Kubernetes configuration scanning tools — Kubescape , Kube-bench, and Checkov — catch misconfigurations before workloads run.
But they cannot detect what happens once a container is running: a cryptominer spawning inside a pod, a shell being opened after a successful container escape, or a lateral movement attempt using a compromised service account. That’s the gap that Kubernetes runtime security tools and admission controllers address.
This guide covers the runtime and policy enforcement layer specifically. For config scanning (CIS benchmarks, Kubernetes hardening guidelines, manifest misconfiguration), see the Kubernetes security tools comparison . For container image vulnerability scanning, see Trivy , Grype , and the container security tools overview.
Runtime vs config scanning
Kubernetes security tools divide into two distinct categories based on when they act.
Config scanners act before a workload runs. They scan Kubernetes manifests, Helm charts, and cluster configurations for misconfigurations — containers running as root, missing resource limits, exposed secrets in environment variables, privileged pod specs.
Tools like Kubescape , Kube-bench, and Checkov operate here. They are essential for shift-left security but blind to runtime behavior.
Runtime security tools act while workloads are running. They monitor system calls, network connections, process execution, and file access from inside running containers.
They detect container escapes, unexpected process spawns, data exfiltration attempts, and cryptomining. Falco and Tetragon operate here.
Admission controllers are a third category that acts at the boundary — they intercept resource creation requests before resources are scheduled and enforce policy.
Kyverno and OPA Gatekeeper are admission controllers: they prevent non-compliant pods from starting based on defined policies. They are neither config scanners nor runtime detectors — they’re the enforcement point between the two.
A mature Kubernetes security program uses all three layers. This guide covers the runtime and admission controller layer.
Top Kubernetes runtime security tools
1. Falco
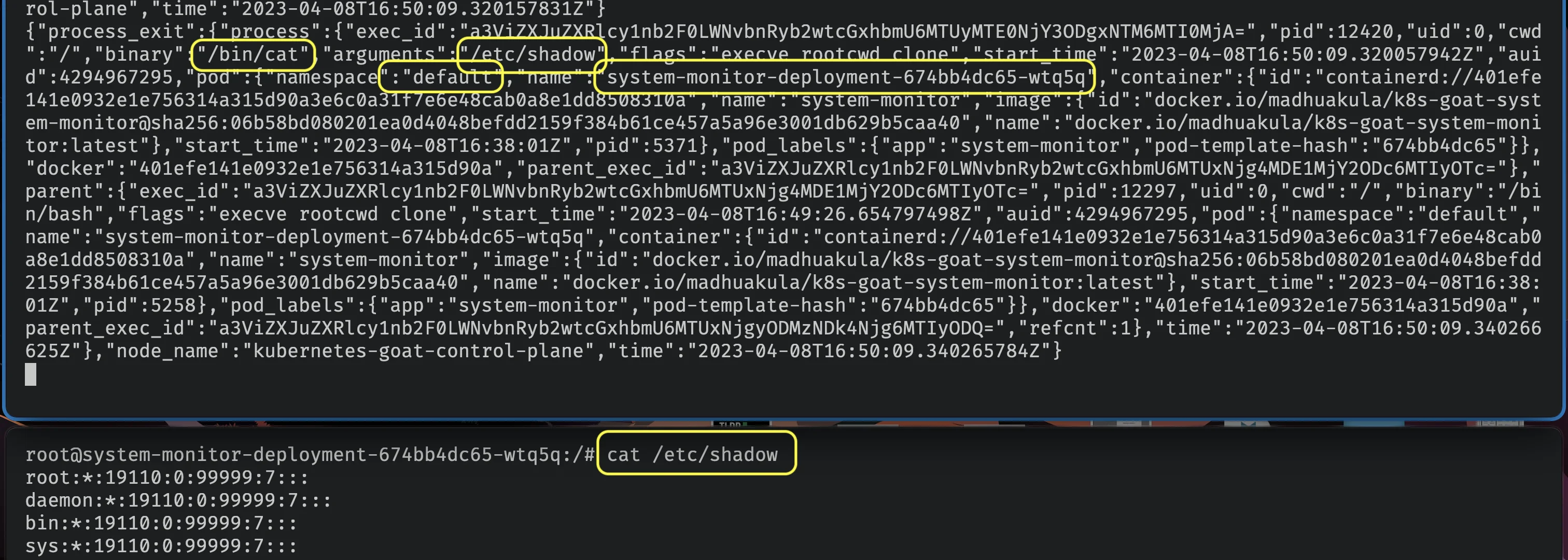
Falco is the CNCF-graduated standard for Kubernetes runtime threat detection — it graduated within CNCF on February 29, 2024. It observes Linux kernel system calls from running containers using a kernel module or eBPF probe and evaluates them against a rule engine.
