Data Theorem Mobile Secure is a commercial mobile application security platform that combines SAST, DAST, SCA, and runtime protection in a single analyzer — covering iOS and Android apps from source code through deployed behavior.
Data Theorem protects applications serving over 2.8 billion users worldwide, including 7 of the top 10 largest banks. Unlike point tools that handle only static or dynamic analysis, Data Theorem runs all four testing types — SAST, DAST, SCA, and runtime — in a single pipeline.
What is Data Theorem?
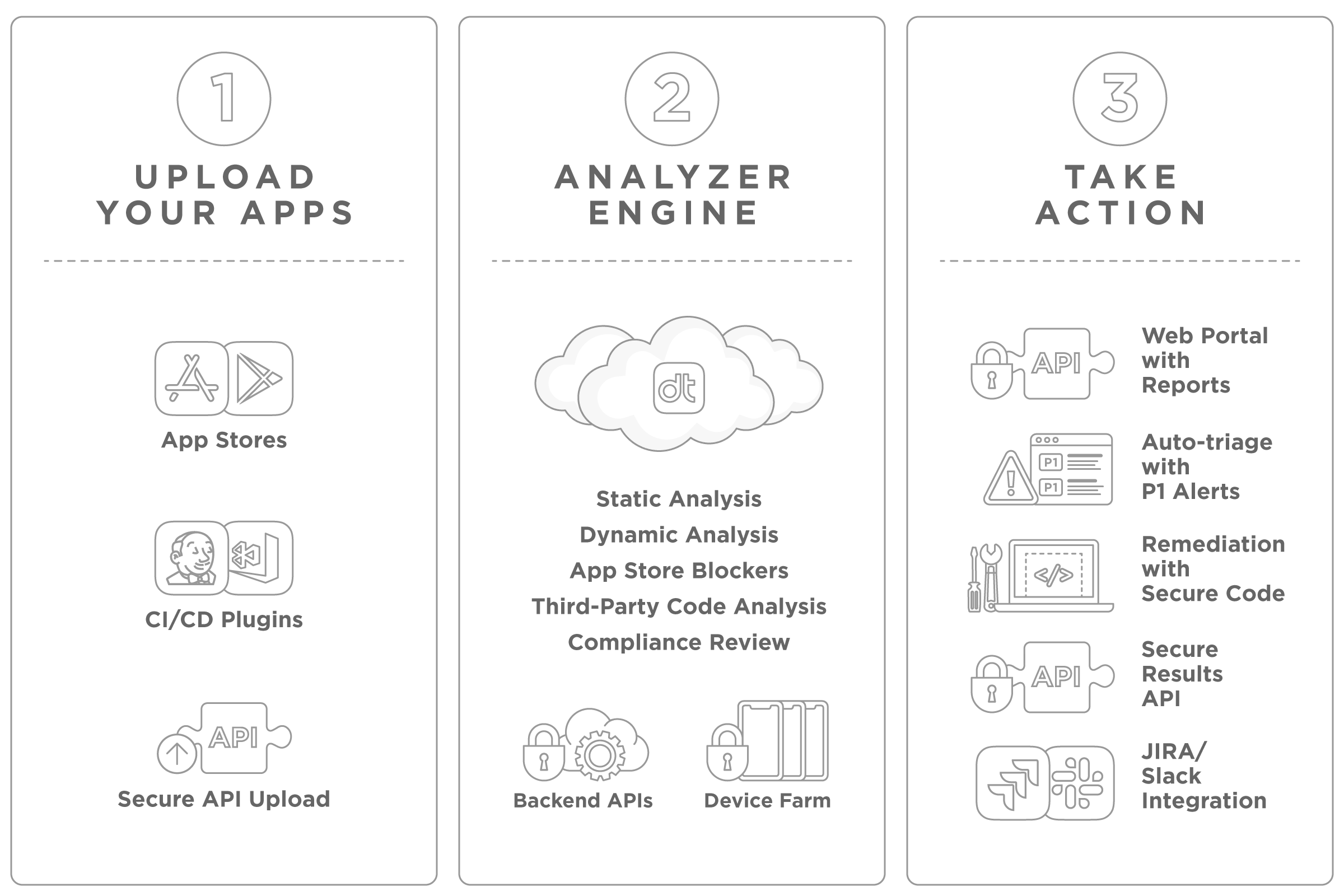
Data Theorem Mobile Secure is a full-stack mobile AppSec platform built specifically for iOS and Android. Its Analyzer Engine processes mobile app binaries through static analysis, dynamic testing, app store blocker checks, third-party code analysis, and compliance review — all in one pass.
You can upload apps directly, pull them from the Apple App Store or Google Play, or push binaries through CI/CD plugins and the upload API.
