Checkmarx SCA is an enterprise SCA tool that goes beyond CVE matching by using behavioral analysis to detect malicious packages and supply chain attacks. Part of the Checkmarx One platform, it has identified more than 420,000 malicious packages through a three-pronged approach: evaluating package provider credibility, assessing maintenance patterns, and analyzing package behavior.
The tool integrates with Checkmarx’s SAST, DAST, and API security products, letting teams correlate SCA findings with other vulnerability types for unified prioritization. Checkmarx One is used by 40% of the Fortune 100.
What is Checkmarx SCA?
Checkmarx SCA evaluates dependencies from three angles — this is a heavier software composition analysis model than a classic manifest-only CVE scan. First, it checks maintainer credibility: contributor history, publishing patterns, and association with known malicious actors.
Second, it assesses maintenance health: release frequency, issue response times, and community engagement.
Third, it performs behavioral analysis: detecting packages that access sensitive system resources, establish suspicious network connections, or exhibit dependency confusion patterns.
Key features
| Feature | Details |
|---|---|
| Malicious package detection | 420,000+ identified packages; behavioral, credibility, and maintenance analysis |
| Accuracy | Zero false positives in industry testing (vs. 10% competitor FP rate) |
| Transitive dependency scanning | Unlimited depth; covers direct and indirect references |
| Exploitable path analysis | Maps all potential call paths to vulnerable code |
| License compliance | Policy-based enforcement with automated actions |
| SBOM generation | Industry-standard CycloneDX format |
| CVSS support | Up to CVSS 4.0 severity scoring |
| Container scanning | Docker and OCI image analysis |
| Private registries | JFrog Artifactory integration for private packages |
Supply chain risk analysis
Checkmarx SCA evaluates the trustworthiness of package maintainers and repositories. Packages from suspicious sources receive higher risk scores regardless of known vulnerabilities.
The analysis catches zero-day supply chain attacks before CVEs are published.

Behavioral analysis
The engine analyzes what packages actually do: accessing sensitive system resources, establishing network connections, or exhibiting patterns associated with dependency confusion. This catches malicious code that CVE databases have not cataloged yet.
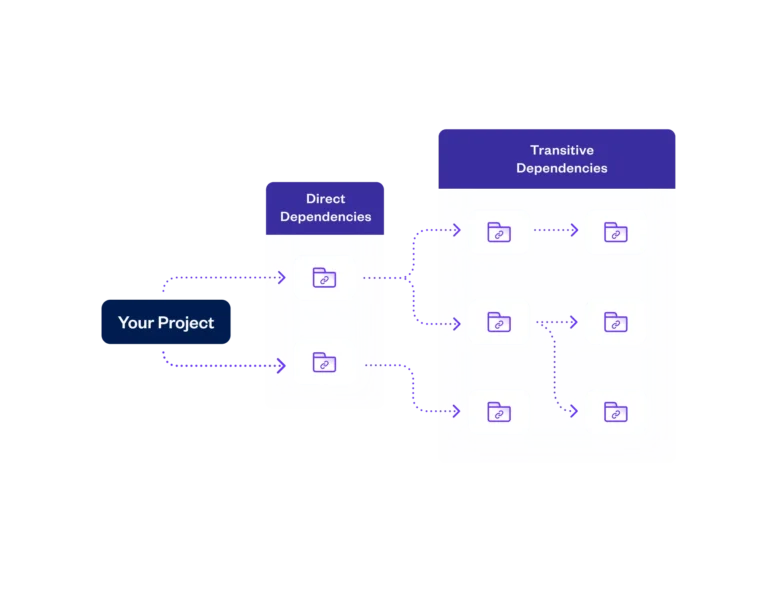
Transitive dependency scanning
The tool scans transitive dependencies to unlimited depth. It covers both direct and indirect package references, including packages pulled from private JFrog Artifactory registries.
