Corellium is a virtual hardware platform that creates ARM-native digital twins of iOS and Android devices for mobile security testing, vulnerability research, and app development. It is the only platform in the world that offers virtualized iPhones with instant jailbreak access — without relying on any iOS exploits.
Founded in 2017 by Amanda Gorton (CEO) and Chris Wade (CTO), Corellium runs on ARM hardware through its proprietary CHARM (Corellium Hypervisor for Arm) type-1 hypervisor. Unlike Android emulators that translate ARM instructions to x86, Corellium uses ARM-on-ARM virtualization, which means virtual devices behave identically to their physical counterparts at the firmware and kernel level.
Cellebrite acquired Corellium in December 2025 for $170 million, with CFIUS (Committee on Foreign Investment in the United States) approving the deal under a national security agreement. Corellium continues to operate its platform and product lines.
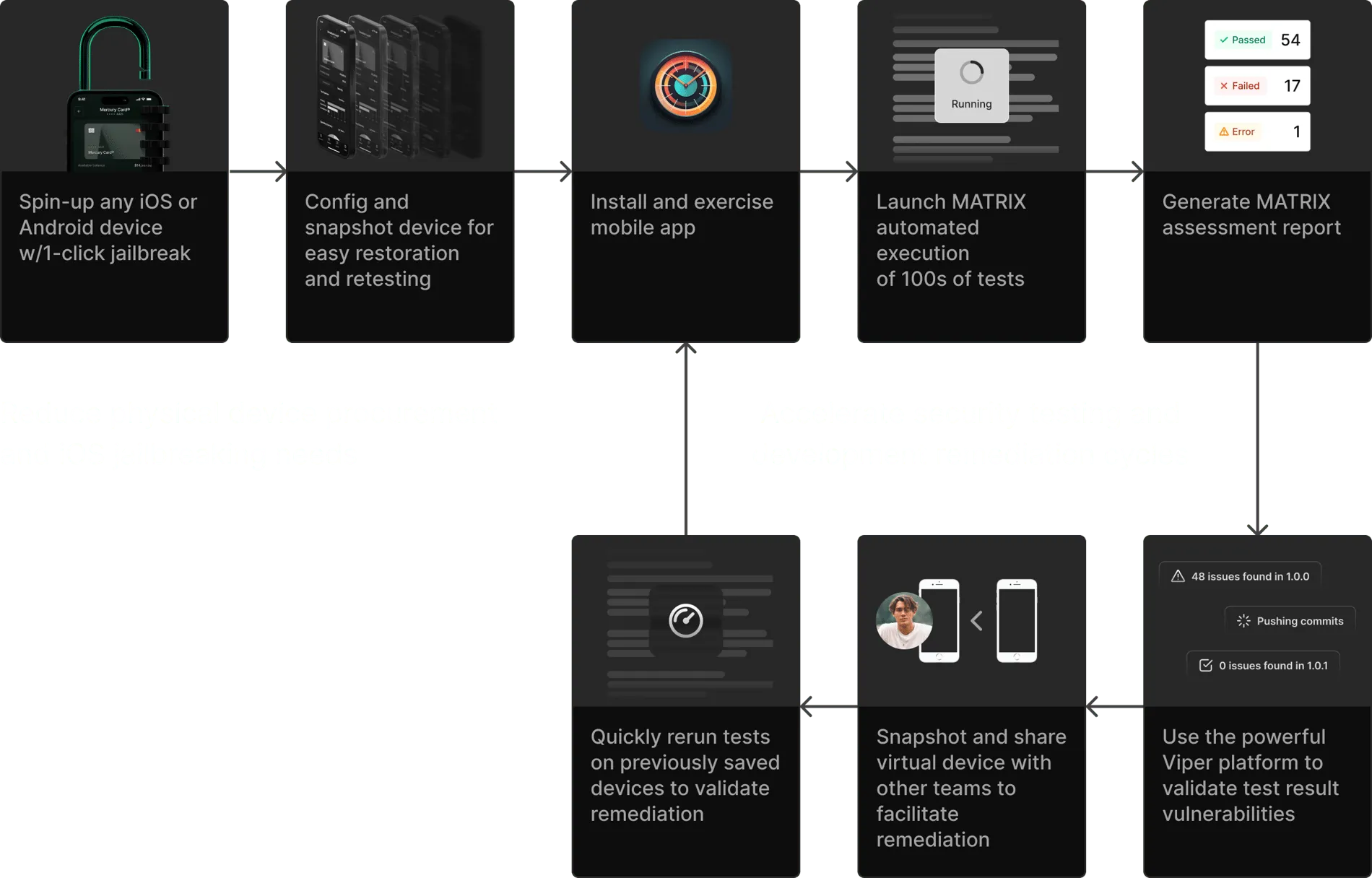
The MATRIX automated testing engine runs hundreds of OWASP-aligned security checks on mobile apps, covering 7 test categories including authentication, cryptography, and data storage.
