APIs are the dominant attack surface for web applications. Gartner predicted that by 2022, API abuses would become the most frequent attack vector for enterprise web applications — and the trend has continued since.
Traditional DAST tools like Burp Suite , Invicti , and Acunetix were designed to crawl web applications by following HTML links. They work poorly against APIs that return JSON without any HTML for the scanner to parse.
This guide covers tools built specifically for API security testing: tools that consume OpenAPI specifications, GraphQL schemas, and Postman collections to enumerate and test API endpoints systematically.
API DAST vs web DAST
Traditional web DAST tools crawl applications by following anchor tags, submitting forms, and probing HTML page inputs. This approach breaks down for APIs in several ways.
No HTML to crawl. A JSON REST API returns no anchor tags or form inputs. A traditional DAST crawler cannot discover endpoints by following links — it needs the API specification to know what endpoints exist and what parameters they accept.
Authentication complexity. APIs typically use bearer tokens, API keys, or OAuth 2.0 flows rather than session cookies set by HTML login forms. Traditional DAST tools need manual configuration to handle token-based authentication; API DAST tools handle these natively.
OWASP API Top 10 coverage. Web DAST tools test for XSS, SQL injection, and command injection — all relevant to APIs, but not the primary API risks. BOLA/IDOR (Broken Object Level Authorization) , broken function-level authorization , and mass assignment are the top API vulnerabilities and require API-aware testing logic to detect.
Schema-based test generation. API DAST tools consume an OpenAPI 3.0 spec or GraphQL schema to automatically generate test cases for every endpoint, method, and parameter combination. This produces higher coverage than manual test case creation.
Top API DAST tools
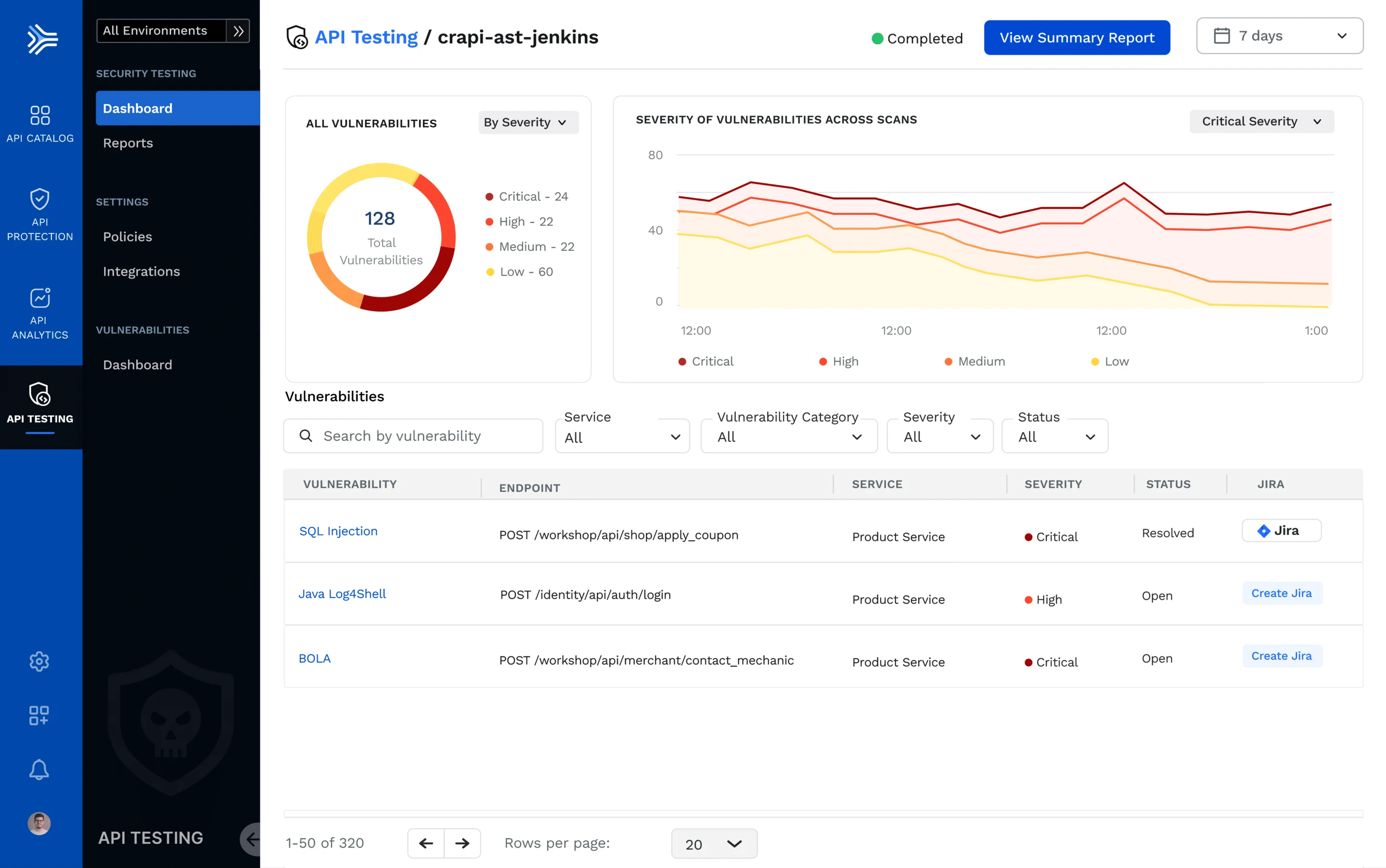
1. Escape
Escape is an API security testing platform built specifically for REST and GraphQL APIs. It ingests an OpenAPI spec or GraphQL schema and generates hundreds of security tests covering the OWASP API Security Top 10 , business logic flaws, and authentication issues.