License compliance
Define acceptable licenses for your organization, get alerts when dependencies introduce problematic terms, and generate compliance reports. Policy rules support automated actions including alerts, PR blocking, and build breaks.

SBOM generation
Generates Software Bills of Materials in CycloneDX format. SBOMs include full dependency trees with vulnerability status and license information.

Container scanning
Analyzes container images for vulnerable base layers and installed packages. Examines Dockerfiles, identifies the base image supply chain, and maps vulnerabilities across all image layers.
Reachability analysis
Checkmarx SCA’s exploitable-path feature is a form of reachability analysis. It pairs the manifest scan with SAST-style code scanning to check whether a vulnerable package’s vulnerable method is actually reachable from the application’s own code, and then walks the static call graph to show the exact path. Reachability coverage is currently available for Python, Java, JavaScript, and C#.
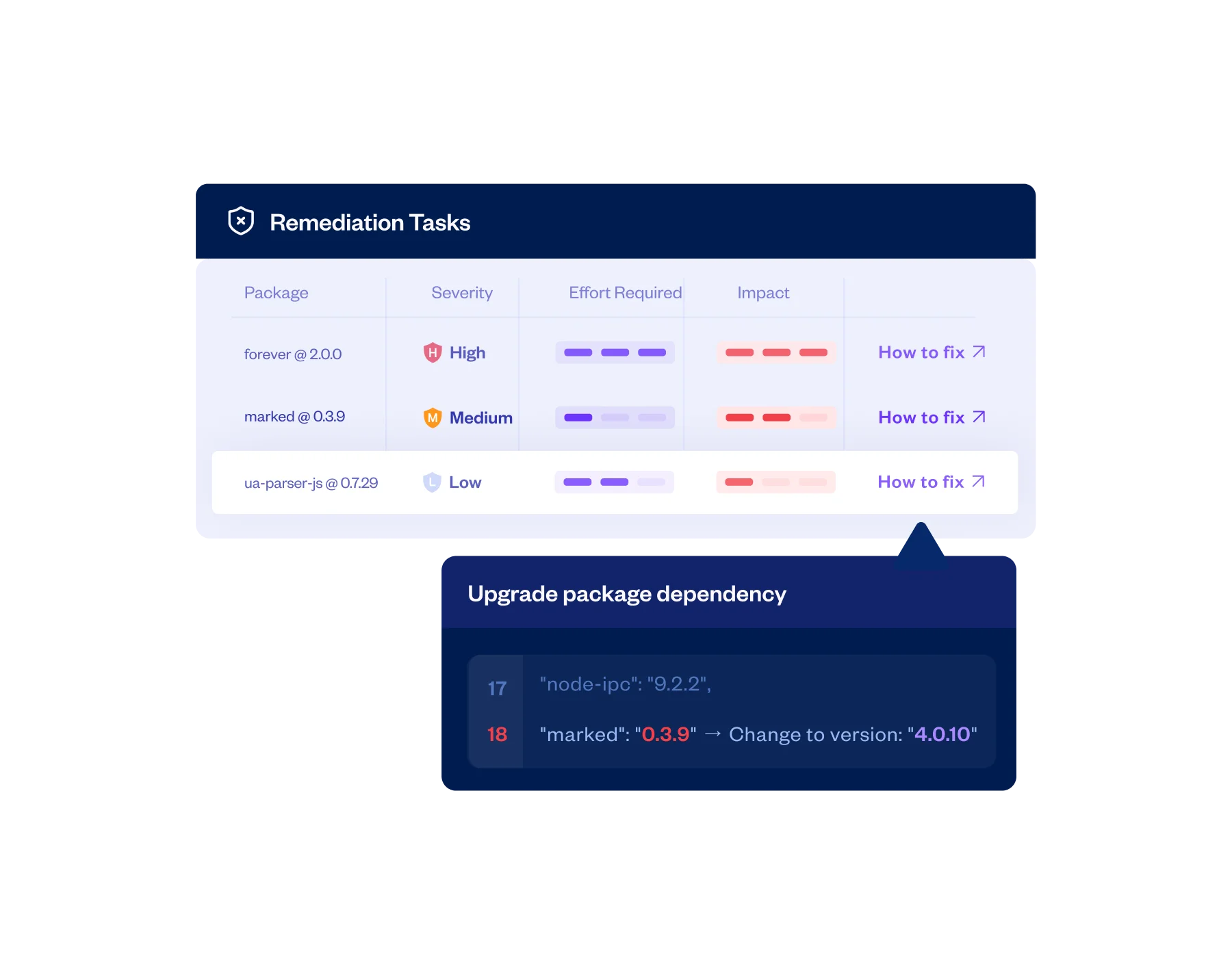
Dependency update automation
Checkmarx SCA does not ship automated dependency-update pull requests in the Dependabot or Renovate pattern. Remediation in Checkmarx SCA is policy-driven: configurable policies can block PRs that introduce new critical vulnerabilities, and the dashboard surfaces suggested fix versions for developers to apply manually. Teams that want auto-merging update PRs typically layer Dependabot or Renovate on top of Checkmarx SCA rather than replacing them.
