Container security splits across two distinct moments: before a container runs and while it runs. Open-source tools cover both. Image scanners like Trivy , Grype , and Clair catch known CVEs before deployment.
Runtime tools like Falco detect actual threats in production. This guide compares the eight most widely used open-source container security tools, explains where each one fits, and helps you pick the right combination for your environment.
Why open source for container security?
Open-source container security tools scan container images, monitor running containers, and check Kubernetes configurations without licensing costs or procurement delays.
They have become the standard in most engineering organizations — not because commercial tools are lacking, but because the open-source options are genuinely strong and the community has invested heavily in them.
The six load-bearing projects in 2026:
- Trivy — Aqua Security, 34,000+ GitHub stars, image + IaC + SBOM scanning
- Grype — Anchore, fast vulnerability matching against the Anchore feed
- Syft — Anchore, SBOM generation in CycloneDX and SPDX
- Clair — Red Hat, the original Quay registry scanner
- Falco — CNCF Graduated 2024, eBPF-based runtime detection
- kube-bench — Aqua, CIS Kubernetes Benchmark auditor
Together they cover the full lifecycle without paying a licensing fee, though commercial CNAPPs still win on cross-tool prioritization and attack-path context.
Trivy is backed by Aqua Security and has over 34,000 GitHub stars, making it the most-starred open-source security scanner.
Falco graduated from the CNCF in February 2024 . Grype is maintained by Anchore. These are not hobbyist projects — they are production-grade tools with enterprise backing and wide adoption.
The practical advantage for most teams: no licensing costs, no procurement delays, and no vendor lock-in.
The limitation versus commercial platforms like Aqua Security or Sysdig Secure is in correlation and prioritization — commercial tools build attack path context and prioritize findings by exploitability, which open-source tools do not do natively.
