Dastardly is a free DAST scanner from PortSwigger that runs the Burp Suite scanning engine in a Docker container. Give it a URL, get JUnit XML results in under 10 minutes. No API keys, no configuration files, no account required.
PortSwigger built Dastardly for one purpose: fast, high-confidence security checks in CI/CD pipelines. It does not try to be a full DAST scanner.
It finds a focused set of vulnerabilities with minimal false positives.
Key Features
| Feature | Details |
|---|---|
| Price | Free, no limits |
| Scan engine | Burp Suite scanner core |
| Scan time | Under 10 minutes (hard cap) |
| Output | JUnit XML |
| Deployment | Docker container |
| Configuration | Zero — just provide a target URL |
| Auth scanning | Not supported |
| API keys | Not required |
Vulnerability Coverage
Dastardly checks for a focused set of high-confidence vulnerability types. Reflected XSS appears in the OWASP Top 10 under injection flaws, and the Verizon DBIR consistently identifies web application attacks as one of the top breach vectors — making even this narrow coverage valuable as a CI/CD safety net.
- Reflected cross-site scripting (XSS)
- CORS misconfigurations
- Vulnerable JavaScript dependencies
- Content-type mismatches
- Multiple content types specified
- HTML does not specify charset
- Duplicate cookies set
The limited scope is intentional. Every reported issue is a real problem worth fixing. Dastardly will not flood your pipeline with noise.
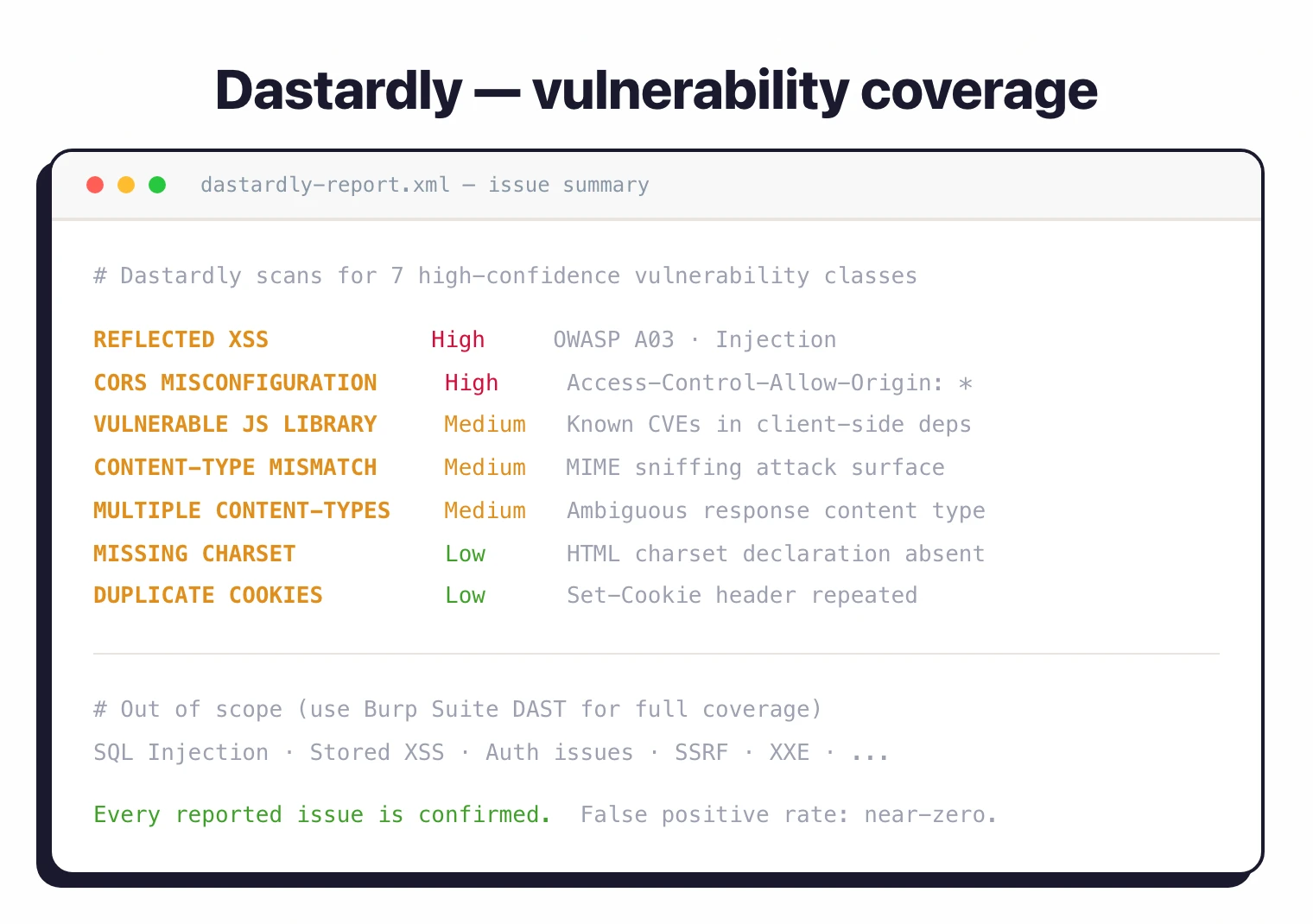
Dastardly does not attempt full DAST coverage. It finds the most common, highest-confidence web vulnerabilities in under 10 minutes.
For deeper scanning with authenticated testing, see Burp Suite DAST edition.