Findings are auto-triaged, with P1 alerts for critical issues and remediation suggestions that include secure code examples. Results come back through a web portal, a results API, or Jira/Slack integrations.
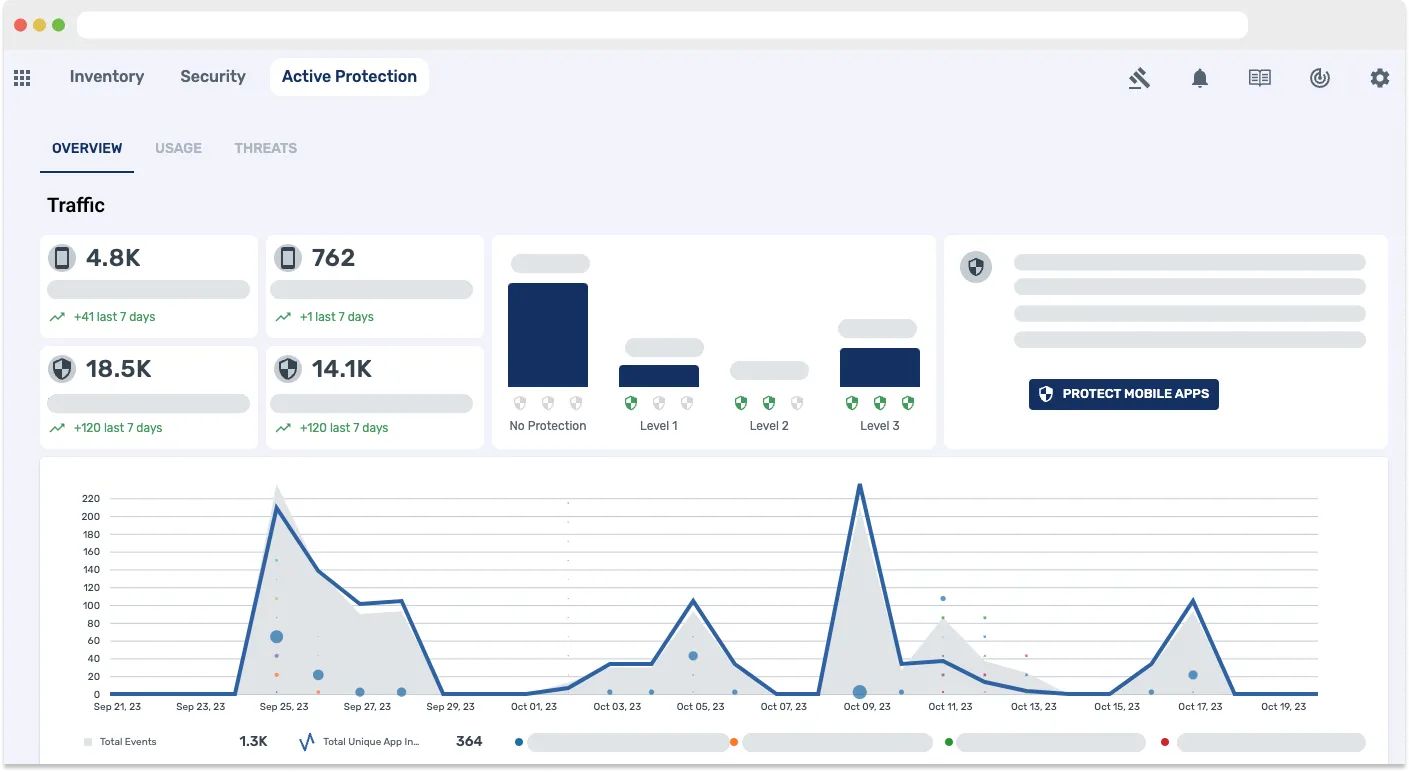
Data Theorem also scans the backend APIs that mobile apps talk to, and performs runtime behavioral analysis through its Active Protection layer.
Unlike static-only scanners, Active Protection watches real behavior: what data an app collects, how it communicates, and whether it stores sensitive information properly.
Customers include Cisco Duo, Zoom, Coinbase, and eBay. Data Theorem also holds kidSAFE certification for its Mobile Protect solution.
What are Data Theorem Mobile Secure’s key features?
| Feature | Details |
|---|---|
| Testing Types | SAST, DAST, SCA, runtime analysis |
| Platforms | iOS, Android |
| App Sources | Direct upload, App Store/Play Store, CI/CD, API |
| SDK Analysis | Third-party code firewall for embedded SDKs |
| Runtime Protection | Device integrity, jailbreak/root detection, hostile traffic observation |
| Integrations | Jenkins, Jira, Slack, CI/CD plugins, results API |
| Compliance | One-click reports, kidSAFE certified |
| Output | Web portal, auto-triage with P1 alerts, secure code suggestions |
App Store Monitoring
Data Theorem can pull public apps directly from the Apple App Store and Google Play for analysis — no build pipeline integration required. You can monitor published apps continuously from day one.
