22 Best Container Security Tools (2026)
Independent ranking — no vendor pays to appear here. See methodology.
Compare 20+ container security tools for 2026. Image scanning, Kubernetes security, and runtime threat detection. Open-source and commercial picks compared.
At a glance
The best container security tools in 2026: Trivy, Falco, Harbor, Kubescape, and Wiz.
- Best free image scanner: Trivy — open-source scanning across images, dependencies, IaC, and SBOMs
- Best runtime threat detection: Falco — CNCF-graduated, eBPF-based detection of malicious container behavior
- Best open-source registry with scanning: Harbor — CNCF registry with built-in scanning and image signing
- Best Kubernetes posture: Kubescape — scans clusters against the CIS and NSA Kubernetes benchmarks
- Best enterprise CNAPP: Wiz — agentless correlation of container, cloud, and Kubernetes risk
I evaluated 22 container security tools using publicly verifiable evidence — vendor docs, CNCF project status, and coverage across image scanning, runtime detection, and Kubernetes posture. No vendor paid to appear on this page.
What is Container Security?
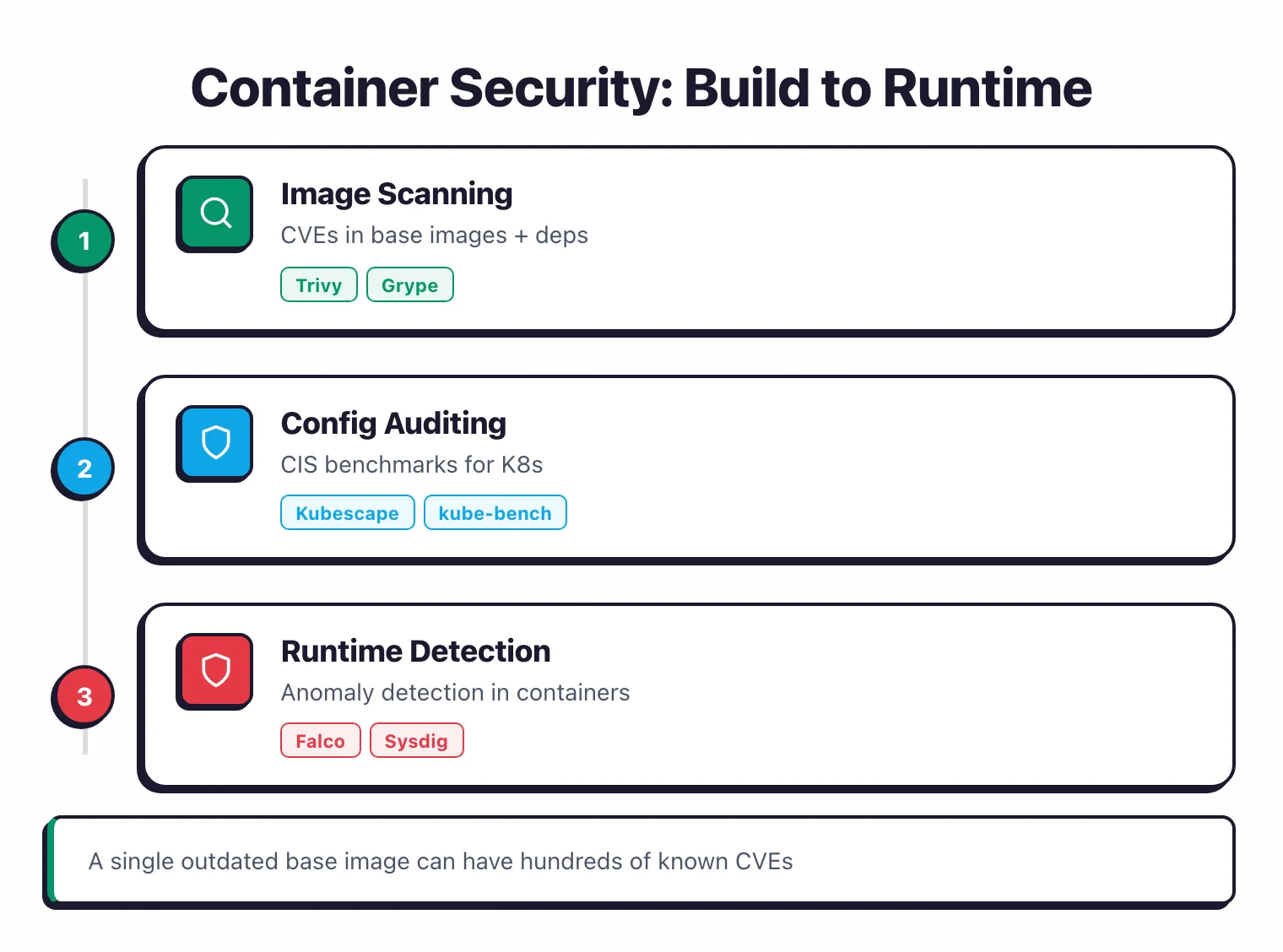
Container security is the branch of application security that protects containerized workloads from build to runtime. It covers three core pillars: scanning container images for known vulnerabilities before deployment, monitoring running containers for malicious behavior, and auditing Kubernetes cluster configurations against benchmarks like the CIS Kubernetes Benchmark.
The first pillar (image scanning) is dominated by Trivy , Grype , Snyk Container , and registry-side scanners in Harbor and ECR.
The second (runtime detection) is owned by Falco , Sysdig Secure , and CNAPPs like Wiz and Prisma Cloud that hook eBPF probes into kernel system calls. The third (Kubernetes posture) is handled by Kubescape , kube-bench, and OPA/Kyverno admission controllers.
