Contrast Security is an application security platform that uses runtime instrumentation to detect and block vulnerabilities. The platform combines IAST , RASP , SAST , and SCA capabilities under a unified developer-focused interface.
Unlike traditional scanners that analyze code statically or test from the outside, Contrast instruments applications with agents that observe code execution in real time.
Platform components
Contrast Security consists of four main products that share a common instrumentation agent and dashboard:
Contrast Assess — Interactive Application Security Testing (IAST) that finds vulnerabilities in running code during development and QA testing.
Contrast Protect — Runtime Application Self-Protection (RASP) that blocks attacks in production without code changes.
Contrast Scan — Static Application Security Testing (SAST) built for CI/CD pipelines with fast scan times and low false positive rates.
Contrast SCA — Software Composition Analysis that identifies vulnerable open-source libraries and prioritizes fixes based on runtime usage.
How Contrast Security works
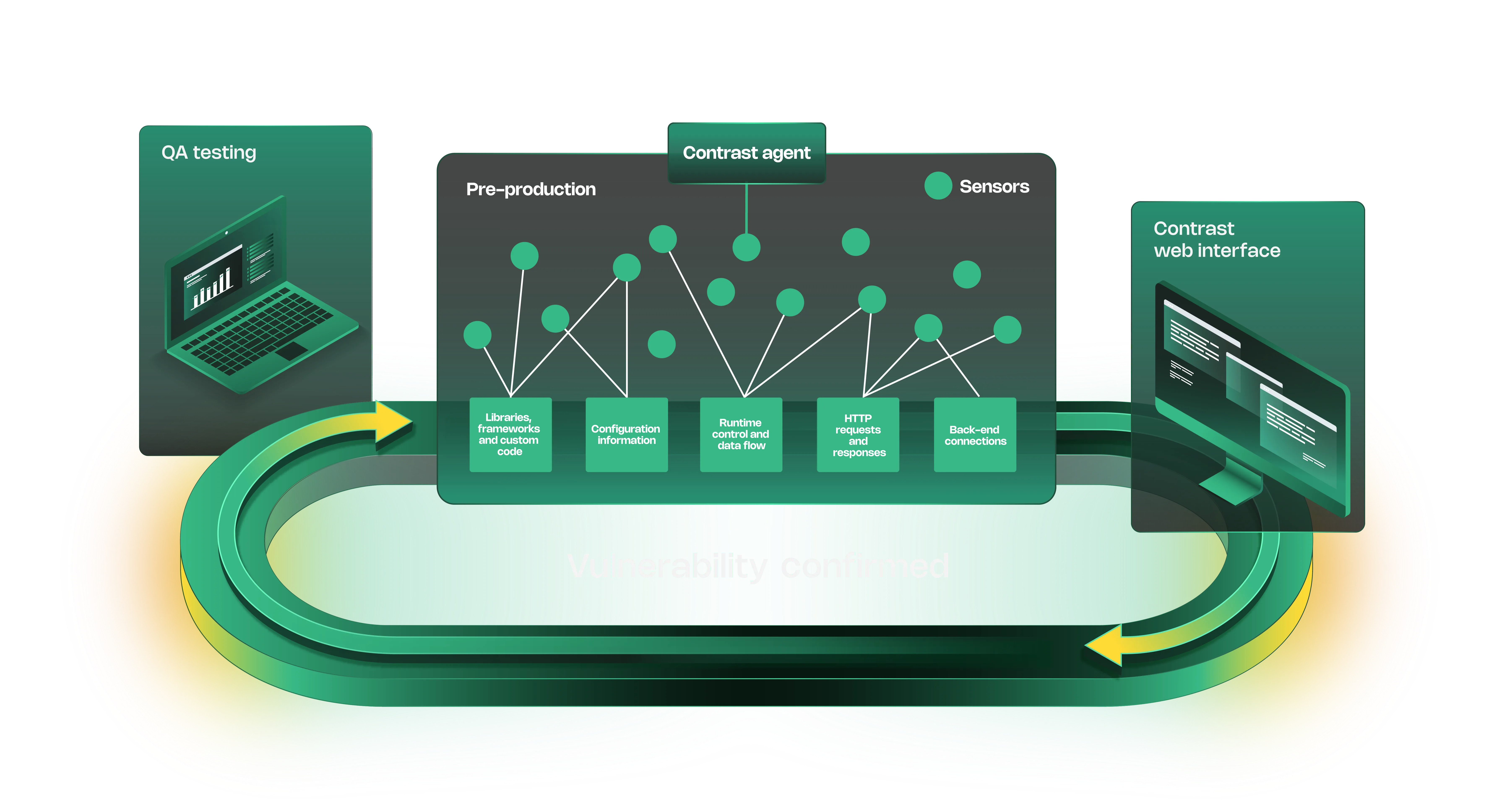
Contrast Security instruments applications with language-specific agents (Java, .NET, Node.js, Python, Ruby, Go). The agent monitors code execution during normal application usage, automated tests, or production traffic.
