Nuclei Alternatives: 8 Better DAST & Vulnerability Scanners in 2026
Nuclei alternatives for teams that need more than template-based checks — crawling DAST, authenticated scanning, and business logic testing compared.
Top Nuclei Alternatives
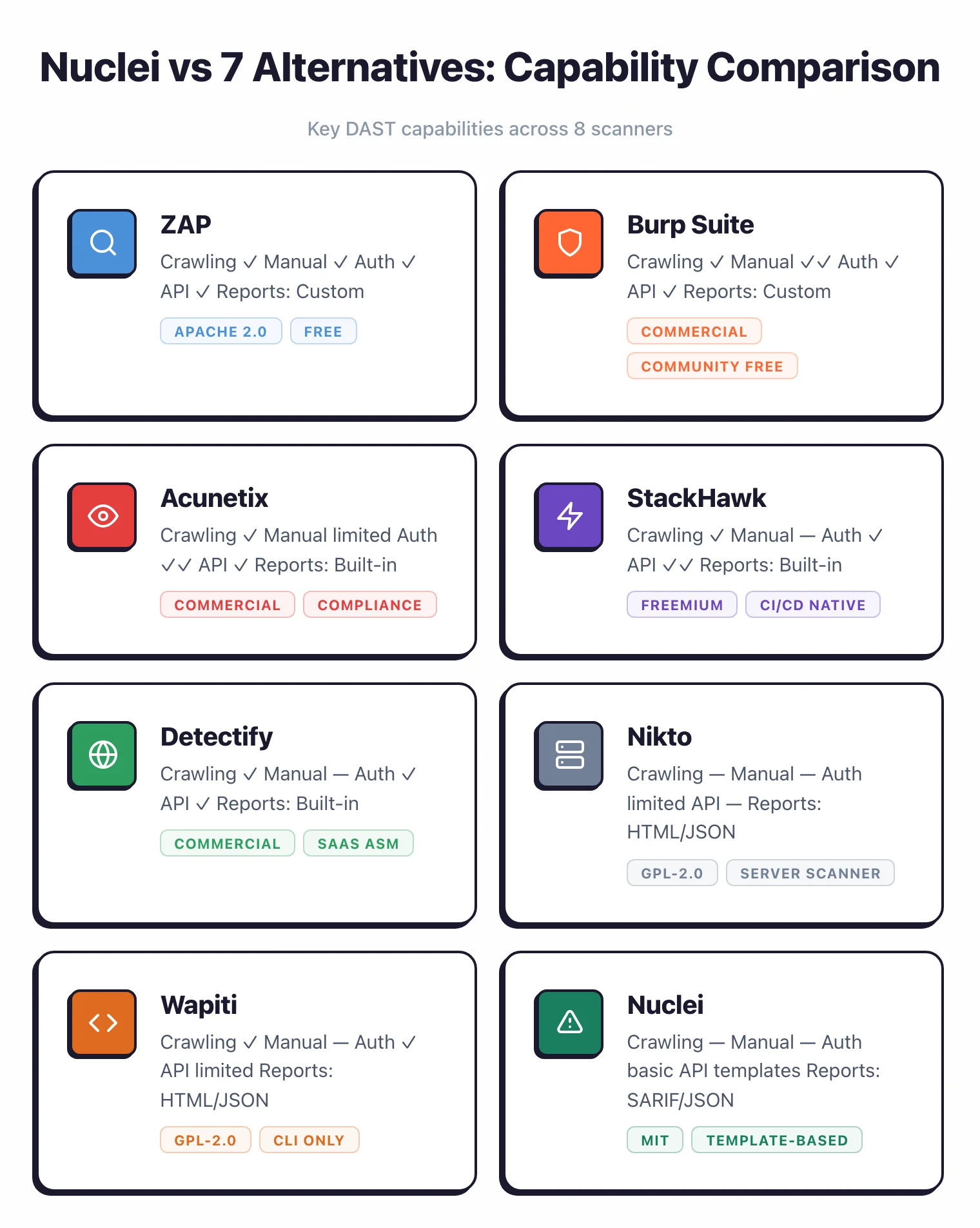
View all 29 alternatives →- Nuclei runs 12,000+ YAML templates for known CVEs and misconfigurations, but it does not crawl applications, test business logic, or find custom application flaws.
