Checkmarx IAST provides runtime security testing as part of the Checkmarx One unified IAST platform. It monitors applications during execution to find vulnerabilities that static analysis misses, while correlating findings across SAST, SCA, and DAST to eliminate duplicates.
CxIAST was first released at Jenkins World 2017 and has been integrated into the Checkmarx One platform alongside SAST, DAST, SCA, API Security, and Container Security. The broader platform scans over 800 billion lines of code per month across 35+ programming languages.
What is Checkmarx IAST?
CxIAST takes a passive approach to runtime testing. A non-intrusive agent monitors your application during functional testing, QA cycles, or automated test suites.
It observes how data flows through the application without actively attacking it, meaning there is zero additional scan time on top of your existing tests.
Once functional testing finishes, the security “scan” is also done. CxIAST detects OWASP Top 10 vulnerabilities and more by tracking how input moves through code at runtime.
Key Features
| Feature | Details |
|---|---|
| Supported Languages | Java, .NET, Node.js |
| Testing Approach | Passive monitoring during functional tests |
| Scan Time | Zero additional time (piggybacks on existing tests) |
| Vulnerability Coverage | OWASP Top 10 and beyond |
| Finding Correlation | Automatic deduplication across IAST, SAST, DAST, SCA |
| API Discovery | Catalogs endpoints exercised during testing |
| Platform | Part of Checkmarx One (cloud-based) |
| CI/CD | Fits into DevOps and CI/CD pipelines |
Passive Runtime Monitoring
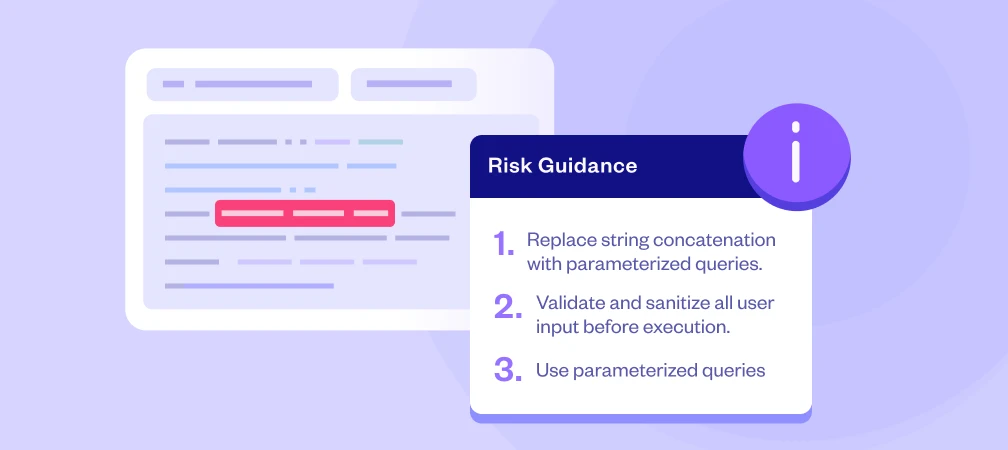
CxIAST monitors application behavior during your existing functional tests. The agent tracks data flow from HTTP requests through business logic to database queries and responses, catching injection flaws, authentication bypasses, and sensitive data exposure as they happen.
The key difference from active DAST scanning: CxIAST does not inject attack payloads. It watches normal test traffic and flags dangerous patterns it observes. This means zero impact on your deployment pipeline.
Cross-Scanner Correlation
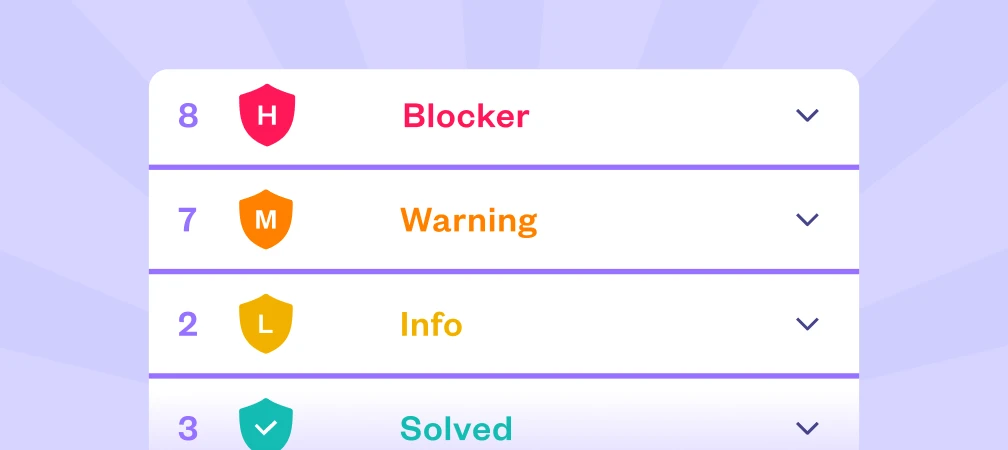
One of the most useful capabilities is automatic correlation between IAST, SAST, DAST, and SCA findings. When the same vulnerability shows up across multiple testing types, Checkmarx One merges them into a single issue.
This prevents developers from getting three separate tickets for the same SQL injection detected by SAST in the source, confirmed by IAST at runtime, and flagged by DAST externally.
API Discovery and Profiling
During testing, the IAST agent automatically discovers and catalogs all APIs the application exposes. This includes endpoints that don’t appear in documentation or aren’t linked from other pages.
The discovery data feeds into the Checkmarx One dashboard to highlight your API attack surface.
Getting Started
Deploy the agent — Add the CxIAST agent to your application in the testing environment. For Java, add it as a JVM argument.
For .NET, configure via application settings. For Node.js, install the agent package. No source code changes required.
When to Use Checkmarx IAST
Checkmarx IAST fits best in organizations that already use other Checkmarx products or want a unified application security platform. The main draw is consolidated findings and single-console management across testing types.
Consider Checkmarx IAST when you need:
- A single platform for all application security testing types
- Automatic correlation to reduce duplicate vulnerability tickets
- API discovery for complex microservices architectures
- Passive runtime testing that adds zero time to your pipeline
- Integration with existing Checkmarx One deployments
If you need an IAST tool that operates independently from a larger platform, look at Contrast Assess or Seeker IAST. If you already use Datadog for observability, Datadog IAST integrates directly with APM tracing.