What Escape does well: GraphQL security testing is Escape’s strongest differentiator.
It tests for introspection exposure , batching attacks (sending hundreds of queries in a single HTTP request to exhaust rate limits), deeply nested query abuse, and authorization bypass through field-level access control gaps. Few tools test GraphQL as thoroughly as Escape.
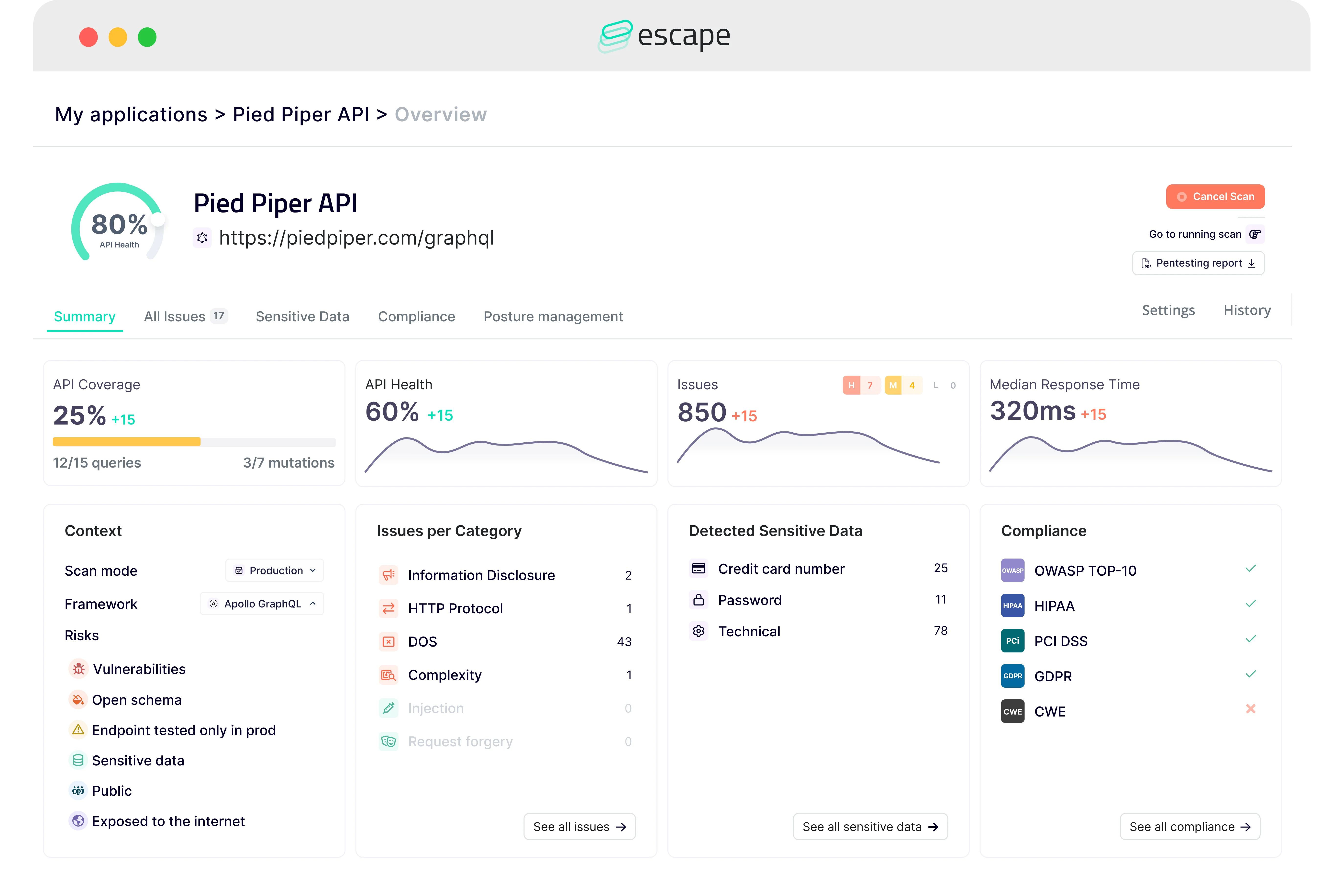
For REST APIs, Escape covers BOLA/IDOR testing by modifying resource identifiers across authenticated users, mass assignment by injecting unexpected properties, and rate limiting gaps by sending repeated requests at varying intervals. Scan configuration is done via a YAML file committed to the repository, making scans reproducible and code-reviewable.
The Escape CI/CD integration runs in GitHub Actions, GitLab CI, and CircleCI. A scan of a medium-complexity API typically completes in under 15 minutes.
Best fit: Teams with GraphQL APIs who need security testing beyond what REST-focused tools provide, or development teams that want DAST integrated directly into their CI/CD pipeline with minimal manual configuration.
2. 42Crunch
42Crunch takes an API security approach centered on the OpenAPI specification itself. It provides two products: API Security Audit (static analysis of the OpenAPI spec for security issues) and Conformance Scan (dynamic testing that validates API runtime behavior against its spec).