- ZAP is the closest free alternative for teams that need a full DAST proxy with an automated scanner, spider, and fuzzer — all under Apache 2.0.
- Burp Suite Professional stays the standard for manual web penetration testing with its intercepting proxy, Repeater, Intruder, and Collaborator for out-of-band detection.
- Acunetix and Detectify bring authenticated crawling, business logic testing, and compliance-ready reports that template scanners cannot produce.
- Most security teams keep Nuclei for fast known-CVE detection and pair it with a crawling DAST tool like ZAP, Burp Suite, or StackHawk for application-level testing.
Why Look for Nuclei Alternatives?
The most useful Nuclei alternatives in 2026 are ZAP, Burp Suite, Acunetix, StackHawk, Detectify, Nikto, and Wapiti.
Nuclei is a template-based vulnerability scanner built by ProjectDiscovery. It is fast, deterministic, and backed by 12,000+ community YAML templates covering known CVEs, misconfigurations, default credentials, and exposed endpoints.
With roughly 28,000 GitHub stars and an MIT license, it has become a staple in reconnaissance and CVE validation workflows.
But Nuclei has deliberate limits. It runs checks defined in templates — it does not crawl your application, click through forms, or reason about business logic.
Note: Nuclei does not crawl your application, click through forms, or reason about business logic. Template checks fire only when the request pattern matches — anything requiring navigation, session state, or multi-step flows is invisible to it.
The most common reason teams look for alternatives is that they need a crawling DAST scanner that actually walks the application and probes dynamic behavior — not a fast runner of predefined checks.
Custom application logic is another blind spot. If your app has a multi-step checkout, an authenticated admin panel, or an API requiring a signed token, Nuclei will not automatically discover those flows.
You would have to write templates for each endpoint — and even then the tool cannot reason about state between requests.
Authenticated scanning is the third gap. Nuclei supports basic auth headers and cookies, but it has no session management, no login recorder, and no handling of CSRF tokens or multi-factor flows.
Commercial DAST tools solve this with recorded login sequences and session replay. Teams that need polished reporting for compliance also hit a wall — Nuclei outputs JSON, JSONL, SARIF, and Markdown, which are great for engineers but light on the executive-friendly PDFs that PCI DSS, HIPAA, or SOC 2 auditors expect.
Pro tip: If authenticated scan coverage is a requirement — OAuth flows, CSRF-protected forms, or multi-factor login — start with Acunetix or StackHawk. Both support recorded login sequences out of the box, which saves hours of custom scripting.
For that, a commercial scanner with built-in compliance templates saves hours of manual report assembly.
Top Nuclei Alternatives
1. ZAP (Zed Attack Proxy)
ZAP is the most complete free alternative to Nuclei. Maintained by Checkmarx (previously an OWASP flagship project), it has nearly 15,000 GitHub stars as of April 2026 and sits under the Apache 2.0 license.
Where Nuclei runs predefined checks, ZAP actively crawls the application, builds a site tree, and probes endpoints dynamically through its spider, AJAX spider, and active scanner .
