Contrast Scan is the SAST component of the Contrast AST (Application and API Security Testing) platform. It scans 30+ languages for security vulnerabilities by focusing on exploitable data paths rather than flagging every theoretical issue.
Part of Contrast Security’s broader platform alongside Contrast Assess (IAST) and Contrast SCA, Contrast Scan is designed to complement runtime security products with static code analysis.
It is one of the few SAST products that shares a runtime agent model with its IAST and RASP siblings.
What is Contrast Scan?
Contrast Scan analyzes source code to find security vulnerabilities before deployment.
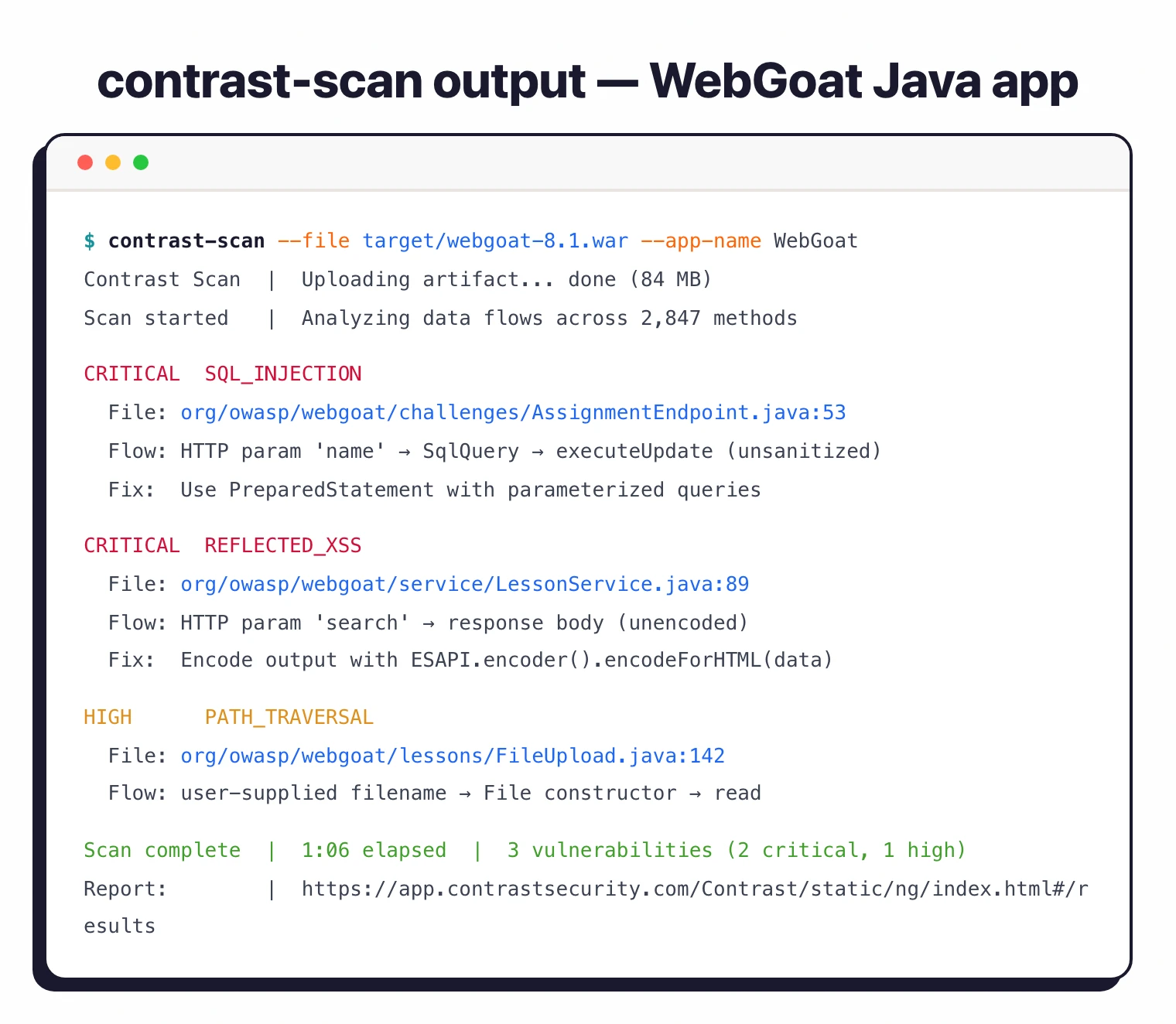
The tool uses a risk-based analysis engine that focuses on exploitable data paths — tracing how data moves through the application to identify where attacks like SQL injection and command injection could succeed.