What 42Crunch does well: Spec-first testing is the core approach. API Security Audit scores your OpenAPI specification against 300+ security checks — missing security schemes, endpoints that accept any input without schema validation, overly permissive CORS configurations, and missing rate limit headers. This catches security design issues before any code is deployed.
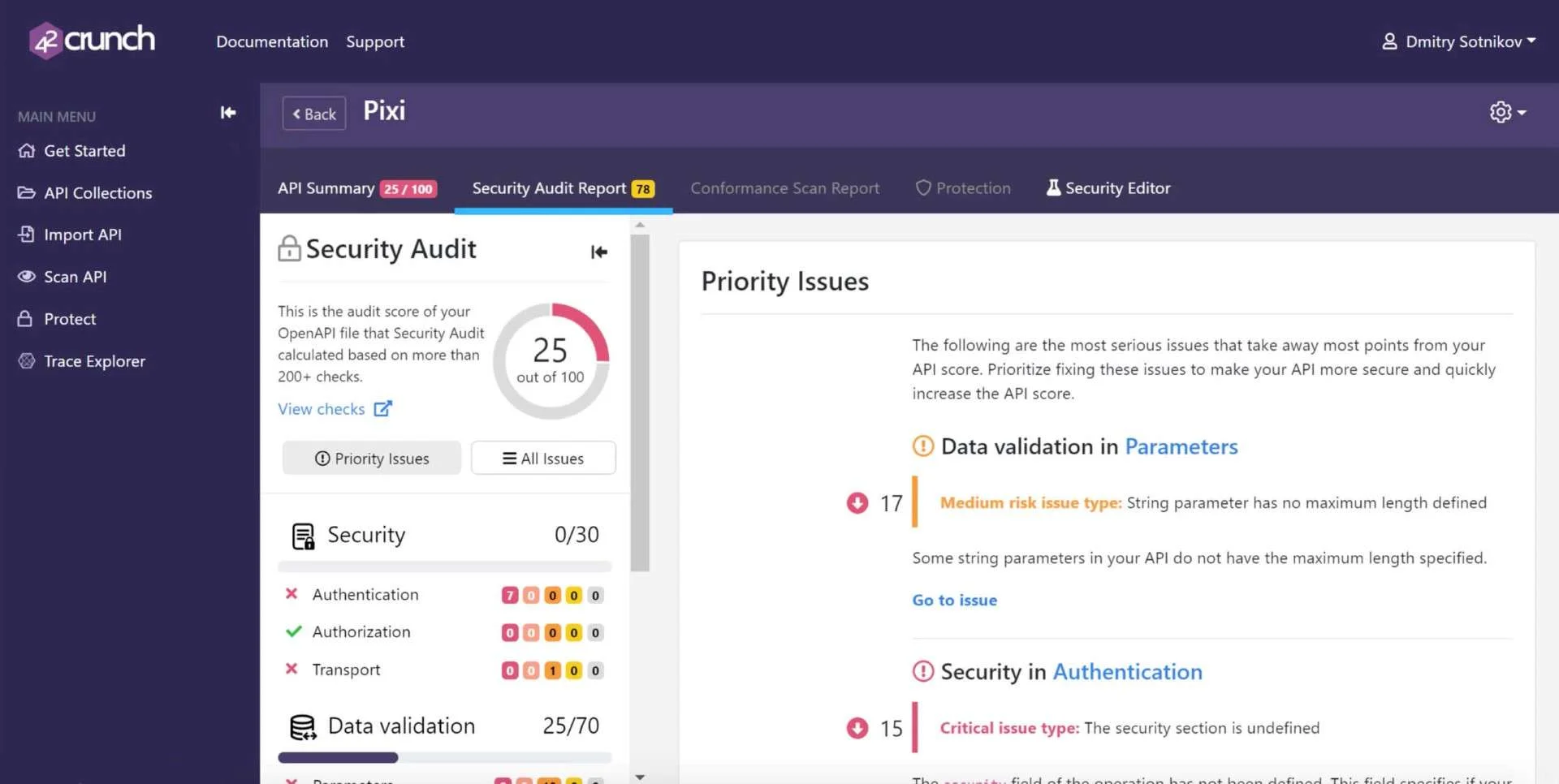
Conformance Scan then tests the running API against the same spec, verifying that the implementation actually validates inputs, rejects malformed requests, and returns errors as documented. This catches implementation gaps where the spec looks correct but the code doesn’t enforce it.
The GitHub App and VS Code extension bring API security analysis directly into the developer workflow — 42Crunch flags spec issues as developers write OpenAPI files before the API is even built.
Best fit: Teams practicing API-first design with OpenAPI specifications who want security feedback from spec design through runtime validation.
3. StackHawk
StackHawk
is a commercial API DAST tool designed from the start for CI/CD integration. Configuration is a YAML file (stackhawk.yml) committed to the repository, making scans reproducible and diff-reviewable. StackHawk is built on top of OWASP ZAP
with significant API-specific enhancements and a managed SaaS layer.
What StackHawk does well: CI/CD-native design is StackHawk’s primary selling point. The hawkscan Docker container runs in any CI/CD platform — GitHub Actions, GitLab CI, CircleCI, Jenkins, Azure DevOps — and produces findings in the pipeline output and a StackHawk SaaS dashboard. Authentication support covers API keys, bearer tokens, OAuth 2.0 (including device flow), and custom auth scripts.