Top 8 open-source container security tools
1. Trivy
Trivy is the most widely adopted open-source container security scanner. A single binary handles container image scanning, Kubernetes manifest analysis, filesystem scanning, and SBOM generation (CycloneDX and SPDX). It also covers IaC security for Dockerfiles and Helm charts.
What Trivy does well: OS package scanning across Alpine, Debian, Ubuntu, RHEL, Amazon Linux, and more. Language runtime library scanning covers Python, Node.js, Java, Go, Ruby, Rust, and PHP.
The trivy k8s cluster command scans all running images in a cluster. No external database setup is needed; the vulnerability DB is bundled and updated at scan time.
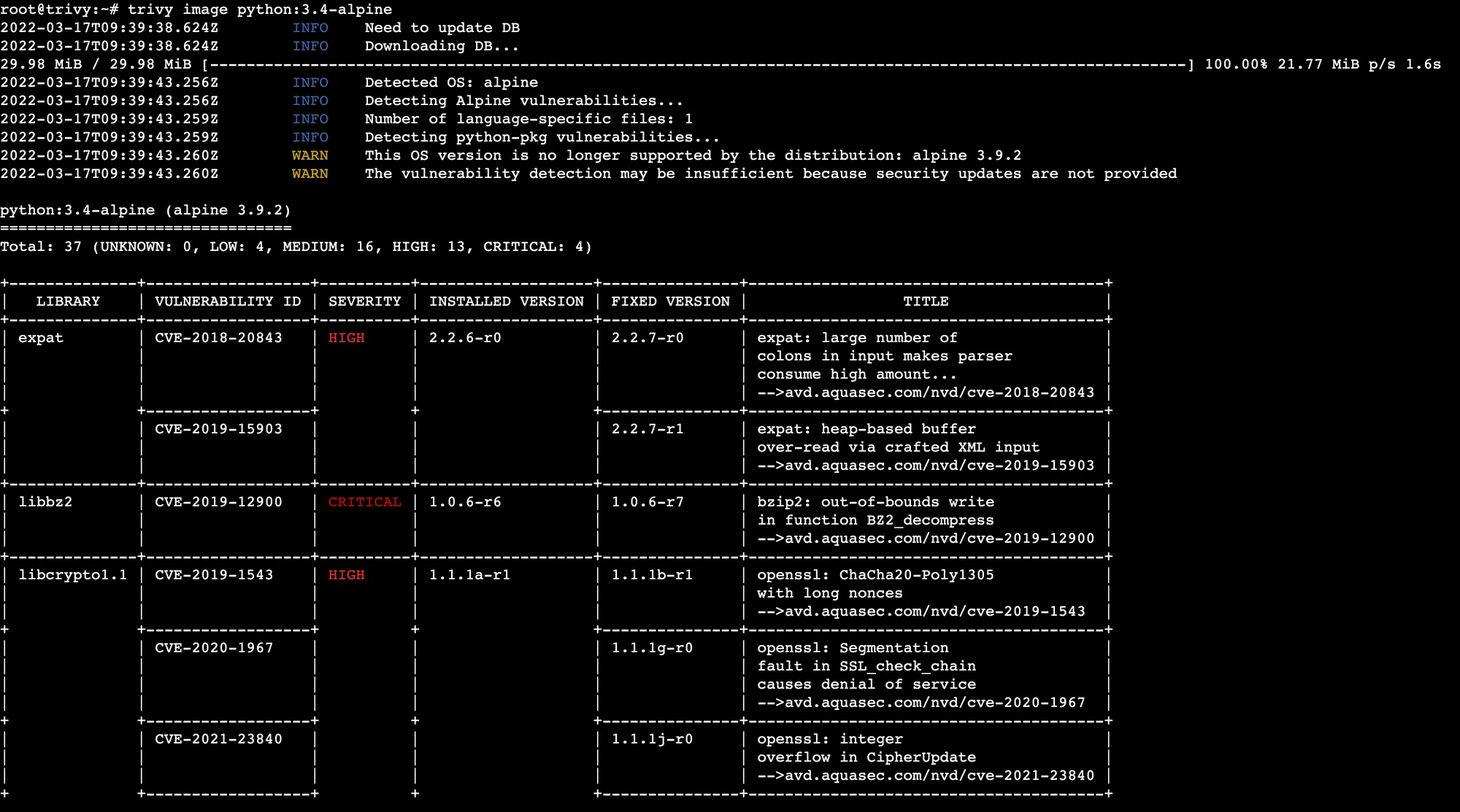
Where Trivy falls short: No runtime monitoring — it scans at a point in time. No attack path analysis or exploitability scoring. False positives on some language libraries where transitive dependencies are included.
Best fit: Any team that wants a single open-source tool covering image scanning, Kubernetes manifest checks, and SBOM generation. Trivy belongs in every CI/CD pipeline before container images are pushed to a registry.
2. Grype
Grype is an open-source vulnerability scanner from Anchore focused specifically on container images and SBOMs. It pairs naturally with Syft , Anchore’s SBOM generation tool, enabling a scan-against-SBOM workflow where you generate a bill of materials at build time and scan it independently.
What Grype does well: Fast, focused image scanning. SBOM-first workflow — generate a Syft SBOM once, then scan it repeatedly with Grype without re-pulling the image. Supports OCI, Docker, and legacy image formats. Integration with GitHub Actions and GitLab CI is straightforward.
Where Grype falls short: Narrower scope than Trivy — no Kubernetes manifest scanning, no IaC checks. Requires Syft as a companion for full SBOM workflows.
Best fit: Teams that already use Anchore Enterprise or prefer a dedicated image+SBOM scanner over a multi-purpose tool. Also a good choice for teams that need reproducible SBOM-based scanning where the same SBOM is scanned at multiple stages.