Most teams need at least one tool from each pillar — image scanning catches known CVEs, runtime detection catches active exploitation, and posture management closes the configuration gaps in between.
The scale of the problem is significant. According to Sysdig’s 2023 Cloud-Native Security and Usage Report, 87% of container images contain high or critical vulnerabilities.
That same year, Sysdig’s 2023 Global Cloud Threat Report found that attackers go from initial reconnaissance to full compromise in an average of just 10 minutes.
These two data points explain why image scanning alone is not enough — you also need runtime detection fast enough to catch attacks in progress, and posture management to close the configuration gaps that make those attacks possible in the first place.
Key Insight
Image scanning catches known CVEs before deployment. Runtime detection catches zero-days, container escapes, lateral movement, and cryptominers. Neither layer is optional.
Trivy is the most popular open-source option with 34,000+ GitHub stars, covering images, K8s clusters, IaC, and SBOMs in a single binary. Trivy is canonical to my IaC security tools hub because it cross-covers Kubernetes manifest, Terraform, and CloudFormation scanning — but it earns its place in any container stack. For runtime detection, Falco (CNCF graduated, 8.7k+ stars) leads with eBPF-based kernel monitoring.
Enterprise teams needing full-lifecycle coverage should look at Aqua Security or Sysdig Secure .
Advantages
- Catches known vulnerabilities before deployment
- Detects attacks in running containers in real time
- Audits K8s clusters against CIS benchmarks
- Most tools are free and open-source
Limitations
- Image scanning only finds known CVEs
- Runtime tools add resource overhead to nodes
- Requires tuning to reduce alert fatigue
- Runtime detection needs privileged kernel access (eBPF or modules)
How does container image scanning work?
Image scanning is the build-side pillar. A scanner reads every layer of an OCI image, extracts the package manifest (apk, dpkg, rpm, language-specific lockfiles), and matches each package against vulnerability databases — NVD, GitHub Advisory Database, and distro feeds like Alpine secdb or Debian DSA.
The scanner reports CVE IDs, severity, fixed versions, and (in newer scanners) reachability to call paths. The same engine usually flags embedded secrets, license issues, and known malware hashes.
Scanners run at three points: in CI before push, on the registry when an image lands, and during admission to a cluster. Most teams run them in CI at minimum because that is where a developer can still fix things cheaply.
| Tool | Scope | License | Best for |
|---|---|---|---|
| Trivy | Image, IaC, K8s, SBOM | Apache 2.0 | All-in-one CI scan; my default |
| Grype | Image + SBOM | Apache 2.0 | SBOM-first workflows; pairs with Syft |
| Docker Scout | Image | Free + paid | Built into Docker Desktop |
| Clair | Image (registry-side) | Apache 2.0 | Self-hosted Quay registries |
| Snyk Container | Image, base-image fixes | Commercial | Developer-first, IDE feedback |
| Anchore | Image, SBOM, policy | Apache 2.0 / Commercial | Anchore is the SCA canonical; container scanning is a side use |
I use Trivy as the default scanner because it scans images, Kubernetes manifests, IaC files, and SBOMs from a single binary with no database setup. Snyk Container wins when developers need fix advice in their IDE; Docker Scout wins when teams have not yet adopted a separate scanner. The honest gap across all open-source scanners: they tell you which CVEs exist, not which are reachable from your code path.
What is Kubernetes posture management and admission control?
Kubernetes posture management answers a different question than image scanning: is this cluster configured the way it should be? Posture tools audit the API server flags, kubelet settings, RBAC roles, network policies, and pod security context against benchmarks like CIS Kubernetes Benchmark, NSA-CISA Kubernetes Hardening Guidance, and MITRE ATT&CK for Containers.
Admission control is the enforcement layer. When a workload is submitted to the cluster, validating and mutating webhooks intercept the request and approve, modify, or reject it based on policy. This is how you prevent privileged containers from being scheduled in the first place.
Pod Security Standards define three baselines — Privileged (no restrictions), Baseline (block obvious escalations), and Restricted (production-grade hardening). The Restricted profile enforces non-root containers, read-only root filesystems, no host namespace sharing, dropped capabilities, and seccomp profiles.
The dominant tools split by job:
- Posture audit — Kubescape
(CNCF; CIS + NSA-CISA + MITRE), kube-bench
(CIS-only, focused), Trivy
trivy k8smode. - Admission policy — OPA Gatekeeper (Rego policies, mature), Kyverno (Kubernetes-native YAML, simpler authoring), Polaris (read-only audit).