Falco rules match on syscall patterns: a rule fires when a container spawns a shell (execve of sh or bash), reads from /etc/shadow, opens a sensitive directory like /proc, or establishes a network connection to an unexpected address.
The default ruleset ships 200+ rules covering common attack patterns including container escapes, credential access, lateral movement, and crypto mining.
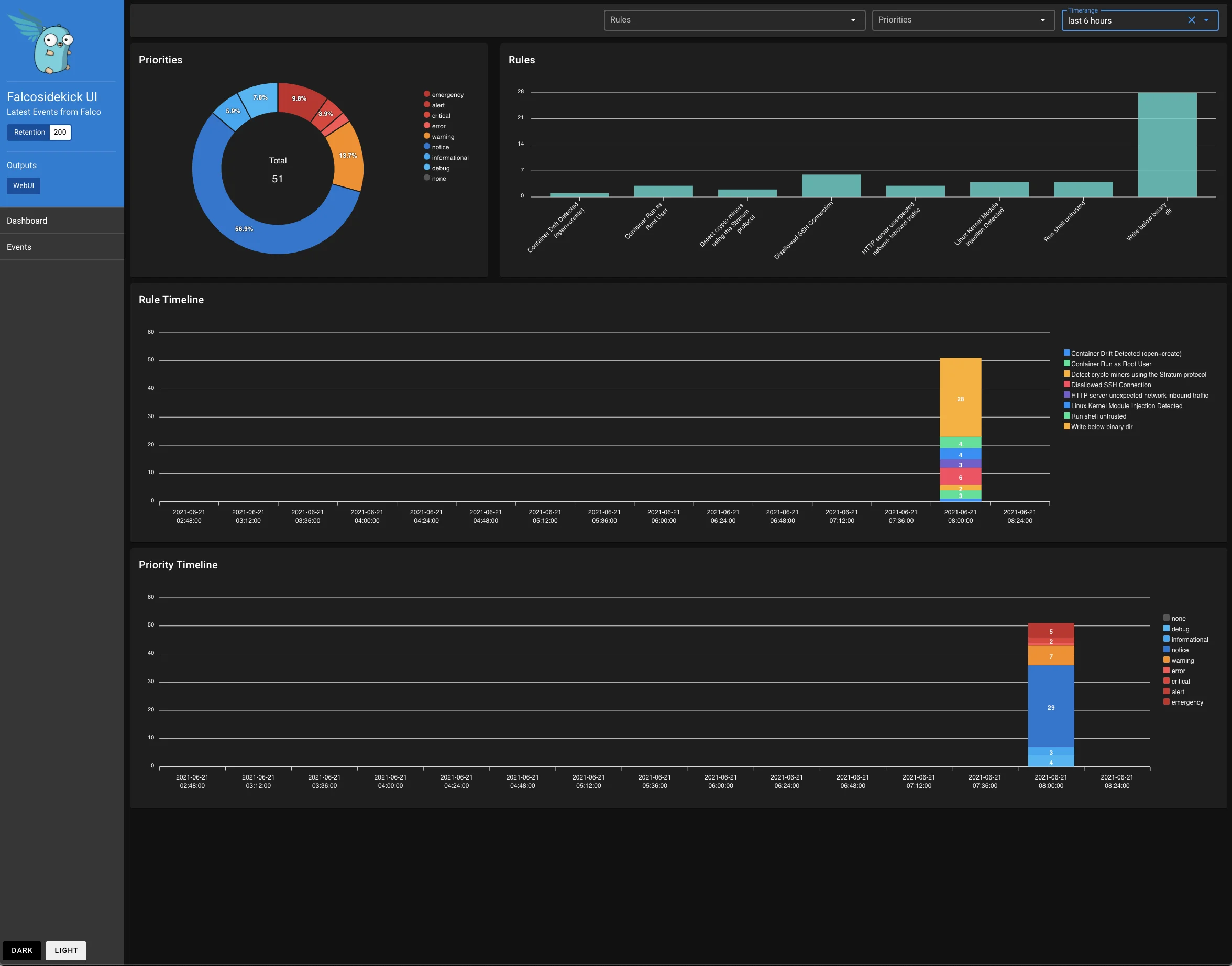
Rules are written in YAML with a conditional expression language. Custom rules can match on any combination of syscall fields — process name, file path, network address, user ID, and more. Falcosidekick routes alerts to Slack, PagerDuty, Elasticsearch, Datadog, or any webhook.
Falco runs as a DaemonSet on each node and adds minimal overhead — typically under 3% CPU on active workloads. The eBPF-based probe (the preferred modern mode) does not require kernel headers and is stable across major Kubernetes distributions.
