OpenText Core SCA (formerly Debricked) is a developer-friendly SCA platform that uses machine learning to prioritize vulnerabilities and assess dependency health.
Acquired by Micro Focus in 2022 and now part of OpenText, it integrates natively with the Fortify portfolio for unified SAST+SCA management.
Its ML-based approach addresses a real gap: the Sonatype 2026 State of the Software Supply Chain report frames open-source malware as a nation-state-scale threat, and Sonatype has continued to log tens of thousands of malicious packages across public registries year after year — so intelligent prioritization stays essential.
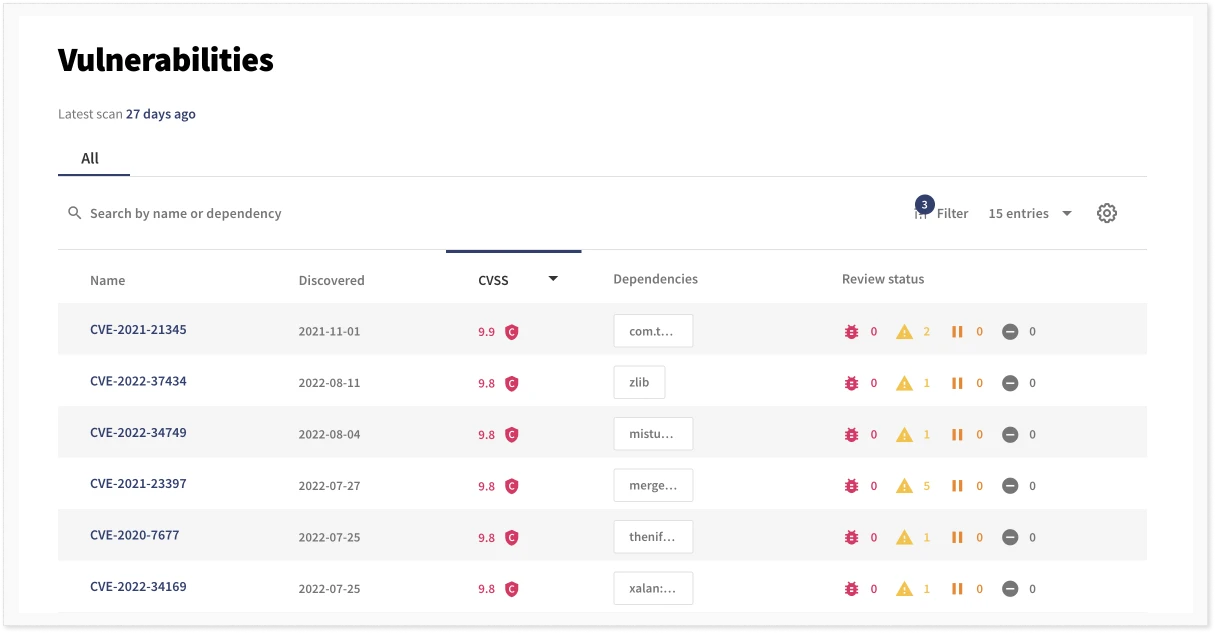
ML models predict exploit likelihood, estimate time-to-fix, and identify patterns beyond what CVSS scores alone provide. A dependency health scoring system flags risky packages even without known vulnerabilities.
What is OpenText Core SCA?
Debricked was founded to make SCA accessible to developers without sacrificing depth. After acquisition, it became OpenText Core SCA while keeping its developer-focused approach.
The Fortify SSC and Fortify on Demand integration means organizations can manage SAST and SCA findings in a single dashboard.
