DefectDojo Alternatives
Thinking of switching from DefectDojo? Compare top competitors including Invicti ASPM, ArmorCode, Cycode, and open-source options for vulnerability management.
Top DefectDojo Alternatives
View all 11 alternatives →Proof-Based ASPM with 99.98% Accuracy and 110+ Integrations
All-in-One AppSec with 95% Noise Reduction
Deep Code Analysis ASPM with Risk Graph
AI-Powered Risk Correlation
Complete ASPM with 94% Fewer False Positives
Open-Source ASPM with 80+ Tool Integrations
- DefectDojo is the gold standard for open-source vulnerability management, but teams outgrow it when they need RBAC, SLA tracking, or vendor-managed infrastructure.
- Invicti ASPM (formerly Kondukto) and ArmorCode offer the closest commercial alternatives with scanner aggregation, deduplication, and risk-based prioritization built in.
- For teams that want to stay open-source, Dependency-Track handles SCA-specific vulnerability management, while Faraday covers penetration testing findings.
- ASPM platforms like Apiiro and OX Security go beyond vulnerability management by adding code-to-cloud risk context and developer workflow integration.
DefectDojo alternatives are vulnerability management and ASPM platforms that replace or extend DefectDojo’s open-source scanner aggregation capabilities. Teams typically switch when they outgrow DefectDojo’s self-hosted model and need managed infrastructure, granular role-based access control, SLA enforcement, or code-to-cloud risk context that the community edition does not provide.
Why Look for DefectDojo Alternatives?
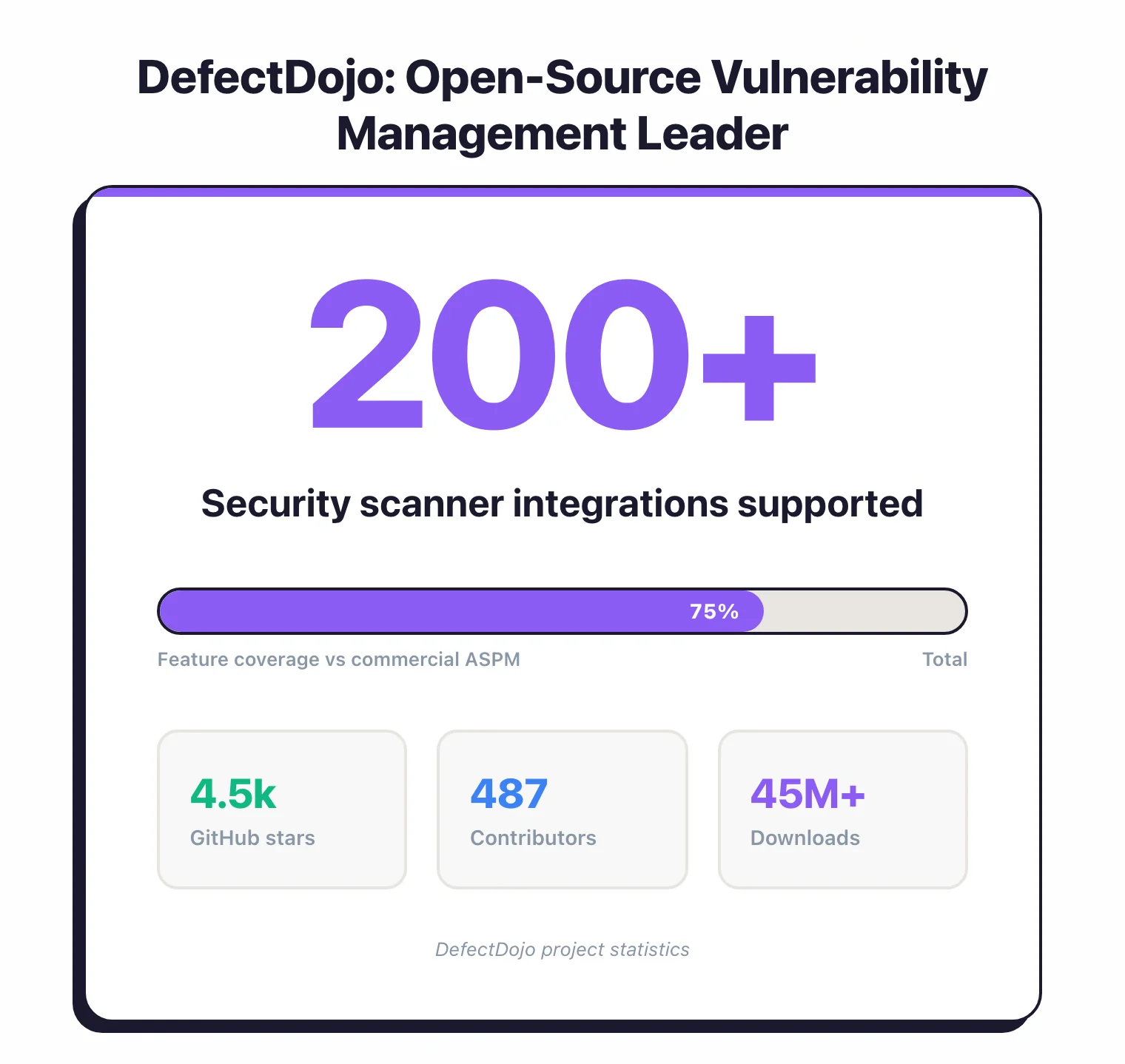
DefectDojo is an open-source vulnerability management platform that aggregates findings from 200+ security scanners into a single triage and tracking workflow.
It is an OWASP Flagship Project with 4.5k GitHub stars, 487 contributors, and 45M+ downloads. For teams running multiple security tools, it remains the default open-source choice for centralized vulnerability management.
So why look elsewhere?
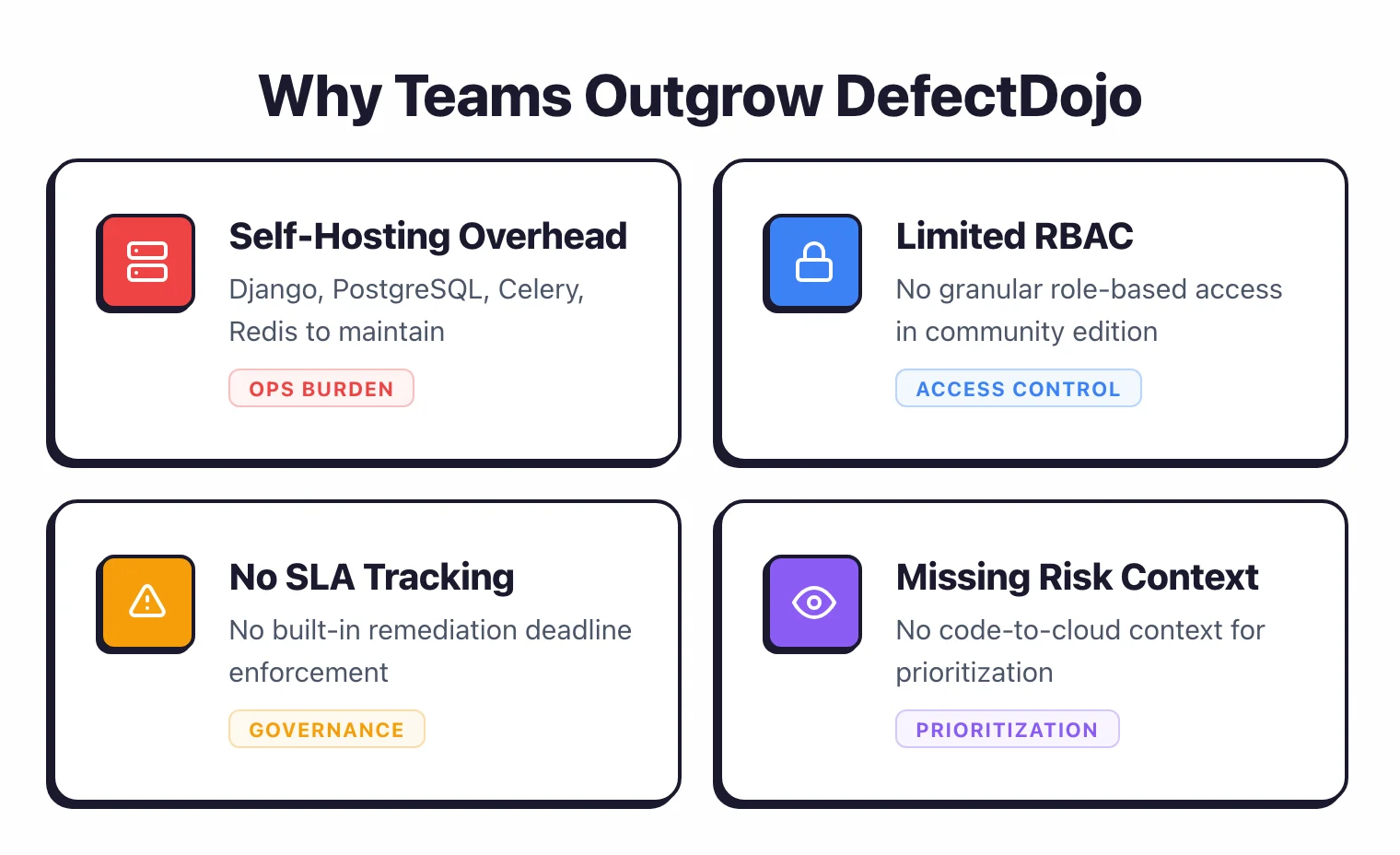
Self-hosting overhead adds up. DefectDojo runs on Django, PostgreSQL, Celery, and Redis. That is four services to monitor, patch, back up, and scale.
Teams that start with a quick Docker Compose setup eventually face production concerns: database migrations during upgrades, Celery worker tuning for large scan imports, and Redis memory management.
If you lack a dedicated DevOps engineer, this maintenance burden grows with every scanner you connect.
The Community Edition has limited access control. DefectDojo’s open-source version provides basic user roles, but granular role-based access control (RBAC) is restricted.
In organizations with multiple product teams, you often want developers to see only their own findings while managers get cross-team dashboards. Getting there with the community edition requires workarounds.
No native SLA tracking or enforcement. DefectDojo tracks findings and their status, but it does not enforce remediation deadlines.
There is no built-in mechanism to set severity-based SLA targets, send escalation reminders, or report on SLA compliance.
Teams that need remediation governance build it themselves or layer a ticketing system on top.
Scaling with large scanner output gets rough. Organizations importing tens of thousands of findings per week from multiple scanners can hit performance bottlenecks.
The deduplication engine handles standard volumes well, but at enterprise scale, import times and UI responsiveness degrade without significant infrastructure tuning.
Missing code-to-cloud context. DefectDojo tells you which vulnerabilities exist.
It does not tell you whether those vulnerabilities sit in code that is reachable from the internet, handles sensitive data, or runs in production.
That risk context — mapping findings to business impact — is what modern ASPM platforms add on top.