CI/CD Integration
GitHub Actions
name: Security Scan
on:
push:
branches: [main]
pull_request:
branches: [main]
jobs:
dast:
runs-on: ubuntu-latest
steps:
- name: Run Dastardly
uses: PortSwigger/dastardly-github-action@main
with:
target-url: 'https://staging.example.com'
- name: Upload Report
if: always()
uses: actions/upload-artifact@v4
with:
name: dastardly-report
path: dastardly-report.xml
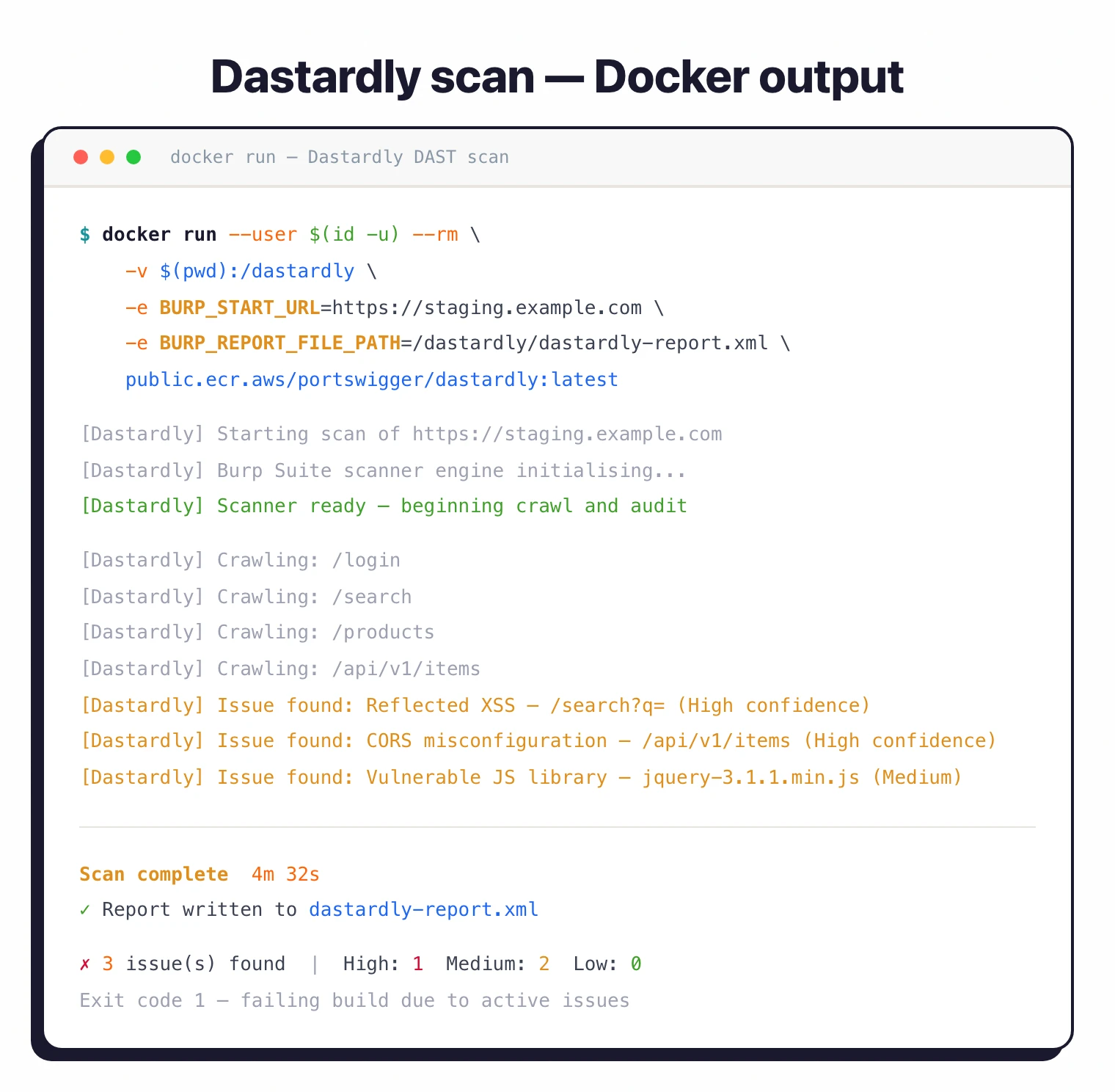
Docker (any CI system)
docker run --user $(id -u) --rm \
-v $(pwd):/dastardly \
-e BURP_START_URL=https://your-app.example.com \
-e BURP_REPORT_FILE_PATH=/dastardly/dastardly-report.xml \
public.ecr.aws/portswigger/dastardly:latest
GitLab CI
dast:
stage: test
image: public.ecr.aws/portswigger/dastardly:latest
variables:
BURP_START_URL: "$STAGING_URL"
BURP_REPORT_FILE_PATH: "/dastardly/gl-dast-report.xml"
artifacts:
reports:
junit: gl-dast-report.xml
The JUnit XML output works natively with Jenkins, GitHub Actions, GitLab CI, CircleCI, Azure DevOps, and virtually every other build system.
Getting Started
docker pull public.ecr.aws/portswigger/dastardly:latestTeams that want a free, zero-friction security gate in CI/CD. Run it on every pull request. If Dastardly finds something, it is almost certainly real.
Think of it as a smoke test for web security, not a full assessment. When you need deeper scanning, upgrade to Burp Suite DAST.
Limitations
Dastardly does not support authenticated scanning, custom scan profiles, or API specification imports. It cannot test pages behind login forms.
The 10-minute cap means large applications get incomplete coverage. It checks a narrow set of vulnerability types compared to full DAST tools.
For authenticated scanning, API testing, or full OWASP Top 10 coverage, you need a commercial DAST tool like Acunetix or Invicti.
Our free DAST tools guide covers other no-cost options, including ZAP which offers broader coverage. Dastardly is the entry point, not the replacement.