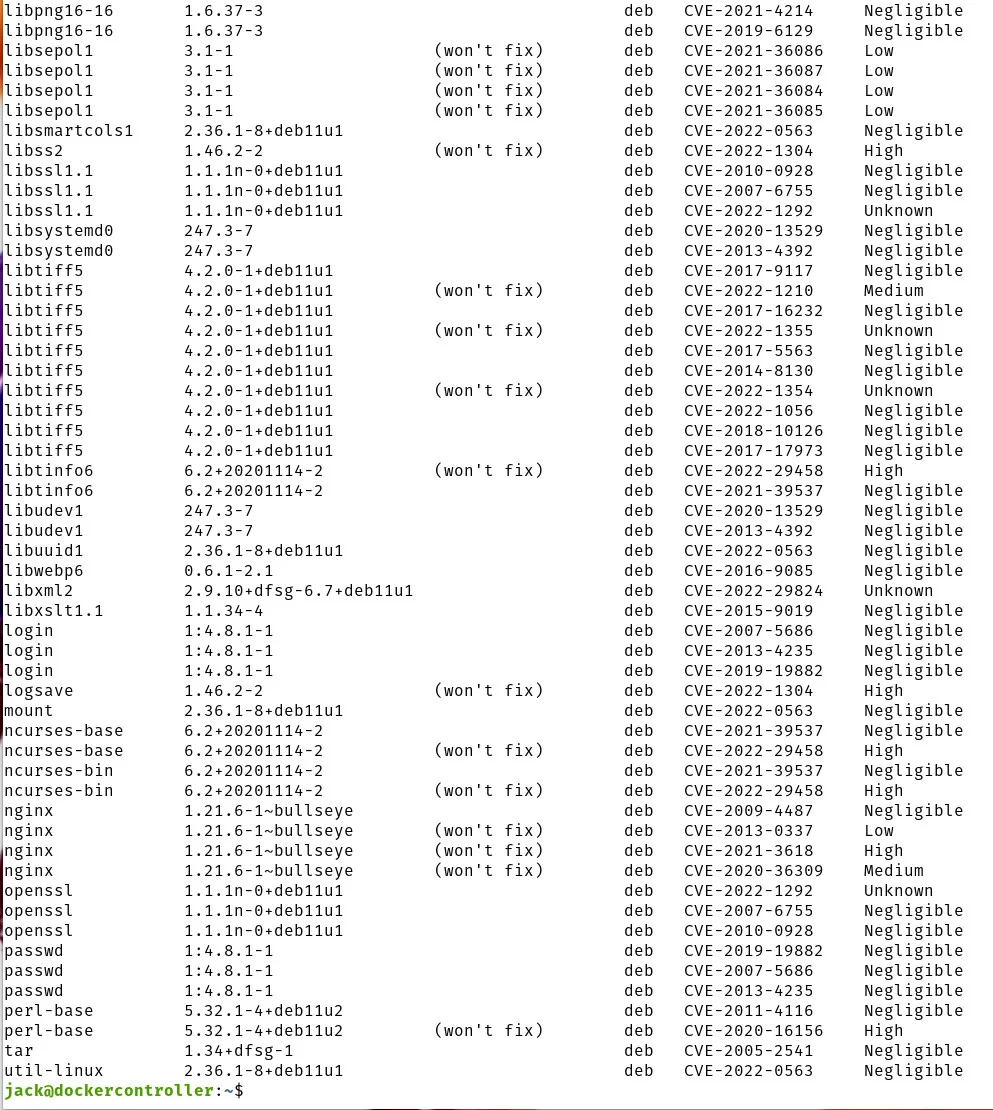
3. Clair
Clair is an open-source container image vulnerability scanner developed by Quay (now maintained by Red Hat). Unlike Trivy and Grype which are CLI-first tools, Clair v4 (ClairCore) is designed as a microservice that integrates directly with container registries.
What Clair does well: Registry-integrated scanning — images are scanned automatically when pushed to a Quay.io or self-hosted registry using Clair. Broad distribution support including Alpine, Debian, Ubuntu, RHEL, Oracle Linux, Amazon Linux, and SUSE. Efficient layered analysis avoids re-scanning identical layers across images.