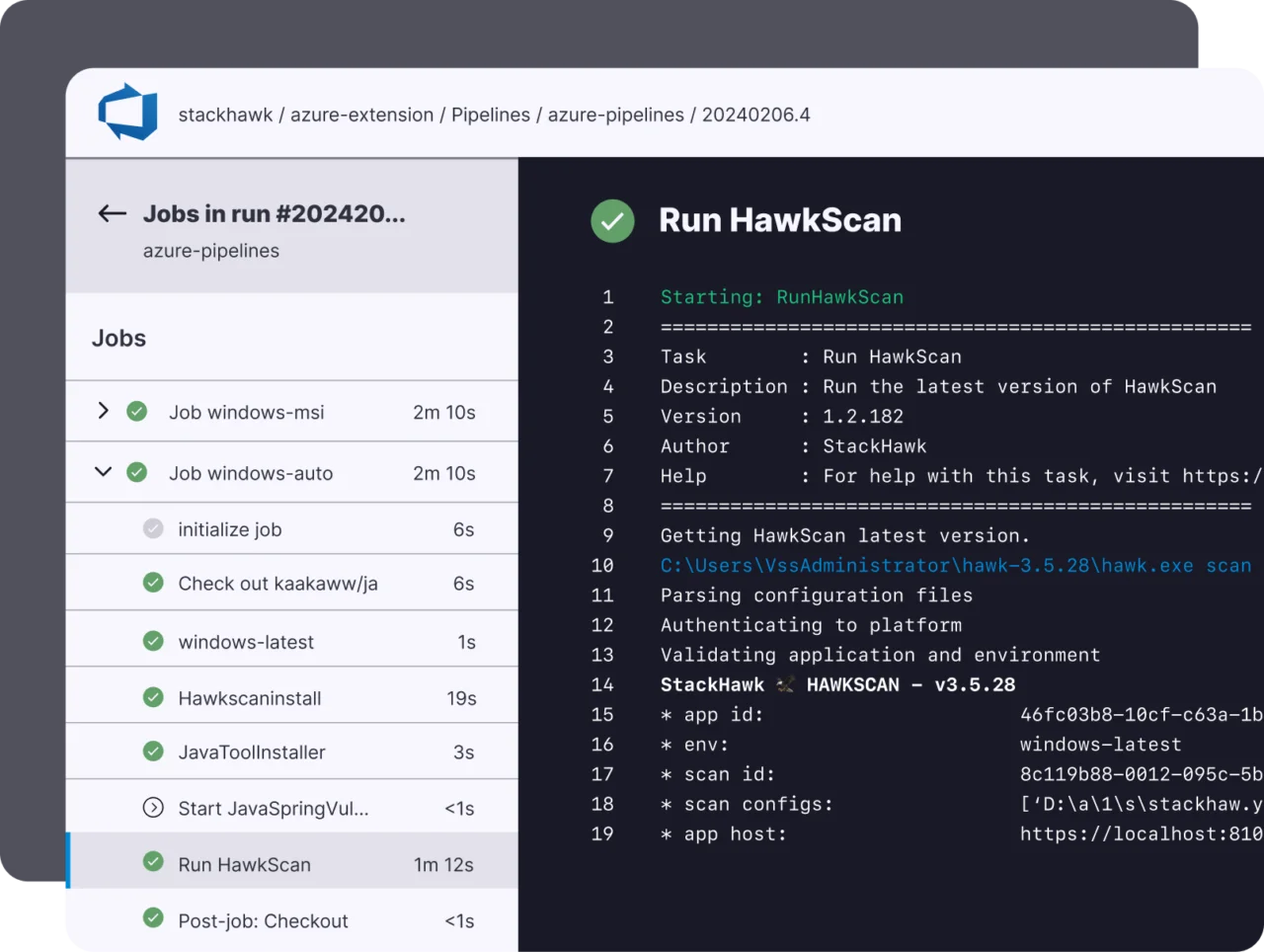
StackHawk consumes OpenAPI 3.0, Swagger 2.0, GraphQL schemas, and Postman collections. Dynamic discovery mode crawls APIs not covered by a spec. A free tier covers one application with unlimited scans.
Where StackHawk falls short: Findings depth is tied to its ZAP heritage — it covers standard injection vulnerabilities and OWASP Top 10 well, but BOLA/IDOR detection (which requires cross-user authorization testing) requires additional configuration. Its GraphQL coverage is improving but trails Escape.
Best fit: Development teams that want DAST integrated into GitHub Actions or GitLab CI with minimal configuration and a developer-friendly findings interface.
4. Salt Security
Salt Security operates differently from the other tools in this list — it is a production API security platform rather than a pre-production DAST tool. Salt deploys as an inline or out-of-band observer of production API traffic, learns normal API behavior over weeks, and detects anomalies that indicate attack attempts or abuse.
What Salt Security does well: Runtime behavior learning enables detection of attacks that pre-production testing cannot anticipate. BOLA attacks, credential stuffing on API endpoints, account takeover patterns, and shadow API discovery (endpoints that aren’t in your spec because they were never documented) are Salt Security’s core detections. The platform provides API inventory — automatically cataloging every API endpoint receiving traffic, including undocumented ones.
