Cisco DefenseClaw is an open-source security governance framework for agentic AI systems that enforces a strict principle: nothing runs until it has been scanned, and anything dangerous is blocked automatically.
While MCP-Scan focuses specifically on MCP server vulnerability scanning, DefenseClaw provides a broader governance layer that adds skill scanning, static code analysis, runtime inspection, and sandbox isolation.
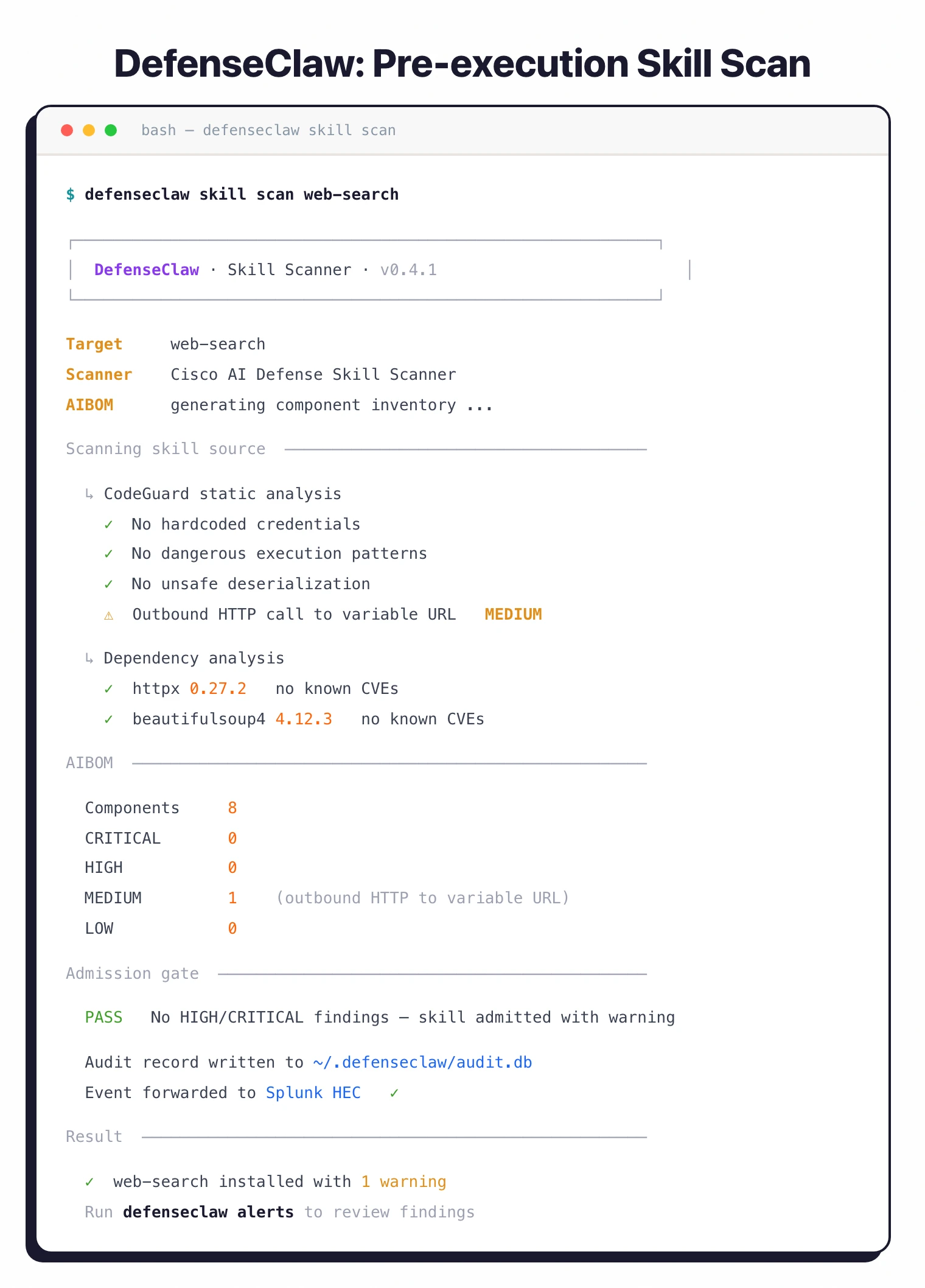
Released at RSA 2026 by Cisco AI Defense, DefenseClaw provides pre-execution scanning of AI agent skills and MCP servers, static code analysis, runtime inspection of LLM interactions, and enterprise-grade audit logging.
The framework serves as a governance layer for OpenClaw, an open-source AI agent framework, but its scanning components work independently.
The project is part of Cisco’s broader AI Defense portfolio, which addresses security across the AI application lifecycle from development through deployment.
What is Cisco DefenseClaw?