Where Clair falls short: Designed for registry integration, not CI/CD pipeline scanning. Deploying Clair standalone requires running its PostgreSQL backend and API service — more operational overhead than a CLI scanner. No runtime monitoring, no Kubernetes manifest scanning.
Best fit: Teams operating a self-hosted container registry who want automated scanning integrated into the push workflow rather than a separate CI step.
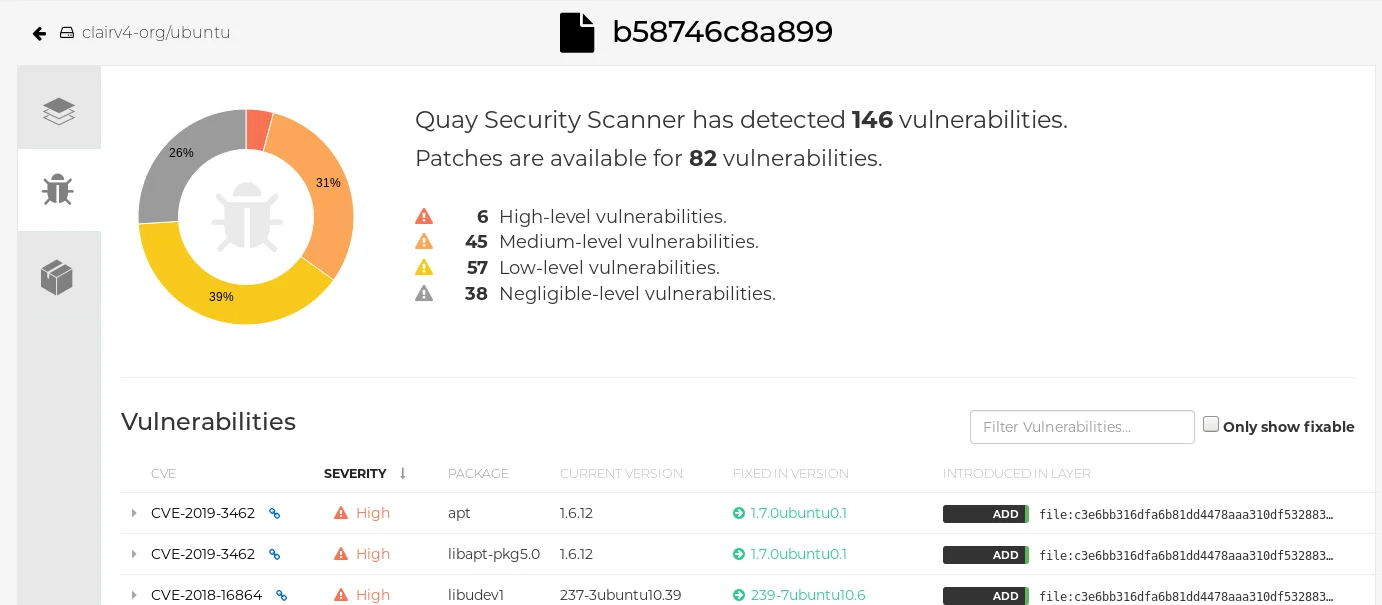
4. Docker Scout
Docker Scout is Docker’s integrated container security tool, available in Docker Desktop and via the Docker CLI. It provides image vulnerability scanning, SBOM analysis, and base image recommendations directly in the Docker workflow.
What Docker Scout does well: Zero-friction integration for Docker users — docker scout cves my-image:latest works from Docker Desktop or CLI without additional setup. Base image suggestions highlight when a less vulnerable base image is available. Policy evaluation flags images that violate defined vulnerability thresholds.
Where Docker Scout falls short: The free tier limits historical image analysis and policy enforcement. No runtime monitoring. No Kubernetes-native scanning. Tightly coupled to the Docker ecosystem.