When vulnerable code paths execute — like unsanitized user input reaching a SQL query — the agent reports the vulnerability with full context: stack trace, data flow, affected endpoints, and fix guidance.
This runtime approach identifies vulnerabilities that exist in actual code paths rather than every possible vulnerability in the codebase. Unused functions and dead code don’t generate findings.
Contrast Assess (IAST)
Contrast Assess finds vulnerabilities during development and QA testing. Install the agent, run automated tests or manually use the application, and Assess reports security issues it observes.
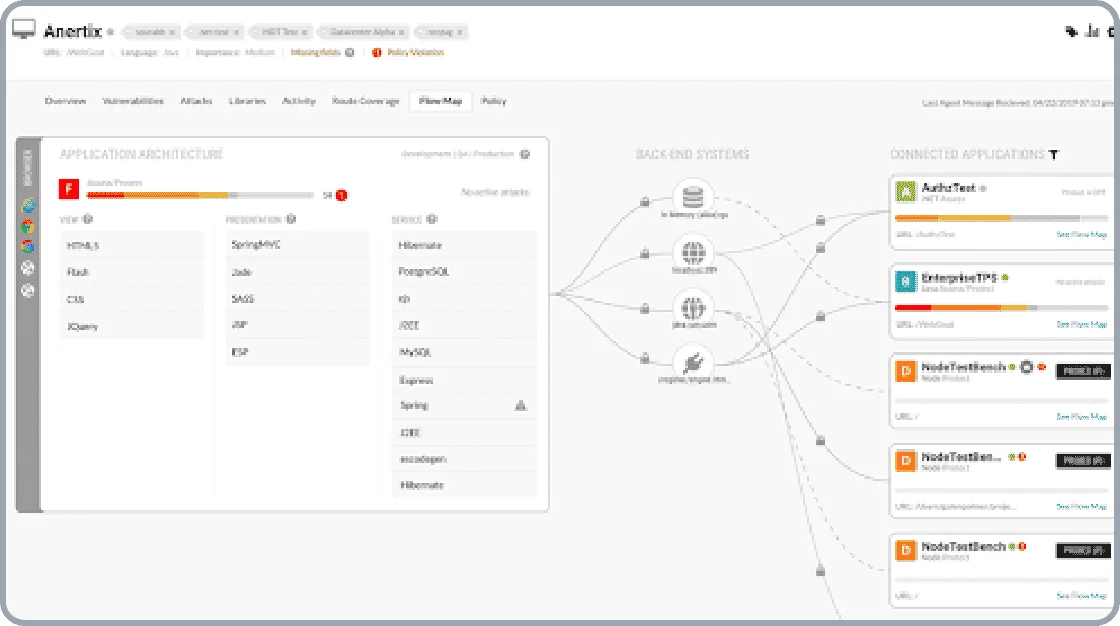
The IAST engine traces data from sources (user input, file reads, external APIs) through the application to sinks (database queries, OS commands, file writes). When tainted data reaches a dangerous operation without proper validation, Assess reports the vulnerability.
Supported languages: Java, .NET (Framework & Core), Node.js, Python, Ruby, Go.
Detected vulnerabilities: SQL injection, XSS, command injection, path traversal, XXE, insecure deserialization, weak cryptography, LDAP injection.
 Contrast Assess vulnerability report — runtime data flow trace from HTTP source to vulnerable database sink.