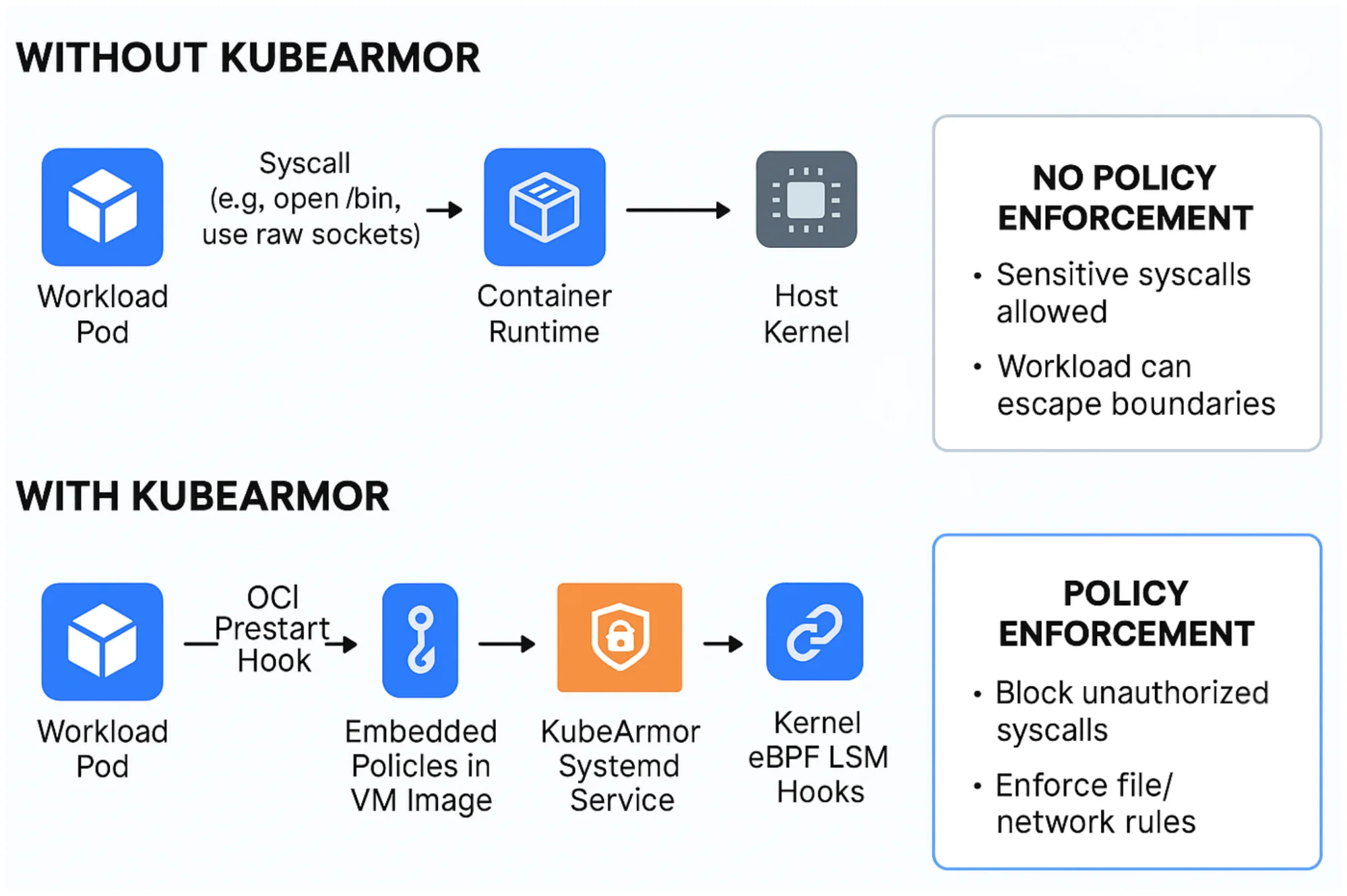
- Runtime enforcement on top — KubeArmor (LSM-based, blocks at kernel) extends admission with continuous in-pod enforcement.
kubernetes admission controller and kubernetes security best practices searches converge on these tools. For deeper coverage of admission policy specifically, the canonical page is /opa-gatekeeper
. Posture without admission catches drift; admission without posture leaves you blind to what was already running. Most production clusters need both layers.
How Does Runtime Threat Detection Work?
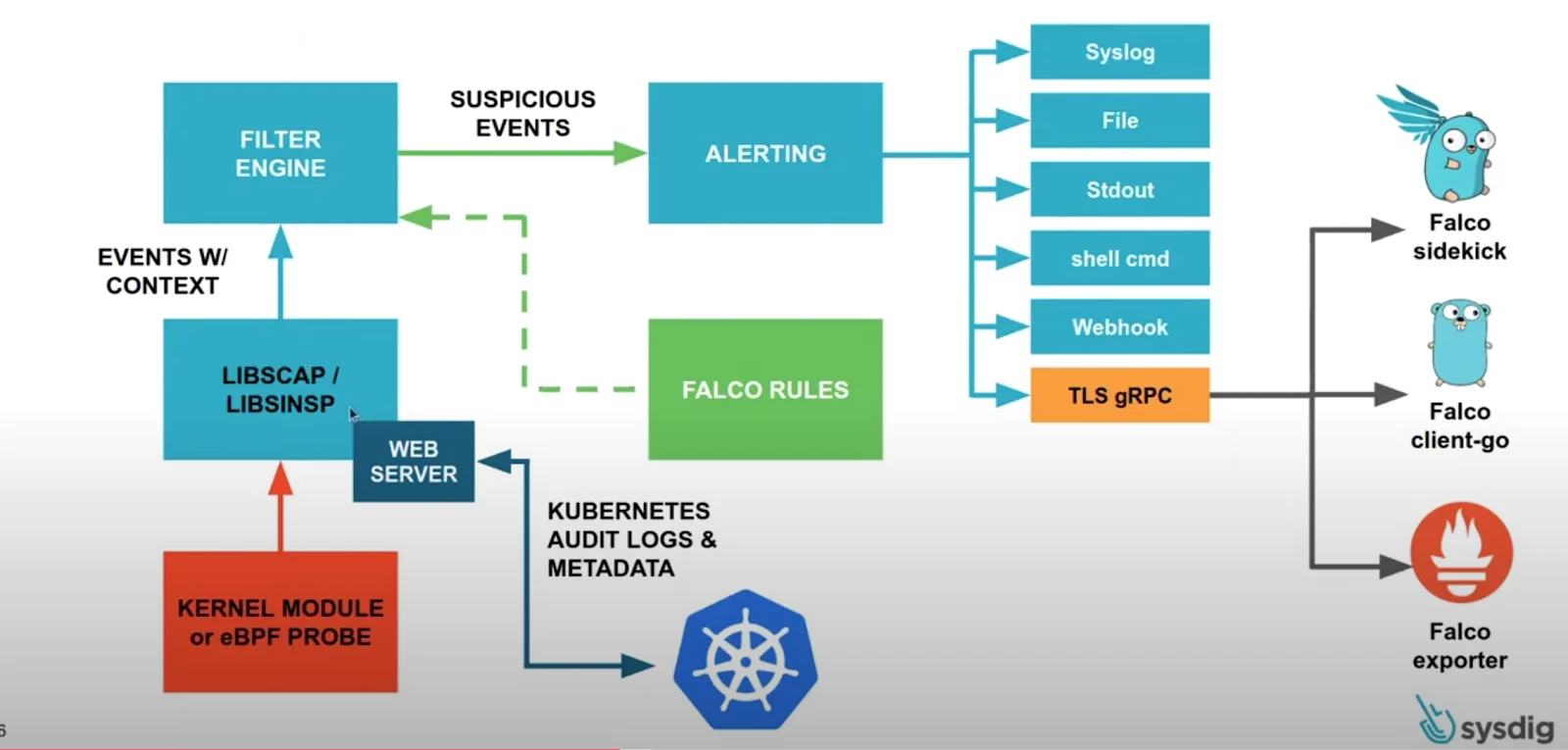
Runtime threat detection monitors the behavior of running containers in real time and fires alerts when activity deviates from expected patterns.