Best fit: Teams that build images with Docker and want integrated vulnerability feedback in the local development loop before pushing to CI. Works well as a complementary tool alongside Trivy in CI/CD.
5. Falco
Falco is a CNCF graduated open-source runtime security project originally created by Sysdig. It monitors the Linux kernel via eBPF or a kernel module to detect anomalous behavior in running containers in real time.
What Falco does well: Runtime threat detection that image scanners cannot provide. Falco detects process spawning inside containers, privilege escalation via setuid, unexpected network connections, and container escape attempts. Pre-built rulesets map common attack techniques to MITRE ATT&CK
, and alerts include pod name, namespace, and deployment context for Kubernetes environments.

Where Falco falls short: Generates high alert volume on default rulesets — tuning rules to reduce noise requires effort. eBPF driver requires kernel 4.14+. No image scanning capability. Alert correlation and triage typically requires a SIEM or alerting platform.
Best fit: Any production Kubernetes environment where you need to detect active attacks and suspicious behavior that no image scan could have caught. Falco is the most mature open-source option for container runtime security. See the container image security guide for how image scanning and runtime monitoring complement each other.
6. Kube-bench
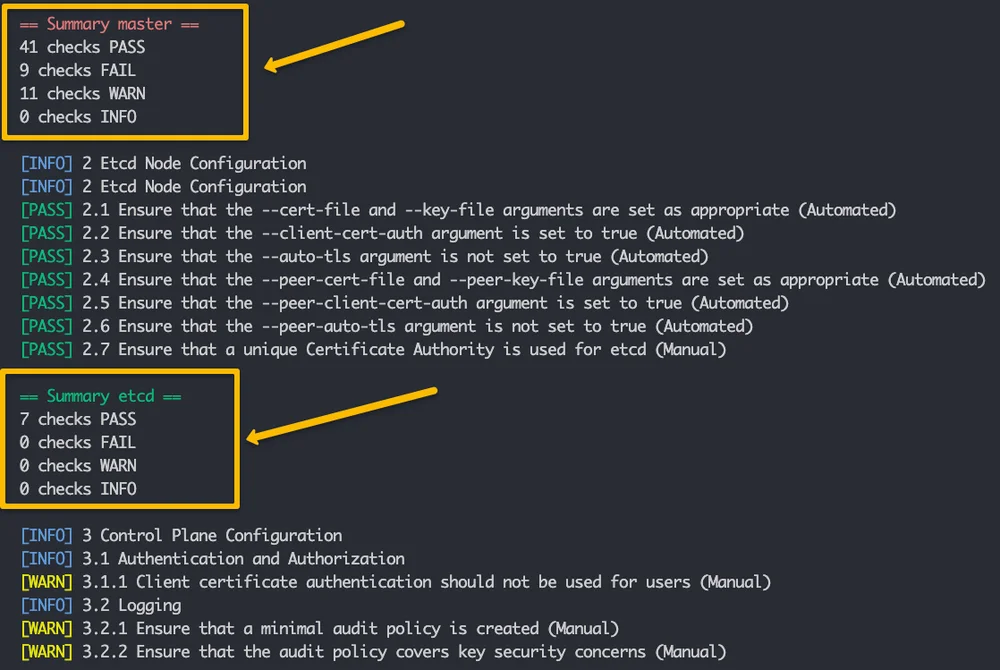
Kube-bench is an open-source tool from Aqua Security that checks Kubernetes cluster configuration against the CIS Kubernetes Benchmark . It audits the API server, controller manager, scheduler, etcd, and kubelet settings against the benchmark’s recommended values.
What Kube-bench does well: Comprehensive CIS benchmark coverage spanning Kubernetes 1.15 through 1.34, with auto-detection of cluster version. Detects common cluster misconfigurations — anonymous authentication enabled, insecure API server ports, audit logging disabled, kubelet read-only port open, and etcd without peer certificates. Runs as a Job inside the cluster or as a standalone CLI on master/worker nodes.