As AI agents gain the ability to execute code, call external APIs, and interact with production systems, the attack surface expands dramatically. A compromised agent skill can exfiltrate data, a poisoned MCP server can hijack agent behavior, and insecure code patterns can introduce vulnerabilities that traditional security tools miss.
DefenseClaw addresses this by inserting a mandatory security gate between AI components and execution. Every skill, MCP server, and code artifact is scanned before it runs.
Runtime interactions between agents and LLMs are inspected for secrets, PII, and injection patterns. All decisions are logged to an immutable audit store.
Key Features
| Feature | Details |
|---|---|
| Skill Scanner | Pre-execution analysis of AI agent skills |
| MCP Scanner | Vulnerability scanning for MCP servers |
| AIBOM | AI Bill of Materials with severity-ranked findings |
| CodeGuard | Static analysis for credentials, injection, unsafe patterns |
| Message Inspection | Prompt/completion scanning for secrets, PII, injection |
| Tool Inspection | Six categories: secrets, commands, paths, C2, tampering, injection |
| Sandbox Mode | OS-level isolation with Landlock LSM and seccomp-BPF |
| Policy Enforcement | Go gateway with REST API and WebSocket bridging |
| Audit Logging | SQLite store with full decision history |
| SIEM Integration | Splunk HEC real-time event forwarding |
| Observability | OTLP export (logs, spans, metrics) to Jaeger, Grafana, Datadog |
| Build System | make build (all), make pycli, make gateway, make plugin |
| Cross-compile | make gateway-cross GOOS=linux GOARCH=arm64 (DGX Spark) |
| Requirements | Python 3.10+, Go 1.25+, Node.js 20+ (plugin only) |
| License | Apache 2.0 |
Three-tier architecture
DefenseClaw consists of three integrated components working together:
The Python CLI is the operator-facing tool for scanning and policy management. Security teams use it to run Skill Scanner, MCP Scanner, and CodeGuard against their AI components.
The Go Gateway is the central daemon that handles REST API requests, WebSocket bridging, policy enforcement, and audit logging.
Every security decision flows through the gateway, which writes to a SQLite audit store and can forward events to Splunk HEC or OTLP-compatible collectors in real time.
The TypeScript Plugin runs inside the OpenClaw agent framework, intercepting tool calls via hooks. When an agent attempts to use a tool, the plugin routes the request through the gateway for policy evaluation before allowing execution.
Sandbox isolation
For high-risk operations, DefenseClaw provides OS-level sandboxing using Landlock LSM (Linux Security Module) for filesystem access control and seccomp-BPF for system call filtering. This creates a restricted execution environment where agent skills can only access explicitly permitted resources — even if the skill itself is compromised.
Enterprise observability
All security decisions flow through the Go gateway and are written to a SQLite audit store.
For enterprise environments, DefenseClaw can forward events to Splunk HEC in real time for SIEM integration, or export logs, spans, and metrics via OTLP to collectors like Jaeger, Grafana, or Datadog. This means every scan result, runtime inspection outcome, and policy enforcement decision is captured in your existing observability stack.
LLM guardrail proxy
DefenseClaw includes a built-in guardrail proxy that inspects all LLM traffic in real time, operating independently of plugin installation. The proxy runs in two modes: observe mode logs findings without blocking, while action mode actively blocks flagged prompts and responses. Severity thresholds are configurable in ~/.defenseclaw/config.yaml.
Tool inspection categories
The runtime tool inspection engine evaluates six specific threat categories: secret (API keys in arguments), command (shell commands like curl/wget/nc), sensitive-path (system files), c2 (command-and-control hostnames), cognitive-file (memory/instruction tampering), and trust-exploit (prompt injection disguised as arguments).
Getting Started
curl -LsSf https://raw.githubusercontent.com/cisco-ai-defense/defenseclaw/main/scripts/install.sh | bash. Requires Python 3.10+, Go 1.25+, and optionally Node.js 20+ for the TypeScript plugin.defenseclaw init --enable-guardrail to set up the Go gateway, configure the SQLite audit store, and enable guardrail functionality. The gateway starts listening for policy enforcement requests.OTEL_EXPORTER_OTLP_ENDPOINT for OTLP collectors.When to use Cisco DefenseClaw
Ideal for organizations deploying agentic AI systems in enterprise environments that need governance controls matching their existing security standards.
The framework covers the full lifecycle — pre-execution scanning, runtime inspection, and audit logging — which makes it a strong fit for regulated industries where every AI component interaction needs to be auditable.
The Cisco backing and enterprise integrations (Splunk, OTLP) make it a natural fit for organizations already in the Cisco security ecosystem, though the open-source license means it works independently of any Cisco product.
For a broader overview of AI security tools, see the AI security tools guide. For MCP-specific vulnerability scanning without the full governance framework, see MCP-Scan. For security analysis of agentic workflows across multiple frameworks, consider Agentic Radar.