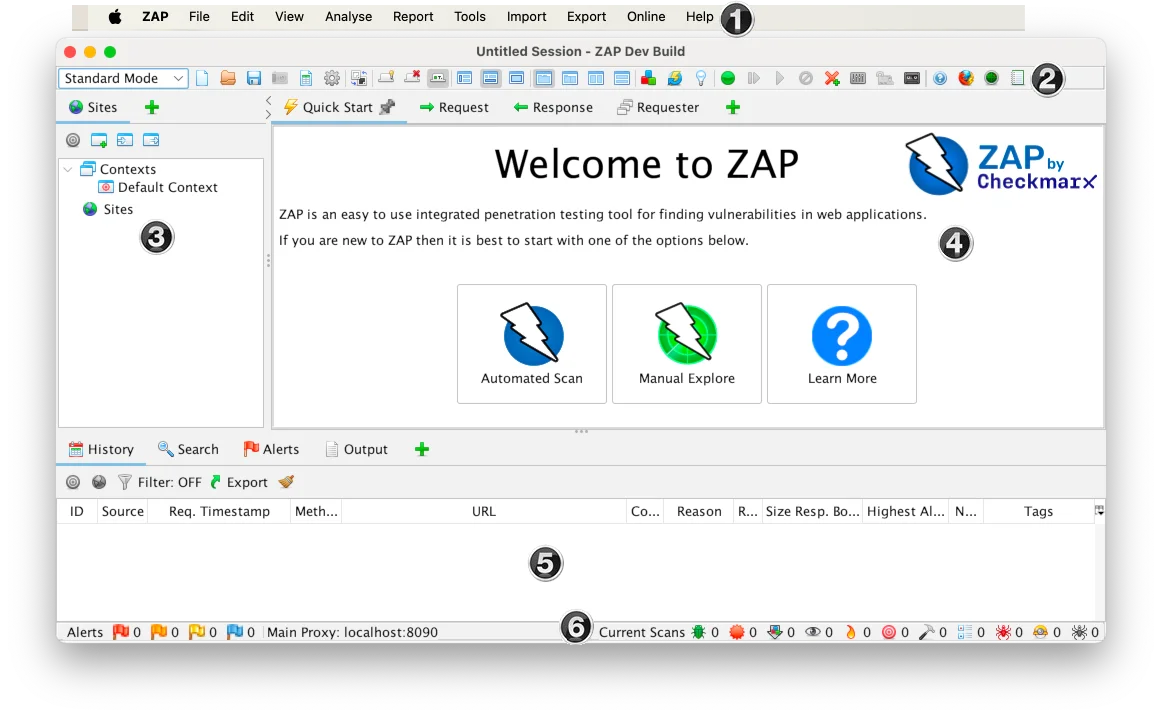
The manual testing side is where ZAP really separates from Nuclei. It ships with an intercepting proxy, Fuzzer, WebSocket support, and a plugin marketplace covering REST, GraphQL, and SOAP API scanning.
Key Insight
The manual testing side is where ZAP really separates from Nuclei — the intercepting proxy, Fuzzer, and WebSocket support turn it into a hands-on tool that Nuclei's template runner can never match.
A YAML-based automation framework supports CI/CD integration, and the official Docker images make it easy to slot into pipelines.
Best for: Teams that want a full DAST scanner with both manual and automated capabilities at zero cost. License: Open-source (Apache 2.0) Key difference: Active crawling and dynamic probing rather than predefined template checks. Includes an intercepting proxy, fuzzer, and authenticated scan support.
2. Burp Suite
Burp Suite is the standard toolkit for web application security testing. Pre-installed in Kali Linux and widely taught in security training, it provides an intercepting proxy, Repeater, Intruder, Comparer, and an extensible scanner.
Burp Collaborator detects blind SSRF, blind XSS, and other out-of-band vulnerabilities that most automated scanners miss entirely.
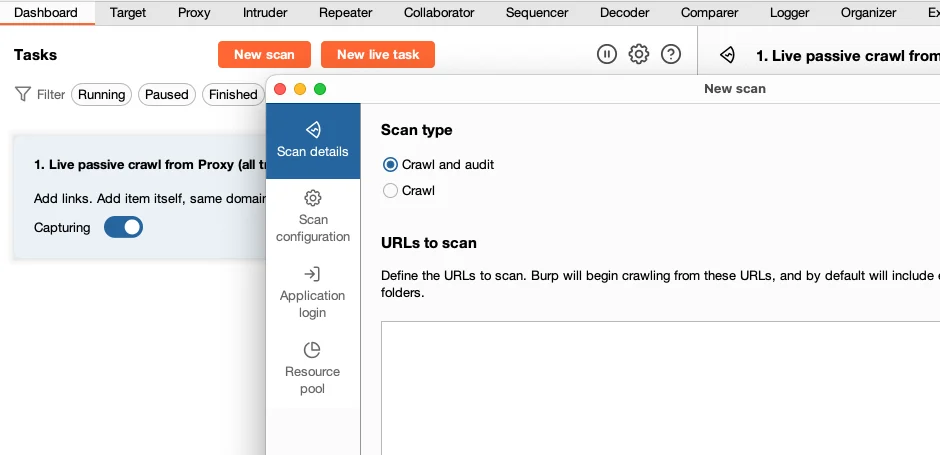
The contrast with Nuclei is stark. Nuclei is a scripted runner of known checks; Burp Suite is a manual pentesting cockpit.