Unlike image scanning, which finds known CVEs before deployment, runtime detection catches zero-day exploits, container escapes, lateral movement, and cryptominers that no scanner would have flagged.
It watches system calls, file access, network connections, and process execution — the actual behavior inside the container, not just the packages it was built from.
Most runtime detection tools rely on eBPF (extended Berkeley Packet Filter) to hook into the Linux kernel without modifying the application or loading kernel modules. The performance cost is lower than you’d expect.
Well-tuned setups with Tetragon or Falco typically add 1-3% CPU overhead, though that climbs with more rules and higher event volume.
Speed matters here because attackers move fast. Sysdig’s 2023 Global Cloud Threat Report found that the average time from reconnaissance to full compromise is about 10 minutes.
Detection has to be faster than that window. Tools like Falco and KubeArmor process kernel events in near real-time, giving security teams the millisecond-level visibility needed to catch threats before attackers achieve their objectives.
| Tool | License | Detection Method | K8s Native | Policy Engine |
|---|---|---|---|---|
| Falco | Open Source | eBPF kernel-level syscall monitoring | ✓ | YAML rules |
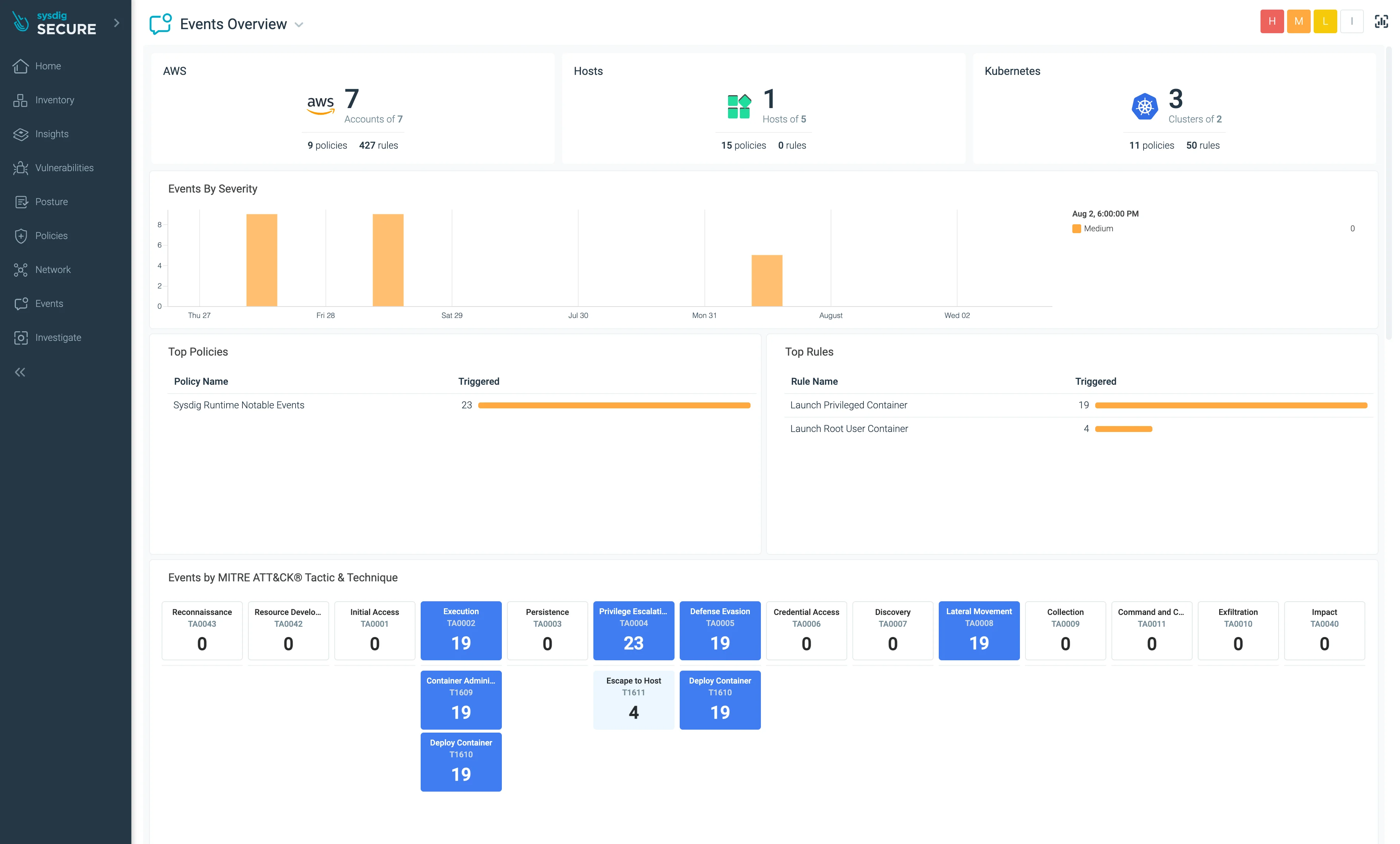
| Sysdig Secure | Commercial | Falco-powered + AI analyst (Sysdig Sage) | ✓ | OPA + Falco |
| KubeArmor | Open Source | eBPF + LSM (AppArmor/BPF LSM/SELinux) | ✓ | K8s CRDs |
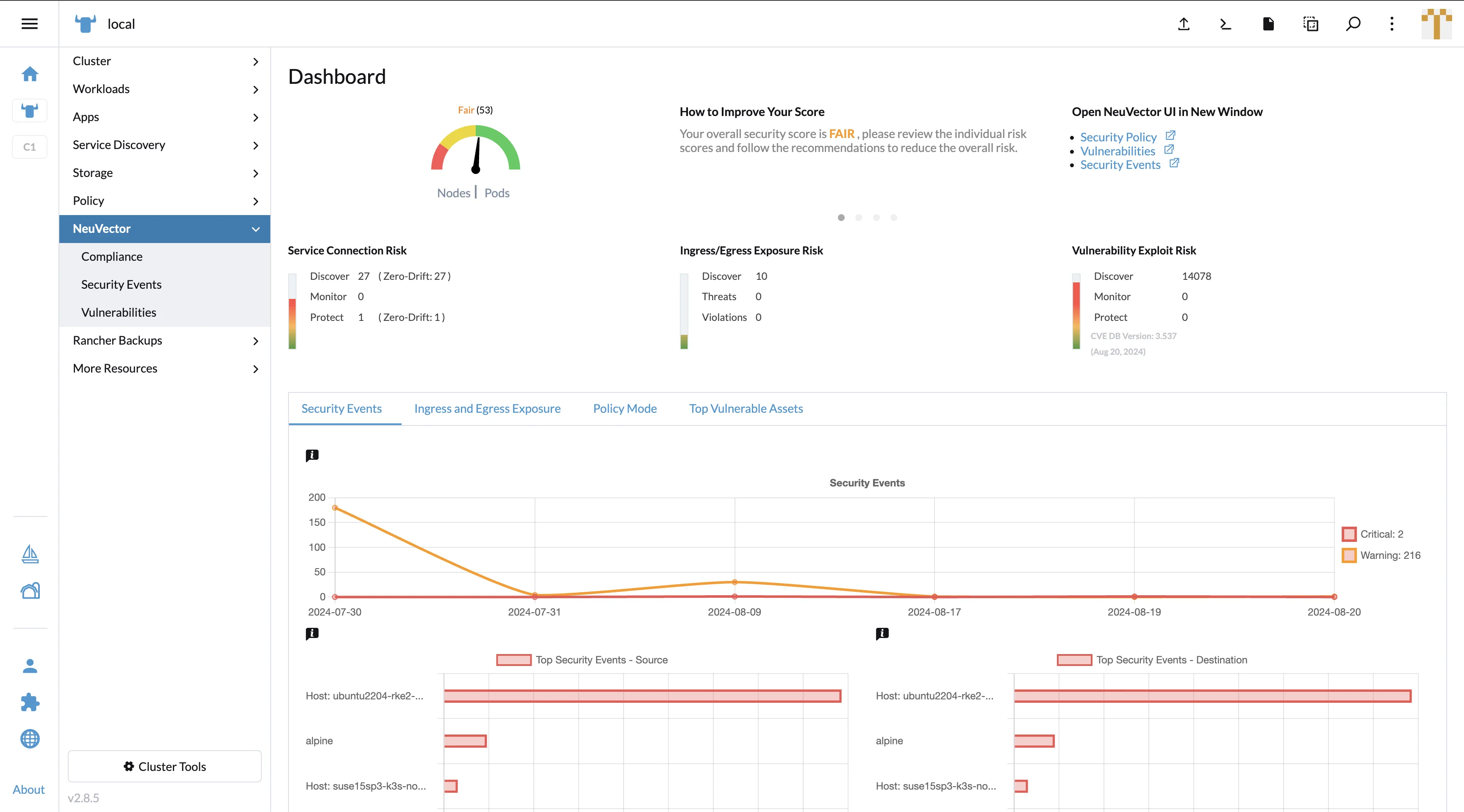
| NeuVector | Open Source | Deep packet inspection + behavioral learning | ✓ | Zero Trust |
Here is what each runtime detection tool looks like in production:
How to Choose a Container Security Tool
For Image Scanning: Trivy or Docker Scout
Start here. Trivy is the best free option for CI/CD image scanning, and it also covers IaC, secrets, and SBOMs. If you're already deep in the Docker ecosystem, Docker Scout is built right into Docker Desktop and CLI, so there's nothing extra to install.