Key features
| Feature | Details |
|---|---|
| ML-powered analysis | Predicts exploit likelihood and time-to-fix beyond CVSS |
| Dependency health scoring | Maintenance activity, community size, release frequency assessment |
| Automated fix PRs | Version updates with breaking change warnings |
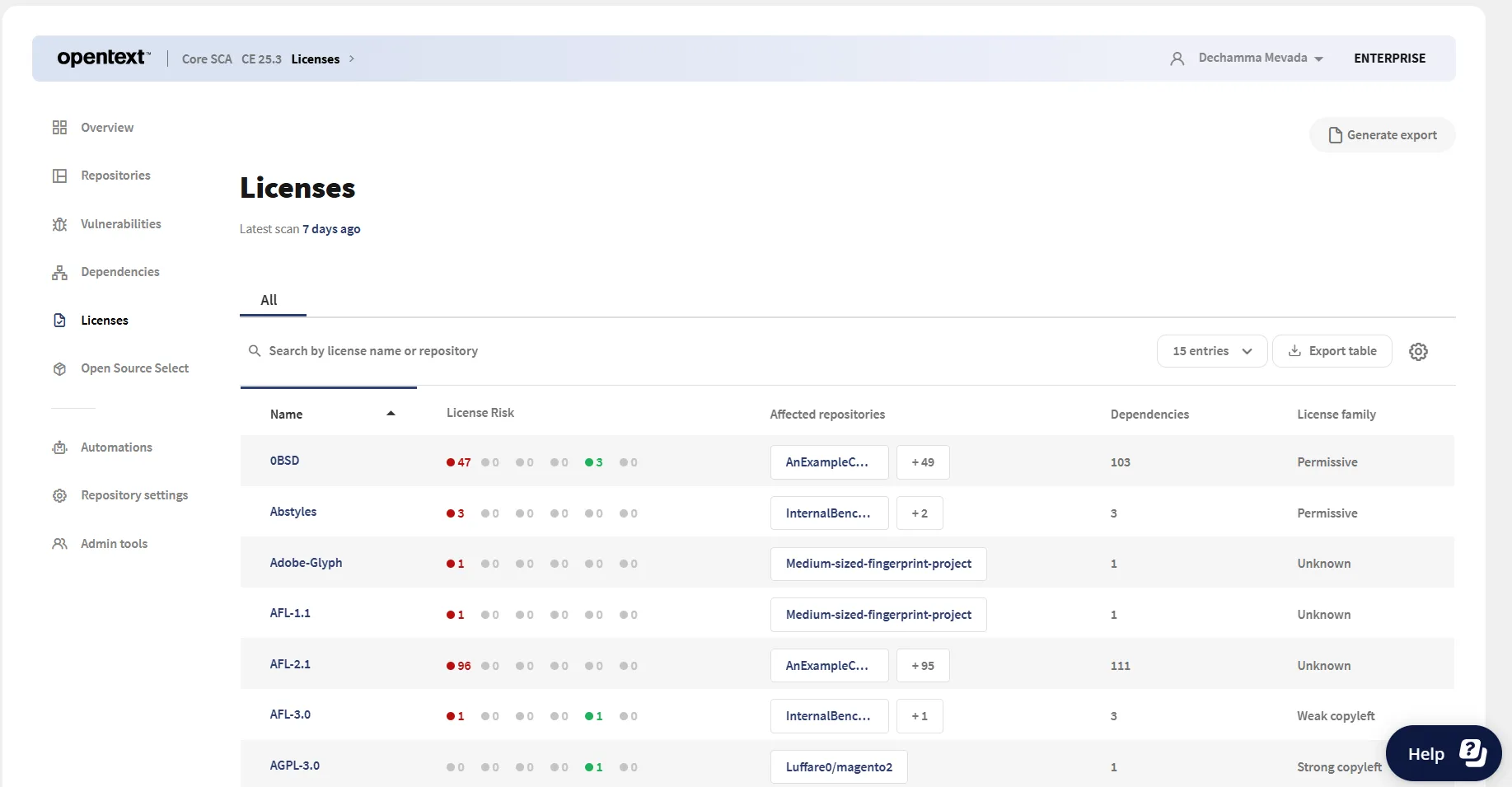
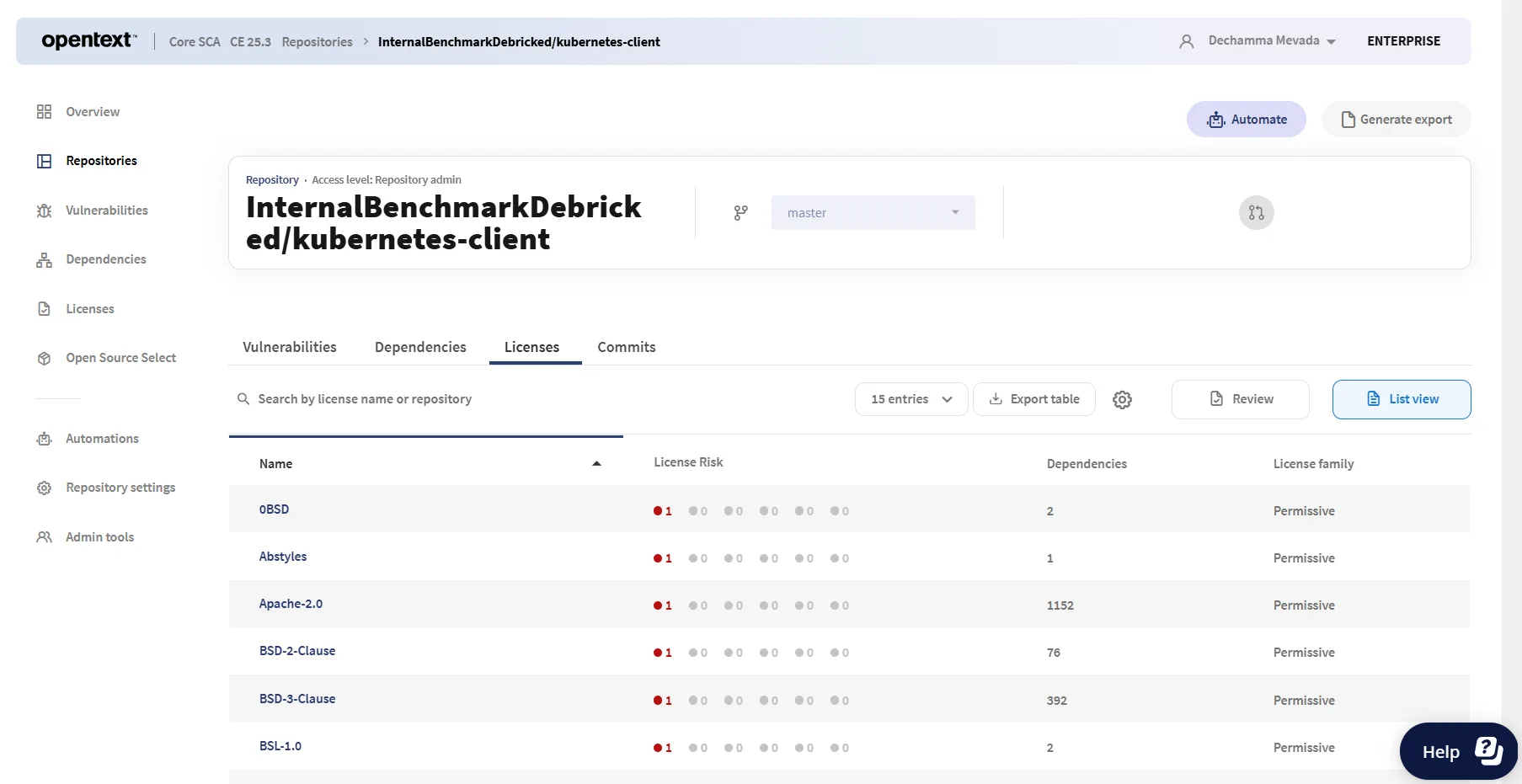
| License compliance | Hundreds of license types including custom and uncommon |
| SBOM generation | SPDX and CycloneDX formats with transitive dependencies |
| Ecosystems | npm, yarn, pnpm, pip, Poetry, Maven, Gradle, Go, Composer, Bundler, NuGet, Cargo |
| Fortify SSC | Native integration for unified SAST+SCA management |
| Pricing | Free tier for open-source; Premium and Enterprise plans |
ML-powered vulnerability analysis
Machine learning models enrich vulnerability data beyond CVE databases. The system predicts exploit likelihood, estimates time-to-fix, and identifies disclosure patterns to help teams prioritize based on actual risk.