The BApp Store adds hundreds of extensions covering JWT manipulation, authorization testing, and content discovery. Burp AI is built into the Professional edition for vulnerability triage assistance.
Best for: Hands-on security testers and penetration testers who need deep manual testing tools and out-of-band detection. License: Community (free, limited) / Professional (commercial) Key difference: Manual testing workflow with intercepting proxy, Repeater, Intruder, and Collaborator — capabilities Nuclei does not offer.
3. Acunetix
Acunetix is a commercial DAST scanner from Invicti with 7,000+ vulnerability checks and a Business Logic Recorder that captures multi-step workflows.
AI-powered Predictive Risk Scoring prioritizes findings by exploitability, and the AcuSensor IAST agent can be installed alongside DAST scanning for combined coverage.
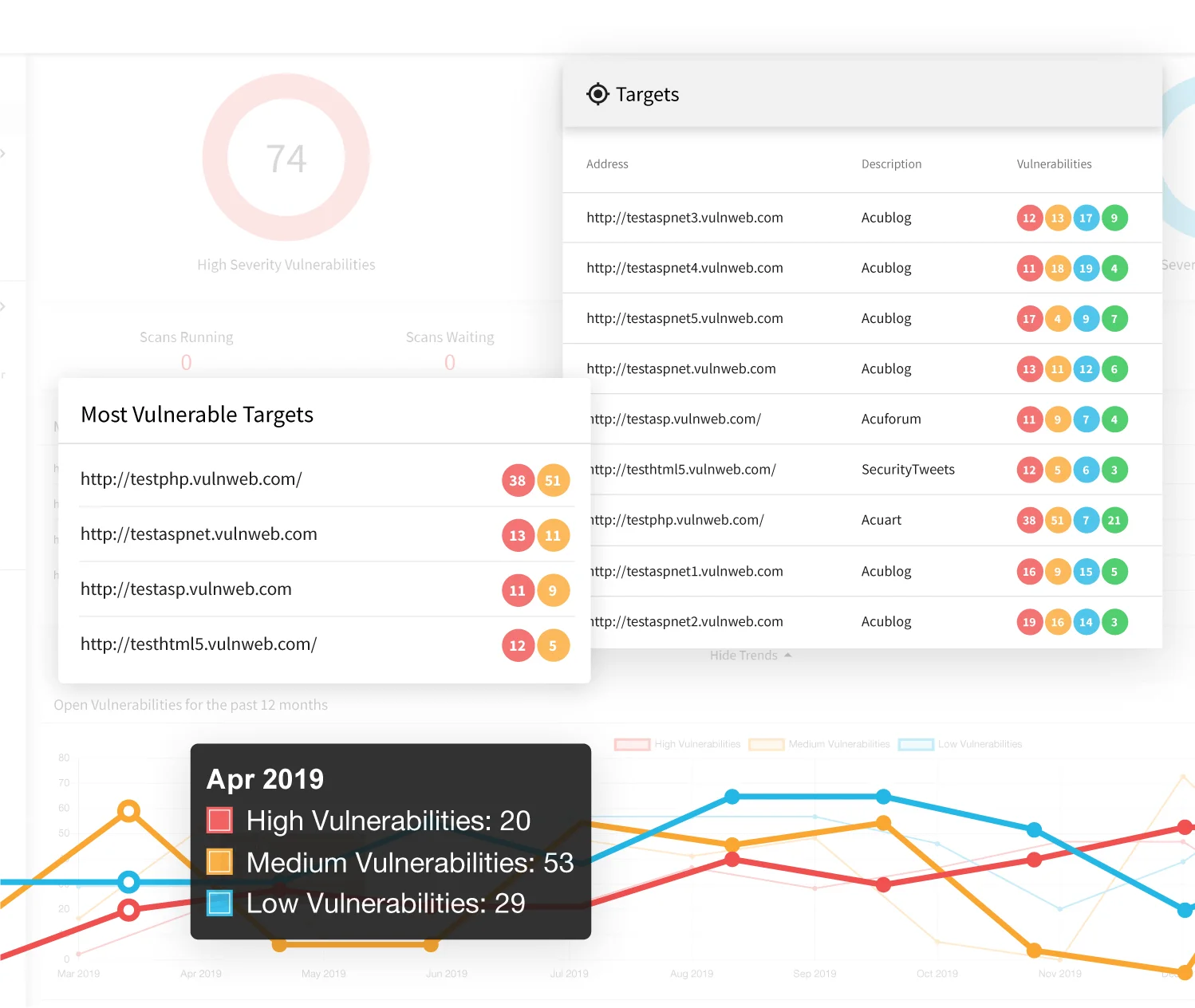
Authenticated scanning is a strength. Acunetix supports form-based login, NTLM, OAuth, and recorded login sequences for complex auth flows.