Integrations
Getting started
cx) from the Checkmarx One portal. Available for Linux, macOS, and Windows.cx configure and enter your Checkmarx One tenant, API key, and base URL.cx scan create --project-name my-project --source . --scan-types sca.cx results show. Focus on exploitable path findings first.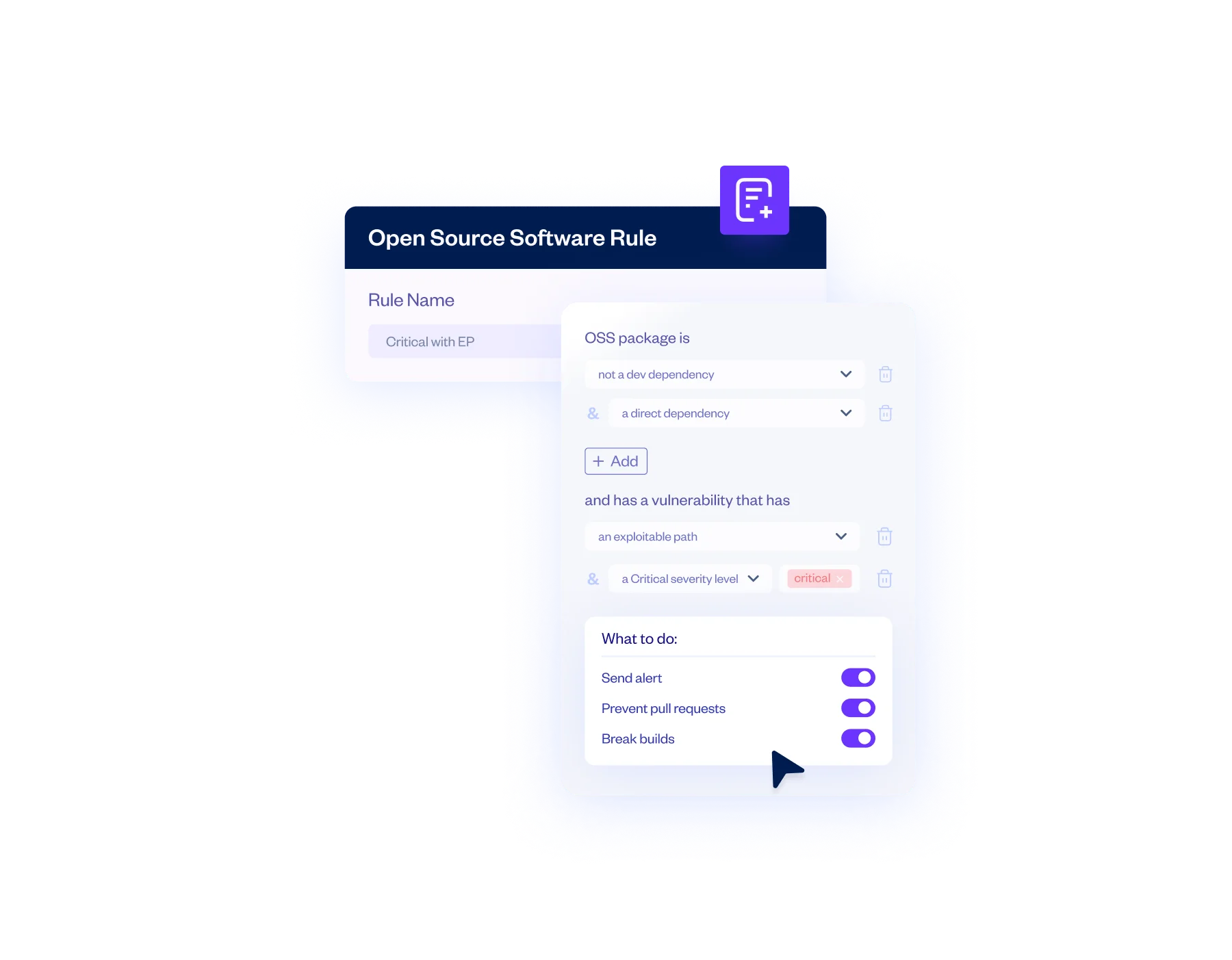
When to use Checkmarx SCA
Checkmarx SCA fits organizations that need supply chain attack detection beyond standard CVE matching, especially those already using or considering Checkmarx One for SAST.
The behavioral analysis and malicious package database (420K+ packages) provide detection that CVE-only scanners miss. Exploitable path analysis cuts through alert noise by showing which vulnerabilities have reachable code paths.
It is a commercial product with no permanent free tier. Median annual Checkmarx platform contract: $54,000 (range: $25,000–$111,000). Organizations only needing basic CVE scanning may find lighter-weight tools sufficient.
On false-positive rate, Checkmarx SCA’s accuracy characteristics follow the broader Checkmarx One exploit-path correlator: the more of the suite that is cross-correlated (SAST, SCA, API), the higher the prioritization signal and the lower the effective false-positive rate in the triage queue. Standalone SCA without exploit-path correlation behaves more like a classic CVE scanner. Note that “Checkmarx SCS” (Supply Chain Security) is a distinct extension module in the Checkmarx One platform focused on package-level supply-chain threats — it layers on top of Checkmarx SCA rather than replacing it.