Top DefectDojo Alternatives
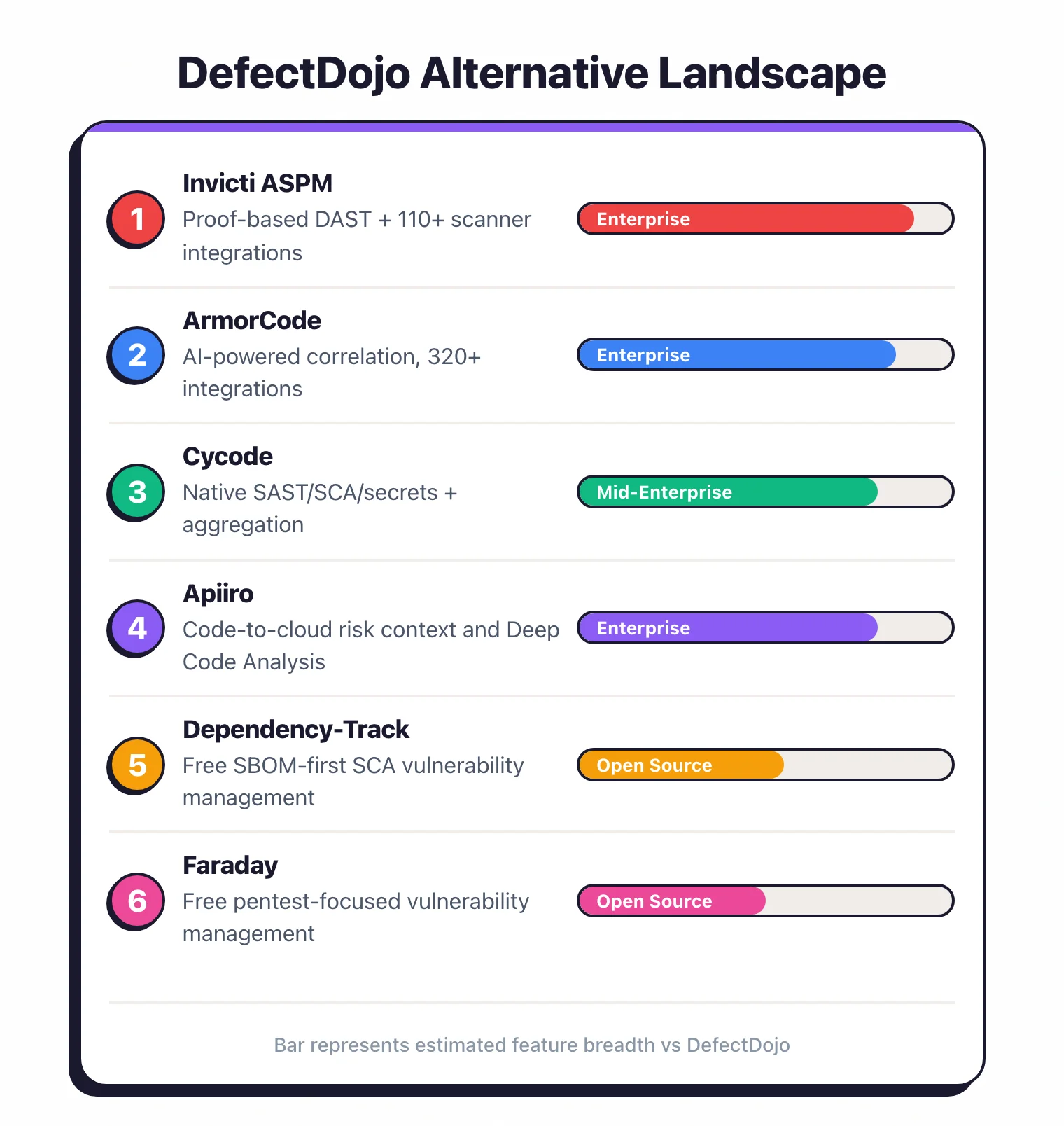
1. Invicti ASPM (formerly Kondukto)
Invicti ASPM formed from Invicti’s acquisition of Kondukto in August 2025. The platform combines scanner orchestration with proof-based DAST validation.
It connects 110+ security tools, normalizes their output, deduplicates findings, and routes them through automated remediation workflows.
The standout feature is proof-based scanning: instead of reporting potential vulnerabilities, Invicti’s DAST engine safely exploits them to confirm they are real, achieving 99.98% scan accuracy. This means fewer false positives reaching your triage queue, a persistent problem with aggregation-only platforms like DefectDojo.
Best for: Teams that want DefectDojo’s aggregation model with managed infrastructure, proof-based DAST, and release criteria gates. Key difference: Proof-based validation eliminates false positives at the source rather than filtering them after import.
2. ArmorCode
ArmorCode is an AI-powered ASPM platform that ingests findings from 320+ security tools and correlates them using its Anya AI engine. The platform has processed over 40 billion findings and is recognized as a Leader in the IDC MarketScape for ASPM.