Contrast Assess vulnerability report — runtime data flow trace from HTTP source to vulnerable database sink.
Contrast Protect (RASP)
Contrast Protect blocks attacks in production by monitoring requests and blocking exploitation attempts. The same instrumentation agent used for IAST adds runtime protection.
When an attack is detected — like SQL injection in a query parameter — Protect blocks the request and logs the event. No code changes required.
The protection runs inside the application, not at the network perimeter.
Performance impact is typically under 5% overhead. Protect runs alongside existing WAF and network security tools.
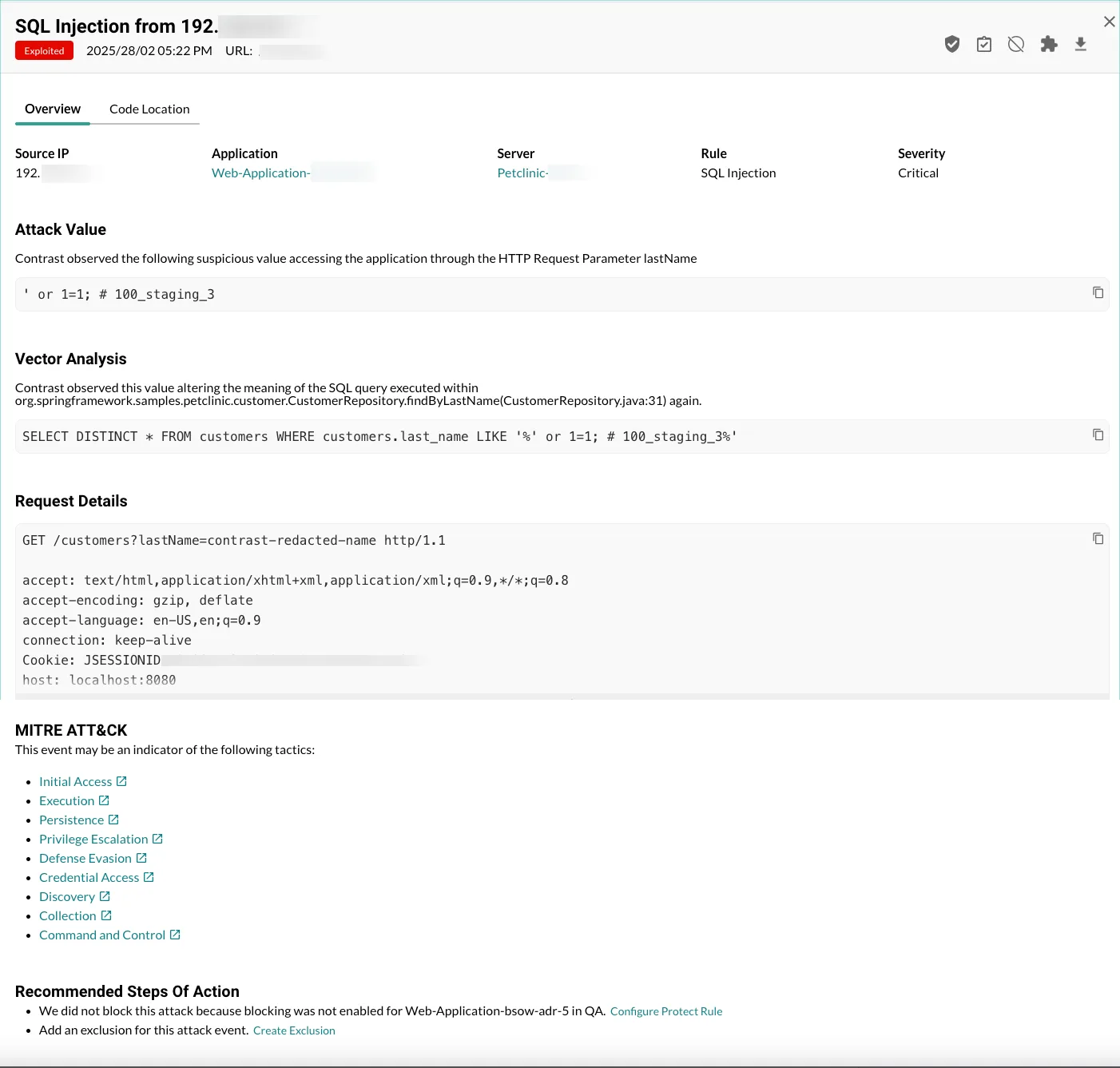 Contrast Protect attack event — blocked SQL injection attempt with payload, source IP, and targeted endpoint.