Dependency health scoring
Each dependency receives a health score based on maintenance activity, community size, release frequency, and security track record. Low scores indicate risky dependencies even without known vulnerabilities.
Automated fix pull requests
The platform creates pull requests with version updates when vulnerabilities are detected. Fix PRs include context about changes and breaking change warnings.
License compliance
Detection covers hundreds of license types including custom and uncommon licenses. Policy rules flag copyleft, commercial restrictions, or specific requirements. Handles multi-license packages and license expressions.
SBOM generation
Generates SBOMs in SPDX and CycloneDX formats with transitive dependencies, license information, and vulnerability status.
Malicious package detection and reachability analysis
OpenText Core SCA’s ML-powered analysis is centred on vulnerability prioritization and dependency health scoring — not on behavioural analysis of packages the way Socket or Phylum-era Veracode run it. The product surfaces advisories on typosquats or compromised releases that already exist in public vulnerability feeds (NVD, vendor advisories, proprietary research), but it does not execute or sandbox packages to detect install-time scripts or exfiltration behaviour. For teams whose primary concern is malicious OSS, pair Core SCA with a behavioural tool rather than relying on it alone.
Reachability analysis is similarly scoped. Core SCA does not ship a function-level call-graph reachability layer comparable to Endor Labs or Snyk Open Source on supported languages. Where reachability-adjacent prioritization exists, it is handled through the ML model’s exploit-likelihood and time-to-fix prediction rather than static call-graph tracing. Teams that need explicit code-path reachability typically run a SAST scanner such as Fortify alongside Core SCA and correlate findings inside Fortify SSC.
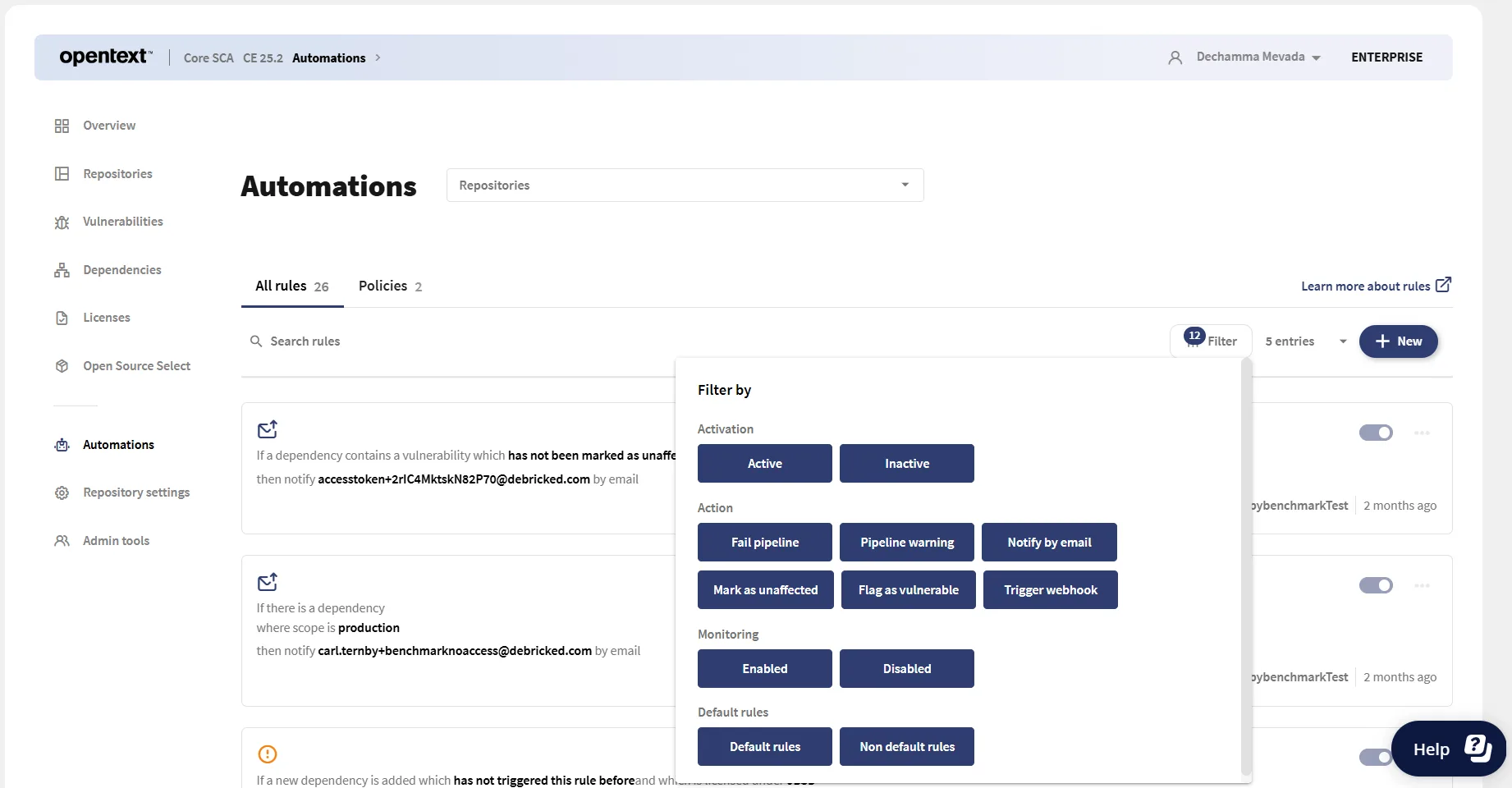
Integrations
The CLI hooks into Jenkins, GitHub Actions, GitLab CI, Azure DevOps, Bitbucket Pipelines, and CircleCI — the same six pipelines declared in the page’s frontmatter — so dependency scanning runs on every push or pull request without a dedicated scanner host. IDE plugins for VS Code and IntelliJ let developers inspect findings on a branch before opening a PR.
For unified AppSec management, the Fortify SSC connector forwards Core SCA findings into the same dashboard as Fortify SAST and Fortify on Demand results, so security and engineering leads review one correlated queue rather than two. Dependency update automation is handled through automated fix pull requests — the platform opens PRs with safe version bumps and breaking-change warnings, which teams typically pair with Renovate or Dependabot for the non-security update cadence.