Key Features
| Feature | Details |
|---|---|
| Virtual iOS Devices | Jailbroken or non-jailbroken iPhones across all iOS versions, typically supported within days of release including betas |
| Virtual Android Devices | Ranchu-based Android models with root access and permissive SELinux enforcement |
| CHARM Hypervisor | Type-1 bare-metal hypervisor purpose-built for ARM device virtualization |
| MATRIX Testing | Automated security testing engine aligned with OWASP MASTG covering 7 test categories |
| Frida Integration | Pre-installed Frida daemon in all jailbroken iOS and rooted Android VMs |
| HyperTrace | Kernel execution path mapping for coverage-guided fuzzing and diagnostics |
| CoreTrace | System call tracing for runtime behavior analysis |
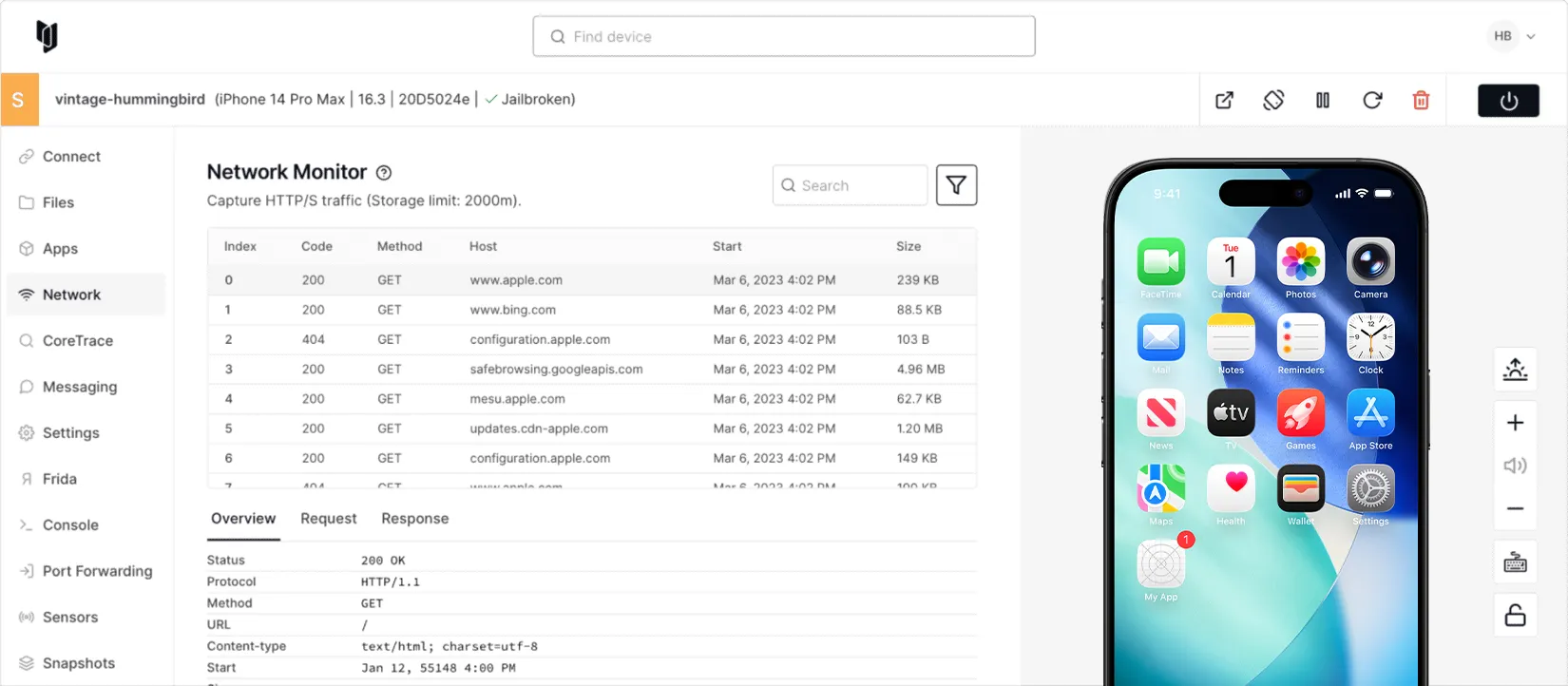
| Network Monitor | Traffic inspection by process/port/PID with transparent SSL pinning bypass |
| Snapshots | Save, restore, and clone entire device states for reproducible testing |
| REST API & CLI | Full automation support for CI/CD integration and scripted workflows |

How Corellium Works
Corellium’s architecture has four layers. At the base, ARM-native server hardware (AWS Graviton in the cloud, or custom Arm appliances on-premises) provides compute.