Reports ship with pre-built templates for PCI DSS, HIPAA, ISO 27001, NIST, and other compliance frameworks, which saves teams the hours they would otherwise spend reformatting Nuclei JSON into auditor-friendly PDFs.
Best for: Organizations that need authenticated crawling, business logic testing, and compliance-ready reporting. License: Commercial Key difference: Crawling DAST with authenticated scanning, business logic workflow recording, and out-of-the-box compliance reports.
4. StackHawk
StackHawk is built for developers and CI/CD. Its HawkScan engine — a complete re-engineering of ZAP’s original foundation into a container-first, cloud-native platform — wraps that scanning capability in a developer-friendly interface with YAML configuration and fast setup.
It supports REST, GraphQL, gRPC, and SOAP API testing, and HawkAI provides API discovery for unclassified endpoints.
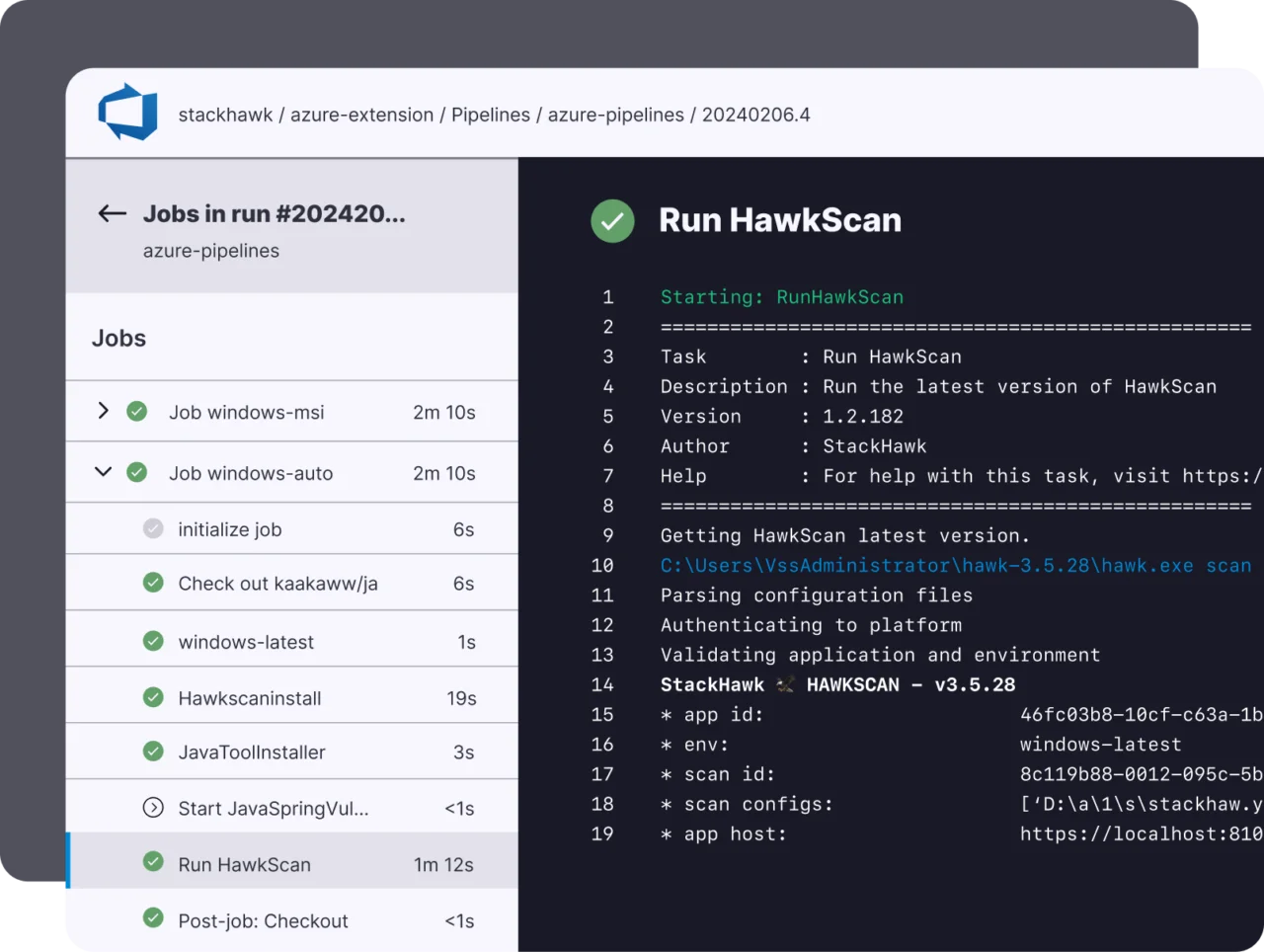
Integrations cover GitHub Actions, GitLab CI, Jenkins, CircleCI, and Azure DevOps. Scan times run 3 to 10 minutes, which fits PR-level feedback loops.
