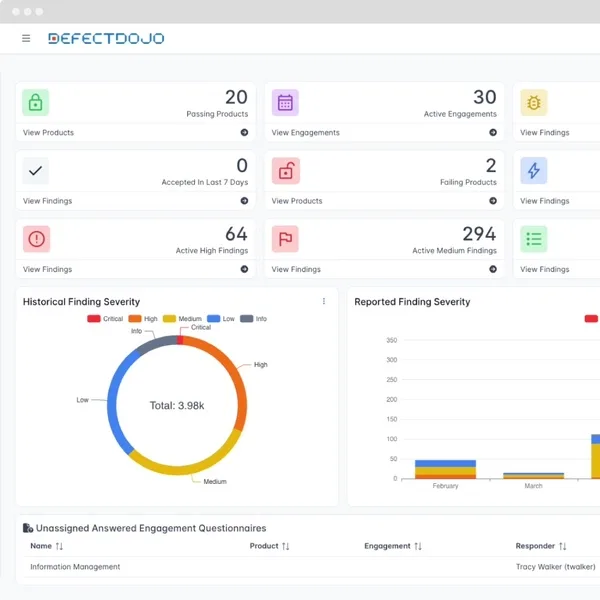
DefectDojo is a widely adopted open-source ASPM platform, with 45M+ downloads, 4.5k GitHub stars, 487 contributors, and 10K+ organizations using it. It is an OWASP Flagship Project that aggregates vulnerability findings from 200+ security tools into a single source of truth.
The project runs on Django with PostgreSQL, Celery, and Redis. Latest release is v2.55.1 (February 2026). Licensed under BSD 3-Clause.
GitHub: DefectDojo/django-DefectDojo
What is DefectDojo?
DefectDojo sits between your security scanners and your remediation workflow.
It ingests scan results, deduplicates findings, assigns risk scores, and tracks remediation — all without requiring you to replace your existing tools.
A commercial Pro edition adds DefectDojo Sensei AI, advanced reporting, and enterprise support. The community edition is fully functional for most teams.
Key features
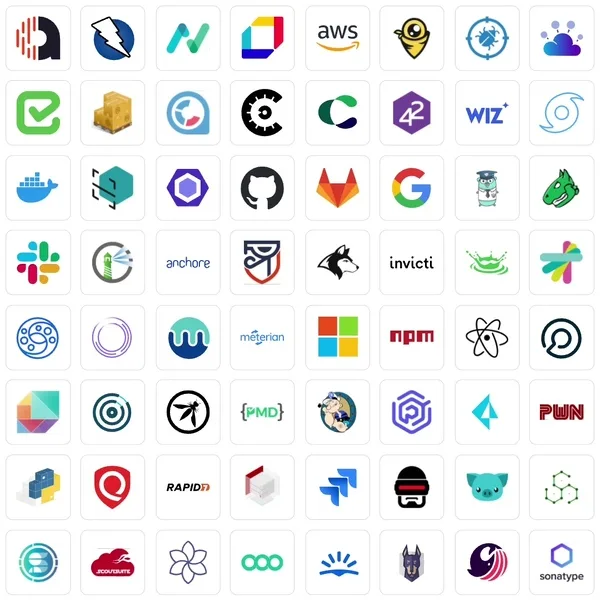
200+ tool integrations
DefectDojo parses results from tools across every security category:
| Category | Tools |
|---|---|
| SAST | Bandit, Semgrep, SonarQube, Checkmarx, Fortify, Veracode, CodeQL, Snyk Code |
| DAST | OWASP ZAP, Burp Suite, Acunetix, Nessus, Nuclei, Nikto |
| SCA | OWASP Dependency-Check, Snyk, npm audit, Trivy, Grype |
| Infrastructure | Trivy, Checkov, KICS, AWS Inspector, ScoutSuite |
| Containers | Trivy, Grype, Docker Scout |
Deduplication engine
DefectDojo automatically deduplicates findings based on:
- Vulnerability type and CWE classification
- File path and line number
- Endpoint and parameter
- Custom hash algorithms for tool-specific matching
A real-world example: 500 raw findings from 5 different scanners typically reduce to about 150 unique vulnerabilities after deduplication.
Risk-based prioritization
Risk scores factor in CVSS severity, business criticality of the affected product, exposure level, and how long the vulnerability has been open. Teams can define custom risk acceptance policies and track exceptions.
CI/CD integration
Push scan results from any pipeline:
# Upload findings from CI/CD
curl -X POST "https://defectdojo.example.com/api/v2/import-scan/" \
-H "Authorization: Token $DD_TOKEN" \
-F "scan_type=ZAP Scan" \
-F "file=@zap-report.xml" \
-F "product_name=My App" \
-F "engagement_name=CI/CD Import" \
-F "auto_create_context=true"
Architecture
DefectDojo runs on four components:
| Component | Role |
|---|---|
| Django application | Web UI, REST API, business logic |
| PostgreSQL | Persistent data storage |
| Celery workers | Background tasks (imports, deduplication, notifications) |
| Redis | Message queue and caching |
Getting started
git clone https://github.com/DefectDojo/django-DefectDojo.git && cd django-DefectDojo && docker compose builddocker compose up -d launches Django, PostgreSQL, Celery, and Redis. The web UI opens on port 8080.Kubernetes deployment is also supported via Helm:
helm repo add defectdojo https://defectdojo.github.io/django-DefectDojo
helm install defectdojo defectdojo/defectdojo
API access
import requests
response = requests.get(
"https://defectdojo.example.com/api/v2/findings/",
headers={"Authorization": "Token YOUR_TOKEN"}
)
findings = response.json()
When to use DefectDojo
DefectDojo is the default choice when you need open-source vulnerability aggregation. It handles the basics — import, deduplicate, prioritize, track — without licensing costs or vendor dependencies.
If you’re comfortable self-hosting and want full control over your data, it’s hard to beat.
If you want managed SaaS instead of self-hosting, the DefectDojo Pro edition or commercial alternatives like ArmorCode or Seemplicity handle the infrastructure for you. If you only run 1-2 scanners, the aggregation overhead may not be worth it.