Best fit: Any Kubernetes cluster that needs runtime threat detection. Falco is the default choice — it is the only CNCF-graduated runtime security tool and has the broadest community-maintained ruleset.
2. Kyverno
Kyverno is a Kubernetes-native policy engine and admission controller. Policies are written as Kubernetes YAML resources — no new policy language required. It validates, mutates, and generates Kubernetes resources at admission time.
A Kyverno ClusterPolicy can validate that all pods have resource requests and limits, mutate pod specs to add security context defaults like readOnlyRootFilesystem: true, generate NetworkPolicies automatically when a new namespace is created, or block images from untrusted registries. Policies use familiar Kubernetes patterns (label selectors, JMESPath expressions) rather than a separate DSL.
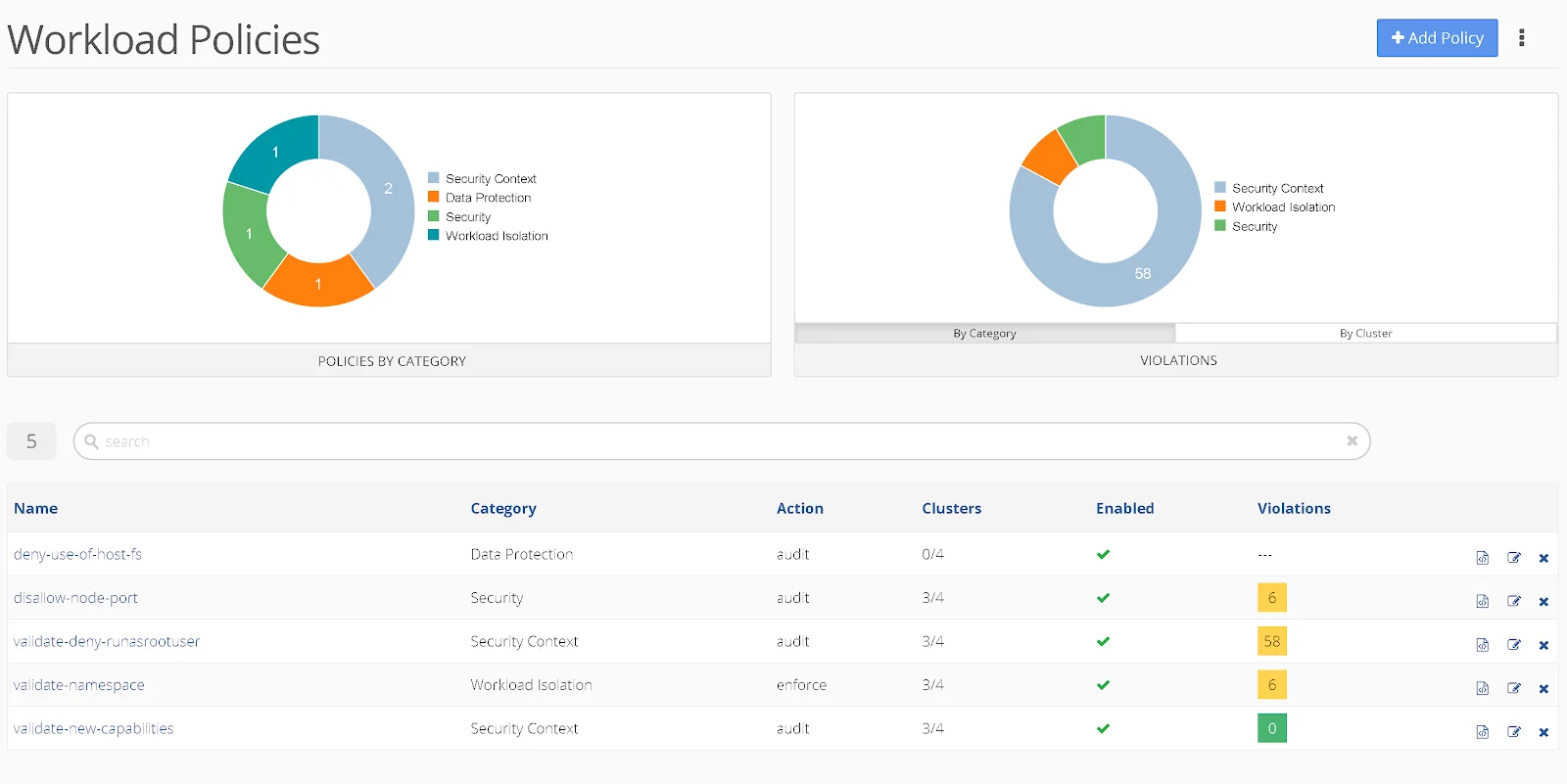
Kyverno also supports image signature verification via Cosign, allowing you to enforce that only signed container images from approved registries are admitted to the cluster. This is a meaningful supply chain security control that most admission controllers require additional tooling to achieve.
Kyverno is a CNCF graduated project (graduated March 2026) with strong adoption across the community. It installs via a Helm chart and integrates with existing GitOps workflows — policies can be stored in Git and synced via Flux or Argo CD.
Best fit: Teams that want Kubernetes admission control without learning Rego. Kyverno is the most accessible policy engine for Kubernetes-native teams and is the default recommendation for new deployments.
3. OPA Gatekeeper
OPA Gatekeeper is a Kubernetes admission controller that enforces policies written in Rego — the policy language of the Open Policy Agent (OPA) project. It is a CNCF graduated project alongside Falco.
Gatekeeper uses a two-resource model: ConstraintTemplates define the Rego logic for a policy, and Constraints instantiate those templates with specific parameters. This separation allows policy authors to create reusable templates and policy consumers to apply them with environment-specific configuration.
