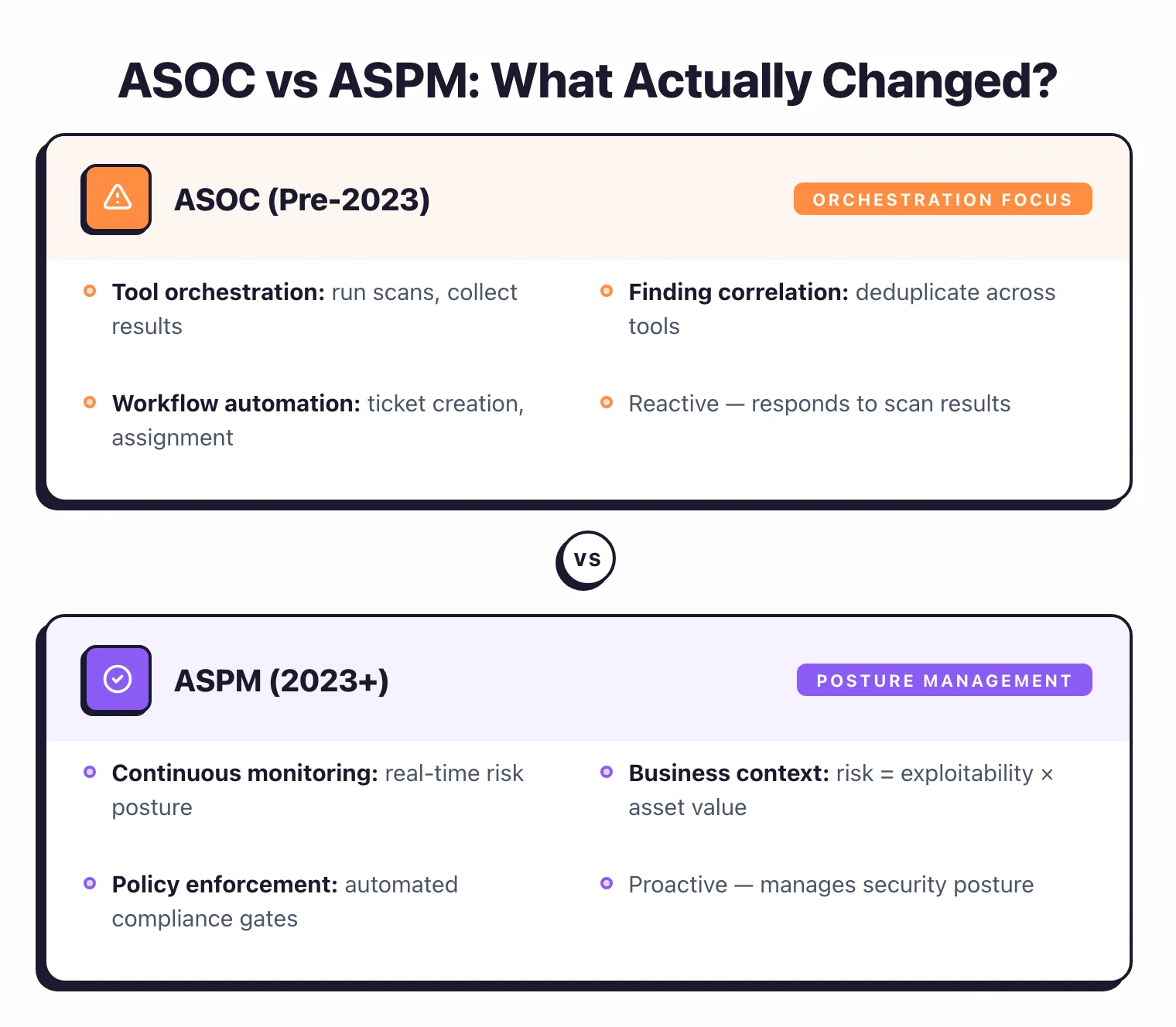
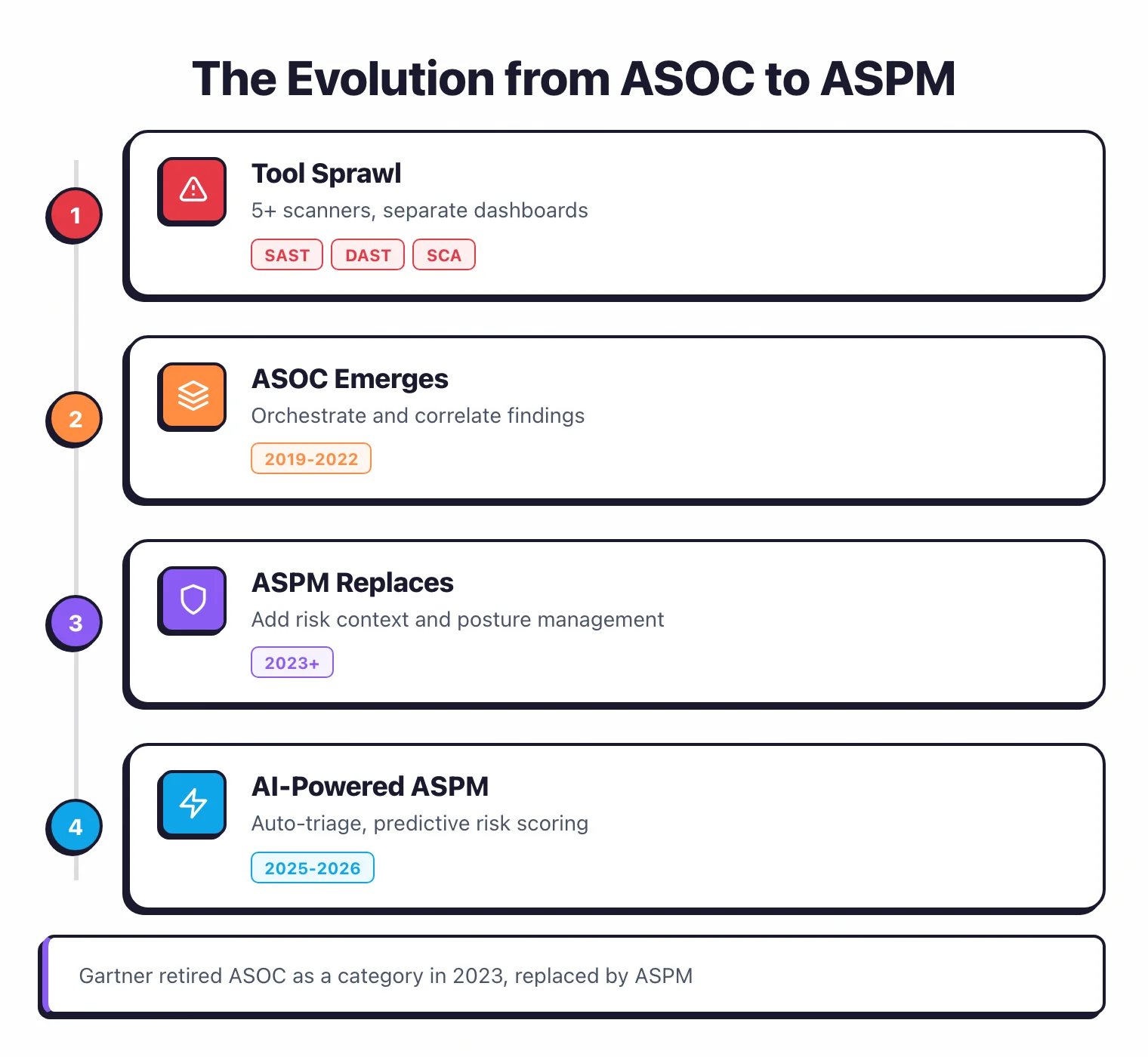
ASPM vs ASOC is a comparison between two Gartner-defined application security categories where ASPM (Application Security Posture Management) replaced ASOC (Application Security Orchestration and Correlation) in 2023.
ASOC aggregated and deduplicated findings from multiple scanners into a single dashboard.