On top of that, the CHARM hypervisor manages multiple virtual device instances on bare metal. Each virtual device runs actual device firmware (iOS, Android, or custom IoT images) as a digital twin.
The tooling layer then provides browser-based UI, CLI, and API access with built-in security research instruments.
Compared to Android emulators like the ones in Android Studio — which translate ARM instructions to x86 and introduce behavioral differences — Corellium’s ARM-on-ARM execution produces higher fidelity results. Timing-sensitive bugs, hardware-specific behaviors, and low-level vulnerabilities manifest the same way they would on a physical device.
Product Lines
Corellium offers four distinct products targeting different user segments:
- Corellium Viper — Enterprise solution for mobile app security testing and DevSecOps integration. Includes MATRIX automated testing, team collaboration features, and CI/CD pipeline integration.
- Corellium Falcon — Government and defense solution for deep vulnerability research, mobile forensics, and threat analysis. Supports air-gapped deployments for classified environments.
- Corellium Atlas — Automotive solution for software-defined vehicle development. Provides ARM-native virtualization for ECU software testing without physical silicon.
- Corellium Solo — Individual researcher and student offering with pay-per-use pricing for mobile security exploration and learning.
Use Cases
Mobile App Penetration Testing
Corellium gives pentesters an environment where they can test mobile apps with full device access. Unlike testing on physical devices, there is no need to find and maintain jailbreaks for each iOS version.
Testers get instant root access, can monitor all network traffic with automatic certificate pinning bypass, trace system calls with CoreTrace, and hook into running processes through the built-in Frida console.
MATRIX can automate the routine portion of a pentest, handling up to 75% of repetitive testing tasks according to Corellium. This lets pentesters focus on the parts of the assessment that require human judgment and creative exploitation.
For the broader workflow that wraps Corellium and Frida together, see my mobile app pentesting guide and the OWASP MASTG dynamic-analysis tests it walks through.
Vulnerability Research
Security researchers use Corellium to discover zero-day vulnerabilities in iOS and Android. HyperTrace maps kernel execution paths, which can feed into coverage-guided fuzzers.
Custom kernels and device trees can be uploaded for targeted research. Device snapshots allow researchers to save and share exact device states for reproducing vulnerabilities.
Malware Analysis
Threat intelligence teams use Corellium’s virtual devices to detonate and analyze mobile malware in a contained environment. System call tracing, network monitoring, and filesystem inspection reveal malware behavior without risking physical device compromise.
The snapshot feature allows analysts to restore a clean state instantly after each analysis run.
Government and Defense
US Department of Defense agencies and intelligence organizations use Corellium for defensive cybersecurity research. The CFIUS national security agreement with Cellebrite underscores the platform’s role in government security operations.
On-premises appliances can run air-gapped for use in SCIFs (Sensitive Compartmented Information Facilities) and other classified environments.
OWASP MASTG Dynamic Analysis
Corellium is one of the canonical platforms for executing OWASP Mobile Application Security Testing Guide (MASTG) dynamic-analysis controls — the MASTG-TEST-0034 / 0050 series and the broader resilience tests that need a rooted or jailbroken device. Because every Corellium VM ships with instant root access, Frida pre-installed, and snapshot/restore baked in, MASTG runbooks that take days on a physical-device lab finish in hours.