Unlike Nuclei, which scans endpoints you feed it, StackHawk crawls the application and performs dynamic active scanning — and it handles authentication through tokens, cookies, or recorded login scripts.
Best for: Developer teams that want automated, crawling DAST in CI/CD with API-first support. License: Freemium Key difference: Developer-focused UX, YAML-based configuration, and native CI/CD integrations built on a cloud-native scanning engine evolved from ZAP’s foundations.
5. Detectify
Detectify is a SaaS DAST scanner that differentiates through its Crowdsource program — a curated network of 400+ ethical hackers who contribute vulnerability modules.
Those human-researched findings become automated checks, giving Detectify 1,765+ modules built from real-world exploit patterns rather than only known CVEs.
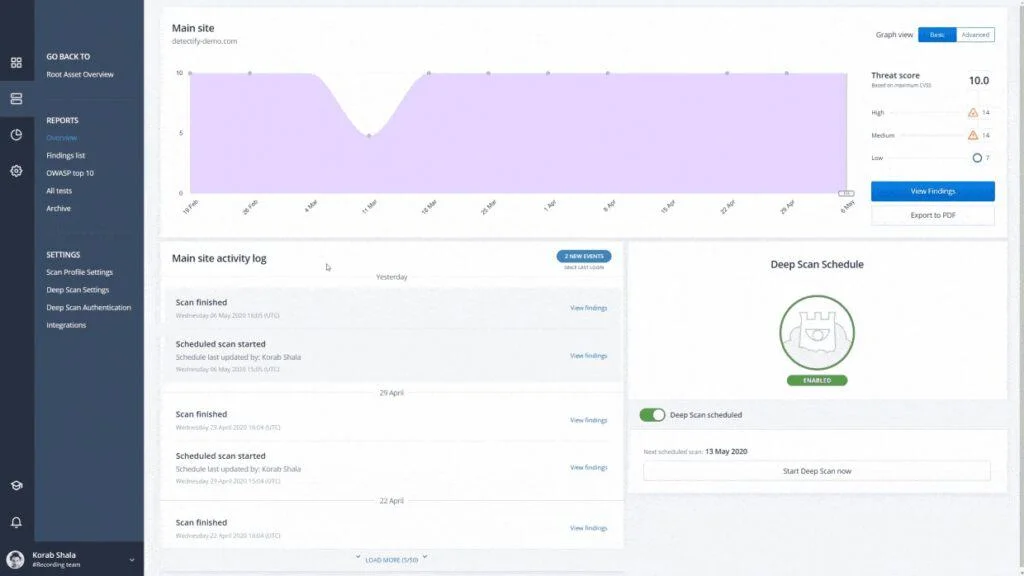
The platform has two products: Surface Monitoring (asset discovery and continuous monitoring) and Application Scanning (deeper authenticated DAST).
Where Nuclei relies on community YAML templates, Detectify relies on its curated Crowdsource research pipeline — fewer but more context-rich findings with new modules validated and live within 15 minutes.
Best for: Organizations that want external attack surface monitoring and crowdsourced vulnerability intelligence built into their DAST. License: Commercial Key difference: Crowdsource-driven vulnerability research, asset discovery, and authenticated application scanning — all delivered as SaaS.