How it compares:
| vs. | Key difference |
|---|---|
| Snyk Open Source | Snyk has a broader developer ecosystem and free tier. Checkmarx SCA has deeper behavioral analysis for supply chain attacks and correlates with Checkmarx SAST. |
| Socket | Socket focuses on behavioral analysis for npm/PyPI. Checkmarx SCA covers more ecosystems and integrates with a full AppSec platform. |
| Veracode SCA | Both offer supply chain detection (Veracode via Phylum acquisition). Checkmarx SCA ties into the broader Checkmarx One platform; Veracode ties into the Veracode suite. |
Learn more about what SCA tools do and how to integrate SCA into CI/CD pipelines.
Checkmarx SCA pricing
Checkmarx does not publish public dollar pricing for Checkmarx SCA or the broader Checkmarx One platform. All paid quotes are routed through sales via the checkmarx.com/contact form.
The commercial shape is an annual enterprise subscription inside the Checkmarx One bundle. Checkmarx SCA is licensed as one scanner in that bundle alongside SAST, Secrets, IaC, API security, and Supply Chain Security, with pricing scaled by the number of active committers or applications on the platform. There is no permanent self-serve free tier — developers can run SCA scans at no cost through the Checkmarx IDE plugins for IntelliJ IDEA Ultimate and VS Code, but platform access requires a paid tenant.