Where Kube-bench falls short: Checks cluster configuration only — no image scanning, no network policy analysis, no RBAC depth analysis. Produces a long checklist that requires Kubernetes expertise to interpret and remediate. Not a substitute for broader cluster security tools like Kubescape .
Best fit: Every new Kubernetes cluster provisioning and after every major upgrade. CIS Kubernetes Benchmark is the baseline compliance standard for managed Kubernetes services including EKS, GKE, and AKS. See Kubernetes security tools for broader cluster security coverage.
7. OpenSCAP
OpenSCAP is an open-source framework for automated security compliance checking using the Security Content Automation Protocol (SCAP). For containers, OpenSCAP scans container images against OVAL definitions and compliance profiles including CIS benchmarks, STIG (DoD Security Technical Implementation Guides), and PCI DSS profiles.
What OpenSCAP does well: Deep compliance mapping — not just CVE detection but configuration compliance against regulatory frameworks. STIG support makes it essential for US government and DoD environments. Red Hat integrates OpenSCAP into RHEL and Red Hat container images natively. Output in multiple formats including ARF, XCCDF, and HTML.
Where OpenSCAP falls short: Significant operational complexity compared to Trivy or Grype. Requires OVAL definitions and SCAP content, which must be kept current. Primarily Red Hat/RHEL ecosystem focused — less coverage for Alpine or Debian-based images. No runtime monitoring.
Best fit: Organizations with regulatory compliance requirements (STIG, DISA, PCI DSS) that need verifiable compliance reporting from container images. Common in US federal government and defense contractor environments.
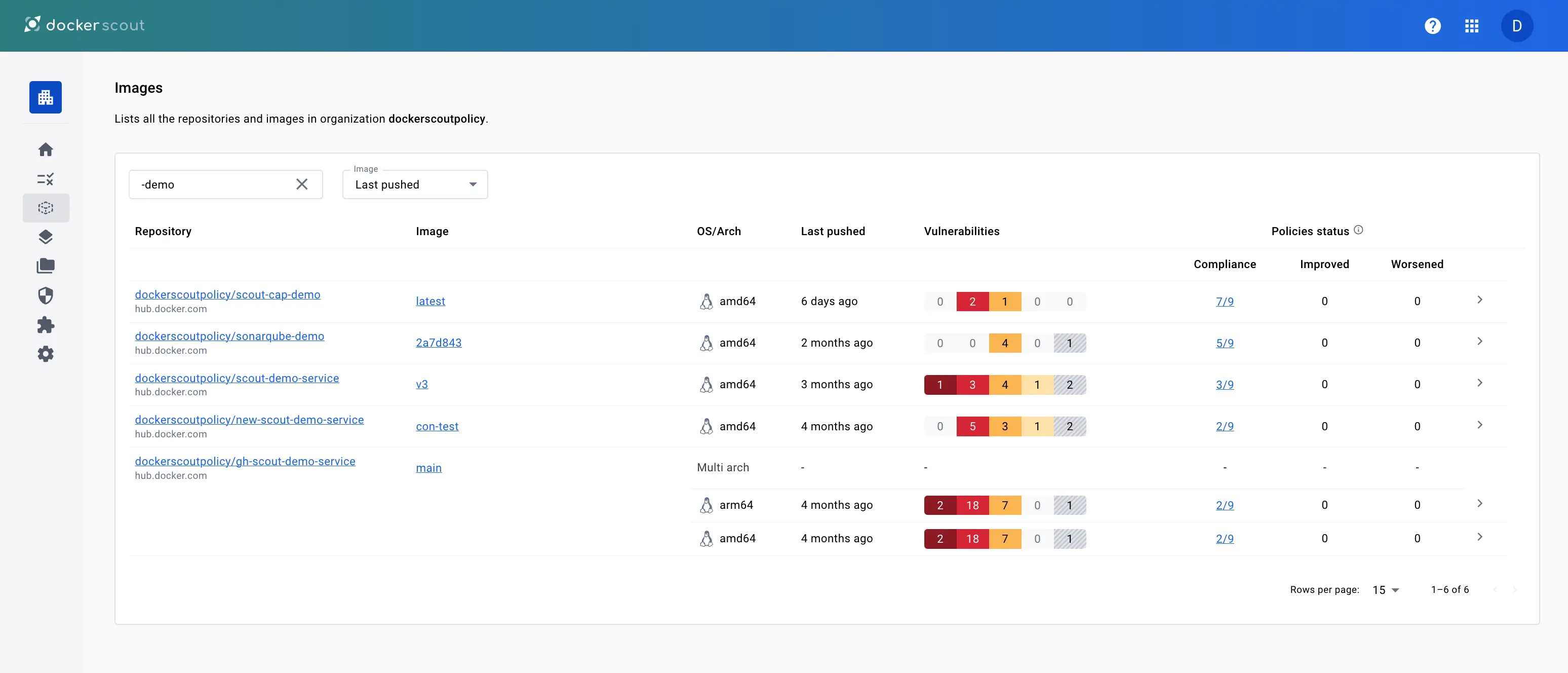
8. Dagda
Dagda is an open-source container security tool that combines static image analysis (CVE scanning) with runtime monitoring using Docker’s event stream. It stores findings in MongoDB and exposes a REST API for integration with other tools.
What Dagda does well: Combines image scanning and runtime monitoring in a single tool — a unique architectural choice among open-source options. Checks images against NVD CVE data and runs Docker event-stream monitoring for anomalies. The REST API enables integration into custom dashboards and security workflows.