6. Nikto
Nikto is a fast, no-frills web server scanner that checks for 7,000+ potentially dangerous files, scripts, and server misconfigurations.
It has been around since the early 2000s and is pre-installed in Kali Linux. Nikto focuses on server-level issues rather than application-level vulnerabilities — outdated server versions, dangerous default files, directory indexing, and common misconfigurations that overlap partially with Nuclei’s misconfiguration templates.
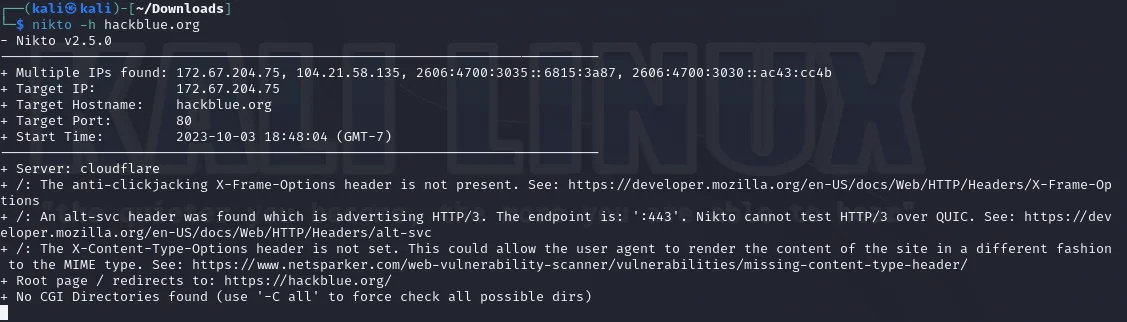
The tool runs from the command line and outputs HTML, XML, JSON, CSV, and plain text. It is not a full DAST scanner and has no crawling, authentication, or modern vulnerability detection to match Nuclei’s template breadth.
Best for: Quick server-level reconnaissance checks during penetration tests and infrastructure audits. License: Open-source (GPL-2.0) Key difference: Server-focused misconfiguration scanner, not an application scanner. Useful alongside Nuclei rather than as a replacement.
7. Wapiti
Wapiti is a free, command-line DAST scanner written in Python. It uses a black-box approach — crawling the web application first to build a URL map, then injecting payloads to test for vulnerabilities.
The scan modules cover SQL injection, XSS, file inclusion, command injection, XXE, CRLF injection, SSRF, and open redirects.
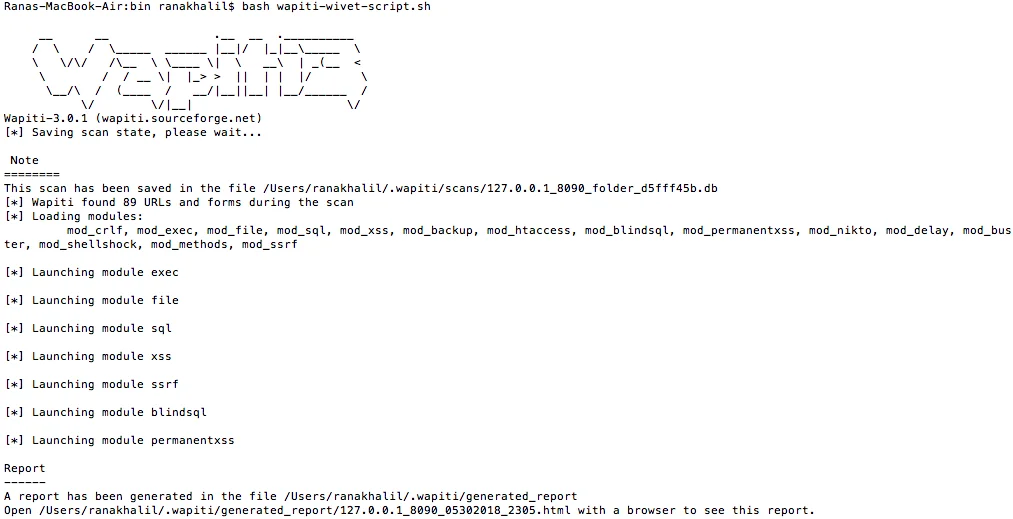
Wapiti supports multiple auth methods (Basic, Digest, Kerberos, NTLM) and handles session cookies, which Nuclei does not do out of the box.