API Backend Scanning
Data Theorem discovers API endpoints by analyzing mobile app traffic, then tests those endpoints for authentication issues, injection vulnerabilities, and data exposure. A separate API Secure product is available for deeper API coverage.
Auto-Triage and Remediation
Findings are automatically prioritized. Critical issues trigger P1 alerts, and each finding comes with remediation guidance including secure code suggestions developers can apply directly.
OWASP MASVS / Mobile Top 10 Coverage
Data Theorem’s Analyzer Engine maps findings into the OWASP Mobile Application Security Verification Standard (MASVS) categories — MASVS-AUTH for credential issues, MASVS-CRYPTO for weak ciphers, MASVS-NETWORK for transport problems, MASVS-PLATFORM for IPC misuse, MASVS-RESILIENCE for anti-tamper, and MASVS-PRIVACY for data exposure.
The third-party SDK firewall lines up directly with OWASP Mobile Top 10 M2 (insecure supply chain). Tokenizing every embedded SDK and tying it to known CVEs is exactly what M2 calls for, which makes Data Theorem’s reports useful straight out of the box for compliance audits and MASTG-driven assessments.
What does Data Theorem Mobile Secure integrate with?
Data Theorem integrates with CI/CD pipelines and issue trackers to fit into existing development workflows.
Beyond Mobile
Data Theorem offers a broader product suite beyond Mobile Secure:
- API Secure — API discovery, security testing, and runtime protection
- Code SAST — SAST, SCA, and SBOM for source code
- Cloud Secure — Cloud-native application protection platform (CNAPP)
- AI Governance — Discovery and security for shadow AI
Organizations already using Mobile Secure can extend coverage to APIs, web apps, and cloud infrastructure without switching vendors.
How do I get started with Data Theorem Mobile Secure?
Data Theorem Pricing
Data Theorem does not publish pricing — every plan is enterprise-quoted by sales. Licensing is per-app or per-organization, scoped to the modules you turn on: Mobile Secure, API Secure, Web Secure, Cloud Secure, and AI Governance are each separate SKUs that can be bundled.
Most buyers I see end up on a multi-module bundle because Data Theorem’s pitch is full-stack coverage rather than a single mobile point tool — the SKU you pick depends on whether you want mobile-only, mobile + API, or full-stack with cloud and AI governance.
A manual penetration testing add-on is also available. Contact Data Theorem with app counts and module scope to get a quote.
When to Use Data Theorem
Data Theorem is a strong fit for organizations that need to secure both their mobile apps and the APIs behind them, especially in regulated industries.
Consider Data Theorem when:
- You need third-party SDK analysis to manage supply chain risk
- Runtime behavior analysis matters for your security program
- You manage both mobile apps and the APIs they connect to
- You want continuous monitoring of published apps from the app stores
- Privacy compliance and auto-triage are priorities
The platform is not a good fit if you only need a one-time static scan or if your budget requires open-source tooling. Unlike MobSF — which is free and covers basic static and dynamic analysis — Data Theorem adds continuous SDK monitoring, auto-triage P1 alerts, API backend scanning, and enterprise compliance reporting out of the box.
See the full mobile security tools category — and the API security tools hub if API Secure is on the shortlist — for more options.
Data Theorem Alternatives
Data Theorem is one of the most-evaluated full-stack mobile MAST + RASP platforms. The closest alternatives, depending on which slice matters most:
- NowSecure . Strong on privacy depth and detailed MASTG-aligned reporting. Often the head-to-head choice for North American buyers; Data Theorem typically wins on breadth (mobile + API + web + cloud) where NowSecure is mobile-focused.
- Zimperium zScan + zDefend (MAPS). Full-stack MAST plus on-device runtime defense. Closest to Data Theorem’s “scanner + Active Protection” combo, with a heavier on-device SDK footprint.
- AppKnox . Enterprise MAST with managed manual penetration testing. Strong in BFSI and regulated-industry shortlists, particularly in EMEA and APAC.
- Guardsquare DexGuard + iXGuard. Compiler-level obfuscation and hardening, narrower than Data Theorem (no SAST/DAST/SCA). Pair them when you need both shielding and scanning.
- Ostorlab Enterprise. Mobile + API + web scanner with an OSS edition (Asteroid). Lower entry price for mid-market teams that want comparable scanning scope without Data Theorem’s full suite.
For a wider category view, see my mobile security tools hub.