Contrast SCA is a software composition analysis tool that uses runtime instrumentation to prioritize vulnerabilities based on actual library usage.
Instead of reporting every CVE in every dependency, it shows which vulnerable components are actually loaded and executed in production.
In a landscape where the Black Duck 2026 OSSRA report — now in its eleventh consecutive year of open-source codebase analysis after the post-Synopsys rebrand — continues to find open-source dominating commercial application risk, knowing which of those components actually run is a meaningful signal cut.
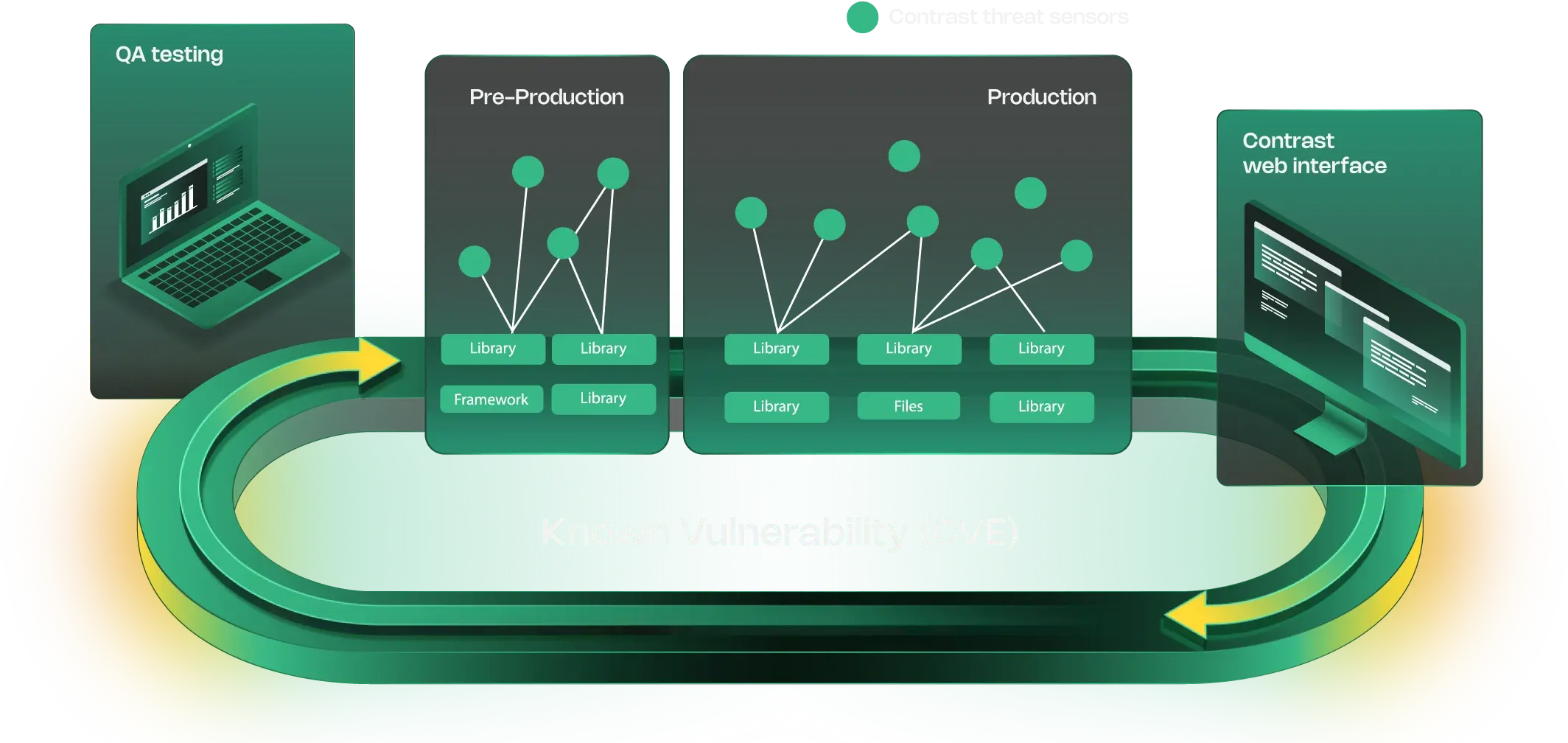
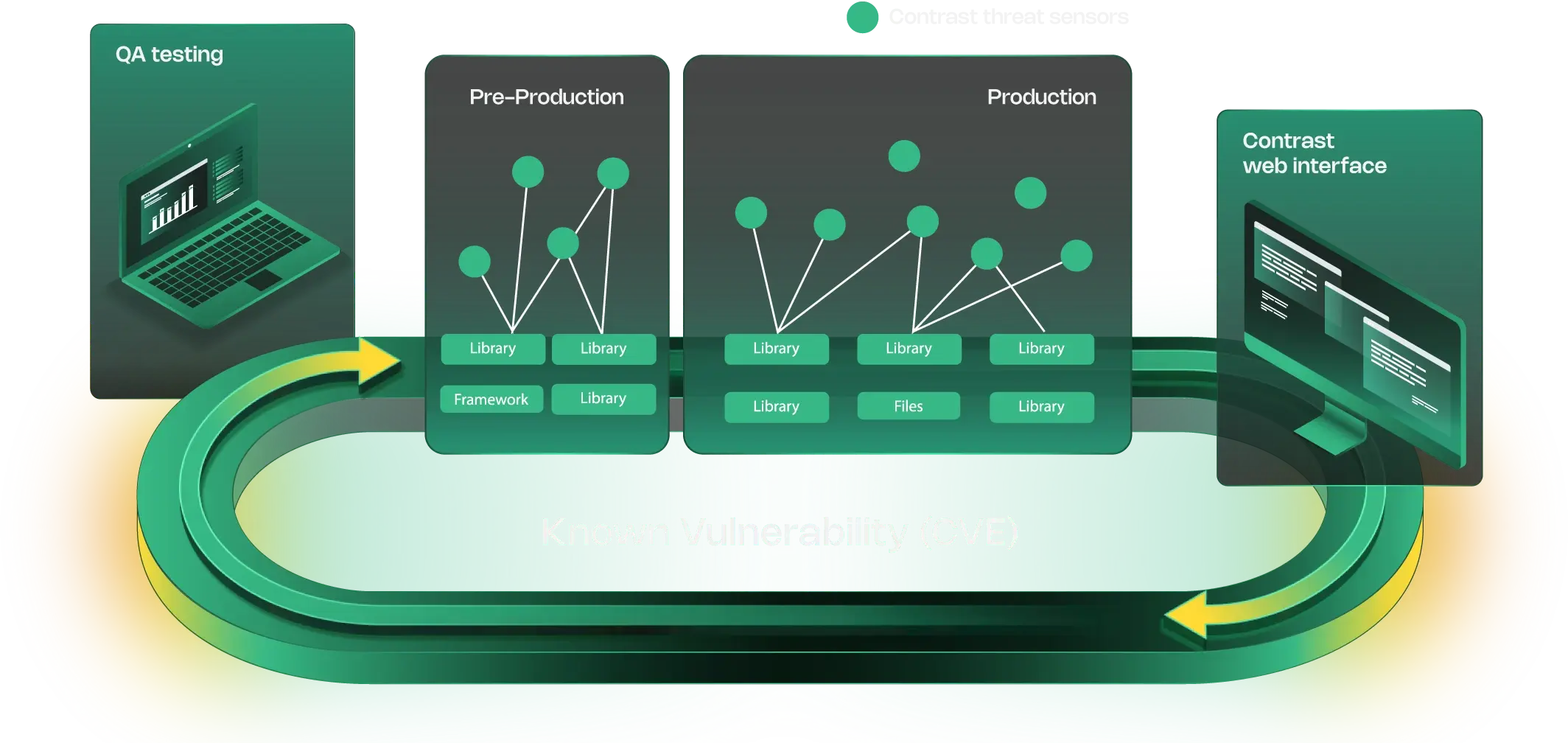
The tool shares the same agent as Contrast Assess (IAST) and Contrast Protect (RASP). The agent monitors which libraries and classes execute at runtime, providing ground-truth usage data that static analysis cannot match.