Getting started
npm install -g @debricked/cli or brew install debricked/tap/cli on macOS.debricked auth login for OAuth, or set DEBRICKED_TOKEN for CI/CD environments.debricked scan . in your project directory. Resolve dependencies first for accurate results.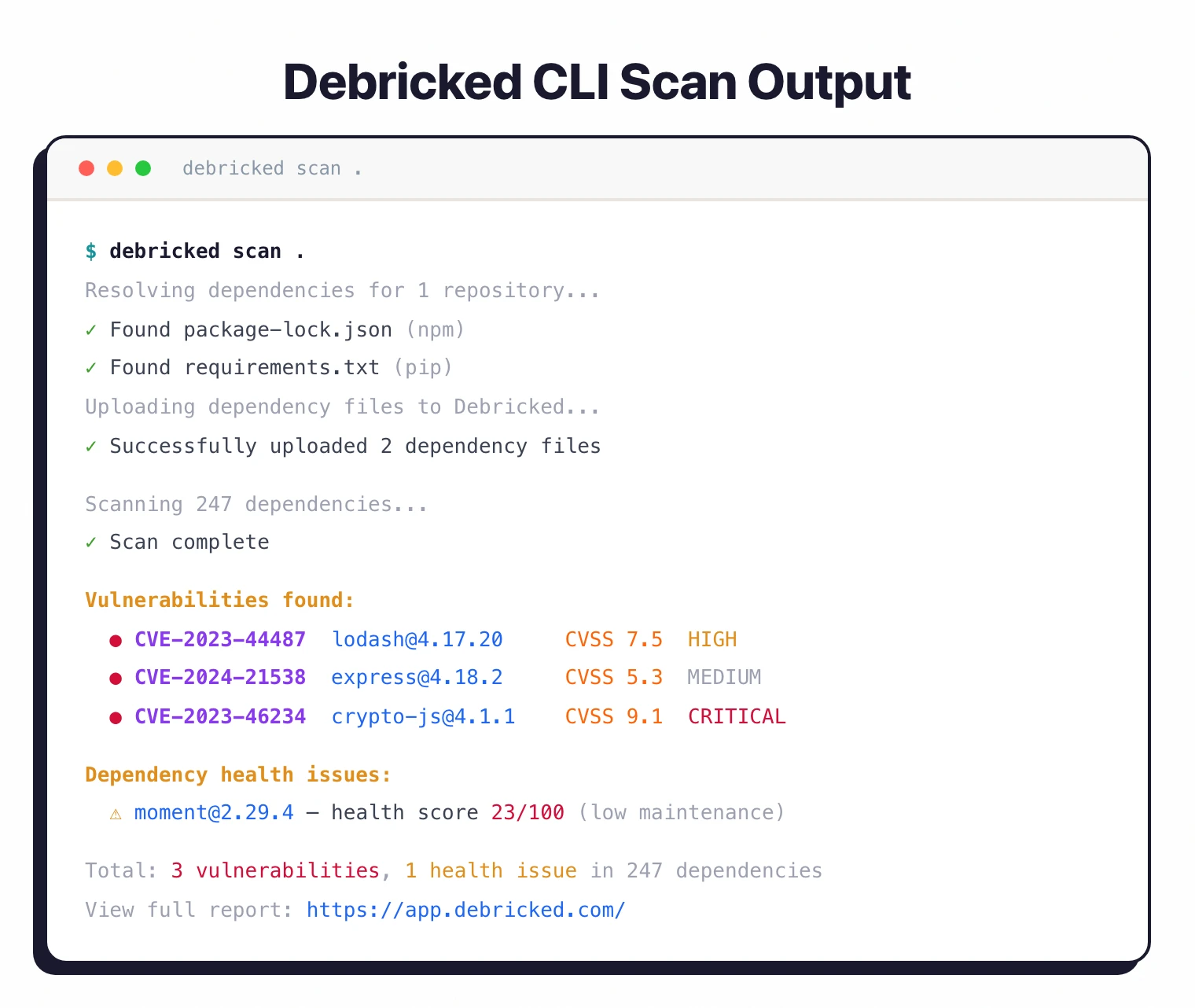
When to use OpenText Core SCA
OpenText Core SCA fits teams wanting developer-friendly SCA with ML-powered prioritization, especially those already using Fortify for SAST.
The ML models and dependency health scoring add intelligence beyond basic CVE matching. The free tier makes it accessible for open-source projects.
The main value of the paid tiers is the Fortify integration and team policy management.
If you do not use Fortify, the ML prioritization and health scoring are still useful, but you lose the unified dashboard advantage.
