endorctl
chmod +x endorctl && sudo mv endorctl /usr/local/bin/
Authenticate via the Endor Labs tenant — the CLI uses OAuth device flow by default, so endorctl auth opens your browser and associates the machine with your workspace. For CI, set ENDOR_NAMESPACE, ENDOR_API_CREDENTIALS_KEY, and ENDOR_API_CREDENTIALS_SECRET environment variables instead and skip the interactive login.
With auth in place, run the first analysis against the repository root:
endorctl scan --path . --namespace your-namespace
The first scan builds the initial call graph for reachability analysis, uploads the results to the SaaS workspace, and surfaces the prioritized finding list in the Endor Labs UI. Subsequent scans are incremental and materially faster than the first one.
When to use Endor Labs
Endor Labs is the right choice for teams drowning in SCA alerts who need accurate prioritization based on actual exploitability.
Strengths:
- Up to 97% alert noise reduction through reachability analysis
- 40+ language support
- Combined SAST, SCA, secrets, and container scanning
- Trusted by OpenAI, Snowflake, Atlassian
- OWASP Top 10 risk detection for open source
Limitations:
- Commercial only, no free tier. Median annual contract: $34,700 (range: $27,500–$39,000)
- Newer platform with smaller community than established tools
- Reachability analysis accuracy varies by language
If reachability-based prioritization does not match your stack, see the Endor Labs alternatives comparison for eight SCA tools evaluated on the same noise-reduction criteria, or the SCA tools overview for the full category landscape.
How it compares:
| vs. | Key difference |
|---|---|
| Snyk Open Source | Snyk has reachability for Java and JS only. Endor Labs covers 40+ languages with deeper call graph analysis. |
| Grype | Grype is a free CLI scanner without reachability analysis. Endor Labs adds prioritization intelligence. |
For context, see the guides on What is SCA? and SCA in CI/CD pipelines.
Endor Labs pricing
Endor Labs publishes a public pricing page at endorlabs.com/pricing but does not publish dollar figures. The structure on the page names two primary tiers plus one add-on:
- Core — entry tier, framed as “reduce noise and prioritize OSS vulnerabilities.” Focused on SCA with reachability.
- Pro — upper tier, adds the features needed to “fix OSS vulnerabilities faster and secure the SDLC.” Superset of Core.
- Patches — available as an add-on across both tiers. Covers the backported security patches described above.
- CoDe and SBOM Hub — additional add-ons for SAST + secrets and SBOM import/management respectively.
Every tier and add-on routes through a contact-sales “Get Quote” flow; there is no self-serve checkout and no free tier. Per site policy I do not publish a list price here because none exists publicly. For directional figures on actual contract sizes, the frontmatter on this page references Vendr’s aggregated data — see the Vendr footnote — which reflects what real customers have paid historically.
Endor Labs alternatives
Endor Labs sits in a narrow slice of the SCA market — reachability-first prioritization — and the right alternative depends on which part of that pitch matters most.
Snyk Open Source
Snyk Open Source is the volume leader on developer-first SCA with the broadest ecosystem coverage and a real free tier. Snyk’s reachability is narrower (Java and JavaScript) but its vulnerability database and developer workflow are hard to beat.
Socket
Socket focuses on malicious-package detection through behavioural analysis — install scripts, network access, filesystem operations. Pick Socket when supply-chain attack prevention (typosquats, compromised maintainers) matters more than reachability filtering.
Aikido
Aikido bundles SCA, SAST, container, secrets, and IaC into a single developer-priced platform. It is the pragmatic alternative when Endor’s narrower SCA-plus-reachability focus feels too specialized for your scope.
Ox Security
Ox Security takes an ASPM angle — pipeline posture, policy enforcement, and risk correlation across multiple scanners. Teams drawn to Endor’s platform breadth but wanting wider pipeline coverage often evaluate Ox head-to-head.
Apiiro
Apiiro is another ASPM-oriented option that emphasises code-to-cloud risk graphs and material-change detection. Choose Apiiro when application inventory and change risk matter more than per-CVE reachability.
For the full landscape, see the Endor Labs alternatives guide and the SCA tools overview.
Endor Labs FAQ
Who founded Endor Labs?
Endor Labs was founded by Varun Badhwar and Dimitri Stiliadis in 2022. Both came from Palo Alto Networks, where they led Prisma Cloud through its hypergrowth phase before starting Endor. Varun serves as CEO and co-founder; Dimitri as CTO and co-founder.
How is Endor Labs funded?
Endor Labs is privately held. The company raised a $25 million seed round in late 2022, a $70 million Series A in 2023, and a $93 million Series B in 2025, with investors including Lightspeed Venture Partners, Coatue, Dell Technologies Capital, and DFJ Growth. It is not publicly traded.
Does Endor Labs replace existing SCA tools?
Usually, yes. Teams tend to adopt Endor Labs as their primary SCA platform rather than layering it on top of another dependency scanner, because the reachability signal only lands if it drives the actual prioritization queue. Where Endor does run alongside another tool, it is most often alongside a free generator like Syft or Dependabot handling simple alert routing, with Endor doing the prioritization work.
How accurate is the 97% noise-reduction claim?
The up-to-97% figure comes from Endor’s own aggregated customer data and depends heavily on the language, the depth of the dependency tree, and how much of the application’s vulnerable-method coverage Endor’s database actually has for your stack. Expect the steepest reductions on Java and Python with well-instrumented test suites; Rust and newer languages will see more variable results.
What ecosystems does Endor Labs support?
Endor Labs advertises 40+ languages for SCA with reachability analysis, with the deepest coverage on Java, JavaScript/TypeScript, Python, Go, C#, Kotlin, and Scala. Full language-specific capability tables live at docs.endorlabs.com — and change between releases, so check for your ecosystem before committing.
Frequently Asked Questions
What is Endor Labs?
How much does Endor Labs reduce alert noise?
What languages does Endor Labs support?
Who uses Endor Labs?
* Pricing data from Vendr — anonymized contract values from real buyer transactions.