Strengths & Limitations
Strengths:
- Only platform offering virtual iOS devices with true ARM-native execution
- Instant jailbreak across all iOS versions without depending on exploit chains
- Deep kernel-level introspection not available on any other cloud platform
- Built-in Frida integration removes setup friction for dynamic analysis
- MATRIX automates OWASP-aligned testing and generates assessment reports
- Available as cloud, on-premises, or dedicated private server deployments
- Legally validated through the Apple fair use ruling
Limitations:
- Commercial platform with enterprise-level pricing; entry point starts at $9,995 for business plans
- Solo tier targets individual users with pay-per-device-hour pricing (free trial limited to students)
- No free tier for professional researchers outside academia
- Virtual devices, while high-fidelity, cannot perfectly replicate all physical hardware behaviors (Bluetooth, NFC, cellular baseband)
- Cellebrite acquisition raises questions for some security researchers about the platform’s future direction, given Cellebrite’s law enforcement focus
In 2019, Apple sued Corellium for copyright infringement over its iOS virtualization technology. In December 2020, a US federal court ruled in Corellium’s favor, finding that virtualizing iOS for security research constitutes fair use under copyright law.
Apple appealed, and the Eleventh Circuit upheld the fair use ruling in May 2023. The parties reached a final confidential settlement in December 2023.
This case established an important legal precedent for security research tooling.
Getting Started
Corellium Pricing
Corellium publishes a tiered pricing model on corellium.com and in its support docs. Solo is pay-as-you-go at $3 per device-hour with no pre-paid minimum, aimed at individual researchers; Viper Essentials/Advanced and Falcon are enterprise plans built around a monthly block of device-hours (1,250+) plus burst rates after the block is consumed.
Entry pricing for the enterprise tier began at $9,995 USD as of November 2025. On-premises appliances and dedicated private servers are quoted separately by the sales team — particularly for air-gapped deployments in classified environments. Corellium also offers a 30-day free trial with up to 100 core hours so prospective buyers can evaluate the platform before committing to a plan.
How Corellium Compares
Corellium sits in a different category from most mobile security tools. Unlike application scanners such as NowSecure or Oversecured that analyze apps, Corellium provides the virtual device infrastructure layer that makes mobile security testing possible at scale. This distinction matters most for iOS, where physical device jailbreaking has become increasingly difficult and unreliable.
For teams doing mobile app penetration testing, Corellium replaces physical device labs entirely. Compared to maintaining a fleet of physical test devices, Corellium offers instant provisioning across iOS versions, consistent jailbreak access, and snapshot-based state management.
For vulnerability researchers, it provides kernel-level access that physical devices cannot offer without fragile jailbreak chains. For organizations with compliance requirements, MATRIX provides automated OWASP-aligned evidence generation.
Open-source alternatives like MobSF cover static and basic dynamic analysis for free, but they cannot virtualize iOS devices or provide kernel-level introspection.
Frida is the standard for dynamic instrumentation and comes pre-installed on Corellium, but Frida alone does not provide virtual device infrastructure. Drozer focuses on Android-specific attack surface enumeration and does not address iOS testing.
Corellium vs Genymotion: Genymotion is an x86 Android emulator targeting developer testing. It runs on Intel/AMD hosts and translates ARM instructions, which is fast for QA but introduces behavioral drift for security work. Corellium runs ARM-on-ARM virtualization, so app and OS code execute on native ARM silicon — closer to a physical device for any test that touches the kernel, hardware features, or low-level cryptography.
Corellium vs Android Studio Emulator: Android Studio’s emulator is built for app development, not security research. It does not support virtualized iOS, ships without root by default, and lacks kernel debugging or system-call tracing. Corellium covers both platforms with root and instrumentation enabled out of the box.
Corellium vs a physical jailbroken-device fleet: Maintaining a lab of jailbroken iPhones means hunting exploits for every iOS version, refreshing devices when jailbreaks die, and limited state-restore. Corellium swaps that operational tax for cloud provisioning, instant snapshots, and consistent OS coverage — which is the lever most security teams cite when they switch.
For a broader overview of mobile security tools and how they compare, see the mobile security tools category page.