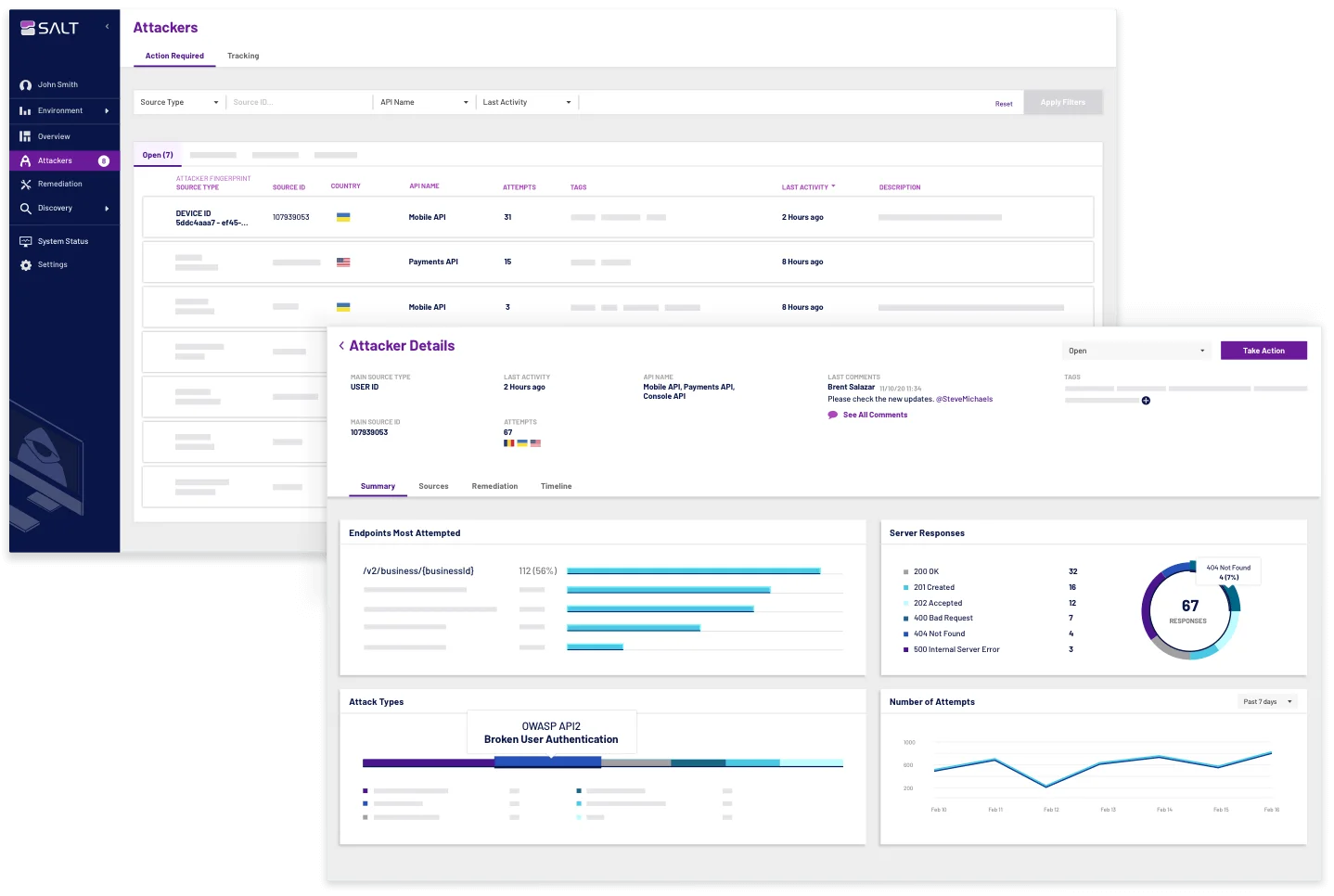
Where Salt Security falls short: Salt is not a pre-production testing tool. It requires production traffic to be effective — there is a learning period before it provides useful detections. For teams that want to catch vulnerabilities before production, Salt must be paired with a pre-production API DAST tool like Escape or StackHawk.
Best fit: Organizations that need API security monitoring in production, API inventory for compliance, or runtime detection of business logic abuse patterns that pre-production testing cannot cover.