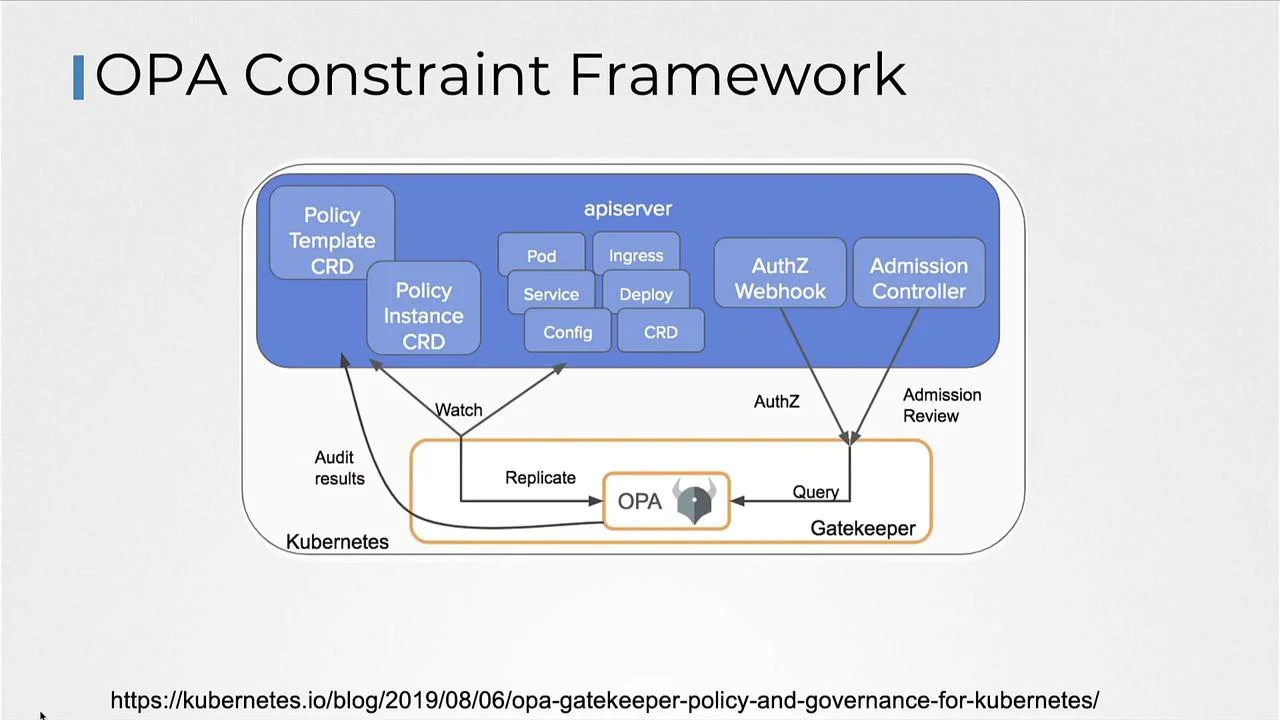
The Gatekeeper policy library provides 80+ pre-built ConstraintTemplates covering standard security policies: disallowing privileged containers, requiring pod security contexts, restricting host networking, blocking NodePort services, and enforcing image tag uniqueness. These can be deployed directly or adapted.
Rego is significantly more expressive than Kyverno’s YAML policies — it can perform arithmetic, string manipulation, data lookups, and complex logical conditions. Organizations that already use OPA for admission control in non-Kubernetes systems (Terraform, Envoy, API gateways) benefit from a single policy language across their infrastructure.
Best fit: Teams with existing OPA investments or those that need complex policy logic that exceeds what Kyverno’s YAML-based policies can express.
4. Cilium Tetragon
Cilium Tetragon is an eBPF-based Kubernetes runtime security tool from the Cilium project. Unlike Falco which operates at the syscall level primarily for detection, Tetragon can both observe and enforce security policies in real-time at the kernel level.
Tetragon’s TracingPolicy resources define kernel-level policies — which processes can be executed, which files can be accessed, which network connections are allowed. Violations can be logged, alerted on, or blocked (with the SIGKILL enforcement mode) without going through the Kubernetes API server. This makes enforcement faster and harder to bypass than webhook-based admission controllers.
Tetragon provides deep observability: every process execution, file open, socket connection, and privilege escalation is captured with full context including the Kubernetes pod, namespace, and workload metadata. This telemetry integrates with OpenTelemetry and can feed into SIEM platforms.