What is Contrast SCA?
Contrast’s research shows 62% of libraries in applications are never used at runtime. Within the active libraries, only 31% of classes are actually invoked.
Traditional SCA tools report every vulnerability across all dependencies. Contrast SCA narrows that down to the subset that is actually loaded and executed.
This is what the industry now calls runtime SCA or runtime-aware prioritization — dependency analysis that rides on runtime agent data rather than static manifest parsing alone. It is Contrast SCA’s core differentiator against classic CI-native SCA like Snyk or Black Duck.
Contrast SCA is distinct from Contrast Assess (the IAST product) and Contrast Protect (the RASP product), even though all three share the same language agent. Contrast SCA is the library-vulnerability view inside that agent; Contrast Assess is the first-party-code IAST view; they are separate licenses with different deployment intent.
Key features
| Feature | Details |
|---|---|
| Runtime tracking | Class and method-level execution monitoring across 7 language agents |
| Library filtering | 62% of libraries never used at runtime; 31% of classes actually invoked |
| Reachability analysis | Combined static call graph + runtime execution data |
| Language agents | Java, .NET, Node.js, Python, Go, PHP, Ruby |
| SBOM generation | CycloneDX and SPDX formats enriched with runtime usage data |
| License compliance | Policy enforcement, conflict detection, attribution generation |
| Shared instrumentation | Same agent covers SCA, IAST (Assess), and RASP (Protect) |
| Reporting | Priority-based reports organized by runtime execution context |
Supported languages and agents
| Language | Agent | Runtime tracking |
|---|---|---|
| Java | Contrast Java Agent | Class and method-level |
| .NET | Contrast .NET Agent | Class and method-level |
| JavaScript/Node.js | Contrast Node Agent | Module-level |
| Python | Contrast Python Agent | Module-level |
| Go | Contrast Go Agent | Function-level |
| PHP | Contrast PHP Agent | Module-level |
| Ruby | Contrast Ruby Agent | Module-level |
Runtime prioritization
Contrast tracks library usage down to the class and method level: which classes are loaded, which methods are called, how often code paths execute, and the call stack context.
This turns the “247 dependencies with 89 vulnerabilities” problem into “focus on these 3 first.”
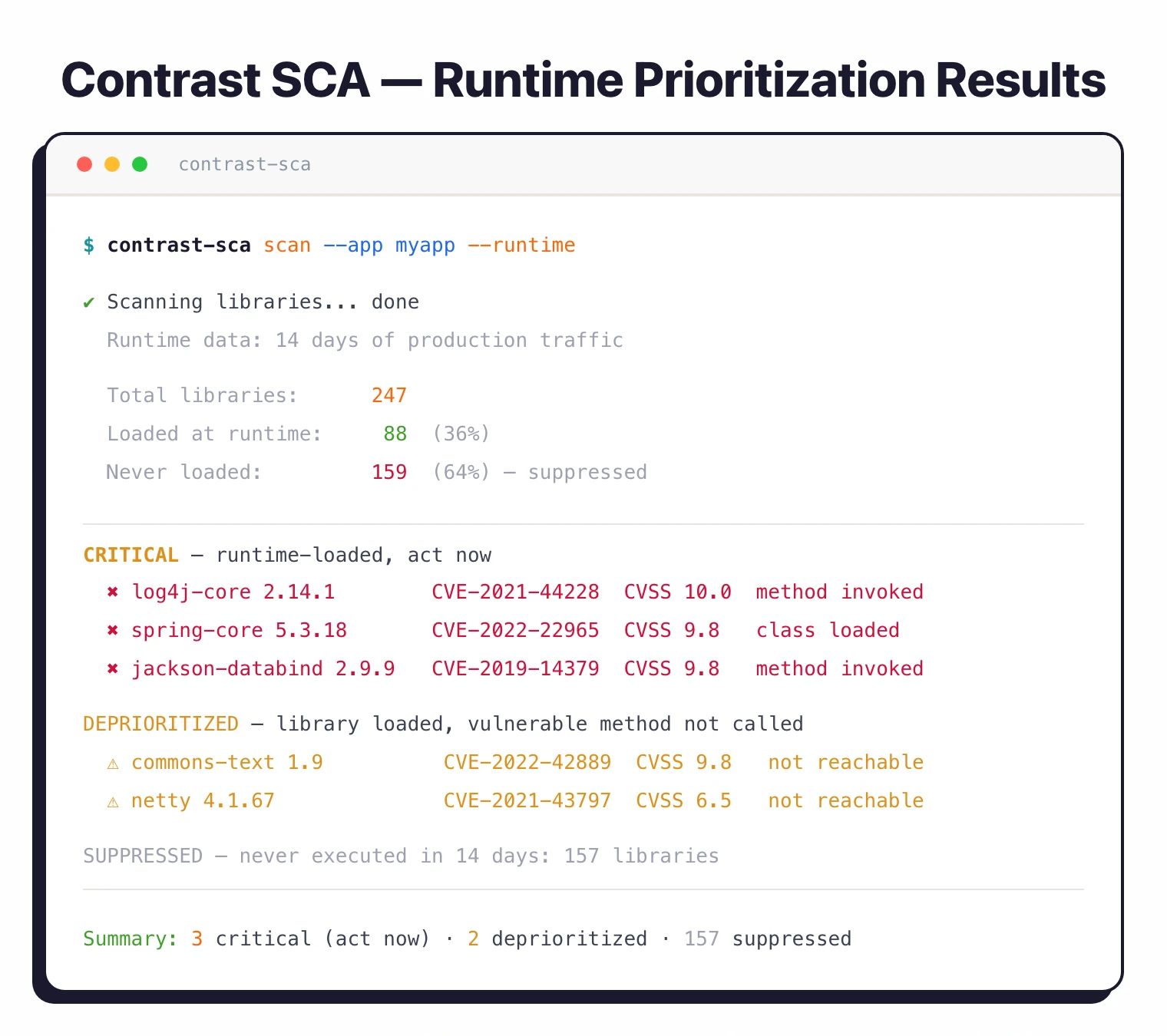
Contrast’s runtime data shows 62% of libraries in applications are never used at runtime. Of the libraries that are loaded, only 31% of their classes are actually invoked.