Where DefectDojo deduplicates based on hash matching and CWE, ArmorCode’s AI correlation identifies relationships across finding types. A code vulnerability, a cloud misconfiguration, and an exposed API endpoint might trace back to the same root cause.
Shutterfly reduced vulnerability remediation from 240 days to 7 days after adopting the platform.
Best for: Enterprise teams with large, heterogeneous security tool portfolios that need AI-driven prioritization. Key difference: AI correlation engine links findings across tool types. 320+ integrations vs DefectDojo’s 200+ parsers.
3. Cycode
Cycode focuses on software supply chain security. Unlike DefectDojo, which aggregates third-party scanner output, Cycode includes native SAST, SCA, secrets detection, and IaC scanning alongside 100+ ConnectorX integrations for existing tools.
The Context Intelligence Graph maps code-to-runtime context and supports natural language queries across your SDLC. Cycode’s native SAST achieves 94% fewer false positives on the OWASP Benchmark compared to competitors.
Best for: Teams that want built-in scanning plus aggregation rather than managing separate scanners and a separate aggregation layer. Key difference: Native scanning engines with 94% fewer false positives, combined with third-party aggregation.
4. Apiiro
Apiiro specializes in code-to-cloud risk context. Its Deep Code Analysis builds an abstract representation of code behavior, tracing data flows across function and service boundaries to detect material changes that shift risk.
DefectDojo tells you a vulnerability exists. Apiiro tells you that the vulnerability sits in code that handles PII, is reachable from the internet, was changed by a junior developer, and deploys to production every Friday. That context changes remediation priority entirely.
Best for: Organizations that need code-to-cloud risk context to prioritize vulnerabilities by actual business impact. Key difference: Risk Graph maps code, infrastructure, and people with business context, queryable in natural language.
5. OX Security
OX Security introduced Active ASPM, which moves beyond passive vulnerability aggregation to real-time pipeline monitoring. The platform blocks risky deployments before they reach production and reports up to 97% reduction in security debt.
OX Security’s Pipeline Bill of Materials (PBOM) extends traditional SBOM by capturing build configs, artifact signatures, deployment targets, and developer identities. The company also co-created the OSC&R framework with security experts from Google, Microsoft, and GitLab, an ATT&CK-like model for software supply chain threats.
Best for: Teams focused on supply chain security and CI/CD pipeline protection alongside vulnerability management. Key difference: Active pipeline enforcement blocks risky deployments. PBOM provides full build-to-deploy provenance.
6. Dependency-Track
Dependency-Track is an OWASP Flagship Project that takes an SBOM-first approach to vulnerability management. It ingests CycloneDX or SPDX SBOMs and continuously monitors them against NVD, GitHub Advisories, and OSS Index.
When a new CVE drops, every affected project gets flagged immediately without requiring a rescan.
Unlike DefectDojo, which handles all scanner types, Dependency-Track focuses exclusively on SCA. That narrower scope means it handles component analysis better than DefectDojo’s SCA parsers, with policy engines for automated risk decisions and portfolio-wide visibility across all applications.
Best for: Teams that primarily need SCA vulnerability management and SBOM compliance tracking. Key difference: Continuous SBOM monitoring with automatic alerts on new CVEs. Open-source under Apache 2.0.
7. Faraday
Faraday is an open-source vulnerability management platform with 6.2k GitHub stars that orchestrates 80+ security tools. It normalizes and deduplicates findings from vulnerability scanners, penetration testing tools, and network scanners into a collaborative workspace.
While DefectDojo leans toward DevSecOps integration and CI/CD workflows, Faraday was built for offensive security teams. Its Agents Dispatcher enables remote scanning across distributed environments, and Faraday Enrichment adds smart vulnerability scoring in the commercial tier.
Best for: Penetration testing teams and offensive security professionals managing multi-tool findings. Key difference: Offensive security focus with remote scanning agents. Stronger pentest workflow than DefectDojo.