Tetragon requires Cilium as the CNI plugin. For clusters already using Cilium for networking, Tetragon adds a security layer with no additional agent overhead.
Best fit: Clusters already running Cilium as the CNI plugin and teams that need kernel-level policy enforcement (not just detection) for high-security workloads.
5. NeuVector
NeuVector (now open-source under SUSE) is a full-lifecycle Kubernetes security platform covering runtime protection, network segmentation, and vulnerability management. It was acquired by SUSE in 2021 and open-sourced in 2022.
NeuVector’s core runtime security capability is behavioral learning: it observes a workload during a learning period, automatically generates a process and network security profile based on observed behavior, and then switches to protect mode — blocking any deviation from the learned profile. This zero-trust behavioral approach catches novel attacks without requiring a pre-written rule for each threat pattern.
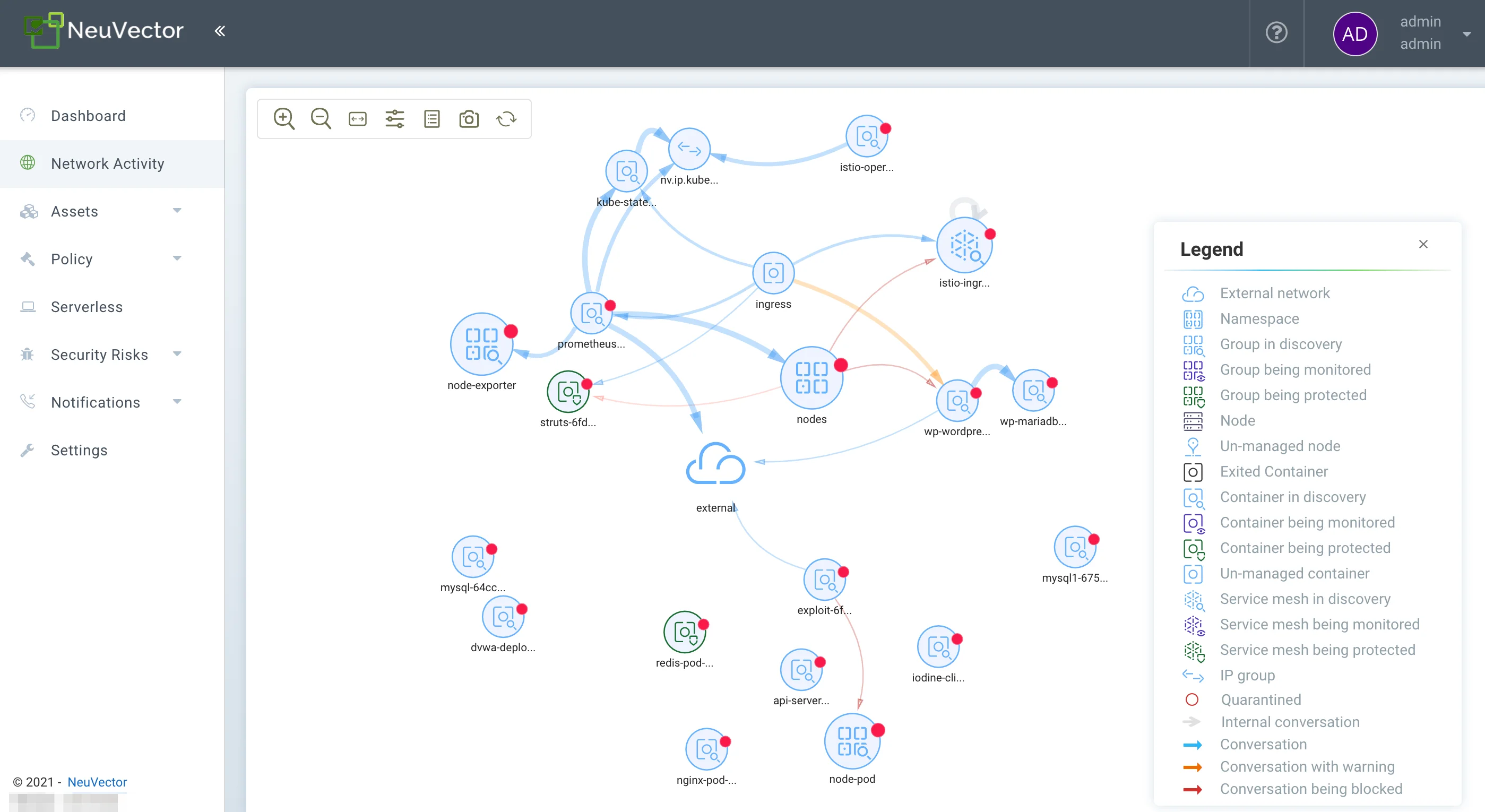
The network segmentation feature provides Layer 7 network policy enforcement directly within Kubernetes, blocking east-west traffic between pods that should not communicate. This is a network security capability that goes beyond what admission controllers and kernel-level security tools typically cover.