ASPM does everything ASOC did and adds business-context risk scoring, developer remediation workflows, security posture trending, and software supply chain visibility.
Gartner retired the ASOC term in its 2023 Innovation Insight report because the market had outgrown aggregation-only tools.
What is ASOC?
ASOC (Application Security Orchestration and Correlation) is a Gartner-defined category from 2019 that describes tools which aggregate, deduplicate, and correlate findings from multiple application security scanners into a single dashboard.
Gartner introduced the term in its 2019 Hype Cycle for Application Security to address a growing problem: organizations running SAST, DAST, SCA, and container scanners had findings scattered across separate dashboards with no unified view.
ASOC tools pulled findings from those scanners into a single interface. They deduplicated results, so a vulnerability flagged by both SAST and SCA would appear once instead of twice.
They correlated related findings, linking a vulnerable dependency identified by SCA to the code path flagged by SAST. They also orchestrated scan workflows, triggering the right scanner at the right stage of the CI/CD pipeline.
ASOC-era vendors included Code Dx (now part of Black Duck), Kondukto, and ZeroNorth (later acquired by Harness and folded into Harness Security Testing Orchestration ). These tools helped teams drowning in scanner output, but they were fundamentally tool-centric.
ASOC answered the question “what did my scanners find?” It did not answer “which of my applications is most at risk and what should I fix first?”
ASOC also lacked developer-facing features. Security teams could see a consolidated view of findings, but there was no built-in mechanism to route specific findings to the right development team, track remediation progress, or provide fix guidance.
The workflow typically ended at the dashboard, leaving security engineers to manually file tickets and follow up.
By 2022, the limitations were becoming clear. Organizations with mature DevSecOps practices needed more than a better dashboard.
They needed a platform that understood business risk, not just vulnerability counts.
What is ASPM?
ASPM (Application Security Posture Management) is a Gartner-defined category introduced in 2023 that manages an organization’s application security risk by combining scanner aggregation with business-context risk scoring, developer remediation workflows, and security posture trending. ASPM replaced ASOC in Gartner’s 2023 Innovation Insight report.
It keeps everything ASOC did – aggregation, deduplication, correlation, orchestration – and adds a layer of capabilities that shift the focus from tools to applications.
The most significant addition is business-context risk scoring. ASPM platforms know which applications matter most to the organization (revenue-critical, customer-facing, handling regulated data) and weight findings accordingly.
A critical vulnerability in an internal admin tool does not carry the same risk as the same vulnerability in your payment processing service. ASOC treated them equally. ASPM does not.
Beyond risk scoring, ASPM adds several capabilities that ASOC never offered:
- Developer remediation workflows – Route findings to the right team with fix guidance, auto-create Jira or GitHub issues, and track time-to-remediation.
- Security posture trending – Show whether your application portfolio is getting safer or riskier over time, with historical baselines and regression alerts.
- Software supply chain visibility – Map dependencies across your codebase, generate SBOMs, and flag risk from transitive dependencies.
- Compliance mapping – Tie findings to regulatory frameworks (SOC 2, PCI DSS, ISO 27001) and generate audit-ready evidence.
For a deeper look at ASPM capabilities, see the What is ASPM guide. The main ASPM vendors today include Apiiro , ArmorCode , Cycode , Ox Security , and Phoenix Security. See the full list at ASPM tools .
Feature comparison
ASOC and ASPM share four core capabilities (aggregation, deduplication, correlation, orchestration), but ASPM adds six that ASOC lacked: application risk scoring, asset inventory with criticality ratings, developer remediation workflows, security posture trending, supply chain visibility, and compliance mapping.
| Capability | ASOC | ASPM |
|---|---|---|
| Aggregate findings from multiple scanners | Yes (core focus) | Yes (included) |
| Deduplicate overlapping findings | Yes | Yes |
| Correlate related vulnerabilities | Yes | Yes, with richer context |
| Orchestrate scan workflows | Yes | Yes |
| Application risk scoring | No | Yes (business context weighted) |
| Asset inventory with criticality ratings | No | Yes |
| Developer remediation workflows | No | Yes (ticketing, fix guidance) |
| Security posture trending over time | No | Yes |
| Software supply chain visibility | No | Yes |
| Compliance framework mapping | No | Yes |
| Runtime context integration | No | Some vendors |
| API and integration ecosystem | Limited | Broad (SCM, CI/CD, cloud, ticketing) |
In short, ASOC covered the collection side of the problem (find and organize findings). ASPM covers both sides (collect findings and drive remediation with business context).