Where Dagda falls short: Less actively maintained than Trivy, Falco, or Grype as of 2026. MongoDB dependency adds operational overhead. For teams that need separate best-of-breed tools, Trivy + Falco outperforms Dagda in both scanning depth and runtime detection capability.
Best fit: Teams that want a single integrated tool combining image scanning and container runtime monitoring and are comfortable with the MongoDB dependency. A practical alternative for environments where running two separate tools (Trivy + Falco) adds operational friction.
Comparison table
| Tool | Type | Image Scanning | Runtime Monitoring | Kubernetes | License |
|---|---|---|---|---|---|
| Trivy | All-in-one scanner | Yes (deep) | No | Yes (manifests, cluster) | Apache 2.0 |
| Grype | Image + SBOM scanner | Yes | No | No | Apache 2.0 |
| Clair | Registry scanner | Yes | No | No | Apache 2.0 |
| Docker Scout | Docker-integrated scanner | Yes | No | No | Commercial / Free tier |
| Falco | Runtime security | No | Yes (eBPF) | Yes | Apache 2.0 |
| Kube-bench | CIS benchmark checker | No | No | Yes (config audit) | Apache 2.0 |
| OpenSCAP | Compliance scanner | Yes (OVAL) | No | Limited | GNU LGPL |
| Dagda | Scanner + runtime | Yes | Yes (Docker events) | No | Apache 2.0 |
Scanning vs runtime: why you need both
Image scanning and runtime monitoring answer different questions. Trivy and Grype ask “does this image contain a known vulnerable package before it runs?” Falco asks “is something unexpected happening inside a running container right now?”
A container with a clean Trivy scan can still be compromised if your application code has a logic vulnerability, an attacker injects a malicious payload at runtime, or a supply chain compromise delivers a valid but backdoored image with no known CVEs.
Runtime monitoring catches container escapes, cryptomining processes, and lateral movement that happen in production and produce zero CVE findings. The container image security guide covers how these two layers interact and why admission control (blocking unsigned or policy-failing images via Kyverno or OPA Gatekeeper) bridges the gap.