Contrast Protect attack event — blocked SQL injection attempt with payload, source IP, and targeted endpoint.
Contrast Scan (SAST)
Contrast Scan analyzes source code for security vulnerabilities without requiring compilation or execution. Built for CI/CD pipelines, scans complete in minutes rather than hours.
The engine traces exploitable data paths from user-controlled sources to dangerous operations rather than pattern-matching every line. This narrows findings to vulnerabilities that are actually reachable, reducing false positives versus signature-based SAST.
Scan covers 30+ languages with full agent support for Java (Kotlin, Scala), .NET (Framework, Core), Node.js, Python, Ruby, Go, and PHP. SAST-only support extends to C/C++, Swift, Objective-C, COBOL, SAP ABAP, RPG IV, PL/SQL, and Transact-SQL.
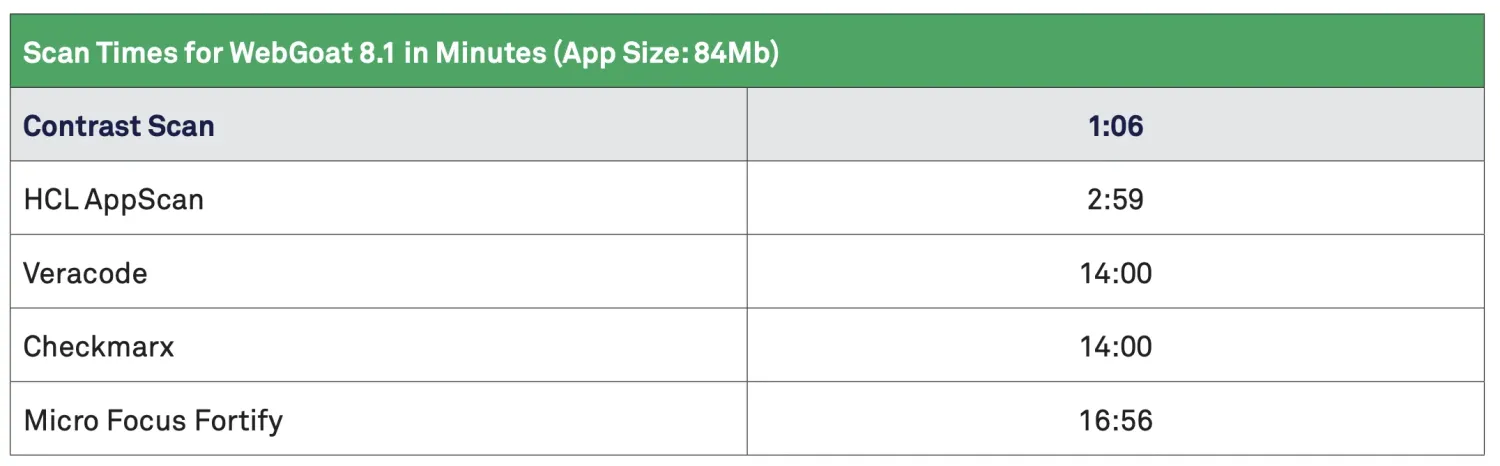 Vendor benchmark: WebGoat scan completes in roughly one minute against Checkmarx and Fortify at 14–16 minutes.
Vendor benchmark: WebGoat scan completes in roughly one minute against Checkmarx and Fortify at 14–16 minutes.
Contrast SCA
Contrast SCA identifies vulnerable open-source libraries in application dependencies. It monitors which libraries are actually loaded and executed at runtime, not just listed in dependency manifests.
This runtime analysis prioritizes vulnerabilities in libraries your application uses. Dependencies listed in package.json but never loaded don’t trigger alerts.