Gartner projects that 40 percent of organizations developing proprietary applications will adopt ASPM by 2026, up from about 5 percent in 2023. That adoption curve says a lot about how fast the market moved past aggregation-only tools.
What actually changed between ASOC and ASPM
Tool-centric vs. application-centric
The biggest difference between ASOC and ASPM is what they organize around. ASOC organized findings by scanner tool, while ASPM organizes findings by application.
In ASOC, the dashboard showed findings grouped by scanner: here are your SAST results, here are your SCA results, here are your DAST results. You could see everything each tool found, but understanding the risk to a specific application required manual correlation.
ASPM flips that view. The dashboard shows each application’s overall risk posture, combining findings from every scanner that touched it.
You see that your payment service has 3 critical findings and your marketing site has 12 medium ones, so you know where to focus.
That application-level view is what security teams and executives actually need for decision-making.
The difference shows up in practice. When a new zero-day drops (like Log4Shell), ASOC could tell you which scanners flagged it.
ASPM can tell you which applications are affected, which ones are internet-facing, and which handle sensitive data, so you know where to patch first.
Aggregation vs posture management
ASOC passively aggregated findings into a dashboard, while ASPM actively manages security posture by tracking risk trends, alerting on regressions, and driving remediation workflows.
ASOC collected data, deduplicated it, and displayed it. The value was in reducing noise, but ASOC did not tell you what to do about it or whether things were getting better or worse.
ASPM tracks risk trends over time, alerts when an application’s security posture degrades, and provides remediation workflows that assign findings to developers with fix recommendations. The shift is from “here is what we found” to “here is what matters and who should fix it.”
In practical terms, ASOC gave you a cleaner inbox. ASPM gives you a workflow that moves findings from detection through triage to resolution, with accountability at each step.
Correlation vs risk scoring
ASOC correlated findings to reduce duplicates, while ASPM scores risk by combining vulnerability severity with business context like application criticality, internet exposure, exploit availability, and data sensitivity.
ASOC correlation linked related findings. If SAST and SCA both flagged the same issue, ASOC recognized the overlap.
That reduced duplicate work but did not help with prioritization.
ASPM risk scoring goes further by weighing the application’s criticality, whether the vulnerable code is reachable, whether the application is internet-facing, whether an exploit exists in the wild, and what data the application handles.
A medium-severity finding in a payment service with an active exploit and internet exposure scores higher than a critical finding in an air-gapped internal tool.
That context-aware prioritization is the capability that drove Gartner to define a new category.
Why the shift happened
Three forces pushed the industry from ASOC to ASPM: DevSecOps maturity demanding developer-facing workflows, high-profile supply chain attacks exposing the limits of dashboard-only tools, and the sheer volume of findings from modern scanner stacks making raw aggregation impractical.
DevSecOps maturity meant development teams expected more than a dashboard. They needed findings delivered to their existing workflows (pull requests, issue trackers) with fix guidance, not a separate security portal to check.
The software supply chain attack wave also raised the bar. SolarWinds in 2020 , Log4Shell in 2021 , and the surge in open-source dependency attacks through 2022-2023 all showed that organizations needed to know which applications depended on which libraries and how deep the risk went. ASOC had no supply chain layer.
On top of that, the sheer volume of findings from modern scanner stacks (often 5 to 15 tools per enterprise) made raw aggregation impractical.
Without business-context scoring, a team with 10,000 open findings had no way to determine which 50 to fix this sprint. ASPM’s risk scoring addressed that prioritization gap.

What are the drawbacks of using ASPM?