NeuVector’s open-source version is fully functional; SUSE offers commercial support contracts.
Best fit: Teams that want automated behavioral security profiles without writing manual rules, or those needing Layer 7 network policy enforcement alongside runtime protection.
6. Aqua Security
Aqua Security offers a full commercial Kubernetes security platform covering admission control, runtime protection, image scanning, and compliance. For runtime security specifically, Aqua uses eBPF to monitor container behavior and provides a managed rules service that keeps threat signatures current.
Aqua’s admission controller enforces image assurance policies — only images that have been scanned and pass defined policies (no critical vulnerabilities, must be from approved registries, must have a valid Aqua scan certificate) are admitted to the cluster. This tightly integrates the build-time scanning and runtime enforcement layers.
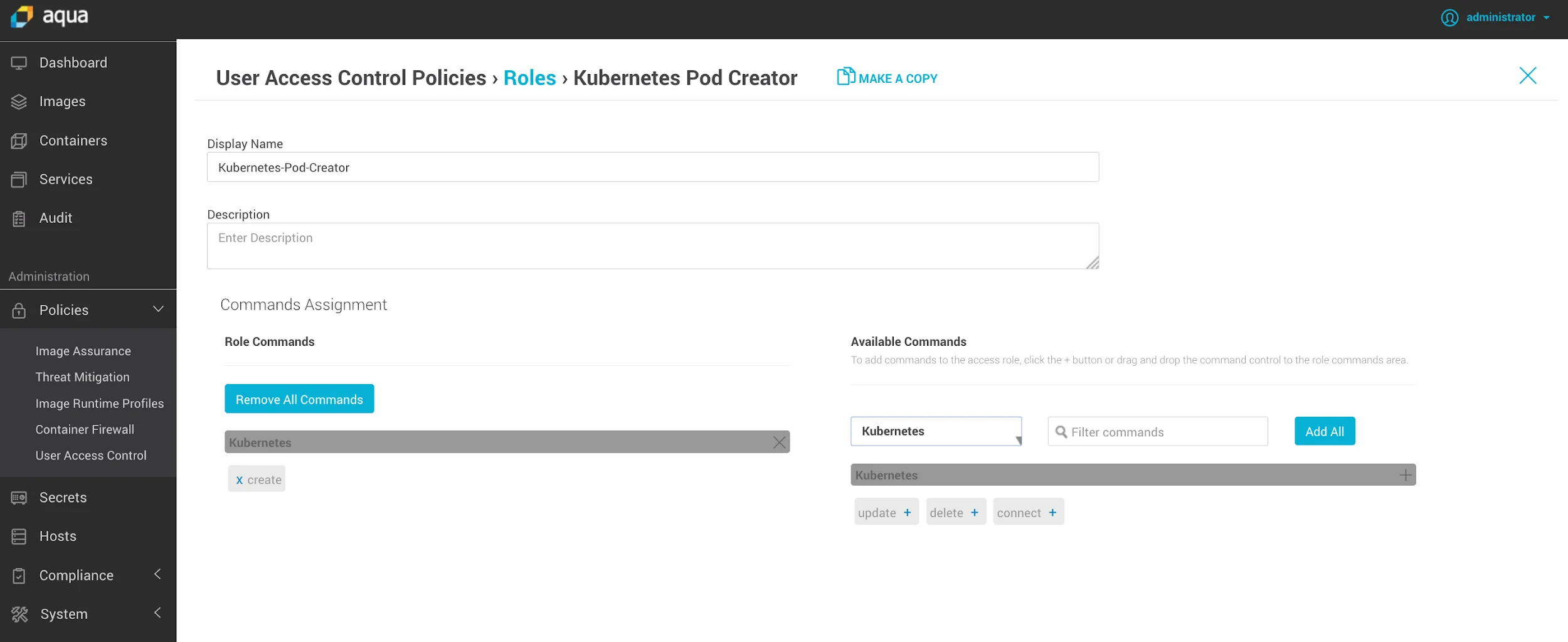
The runtime component monitors process, file, and network activity with policies expressed through Aqua’s policy framework. Aqua provides out-of-the-box compliance mappings for PCI DSS, HIPAA, NIST, and CIS Kubernetes Benchmark.
Best fit: Enterprises that want a single commercial vendor for Kubernetes security across the full lifecycle — image scanning, admission control, and runtime — with managed updates and compliance reporting.
Comparison table
| Tool | Layer | Language | Open Source | Key Strength |
|---|---|---|---|---|
| Falco | Runtime detection | YAML rules | Yes (CNCF) | Syscall-level threat detection |
| Kyverno | Admission control | Kubernetes YAML | Yes (CNCF) | Validate, mutate, generate resources |
| OPA Gatekeeper | Admission control | Rego | Yes (CNCF) | Complex policy logic |
| Cilium Tetragon | Runtime enforcement | TracingPolicy YAML | Yes (CNCF) | eBPF kernel-level enforcement |
| NeuVector | Runtime + network | Behavioral learning | Yes (SUSE) | Auto-learned behavioral profiles |