5. Wallarm
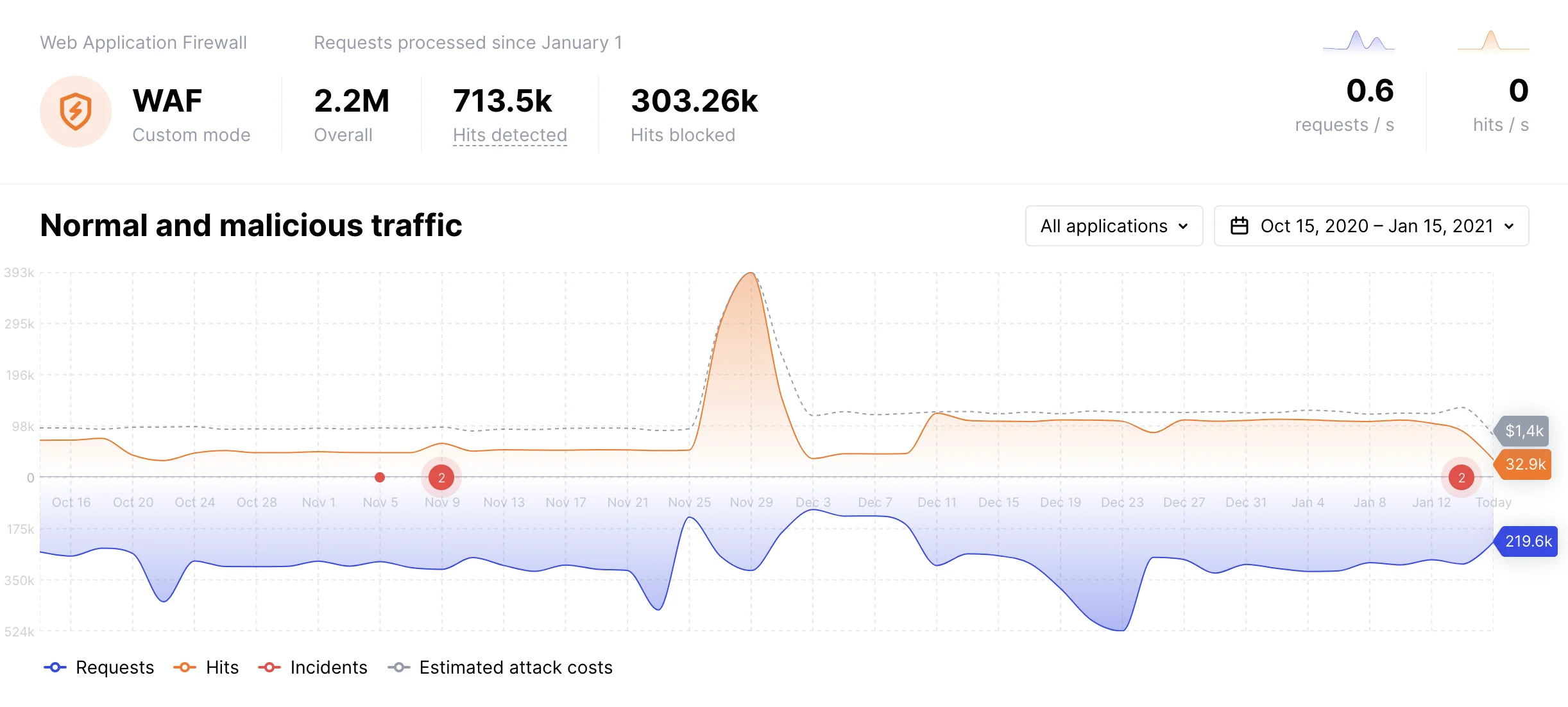
Wallarm is an API security platform covering both pre-production testing and production protection. Its API attack surface management module discovers APIs across your organization; its testing module performs security scanning; and its production WAF/WAAP protects APIs from attacks in real time.
What Wallarm does well: API discovery and inventory is a strong capability — Wallarm can crawl traffic and identify API endpoints, including shadow and zombie APIs, that are not in official specs. The production protection module provides L7 attack detection and blocking including SQL injection, command injection, SSRF, and API-specific attacks. For teams that want pre-production testing and production protection from a single vendor, Wallarm covers both layers.
Where Wallarm falls short: The breadth of the platform makes it more complex to configure than a focused tool like Escape or StackHawk. Teams that only need pre-production DAST may find the full platform overhead unjustified.
Best fit: Organizations that need both API security testing and production API protection from a single vendor, especially those dealing with unknown API inventory from microservices or legacy systems.
6. Akto
Akto is an open-source API security testing platform. It generates test cases from OpenAPI specs or by observing API traffic through a proxy/eBPF sensor. Akto covers the OWASP API Security Top 10 with test modules for BOLA, broken authentication, excessive data exposure, and injection attacks.
What Akto does well: Open-source with a self-hosted option makes Akto the strongest choice for teams with compliance requirements or air-gapped environments that cannot use SaaS tools. The traffic-based test generation automatically creates test cases from observed API calls without requiring a pre-written spec. Akto integrates with CI/CD pipelines for pre-production testing and provides a centralized dashboard for finding management.
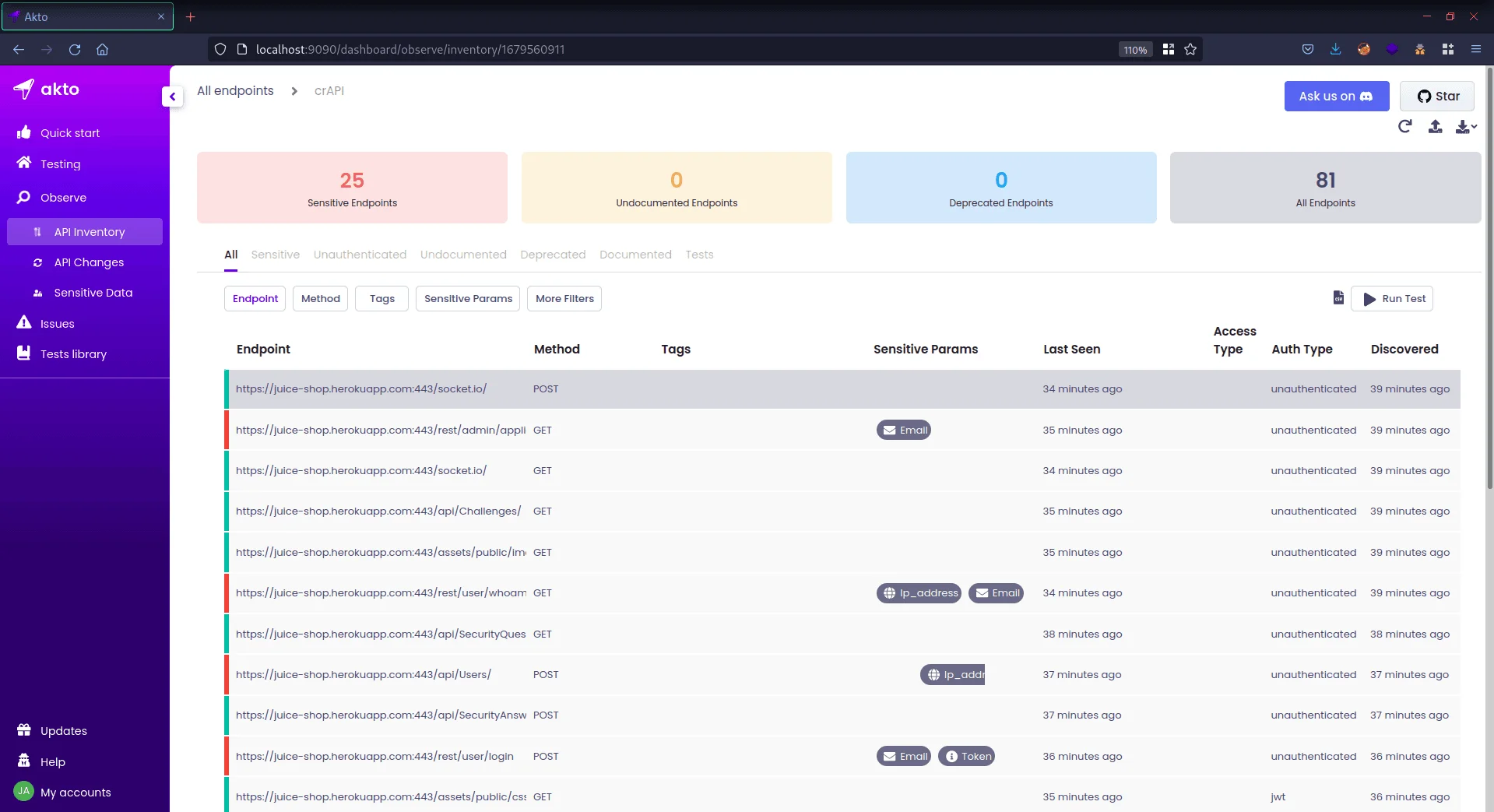
Where Akto falls short: As a younger open-source project, Akto’s detection depth and community ruleset are still maturing compared to commercial alternatives. GraphQL support is limited compared to Escape.
Best fit: Teams that need open-source API DAST with a self-hosted deployment option, or those wanting to generate API tests from observed traffic without writing OpenAPI specs.
7. APIsec