Output formats include HTML, JSON, XML, and plain text, and the scanner runs happily inside CI/CD containers.
Best for: Teams that want a free crawling DAST scanner with active payload-based testing from the command line. License: Open-source (GPL-2.0) Key difference: Active crawling and payload injection for SQLi, XSS, and other application-level flaws. Unlike Nuclei, it discovers endpoints and probes them dynamically.
Feature Comparison
| Feature | Nuclei | ZAP | Burp Suite Pro | Acunetix | StackHawk | Detectify | Nikto | Wapiti |
|---|---|---|---|---|---|---|---|---|
| License | Open-source (MIT) | Open-source (Apache 2.0) | Commercial | Commercial | Freemium | Commercial | Open-source (GPL-2.0) | Open-source (GPL-2.0) |
| Approach | Template-based checks | Crawling DAST + proxy | Manual proxy + scanner | Crawling DAST | Crawling DAST | SaaS DAST + ASM | Server scanner | Crawling DAST |
| Crawls applications | No | Yes | Yes (manual/active) | Yes | Yes | Yes | No | Yes |
| Manual testing | No | Yes | Full toolkit | Limited | No | No | No | No |
| Authenticated scanning | Basic headers/cookies | Yes | Yes | Recorded sequences | Tokens, cookies, scripts | Yes | Limited | Basic, Digest, NTLM |
| API scanning | HTTP templates | REST, GraphQL, SOAP | Yes | OpenAPI, Postman | REST, GraphQL, gRPC, SOAP | Yes | No | Limited |
| CI/CD native | Yes (Go binary) | YAML automation | DAST edition | Yes | Core feature | Via API | CLI-only | CLI-only |
| Vulnerability modules | 12,000+ YAML templates | Add-ons marketplace | BApp Store extensions | 7,000+ checks | Active scan rules | 1,765+ Crowdsource modules | 7,000+ server checks | Modular |
| Compliance reports | SARIF, JSON | Custom | Custom | Built-in templates | Built-in | Built-in | None | HTML, JSON |
When to Stay with Nuclei
Nuclei remains the right choice in several scenarios:
- You need fast known-CVE detection across many targets. Nothing matches Nuclei for firing off thousands of precise checks against a target list in seconds. New CVE templates often appear within hours of public disclosure, which keeps the scanner current.
- You value deterministic, transparent checks. Every Nuclei template is a readable YAML file. You can see exactly what request is sent and what response indicates a finding — no black-box scanner logic to trust.
- Your workflow centers on reconnaissance. Nuclei pairs beautifully with other ProjectDiscovery tools (subfinder, httpx, katana) for asset discovery plus vulnerability validation across large surfaces. If you already use that stack, Nuclei slots in without friction.
- You want a single Go binary with no runtime dependencies. Nuclei drops into any CI/CD pipeline, container, or ephemeral runner with a single download. No Java, no Python, no browser dependency.
- Template customization is a requirement. Writing a Nuclei template for a custom check takes minutes, and the
-aiflag generates templates from natural language descriptions. For teams that want internal security rules versioned in Git, this is hard to beat.
Key Insight
Many teams run Nuclei alongside a crawling DAST tool — Nuclei for fast known-CVE validation across large surfaces, ZAP or StackHawk for the crawled, authenticated application layer. The two approaches are complementary, not competitive.
For teams that need more than template-driven checks — authenticated crawling, business logic testing, manual pentesting, or compliance reporting — one of the alternatives above will fit better. Many teams run Nuclei alongside a crawling DAST tool so they get the best of both worlds.
For detailed reviews of each alternative, browse the AppSec Santa DAST tools category or read the what is DAST primer.
Frequently Asked Questions
What is the best free alternative to Nuclei?
Is Nuclei enough on its own, or do I need another scanner?
Which Nuclei alternative is best for CI/CD pipelines?
Can ZAP replace Nuclei for known-CVE scanning?
What is the best Nuclei alternative for API security testing?

Founder, AppSec Santa
Years in application security. Reviews and compares 215 AppSec tools across 12 categories to help teams pick the right solution. More about me →