Feature Comparison
| Feature | DefectDojo | Invicti ASPM | ArmorCode | Cycode | Apiiro | OX Security | Dep-Track | Faraday |
|---|---|---|---|---|---|---|---|---|
| License | Open Source | Commercial | Commercial | Commercial | Commercial | Commercial | Open Source | Freemium |
| Scanner Integrations | 200+ | 110+ | 320+ | 100+ | Tool-agnostic | Multi-scanner | SCA-only | 80+ |
| Deduplication | Yes | Yes | Yes (AI) | Yes | Yes | Yes | N/A | Yes |
| SLA Tracking | No | Yes | Yes | Yes | Yes | Yes | No | No |
| RBAC | Limited | Yes | Yes | Yes | Yes | Yes | Basic | Basic |
| SBOM Support | Limited | SBOM Radar | Yes | Yes | XBOM | PBOM | Core feature | No |
| Native Scanning | No | DAST | No | SAST/SCA/Secrets | DCA | No | SCA monitoring | No |
| Self-Hosted | Yes | Yes | No | No | No | No | Yes | Yes |
| AI Features | Sensei (Pro) | Proof-based | Anya AI | Cycode AI | Risk Graph | VibeSec AI | No | Enrichment |
Open-Source Options
If staying open-source matters to your team, three projects cover different slices of what DefectDojo does:
Dependency-Track for SCA vulnerability management. If your primary concern is tracking vulnerable dependencies across your software portfolio, Dependency-Track handles it better than DefectDojo’s SCA parsers.
It maintains a persistent component inventory, continuously monitors for new CVEs, and provides policy engines for automated decisions. OWASP Flagship Project, Apache 2.0 license, 3.6k GitHub stars.
Faraday for penetration testing findings. Faraday is purpose-built for offensive security teams managing findings from Nessus, OpenVAS, Burp Suite, ZAP, Nmap, Metasploit, and other pentesting tools. Its Agents Dispatcher supports remote scanning across distributed environments.
GPL-3.0 license, 6.2k GitHub stars, backed by Infobyte since 2004.
Archery for scan orchestration. Archery is a smaller open-source project that orchestrates ZAP and OpenVAS scans with a web interface. It handles basic vulnerability aggregation and reporting.
Less mature than DefectDojo or Faraday, but useful for teams that only run a few scanners and want a lightweight alternative without the full Django/Celery/Redis stack.
None of these individually replaces DefectDojo’s full scope. Dependency-Track covers SCA.
Faraday covers pentesting. DefectDojo covers everything but not as deeply.
The choice depends on where your vulnerability management pain concentrates.
When to Stay with DefectDojo
DefectDojo remains the right choice in several scenarios:
- Your team has DevOps capacity. If you already run Kubernetes clusters and have engineers comfortable with Django, PostgreSQL, and Celery, DefectDojo’s self-hosting overhead is manageable. The Docker Compose and Helm chart deployments are well-documented.
- You need full data sovereignty. DefectDojo runs on your infrastructure. No vulnerability data leaves your network. For regulated industries with strict data residency requirements, this alone can rule out SaaS alternatives.
- Budget constraints are real. The community edition is free. No per-user licensing, no per-scan fees, no contracts. For startups and small teams, this matters more than the missing enterprise features.
- Simple vulnerability tracking is sufficient. If your workflow is “import scans, deduplicate, assign, track” without SLA enforcement, AI prioritization, or code-to-cloud risk mapping, DefectDojo handles the basics well. Not every team needs a full ASPM platform.
- You value extensibility. DefectDojo’s REST API covers all major operations. Teams that want to build custom integrations, automate workflows, or extend the platform with internal tools have more freedom than with most commercial alternatives.
For teams that have outgrown DefectDojo’s capabilities, the ASPM tools category page compares all options side by side. If you are evaluating your broader application security strategy, the What is ASPM? guide explains where vulnerability management fits into the bigger picture.
Frequently Asked Questions
What is the best alternative to DefectDojo?
Is there a free alternative to DefectDojo?
What is the difference between DefectDojo and an ASPM platform?
Should I self-host DefectDojo or use a commercial alternative?

Founder, AppSec Santa
Years in application security. Reviews and compares 209 AppSec tools across 11 categories to help teams pick the right solution. More about me →