APIsec (formerly Fuzzbuzz) is a commercial API security testing platform focused on automated test generation from OpenAPI specifications. It generates thousands of test cases per API, covering positive testing (valid inputs), negative testing (malformed inputs, boundary conditions), and security testing (injection, authorization bypass, mass assignment).
What APIsec does well: Test coverage volume — APIsec generates thousands of test cases covering every endpoint, method, and parameter in the spec with positive and negative variants. This catches missing input validation, inconsistent error handling, and edge cases that manually written test cases miss. Findings route to Jira, Slack, and ServiceNow for remediation tracking.
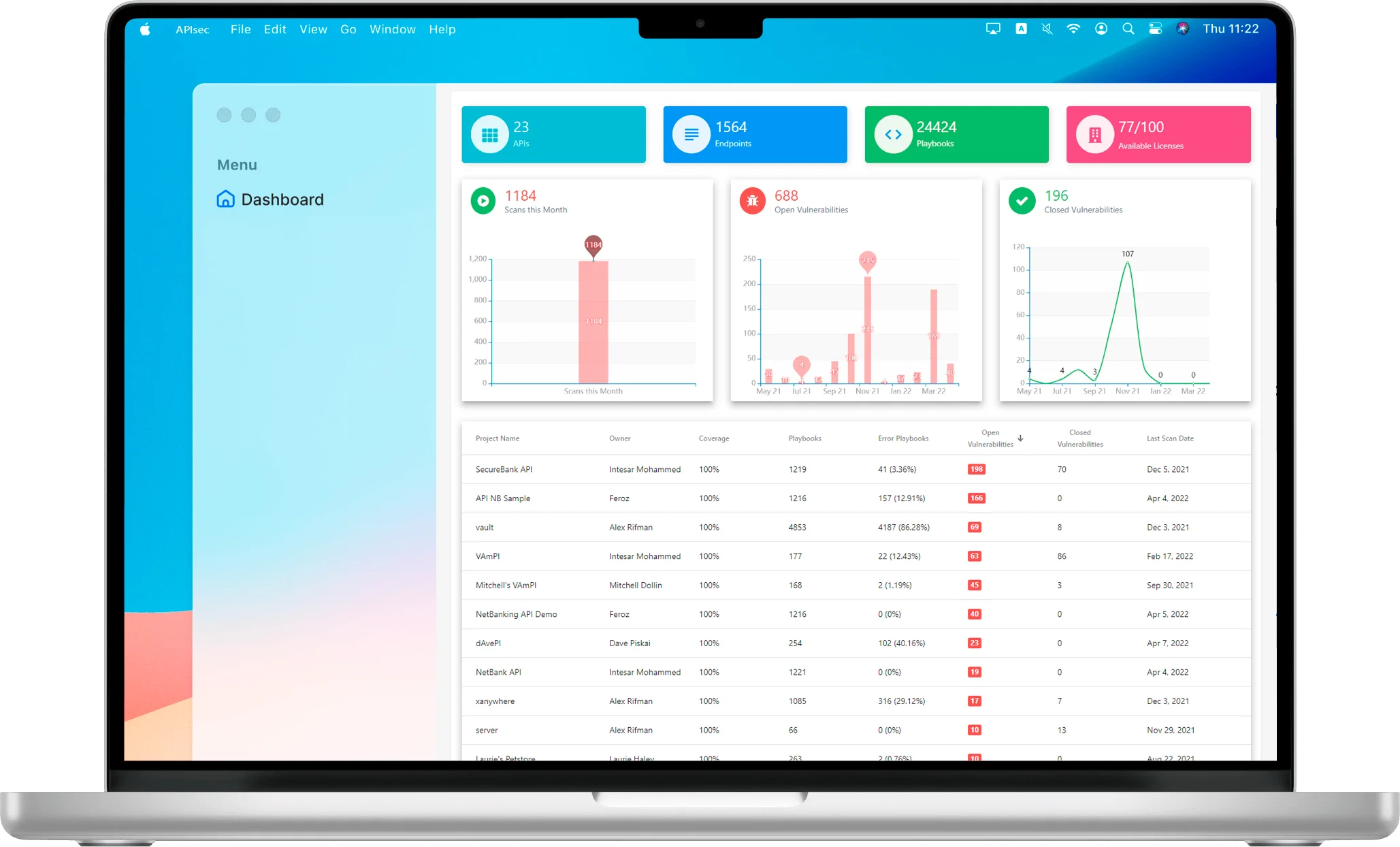
Best fit: Teams with large API surfaces that want automated, comprehensive test coverage from their OpenAPI specifications rather than configuring test cases manually.
8. Traceable AI
Traceable AI is an API security platform that combines API observability (using distributed tracing and eBPF) with threat detection and security testing. Its approach is rooted in tracing every API request with full context — user identity, session, request chain, and data accessed.
What Traceable does well: The distributed tracing foundation gives Traceable deep visibility into API call chains — it knows not just that an API endpoint was called but which services were involved, what data was accessed, and whether the access pattern deviates from the user’s baseline behavior. This enables detection of BOLA attacks, account takeover, and API abuse patterns that appear legitimate in isolation.
Traceable also provides an API catalog built from observed traffic, automated API testing seeded by traced request patterns, and runtime threat detection with WAF capabilities.
Best fit: Organizations with complex microservices architectures where distributed tracing is already in use (Jaeger, Zipkin, OpenTelemetry) and who want security analysis built on that telemetry.
Comparison table
| Tool | Primary Use | OpenAPI Support | GraphQL | CI/CD Native | Deployment |
|---|---|---|---|---|---|
| Escape | Pre-production DAST | Yes | Excellent | Yes | SaaS |
| 42Crunch | Spec audit + conformance | Yes (spec-first) | No | Yes | SaaS |
| StackHawk | CI/CD DAST | Yes | Good | Yes (by design) | SaaS |
| Salt Security | Production monitoring | Auto-discovery | Yes | No | SaaS / on-prem |
| Wallarm | Pre-prod + production | Yes | Yes | Yes | SaaS / on-prem |
| Akto | Pre-production DAST | Yes + traffic | Limited | Yes | Self-hosted / SaaS |