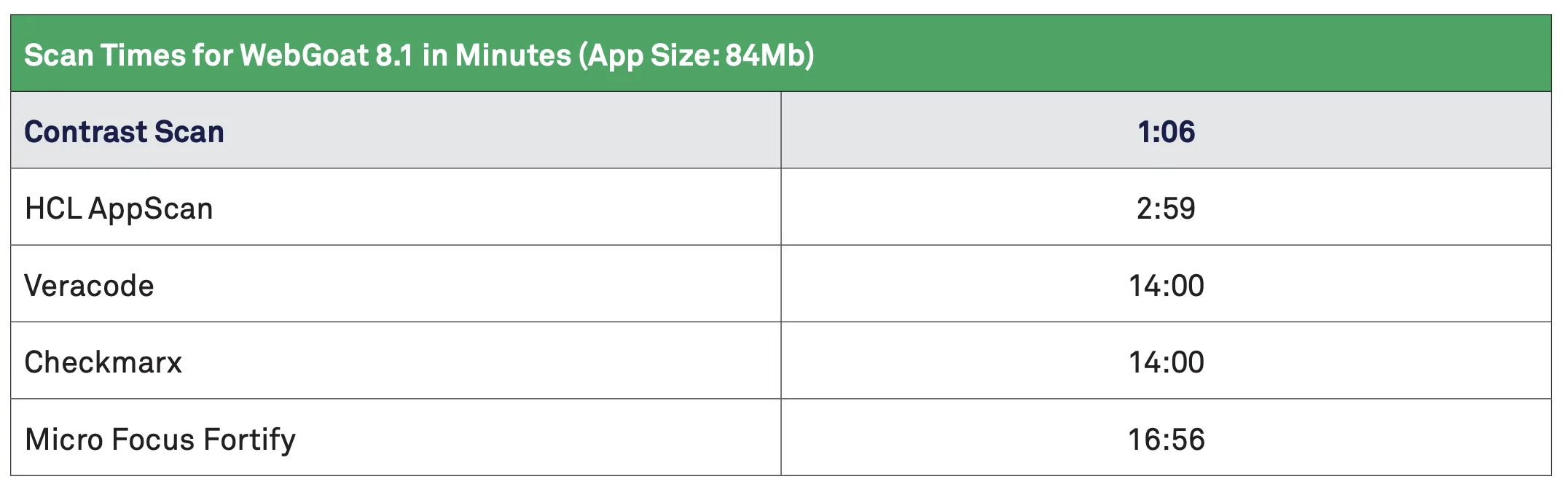
Users upload binary packages to Contrast’s secure environment for analysis. Scan results are delivered in seconds according to the product page.
The tool does not scan open-source code or libraries; that is handled separately by Contrast SCA.
Key features
Risk-based analysis
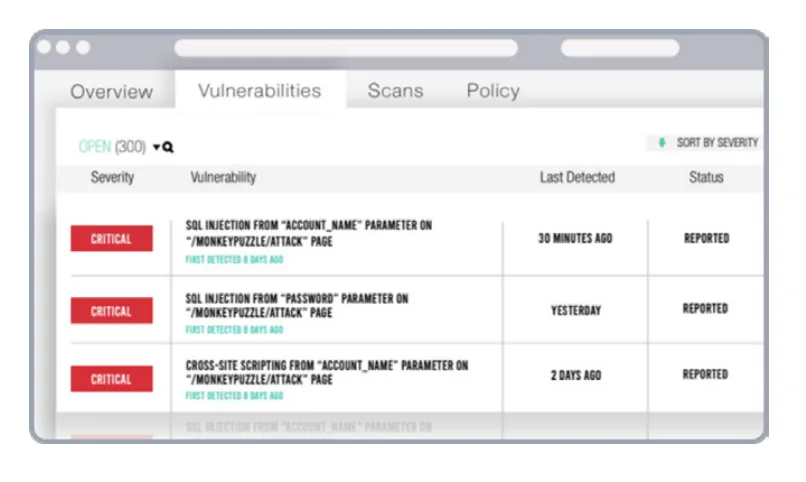
Contrast Scan traces data flows to identify vulnerabilities that could allow attacks.
Rather than flagging all code that matches a pattern, it focuses on paths where data can flow from a user-controlled source to a dangerous operation without sanitization.
The analysis covers injection vulnerabilities (SQL, command, server-side), among other vulnerability categories.