| Aqua Security | Full lifecycle | Commercial policy | Commercial | Integrated lifecycle enforcement |
How to choose
Start with your primary security gap: detection or prevention.
If your priority is threat detection in running workloads: Deploy Falco first. It is the easiest path to runtime visibility with the most mature community ruleset. Add Tetragon later if you need kernel-level enforcement or are already on Cilium.
If your priority is policy enforcement at admission: Choose Kyverno if your team works primarily in Kubernetes YAML and you want the simplest path to admission control. Choose OPA Gatekeeper if you already use OPA across other systems or need complex policy logic that Kyverno cannot express.
If you need both: Deploy Falco for runtime detection and Kyverno for admission control — this is the most common production combination for teams using open-source tools.
For enterprises: Evaluate Aqua Security if you want a single commercial vendor covering image scanning, admission control, and runtime protection with managed compliance reporting.
Combining tools
Runtime and admission control tools are not mutually exclusive — they are complementary. A typical production setup might look like:
- Kyverno (admission control) — prevents non-compliant pods from starting, enforces image signing, and auto-generates NetworkPolicies.
- Falco (runtime detection) — alerts on malicious behavior in running containers with kernel-level precision.
- Kubescape or Kube-bench (config scanning) — audits the cluster configuration against CIS benchmarks before workloads are scheduled.
For IaC-layer scanning of Kubernetes manifests and Helm charts before deployment, Trivy and Checkov add a fourth layer to the stack. See the IaC security tools overview for context on where manifest scanning fits in the pipeline.
This three-layer approach covers the full Kubernetes security lifecycle: configuration hardening, admission policy enforcement, and runtime threat detection.