SCA detects vulnerable versions, license compliance issues, and outdated dependencies. Integrates with Dependabot, Snyk, and other supply chain tools for unified visibility.
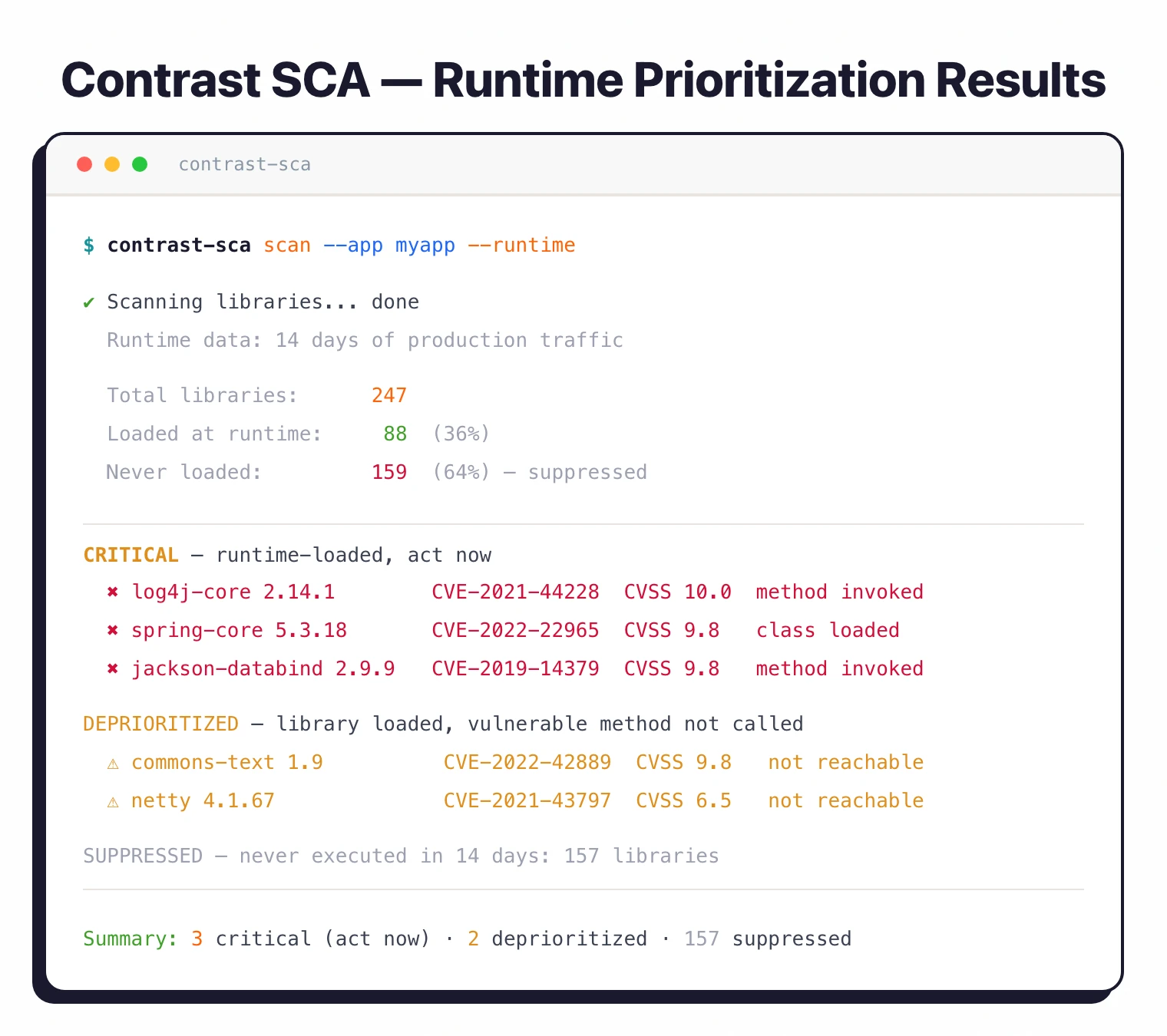 Contrast SCA runtime prioritization — vulnerabilities ranked by whether vulnerable functions are actually invoked, not just declared.