CI/CD integration
Container security has four scan points: pre-commit (Dockerfile linting), CI on pull request (image build + Trivy or Grype scan), pre-deploy (admission control via Kyverno or OPA Gatekeeper), and runtime (Falco or KubeArmor watching the live cluster). Open-source tools cover all four cleanly, but most teams only wire up CI scanning at first.
A practical failure-policy pattern: warn on MEDIUM and below, block on HIGH with a fix available, ignore unfixable OS-level CVEs your app never calls. Tier the gates so build-breakers are exploitable findings only — chasing every MEDIUM is the fastest way to get scanners disabled by frustrated developers.
Trivy in GitHub Actions:
- name: Scan container image
uses: aquasecurity/trivy-action@master
with:
image-ref: "myimage:latest"
exit-code: "1"
severity: "CRITICAL,HIGH"
Grype in CI/CD:
grype myimage:latest --fail-on high
Falco deployment: Falco runs as a DaemonSet in Kubernetes — it is a runtime tool, not a CI/CD step. Deploy it via Helm: helm install falco falcosecurity/falco.
Kube-bench as a Kubernetes Job:
kubectl apply -f https://raw.githubusercontent.com/aquasecurity/kube-bench/main/job.yaml
For a complete DevSecOps pipeline covering SAST, SCA, secrets, and container scanning, see the DevSecOps implementation guide .
How to choose
Starting from scratch: Begin with Trivy in CI/CD and Falco in production. That combination covers image scanning before deployment and runtime threat detection after deployment. Add Kube-bench after cluster provisioning for CIS benchmark compliance.
Already using Docker Desktop: Docker Scout gives you local image feedback with no setup. Pair with Trivy in the CI pipeline for deeper CI scanning and Kubernetes manifest coverage.
Running a self-hosted registry: Clair is the natural choice for registry-integrated scanning, especially if you are using Quay.io or building a private Quay instance.
Regulatory compliance required (STIG, PCI DSS): OpenSCAP is the only open-source tool with STIG and DISA compliance profiles. It supplements Trivy for CVE detection with compliance framework alignment.
Commercial tool comparison: For teams evaluating commercial container security platforms alongside open-source options, see Aqua Security , Sysdig Secure , and the broader container security tools list. By use case (OSS-first stack with commercial pairings):
| Use case | Recommended OSS tool | Pair with (commercial) |
|---|---|---|
| Image scanning in CI | Trivy | Snyk Container |
| Runtime detection | Falco | Sysdig Secure |
| Kubernetes posture | Kubescape | StackRox / RHACS , Aqua Security |
| Network policy | Calico | Tigera Calico Cloud |
| CIS benchmark audit | Kube-bench | Aqua Security |
| Container registry | Harbor | Quay (Red Hat) |
OSS-only stacks work for small to medium clusters with strong in-house Kubernetes expertise. Add a commercial overlay (Aqua, Sysdig, Wiz) once you need cross-tool correlation, exploitability scoring, or a single audit-ready compliance pane. The transition point is usually 30+ engineers or the first compliance audit.
Tools shared with IaC Security and SCA
Five of the eight tools on this page also appear in other AppSec Santa hubs because their primary scope spans more than just containers. The mapping table below points each one to the canonical review.
| Tool | Where to find canonical |
|---|---|
| Trivy | IaC canonical, also widely used for container scanning |
| Falco | IaC canonical (runtime threat detection for Kubernetes) |
| Kubescape | IaC canonical (CNCF; cluster + manifest scanning) |
| KubeArmor | IaC canonical (LSM-based runtime security) |
| Anchore | SCA canonical (Anchore Enterprise covers container image scanning) |
These tools belong in this open-source container list because containers are one of their first-class targets. The cross-link tells you where the full review, changelog, and pricing notes live, and signals which AppSec Santa hub owns the head term for that tool. Grype is also tracked under SCA in some pages because it’s typically paired with Syft for SBOM-first workflows.