For K8s Compliance: Kubescape or kube-bench
Kubescape is the broader tool here: CIS, NSA-CISA, and MITRE ATT&CK frameworks, plus image scanning built in. kube-bench does one thing well: CIS Kubernetes Benchmark checks for control plane, worker nodes, and etcd. Pick based on how much scope you need.
For Enterprise Full-Lifecycle: Aqua Security or Sysdig
Want one platform for build, deploy, and runtime? Aqua Security (the company behind Trivy) and Sysdig Secure (powered by Falco) both cover the full lifecycle with compliance automation, investigation tooling, and multi-cloud support.
Best container security tool by use case
I keep getting asked “which tool is best?” without a use case. Use case changes the answer. The matrix below mirrors the segmentation Wiz Academy uses, with my picks:
| Use case | Free / OSS | Commercial overlay |
|---|---|---|
| Image scanning in CI | Trivy | Snyk Container |
| Runtime threat detection | Falco | Sysdig Secure |
| Kubernetes posture | Kubescape | Aqua Security |
| Runtime enforcement (block) | KubeArmor | Aqua Security |
| Network policy + zero trust | Calico , Cilium | Tigera Calico Cloud |
| CIS benchmark audit | kube-bench | Aqua Security |
| Container registry | Harbor | Quay (Red Hat), JFrog |
| Enterprise CNAPP | — | Wiz , Prisma Cloud , Sysdig Secure |
| Hardened base images | Wolfi (Chainguard images) | Echo, RapidFort, Chainguard |
The free column is enough for most teams under 50 engineers. The commercial column starts to matter once you cross multi-cloud, regulated industries, or enough findings that triage becomes a full-time role.
CI/CD integration: where to scan in the pipeline
There are four points in a delivery pipeline where container security tools attach. Pick at least two — the rest are free wins.
- Pre-commit / IDE. Developer-side feedback. Snyk Container, Docker Scout, and IDE Trivy plugins flag obvious CVEs before code lands in a PR.
- CI on PR. This is the load-bearing layer. Trivy or Grype scans the freshly built image; the build fails on configurable severity thresholds. Most teams gate on
CRITICAL,HIGHwith a reachability or fix-available filter. - Pre-deploy / admission. OPA Gatekeeper or Kyverno reject images that did not pass the CI gate or are not signed with Cosign .
- Runtime. Falco, KubeArmor, or Sysdig Secure watches what actually happens after deploy.
A common failure pattern: teams configure CI to fail on every HIGH finding, drown in noise, and disable the gate within a sprint. The fix is policy tiering — block on findings with both an exploit and a fix, warn on HIGH without an exploit, ignore OS-level CVEs the application never calls. Reddit’s r/kubernetes thread on Trivy alert fatigue is the clearest write-up I have seen on this.
For full pipeline patterns including SAST, SCA, and secrets, see the DevSecOps implementation guide .
Container security by deployment target
Tooling choices are not universal — they depend on where containers run.
- Kubernetes (self-managed or managed) — the dominant scope. Trivy + Falco + Kubescape cover image, runtime, and posture. Add KubeArmor or Cilium for enforcement. CIS benchmarks via kube-bench .
- Managed Kubernetes (EKS, GKE, AKS) — managed control plane limits some scanners. EKS pairs naturally with AWS GuardDuty + Trivy + Falco; GKE with Google Container Threat Detection + Kubescape; AKS with Microsoft Defender for Containers + Trivy. The Kubernetes security tools page breaks this down by distro.
- Serverless containers (EKS Fargate, GKE Autopilot, AWS App Runner, Cloud Run) — no on-cluster DaemonSet. You scan images in CI and rely on cloud-side detection. KubeArmor and Falco lose most of their footing on Fargate-style runtimes.
- Docker Compose / single-host Docker — Docker Scout for image feedback, Trivy in CI, host-level auditd or osquery instead of K8s-aware runtime tools.
- HashiCorp Nomad — Trivy in CI, Falco at the host level, Cosign for image signing. Nomad does not have admission webhooks, so policy enforcement is manual.
- Cloud Run / ECS Fargate — image scan in CI is the primary gate. Add cloud-native posture (AWS Inspector, GCP Container Threat Detection) for runtime visibility.
Match your stack first, then pick from each layer the matching tool.
Container security by lifecycle stage: build → registry → runtime
A simpler way to choose tools: walk the image’s life from Dockerfile to running pod and pick one tool per stage.
- Build — Dockerfile linting (Hadolint), base-image selection (Wolfi, Distroless, Chainguard), in-build scanning (Trivy or Grype), and SBOM generation (Syft, Trivy
--format spdx). - Registry — registry-side scanning (Harbor with Trivy, Quay with Clair, ECR with native Inspector), image signing with Cosign, and replication policies that block unsigned tags.
- Admission — OPA Gatekeeper or Kyverno enforce “no unscanned image, no unsigned image, no privileged pod, no host-network pod” at the API server.
- Runtime — Falco or KubeArmor for kernel-event detection, Calico or Cilium for network policy, NeuVector for deep packet inspection.
- Response — Falcosidekick or Sysdig Secure for alert routing; SOAR integrations for automated isolation.
Each stage has at least one mature open-source option. The shortest viable path: Trivy in build, Cosign signing on push, Gatekeeper on admission, Falco at runtime. That covers ~80% of real attack patterns documented by the CNCF Cloud Native Security Whitepaper .