Contrast SCA runtime prioritization — vulnerabilities ranked by whether vulnerable functions are actually invoked, not just declared.
What are Contrast Security’s key features?
| Feature | Details |
|---|---|
| Instrumentation | Java, .NET (Framework/Core), Node.js, Python, Ruby, Go |
| IAST (Assess) | Runtime vulnerability detection during testing with data flow analysis |
| RASP (Protect) | Production attack blocking with sub-5% overhead |
| SAST (Scan) | Fast pipeline-native source code scanning |
| SCA | Runtime library analysis and vulnerability prioritization |
| Deployment | On-premises, SaaS, hybrid, air-gapped environments |
| Integrations | IDE plugins, CI/CD (GitHub Actions, Jenkins, GitLab), Jira, Slack |
| Compliance | OWASP Top 10, CWE coverage, PCI-DSS, HIPAA, SOC 2 support |
How do I get started with Contrast Security?
CI/CD integration
Contrast Scan integrates into CI/CD pipelines as a CLI tool. Run scans in GitHub Actions, GitLab CI, Jenkins, or any pipeline that executes shell commands.
# GitHub Actions example
- name: Contrast Scan
run: |
contrast scan \
--file target/app.jar \
--api-key ${{ secrets.CONTRAST_API_KEY }} \
--authorization ${{ secrets.CONTRAST_AUTH }} \
--organization-id ${{ secrets.CONTRAST_ORG_ID }}
The CLI exits with non-zero status when vulnerabilities above a severity threshold are detected. This fails builds before vulnerable code merges.
The agent-side products integrate the same way. Contrast Assess and Contrast Protect ship CI plugins for Jenkins, GitLab CI, GitHub Actions, Azure DevOps, and CircleCI, with build-break thresholds tied to severity, route coverage, or specific rule IDs.
The build-break trigger is the buyer-side question that comes up most often: a critical finding (or a regression in route coverage) fails the pipeline before the artifact promotes to staging.
Findings flow into the issue trackers developers already use — Jira and ServiceNow on the enterprise side, GitHub Issues and GitLab Issues on the developer side — so a Contrast Assess vulnerability lands as a ticket with the file, line, full data flow trace, and remediation guidance attached.
IDE plugins for IntelliJ, Visual Studio, VS Code, and Eclipse mirror the same view inline. Teams that prefer to pin the integration to the agent itself can use the Contrast REST API plus the agent’s environment variables (CONTRAST_API_KEY, CONTRAST_SERVER_NAME, severity threshold flags) to script the gate without a vendor plugin.
When to use Contrast Security
Contrast Security works well for teams that want runtime-based security testing with low false positives. The instrumentation approach reduces alert fatigue by focusing on vulnerabilities in code paths that actually execute.
Organizations running Java, .NET, or Node.js applications benefit most from the runtime agent support. Teams that already use automated testing get immediate value from IAST without changing their test process.
The platform suits both development (Assess, Scan, SCA) and production (Protect) use cases. Running IAST during QA and RASP in production provides security coverage across the lifecycle.
For teams preferring non-instrumentation approaches, Snyk Code offers IDE-integrated SAST and Semgrep provides custom rule-based static analysis. For web application scanning without agent installation, Invicti and Burp Suite provide DAST capabilities.
Browse other IAST tools and RASP tools to compare runtime security options.
What are alternatives to Contrast Security?