This means most SCA alerts from static-only tools are noise for code that never runs.
Vulnerability reachability
The tool combines static call graph analysis with runtime execution data and data flow to vulnerable methods. A CVE in a library that is loaded but never called gets deprioritized.
A CVE in a method your application calls every request gets flagged immediately.
License compliance
Tracks open-source license obligations with license identification, compliance policy enforcement, license conflict detection, and attribution generation.
SBOM generation
Generates SBOMs in CycloneDX and SPDX formats. The runtime data enriches the SBOM with actual usage information beyond what static analysis provides.
Transitive dependency analysis
The runtime agent observes which libraries actually load at runtime, which includes transitive dependencies pulled in indirectly through direct imports and libraries injected by the application server or framework. This catches transitive packages that pure static-manifest SCA can miss when a library is resolved dynamically rather than declared in the top-level manifest.
Malicious package detection
Contrast SCA is not positioned as a behavioral malicious-package detector in the Socket or Phylum pattern. Typosquat detection, maintainer-compromise alerts, and dependency-confusion signals are not core differentiators here. Teams that need explicit supply-chain-attack catchup typically layer Contrast SCA’s runtime view on top of a behavioral SCA such as Socket or pair it with Black Duck’s registry controls.
Dependency update automation
Contrast SCA does not ship automated dependency-update pull requests in the Dependabot or Renovate pattern — the product’s remediation model is runtime-prioritized triage and CI policy gating, not auto-merge update PRs. Teams running Contrast SCA typically keep a dedicated updater (Dependabot, Renovate, or Mend Renovate) running in parallel for routine upgrade hygiene.
Integrations
Getting started
When to use Contrast SCA
Contrast SCA fits teams that want runtime-aware vulnerability prioritization, especially those already using Contrast Assess or Protect. The shared agent means adding SCA requires no additional deployment.
The runtime data genuinely cuts through alert noise. If 62% of your libraries never execute, that is 62% fewer alerts to triage.
The tradeoff: you need to instrument your application with the Contrast agent, which means SCA only works on running applications.