Multi-language support
| Category | Languages |
|---|---|
| JVM | Java, Kotlin, Scala |
| .NET | C#, VB.NET, .NET Core, .NET Framework, ASP.NET |
| Web | JavaScript, TypeScript, Node.js, PHP, Ruby, Python |
| Systems | C, C++, Go, Swift, Objective-C |
| Enterprise | COBOL, SAP ABAP, RPG IV, PL/SQL, Transact-SQL |
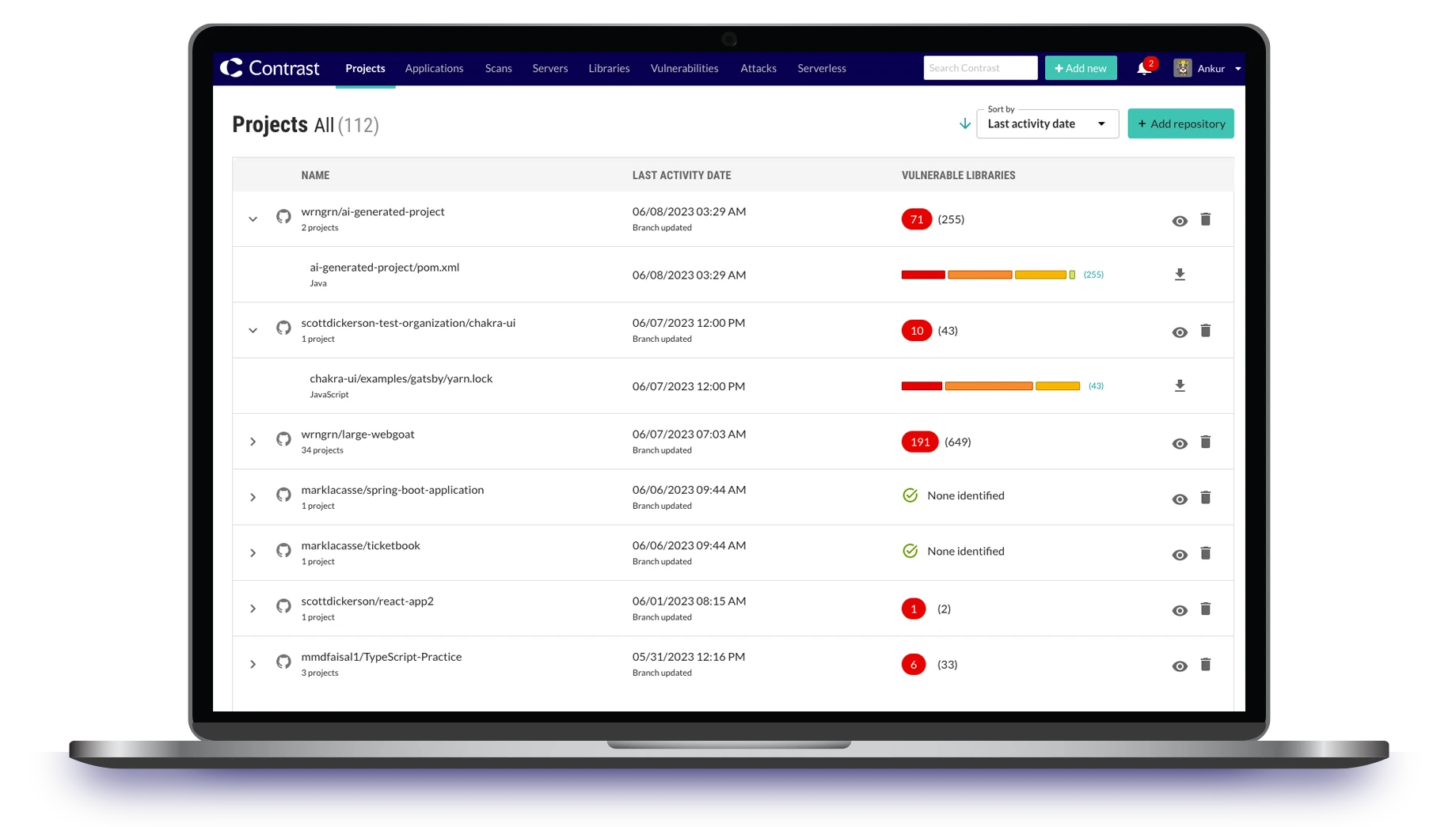
Contrast Scan is one piece of the Contrast AST platform. Contrast Assess provides IAST (runtime testing), Contrast SCA handles dependency vulnerabilities, and Contrast ADR provides application detection and response.
The platform uses the “Contrast Graph” to combine threat sensors, risk scoring, and analytics.
Remediation guidance
Contrast Scan provides code-level remediation guidance in multiple languages, showing developers how to fix each vulnerability rather than just flagging it.
Integrations
Getting started
When to use Contrast Scan
Contrast Scan is a good fit for organizations that already use or plan to use Contrast’s runtime security products (Assess and ADR). The platform provides coverage from static analysis through to runtime protection under one roof.
Teams focused exclusively on SAST may find more flexibility with standalone tools like Semgrep or Checkmarx.
Contrast Scan’s strength is its integration with runtime context rather than standing alone as a SAST tool. See our Contrast alternatives guide for more options.
Customers include Unit4, Snap Finance, AARP, and Citizens Bank.
Frequently Asked Questions
What is Contrast Scan?
Is Contrast Scan free?
What languages does Contrast Scan support?
How does Contrast Scan work?
What integrations does Contrast Scan support?
* Pricing data from Vendr — anonymized contract values from real buyer transactions.