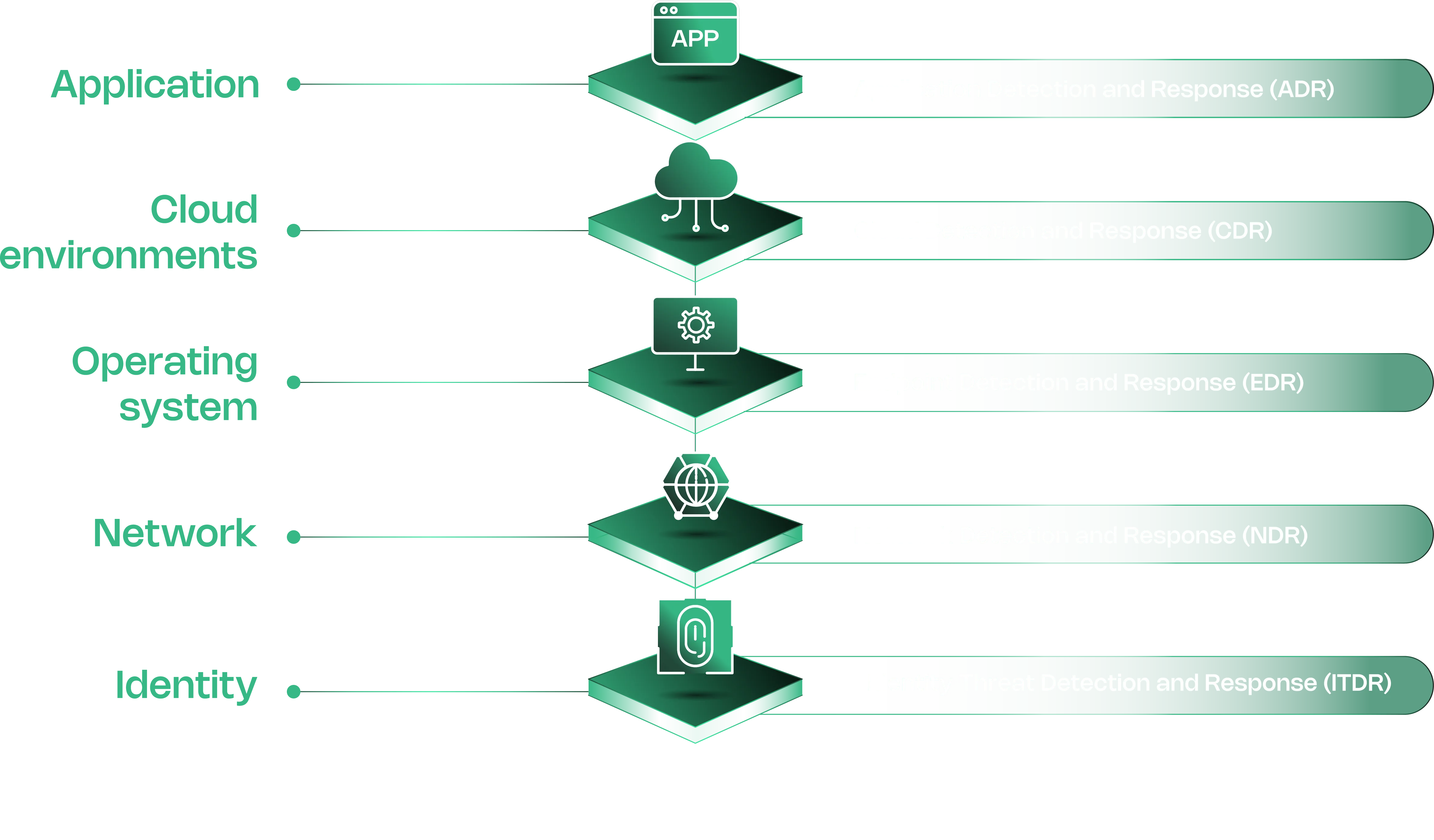
Contrast Security competes in two adjacent markets — IAST for testing and runtime defense (RASP / ADR) for production. The closest alternatives split along that line.
- APM-coupled runtime security. Datadog Code Security is the closest like-for-like for teams already running Datadog observability. Datadog acquired the Hdiv runtime engine in May 2022 and now bundles IAST alongside SAST and SCA under the Code Security suite. Single env-var deployment vs Contrast’s per-app agent install.
- Wider language coverage. Seeker IAST , now part of Black Duck Software after the late-2024 Synopsys spin-off, covers 10+ languages and adds active verification — Seeker confirms each finding is exploitable before it lands in the report.
- Java enterprise SAST+IAST bundle. HCL AppScan is the regulated-industry pick for shops that already license SAST and DAST from HCL.
- DAST+IAST hybrid. Invicti Shark layers an IAST sensor inside the Invicti DAST scanner — a different architecture, useful when the headline need is proof-based DAST findings.
For the deeper list and side-by-side scoring, see Contrast Security alternatives and the head-to-head Contrast Security vs Seeker .