ASPM is the right architecture for most multi-scanner AppSec programs, but it is not free of trade-offs. Five drawbacks come up in every honest evaluation I run with buyers:
- Licence on top of licences. ASPM platforms charge per application or per developer on top of the SAST, DAST, and SCA tools they aggregate. At enterprise tier the platform fee can rival the cost of an individual scanner, and the buying committee has to defend it as a separate line item.
- Integration time is real. Connecting five-to-fifteen scanners, ticketing, SCM, and asset inventory through APIs is weeks of platform-engineering work before you see consolidated value. Vendors quote “one-day setup” and that is true for the first scanner; the rest of the integration is what eats the quarter.
- Risk-scoring opacity. Every ASPM platform layers a proprietary risk score on top of raw scanner severity. When security tells engineering a finding is critical and engineering disagrees, the conversation collapses into “explain your scoring algorithm” — and most vendors treat the formula as a trade secret.
- Yet-another-dashboard fatigue. ASPM is meant to consolidate panes of glass; without strong workflow integration into Jira, Slack, and the IDE, it becomes the fifth dashboard nobody opens.
- It assumes maturity. ASPM presumes you already run multiple scanners with real coverage. Teams running one SAST tool and Dependabot will not see ROI proportional to the licence cost — the consolidation savings only show up once you have something to consolidate.
For a longer drawbacks treatment in the context of choosing an ASPM platform, see the ASPM tools hub .
When ASOC terminology still applies
ASOC terminology still applies in four situations: legacy vendor documentation, older analyst reports from 2019-2022, organizations with simple aggregation-only needs, and academic or training contexts that predate the 2023 category change.
Legacy vendor documentation. Tools that were built during the ASOC era may still use the term in their product descriptions.
If a vendor calls their product an ASOC platform, check whether they have added ASPM capabilities since 2023 or whether the product is genuinely limited to aggregation and correlation.
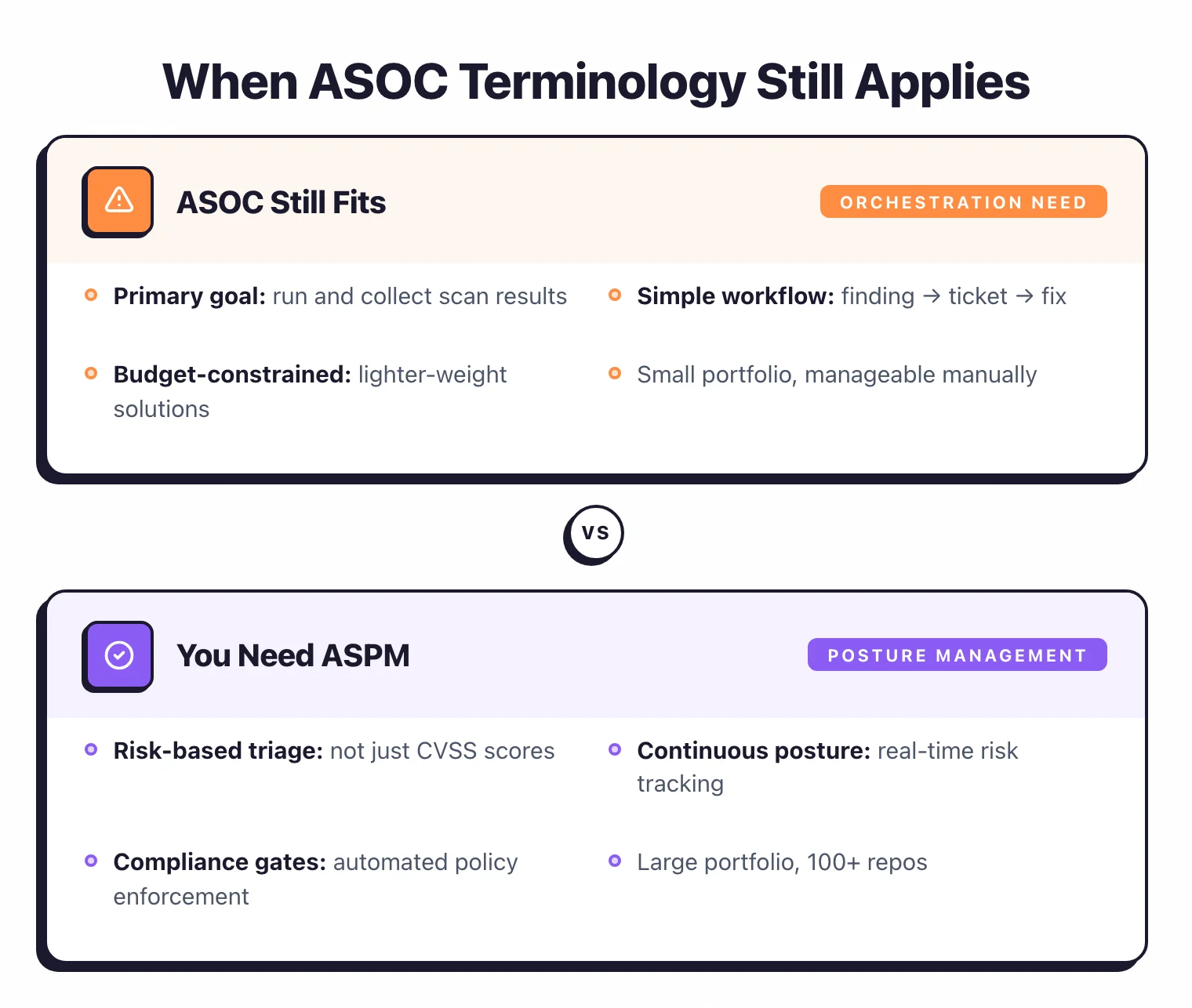
Older analyst reports. Gartner and Forrester reports from 2019-2022 reference ASOC extensively.
When reading those reports, understand that the ASOC capabilities they describe are now a subset of what ASPM covers.
Simple aggregation needs. If all you need is a single dashboard that deduplicates findings from two or three scanners and you do not need risk scoring, trending, or remediation workflows, an older ASOC-style tool may be sufficient.