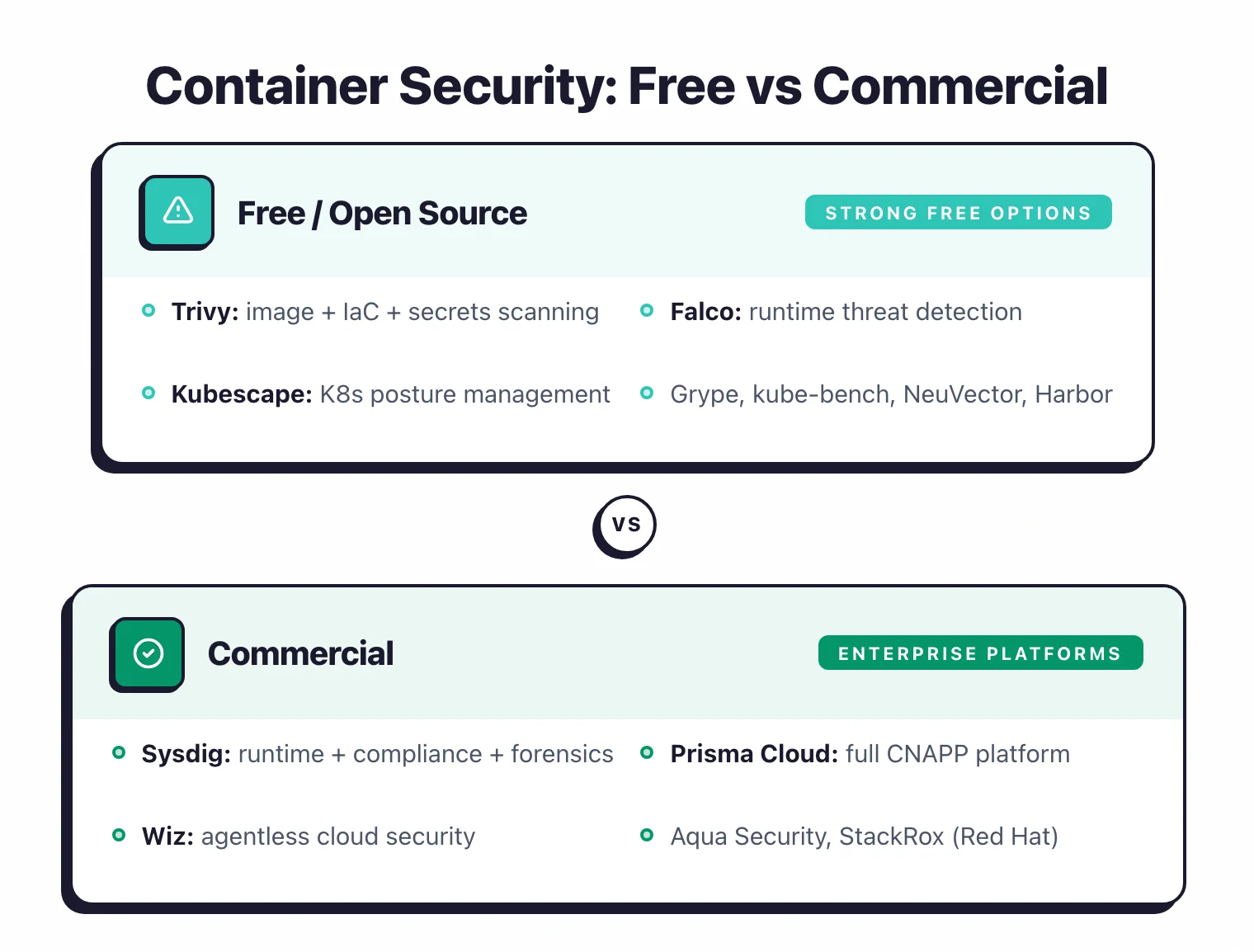
Free vs commercial container security: when paid wins
Open-source tools cover most container security needs at zero license cost. Commercial platforms still earn budget in three concrete situations.
The free stack works when:
- Scope is one or two clusters in one cloud account.
- Engineering team can self-host Falco, Kubescape, and a SIEM for alert routing.
- Compliance is internal or basic SOC 2 Type 1 — no FedRAMP, no STIG, no PCI-DSS audit trail mandates.
- Findings volume is manageable manually (under ~200 active CVEs per scan).
Commercial wins when:
- Multi-cloud scope (AWS + Azure + GCP). Wiz , Prisma Cloud , Sysdig Secure , and Aqua Security consolidate findings across accounts with a single dashboard.
- Reachability + exploitability prioritization. Sysdig Secure runtime context cuts CVE noise dramatically because it knows which packages are actually loaded in memory. Open-source scanners report every CVE in every layer.
- Audit-ready compliance reporting (PCI-DSS, HIPAA, FedRAMP). Commercial CNAPPs ship pre-mapped controls; open-source forces you to build the mapping.
- Hardened base images at scale. Chainguard, Echo, and RapidFort sell CVE-free base images that eliminate findings rather than report them.
I have not seen a team migrate from a working open-source stack to a commercial CNAPP without one of those four triggers. If none of them apply, the open-source stack is the right answer.
Container security vs CNAPP: when to upgrade
Container security covers the container layer — image scanning, runtime detection, Kubernetes posture. CNAPP — Cloud-Native Application Protection Platform — wraps container security inside cloud-account scope with CSPM, CIEM, attack-path graphs, and multi-cloud asset inventory.
The honest answer: container security is enough for one cluster in one cloud. CNAPP starts to pay back when scope grows.
Stay with container security tools when:
- One Kubernetes cluster, one cloud, one team.
- Scope ends at the pod boundary — IAM, S3, and serverless functions are out of scope.
- Budget < $20k/year — the free stack does the job.
Upgrade to CNAPP when:
- Multi-cloud or 10+ accounts. Asset discovery alone takes a CSPM tool.
