Cylake is an AI-native cybersecurity platform that delivers unified threat detection and response exclusively through on-premises and private cloud deployment, ensuring all security data stays within the customer’s perimeter.
Product status (April 2026)
Cylake launched in March 2026 and is currently working with design partners only. General product availability is anticipated in early 2027. You cannot deploy Cylake today — join the design-partner program at cylake.com.
It is an AI security platform built for government agencies, critical infrastructure operators, and regulated enterprises where data sovereignty is a hard requirement, not a preference.
Cylake launched in March 2026, founded by three cybersecurity veterans: Nir Zuk , who founded Palo Alto Networks in 2005 and served as its CTO for over two decades; Wilson Xu, who spent more than a decade building Palo Alto Networks’ engineering organization; and Ehud (Udi) Shamir, a co-founder of SentinelOne .
The company raised $45 million in seed funding led by Greylock Partners , with partner Asheem Chandna (who led Greylock’s Palo Alto Networks investment) leading the deal.
This ranks among the largest seed rounds in cybersecurity history, reflecting investor confidence in the founding team and the unaddressed market gap for sovereign AI-native security.
What is Cylake?
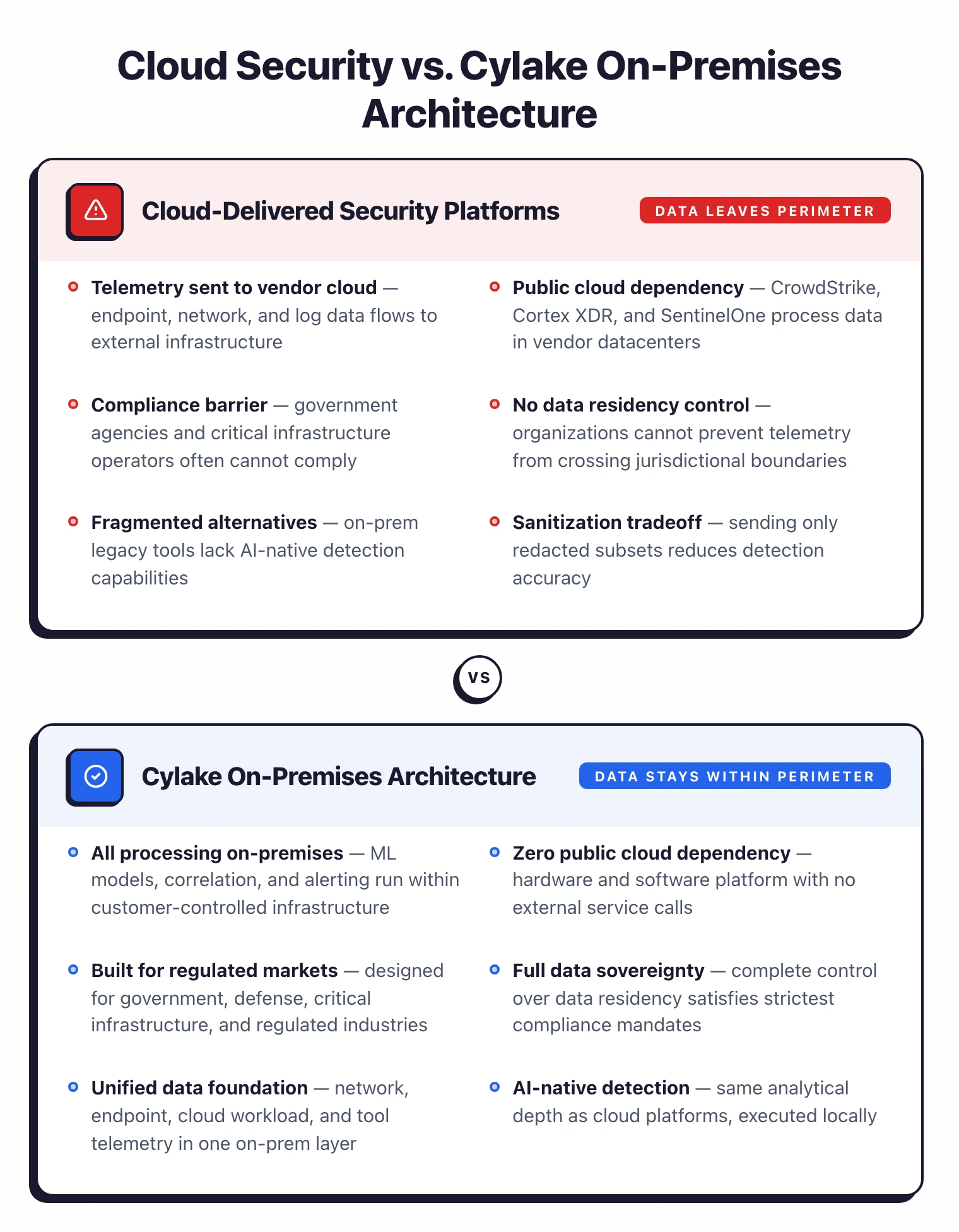
There is a real tension in enterprise cybersecurity: the best security platforms require sending data to vendor cloud infrastructure.
But government agencies, critical infrastructure operators, and heavily regulated enterprises often cannot send security telemetry outside their perimeter.
Cylake combines hardware and software into a single system that collects operational and security data from network infrastructure, endpoints, cloud workloads, and existing security tools.
All of it feeds into one data foundation processed entirely within the customer’s environment.
ML models and automated workflows run locally, analyzing patterns, correlating events across sources, and generating alerts without any data leaving the organization.