Teams that need to scan without running the application (build-time-only scanning) should consider static SCA tools like Snyk or Grype.
How it compares:
| vs. | Key difference |
|---|---|
| Snyk Open Source | Snyk uses static reachability analysis. Contrast SCA uses actual runtime data for more accurate prioritization but requires agent deployment. |
| Endor Labs | Endor Labs uses static call graph analysis for reachability. Contrast SCA adds runtime observation for ground-truth usage data. |
Further reading: What is SCA? | SCA in CI/CD Pipelines
Contrast SCA pricing
Contrast Security does not publish public dollar pricing for Contrast SCA. Quotes are routed through sales via the contrastsecurity.com/contact form.
The licensing shape is typically per-application and per-environment, sold alongside or separately from Contrast Assess (IAST) and Contrast Protect (RASP). Because the same language agent backs all three products, adding Contrast SCA to an existing Contrast Assess deployment does not require a second agent rollout — the cost delta is license-only.
There is no current free tier. Contrast’s previous free developer offering, CodeSec by Contrast, reached end-of-life on May 1, 2025, with new-user sign-ups blocked from January 28, 2025. Teams that need a free SCA entry point today look at static alternatives like Grype or Trivy rather than a Contrast-branded free tier.
Re-check directly with Contrast Security before budgeting — enterprise platform pricing and bundle composition change between renewals.
Contrast SCA alternatives
Contrast SCA’s angle is runtime-aware prioritization from a shared IAST/RASP/SCA agent. The closest alternatives each replace a different dimension of that angle.
Snyk Open Source
Snyk Open Source is the developer-first CI-integrated SCA with static reachability analysis. Snyk wins when the requirement is broad language coverage and automated fix PRs inside pipelines; Contrast SCA wins when runtime ground-truth about which libraries execute is the deciding signal.
Endor Labs
Endor Labs uses function-level static call-graph reachability to cut CVE noise without an agent. Endor is the right pick for teams that want reachability prioritization but cannot run an agent in production; Contrast SCA adds the runtime layer Endor cannot observe.
Black Duck
Black Duck is the classic enterprise SCA with the deepest license-compliance and binary-analysis tooling. Black Duck fits legal-heavy regulated industries; Contrast SCA fits teams where runtime prioritization and IAST co-deployment are more valuable than license-compliance depth.
Socket
Socket focuses on behavioral analysis of npm and PyPI packages for supply-chain-attack catchup. Socket replaces Contrast SCA’s (absent) malicious-package detection layer rather than its runtime layer — larger teams often run both.
For broader landscape, see SCA tools overview and what SCA does.
Contrast SCA FAQ
What makes Contrast SCA runtime-aware vs classic SCA?
Classic SCA parses manifests and lockfiles at build time — every declared dependency shows up in the report, whether the application ever calls it or not. Contrast SCA adds a runtime agent that observes which classes and methods actually execute in production, then uses that data to deprioritize CVEs in dependencies or code paths that are never loaded. The tradeoff: the signal cut only kicks in once the agent is instrumented on a running application.
Does Contrast SCA use the same agent as Contrast Assess (IAST)?
Yes. The Java, .NET, Node.js, Python, Go, PHP, and Ruby agents are the same binary instrumentation across Contrast SCA, Contrast Assess (IAST), and Contrast Protect (RASP). SCA, IAST, and RASP capabilities are licensed separately, but there is no additional agent to deploy once any of the three is already running on an application.
What languages does Contrast SCA support?
Seven language agents: Java, .NET, Node.js, Python, Go, PHP, and Ruby. Java and .NET support class- and method-level tracking; Node.js, Python, PHP, and Ruby are module-level; Go is function-level.
Does Contrast SCA generate SBOMs in SPDX and CycloneDX?
Yes, both formats. The SBOM output is enriched with runtime-usage flags from the agent, so downstream consumers can tell which listed components the application actually loaded rather than just which were declared in the manifest.
Is there a free tier?
No. Contrast’s free developer tier, CodeSec by Contrast, reached end-of-life on May 1, 2025 and is no longer accepting new users. The enterprise Contrast SCA agent is sold as part of the Contrast Security platform and is quoted through sales.