| APIsec | Test generation | Yes | No | Yes | SaaS |
| Traceable AI | Production observability | Auto-discovery | Yes | No | SaaS / on-prem |
How to choose
The right tool depends on where in the lifecycle you need coverage.
For pre-production CI/CD testing: Choose StackHawk if you primarily use REST APIs and want the lowest-friction CI/CD integration. Choose Escape if you use GraphQL or need deeper BOLA/IDOR testing. Choose 42Crunch if you practice API-first design and want spec-level security analysis before implementation.
For open-source requirements: Akto is the only production-grade open-source API DAST tool with self-hosted deployment. For teams that cannot use SaaS tools due to data residency or compliance requirements, Akto is the primary option.
For production monitoring: Salt Security and Traceable AI are runtime platforms that require production traffic to be effective. Both provide API inventory from real traffic — valuable for organizations with undocumented or legacy APIs. Wallarm covers both pre-production testing and production protection if you need one vendor for both layers.
API DAST in CI/CD
Integrating API DAST into CI/CD requires three components: an OpenAPI specification (or traffic-derived test cases), authentication configuration, and a baseline for pass/fail decisions.
Step 1: Maintain an OpenAPI spec. Without a spec, API DAST tools have limited coverage. If your API generates a spec automatically (FastAPI, Spring Boot with Springdoc, Django REST Framework), capture it as part of the CI build and pass it to the scanner.
Step 2: Configure authentication. Most API DAST tools support bearer token injection, API key headers, and OAuth 2.0 client credentials flows. Store credentials in CI/CD secrets and inject them via environment variables — never commit credentials to the scanner configuration file.
Step 3: Set a gate threshold. API DAST tools can produce false positives. Start with a gate that fails the build only on Critical findings, review those manually for the first few sprints, then tighten to block on High findings once you have confidence in the tool’s accuracy for your API.
StackHawk , Escape , and 42Crunch all provide ready-made GitHub Actions and GitLab CI integration examples in their documentation. For broader API security tooling beyond DAST, see the API security tools overview and the API security testing guide . For teams comparing API tools, Escape vs StackHawk covers the two leading CI/CD-native options in depth.