Cylake calls this “agentic protection”: AI-driven security analysis that operates autonomously inside the customer’s own infrastructure.
Why Cylake matters: Nir Zuk’s new company
For anyone following enterprise cybersecurity, Cylake is notable less for the product (which isn’t generally available yet) and more for who is building it. Nir Zuk founded Palo Alto Networks in 2005 and served as its CTO for more than two decades, during which he defined what most people think of today as “next-gen firewall” and later XDR. His public framing of Cylake is that every major security platform he and his peers have built in the last fifteen years assumes customer data can go to vendor cloud infrastructure. A structurally important segment of the market (government, defense, critical infrastructure, heavily regulated finance and healthcare) simply cannot make that assumption.
Wilson Xu spent over a decade leading engineering at Palo Alto Networks and was one of the senior architects behind Cortex XDR. Ehud “Udi” Shamir co-founded SentinelOne, whose 2021 IPO made endpoint-AI a default expectation in the EDR market.
Three founders with that combined track record raising $45M from Greylock in a seed round, with Asheem Chandna (who also led Greylock’s investment in Palo Alto Networks) leading the deal, is the single biggest signal around Cylake right now. It is a reasonable bet by people who previously built two of the most successful companies in this market, aimed at the segment those companies cannot currently serve.
Cylake Key Features
| Feature | Details |
|---|---|
| Deployment Model | On-premises and private cloud exclusively |
| Architecture | Combined hardware and software platform |
| Data Collection | Network, endpoint, cloud workload, and security tool telemetry |
| Analysis | AI-native ML models running locally |
| Correlation | Cross-source event correlation across entire technical stack |
| Automation | Agentic protection workflows for autonomous detection and response |
| Investigation | Automated investigation workflows without external data export |
| Data Sovereignty | All processing within customer-controlled environments |
| Integration | Connects to existing security tools and infrastructure |
| Target Market | Government, critical infrastructure, regulated enterprises |
| Funding | $45M seed (Greylock Partners, March 2026) |
| Product Status | Design partner phase; product availability anticipated early 2027 |
The data sovereignty gap
Most modern cybersecurity platforms, including those built by the Cylake founders’ previous companies, process data in vendor-operated cloud environments. This works for many organizations, but it creates a hard constraint for those subject to strict data residency requirements.
Government agencies, critical infrastructure operators (energy, water, transportation), and enterprises in highly regulated industries (defense, certain financial services, healthcare) often cannot use cloud-delivered security products at all.
Their current options are either fragmented on-premises tools or selectively segmenting data to send only sanitized subsets to cloud platforms.
Cylake is trying to close this gap by bringing cloud-grade AI security capabilities inside the customer’s perimeter.
How Cylake compares to cloud-delivered security platforms
| Cylake | CrowdStrike Falcon | Palo Alto Cortex XSIAM | SentinelOne Singularity | |
|---|---|---|---|---|
| Data plane | On-prem / private cloud only | Vendor cloud | Vendor cloud | Vendor cloud |
| AI/ML processing | Local only | Cloud | Cloud | Cloud |
| Founder lineage | Palo Alto Networks + SentinelOne | Own | Own | Own |
| Data residency | Customer perimeter, always | Vendor-controlled regions | Vendor-controlled regions | Vendor-controlled regions |
| Regulated-industry fit | Built for sovereignty-first | Possible with caveats | Possible with caveats | Possible with caveats |
| Deployment | Combined hardware + software | Cloud-managed agents | Cloud-managed agents | Cloud-managed agents |
| Status (Apr 2026) | Design-partner phase, GA early 2027 | Generally available | Generally available | Generally available |
The short version: cloud-delivered XDR / XSIAM platforms are more mature, have bigger detection libraries, and ship today. Cylake’s bet is that a non-trivial segment of enterprise buyers (government, defense, critical infrastructure, some financial services) cannot use those platforms at all because data cannot leave the perimeter. For those buyers, Cylake is not competing on features against CrowdStrike; it is competing against a combination of fragmented on-prem tools and “no modern AI security at all.”
Unified data approach
Rather than deploying separate tools for network detection, endpoint protection, cloud workload security, and log analysis, Cylake consolidates all security-relevant data into a single foundation.
The platform then applies AI-native analytics across the full dataset, finding patterns and correlations that siloed tools miss.
This mirrors the data-driven approach that cloud security platforms have proven effective (comprehensive visibility leads to better detection) but executes it entirely within the customer’s infrastructure.
Getting Started with Cylake
When to use Cylake
Best for: Government agencies, defense contractors, critical infrastructure operators, and regulated enterprises that need AI-driven cybersecurity but cannot send security telemetry to vendor cloud infrastructure.
Cylake targets a specific market: organizations that need modern, AI-driven cybersecurity but cannot use public cloud infrastructure for security operations.
If data sovereignty is a hard requirement (not a preference, but a regulatory or operational mandate), Cylake is one of the few platforms built from scratch for that constraint.
The founding team’s track record at Palo Alto Networks and SentinelOne gives credibility to the technical vision, and the $45M seed round from Greylock provides runway for platform development.
However, Cylake launched in March 2026 and is currently working with design partners, with product availability anticipated in early 2027.
For a broader overview of AI security solutions, see the AI security tools guide. For cloud-delivered AI security with runtime protection, consider WitnessAI (single-tenant option) or NeuralTrust (split-plane architecture with on-prem data plane).
For AI-specific threat detection in cloud environments, see HiddenLayer or Protect AI Guardian . For open-source AI security testing, look at Garak or Promptfoo .