- Attack-path correlation matters. CNAPP graphs container findings together with IAM, public S3 buckets, and exposed VMs to compute the actual blast radius.
- Compliance scope crosses container boundaries (CIS AWS, ISO 27001, SOC 2 Type 2).
The dominant CNAPP vendors with strong container security: Wiz , Prisma Cloud , Sysdig Secure , Aqua Security , and Orca Security . Each ships container scanning and runtime detection inside a broader cloud security platform.
Tools shared with IaC Security and SCA
Some tools below appear in my IaC Security or SCA hubs as their primary category — that is because they cross multiple boundaries. The container space inherits Trivy, Falco, Kubescape, KubeArmor, and Anchore from those hubs, and listing them here without disclosure would cannibalize the canonical pages. Here is how I split them:
| Tool | Container-security role | Primary canonical |
|---|---|---|
| Trivy | Image, IaC, K8s manifest, SBOM scanner | /iac-security-tools — IaC canonical (covers Terraform, CloudFormation, K8s manifests) |
| Falco | Runtime threat detection (eBPF) | /iac-security-tools — IaC canonical (CNCF graduated runtime project) |
| Kubescape | K8s posture + image scan | /iac-security-tools — IaC canonical (CIS, NSA-CISA, MITRE) |
| KubeArmor | LSM-based runtime enforcement | /iac-security-tools — IaC canonical |
| Anchore | Image scan + policy engine | /sca-tools — SCA canonical (Anchore Enterprise primarily SCA-shaped) |
When a tool spans disciplines, the canonical lives where its primary search demand lives. Trivy’s biggest non-brand search cluster is IaC scanning, so the IaC hub owns the brand keyword; Anchore’s enterprise product is SBOM/policy-shaped, so SCA owns it. Container security still mentions and links them — but the ranking weight stays at the canonical hub.
Common container image misconfigurations
Most container security incidents come from a small set of misconfigurations that scanners flag every time. Here are the ones I see most often during audits:
- Running as root. No
USERdirective in the Dockerfile, so the entrypoint runs as UID 0. A container escape gives an attacker root on the node. - Privileged containers.
securityContext.privileged: truedisables most Linux namespaces and capability restrictions. Required for some host-network workloads, dangerous everywhere else. - Host namespace sharing.
hostNetwork,hostPID,hostIPCset totruelets a compromised pod observe and interact with the host’s network stack and process tree. - Latest tags in production. Pulling
nginx:latestmakes the running version unpredictable and breaks supply-chain integrity. Pin to immutable digests. - Embedded secrets. AWS keys, API tokens, or
.envfiles baked into the image at build time. Trivy and Grype flag the well-known patterns; review every COPY/ADD step. - Outdated base images. Building from
ubuntu:18.04in 2026 ships hundreds of EOL OS CVEs. Distroless or Wolfi images cut this surface drastically. - Capabilities not dropped. By default a container inherits Linux capabilities like
NET_RAWandSYS_ADMIN. Pod Security Standards Restricted profile drops them. - Read-write root filesystem. Without
readOnlyRootFilesystem: true, an attacker who lands in the container can write malware to disk and persist.
The CIS Docker Benchmark and CIS Kubernetes Benchmark codify all eight. Tools like kube-bench
, Kubescape, and Trivy config mode flag them on every scan.
How I evaluated 22 container security tools
This page is a hub, not a vendor-sponsored list. To produce the recommendations above, I worked through every active tool in the table, reviewed vendor documentation, GitHub repositories, and public benchmark publications, and cross-checked the findings against practitioner reports. Here is what went into the analysis:
- Image-scanning capabilities. For each scanner I reviewed the documented CVE database sources, supported image formats, scan-time benchmarks published by the vendor, and false-positive behavior reported in independent comparisons.
- Runtime detection coverage. Falco, KubeArmor, NeuVector, and Sysdig Secure were assessed by reading their detection-rule documentation, eBPF/kernel-module integration model, and runtime threat-detection categories (cryptomining, container escape, lateral movement, C2). I did not run live exploits against a private cluster.
- Posture audit coverage. Kubescape, kube-bench, and Trivy
k8smode were evaluated against their published benchmark coverage (CIS Kubernetes Benchmark, NSA-CISA, MITRE ATT&CK for Containers) using the vendor changelog and rule-pack release notes. - Documentation parity. Every fact, GitHub-star count, and feature claim was checked against the vendor’s official documentation or the project’s README at the time of writing. Numbers are recorded with their source so they can be re-verified.
- What I do not claim. I do not publish detection numbers from a private cluster I run, and I do not test paid-tier features without vendor cooperation. Anything labeled “best for X” reflects documented capability plus practitioner-reported behavior, not a hands-on red-team evaluation.
When data goes stale — Trivy releases new DBs roughly weekly, Falco rules ship monthly, CNCF projects graduate or archive — I update this page and the linked tool pages and refresh the updated date. The current revision is dated at the top of this page.
Frequently Asked Questions
What is container security?
What is the best free container security tool?
How do I scan Docker images for vulnerabilities?
What is the difference between image scanning and runtime security?
Do I need container security if I use Kubernetes?
What is container runtime threat detection?
What is the difference between container security and CNAPP?
Is Trivy free?
What are the 4 C's of Kubernetes security?
Related Container Security Resources
Explore Other Categories
Container Security covers one aspect of application security tools. Browse other categories below.

Written & maintained by
Suphi CankurtEight years on the vendor side of application-security sales — thousands of evaluations and demos. I started AppSec Santa in 2022 to put that insider view to work for buyers. Independent of any vendor, paid by none, and honest about what fits whom.