How it compares:
| vs. | Key difference |
|---|---|
| Snyk Open Source | Snyk has a larger ecosystem and broader language coverage. Debricked has ML-powered prioritization and Fortify integration. |
| Mend SCA | Mend has Renovate-powered remediation and merge confidence. Debricked has dependency health scoring and Fortify integration. |
| Dependabot | Dependabot is free and GitHub-native. Debricked adds ML analysis, health scoring, and Fortify integration. |
Further reading: What is SCA? | Open Source License Compliance
OpenText Core SCA pricing
Debricked.com publishes tier pricing publicly — a rarity among enterprise SCA tools. The SCA product ships in three tiers:
- Free — $0 forever. Includes vulnerability management, licence management, and project health. Capped at 1,000 scans in the first month, then 100 scans per month afterwards.
- Premium — $25 per contributing developer per month (or $275 billed annually per developer). Adds vulnerability and licence reports, API access with a 5,000-requests-per-hour limit, and chat/email support. Unlimited scans.
- Enterprise — starts from $30 per contributing developer per month (or $360 billed annually per developer). Adds enterprise support, SBOM export, enterprise SSO, higher computation limits, and unlimited API access.
The Open Source Select product — the dependency-health evaluation layer — is billed separately at $0 for Select Free and $96 per contributing developer per year for Select Enterprise. Neither tier publishes Fortify-bundle pricing; OpenText routes customers who want SCA plus Fortify SAST or Fortify on Demand through standard enterprise sales, where pricing is not published.
For current figures and the latest packaging, confirm directly on debricked.com/pricing — this is one of the few SCA vendors publishing tier numbers openly.
OpenText Core SCA alternatives
The main deciding axis for Core SCA is whether your organization already runs Fortify. Outside of that bundle, a few tools compete directly.
Snyk Open Source
Snyk Open Source is the developer-first default with broader ecosystem coverage and a real free tier. Pick Snyk when fast onboarding and per-developer pricing matter more than Fortify-correlated findings.
Black Duck
Black Duck goes deeper on licence analysis and binary scanning — the right pick for M&A due diligence or legal-heavy license audits. Core SCA is lighter on licence depth but carries tighter integration with Fortify SAST.
Mend SCA
Mend SCA runs a Renovate-style continuous dependency-update loop alongside security fix PRs, which Core SCA does not. Pick Mend when dependency hygiene is a first-class problem.
Dependabot
Dependabot is free and GitHub-native. It covers dependency alerts and update PRs without ML-based prioritization or Fortify integration — the pragmatic pick for GitHub-only teams that do not need an enterprise AppSec dashboard.
For a broader view, see the open-source SCA tools hub and the SCA tools overview.
OpenText Core SCA FAQ
Is this still Debricked?
Yes and no. The product originally launched as Debricked, was acquired by Micro Focus in 2022, and then folded into OpenText when OpenText acquired Micro Focus. It now ships as OpenText Core SCA but the Debricked.com domain, CLI binary, and developer-facing tooling still carry the Debricked name during the transition.
Does OpenText Core SCA require a Fortify licence?
No. Core SCA is a standalone SCA product — you can buy it, scan with it, and receive fix PRs without owning Fortify SAST or Fortify on Demand. The Fortify SSC integration is a bundle benefit for organizations that already run Fortify and want unified SAST+SCA dashboards, not a licensing prerequisite.
What ecosystems does it support?
The CLI resolves dependencies across npm, yarn, pnpm, pip, Poetry, Maven, Gradle, Go modules, Composer, Bundler, NuGet, and Cargo — the ecosystems declared in the key-features table above. Less-common build tools usually still work if you resolve the lockfile before scanning.
How does it relate to OpenText Fortify SCA (the other “SCA”)?
The names collide because OpenText’s portfolio now has two products using “SCA” — Core SCA (this one, formerly Debricked) is the developer-facing dependency scanner, while Fortify Static Code Analyzer (sometimes abbreviated SCA in Fortify docs) is the first-party SAST engine. Fortify SSC correlates findings from both.
Is there a free tier?
Yes. Debricked.com publishes a Free plan at $0 that includes vulnerability management, licence management, and project health, capped at 1,000 scans in the first month and 100 per month thereafter. Premium and Enterprise are paid and require a contributing-developer seat count; see the pricing section above for current shape.