For budgeting context, our broader Checkmarx contract page lists a median annual platform deal of roughly $54,000 with a range of $25,000 to $111,000 (source: Vendr), but those figures cover the full Checkmarx One platform rather than SCA alone and vary substantially with committer count and module mix.
Re-check directly with Checkmarx before budgeting — enterprise platform pricing changes between renewals.
Checkmarx SCA alternatives
Checkmarx SCA is usually compared against other enterprise SCA tools rather than developer-first OSS scanners. The closest alternatives each shift the tradeoff differently.
Snyk Open Source
Snyk Open Source is the developer-first SCA with the broadest free tier and the most mature automated fix-PR workflow. Snyk wins when developers are the primary audience and speed of onboarding matters; Checkmarx SCA wins when exploit-path correlation across SAST, SCA, and API findings is the requirement.
Black Duck
Black Duck leads on enterprise license compliance and binary analysis. Black Duck fits legal-heavy and regulated industries where license-conflict detection is the core requirement; Checkmarx SCA fits organizations where correlation with SAST and API security sits above pure license depth.
Mend SCA
Mend SCA ships SCA with Renovate-powered automated dependency updates. Mend is the right pick when continuous update automation is the primary workflow; Checkmarx SCA doesn’t replicate that auto-PR model and instead focuses on policy-driven triage.
Sonatype Lifecycle
Sonatype Lifecycle centers on artifact-repository enforcement (Nexus Repository). Sonatype is the right pick when the control point is the artifact pipeline and the policy engine must gate binaries at pull-through; Checkmarx SCA operates at the source-and-manifest layer instead.
For the broader landscape, see SCA tools overview and what SCA does.
Checkmarx SCA FAQ
What is the difference between Checkmarx SAST and Checkmarx SCA?
Checkmarx SAST (formerly CxSAST) scans your own first-party code for vulnerability patterns. Checkmarx SCA scans your open-source dependencies — direct and transitive — for known CVEs, malicious packages, and license issues. They are separate scanners inside the same Checkmarx One platform, and the exploit-path correlator links findings from both.
How does Checkmarx SCA detect exploitable vulnerabilities?
It pairs the manifest scan with SAST-style code scanning to determine whether your application actually calls the vulnerable method in the vulnerable package, then walks the static call graph to show the exact path. Current exploit-path coverage is Python, Java, JavaScript, and C#.
Is Checkmarx SCA included in Checkmarx One?
Yes. Checkmarx SCA is one of the scanners bundled inside the Checkmarx One platform alongside SAST, Secrets, IaC, API security, and Supply Chain Security. It can be licensed standalone, but the exploit-path correlation that drives the zero-false-positive claim requires the other scanners to be live on the same project.
Does Checkmarx SCA generate SBOMs?
Yes, in CycloneDX format. SBOMs include the full transitive dependency tree with vulnerability status, CVSS severity (up to CVSS 4.0), and license information.
How does the SCA Resolver work with the SCA Scanner?
The SCA Resolver is a local CLI that parses manifests and lockfiles to resolve the true dependency graph in your environment, then uploads the resolved list to the Checkmarx SCA cloud scanner for CVE matching and exploit-path analysis. This is the recommended flow for monorepos and private-registry setups where the cloud scanner cannot reach the packages directly.
Does Checkmarx SCA produce license-compliance reports?
Yes. License policies are defined in the Checkmarx One dashboard and can trigger alerts, block PRs, or break builds when a dependency introduces a license that violates policy. Attribution exports and compliance summaries are available from the same policy module.
Frequently Asked Questions
What is Checkmarx SCA?
How does Checkmarx SCA detect supply chain attacks?
Does Checkmarx SCA work standalone?
Is there a free version of Checkmarx SCA?
How accurate is Checkmarx SCA?
* Pricing data from Vendr — anonymized contract values from real buyer transactions.