This is most common in small teams with a handful of applications and limited scanner diversity.
Academic and training contexts. Security certification courses and textbooks published before 2023 reference ASOC.
The underlying concepts (aggregation, correlation, orchestration) are still valid and form the foundation of what ASPM does. Understanding ASOC helps explain why ASPM exists.
When you need ASPM
ASPM becomes necessary when your organization runs three or more AppSec tools, manages applications with varying business criticality, needs developer-facing remediation workflows, or requires executive-level security posture reporting and compliance mapping.
Multiple scanners generating thousands of findings. Once you run three or more AppSec tools (SAST, SCA, DAST, IaC, container scanning), the volume of findings exceeds what a team can manually triage.
ASPM’s deduplication and risk scoring turn thousands of alerts into a prioritized list of what actually matters.
Application portfolio with varying criticality. If you manage dozens or hundreds of applications, not all of them carry the same business risk.
ASPM lets you assign criticality ratings so that findings in your most important applications surface first.
Developer-facing remediation. If your security team is a bottleneck because developers wait for triage before they know what to fix, ASPM’s automated routing and fix guidance push findings directly to the responsible team. That shortens the gap between detection and remediation considerably.
Executive and compliance reporting. When leadership or auditors ask “what is our security posture across all applications,” ASPM answers with trending data and compliance mapping.
ASOC could show raw finding counts but had no business-level view.
Supply chain visibility. After SolarWinds and Log4Shell, many organizations need to know which applications depend on which libraries and what risk those dependencies carry.
ASPM platforms that include SBOM generation and dependency mapping give you that view.
Growing scanner stack. The average enterprise runs 5 to 15 distinct application security tools, each with its own dashboard, severity scale, and definition of “critical.” ASPM normalizes those outputs into a consistent risk model.
If you are already struggling with three tools, the problem only gets worse as your stack grows.
If any of these scenarios describe your organization, I recommend evaluating ASPM platforms rather than settling for ASOC-era aggregation tools.
For detailed ASPM platform reviews, see the ASPM tools category on AppSec Santa. For broader context on building a mature application security program, visit the DevSecOps hub .






