Cerbos is an open-source authorization engine that provides fine-grained, policy-based access control for applications, APIs, AI agents, and MCP servers. Written in Go, it evaluates authorization requests against YAML-defined policies with sub-1ms latency — acting as a stateless policy decision point (PDP) that decouples access control logic from application code. Where MCP-Scan detects vulnerabilities in MCP server configurations, Cerbos solves a complementary problem: controlling which tools an agent can actually use based on user identity and organizational policy.
While Cerbos started as a general-purpose authorization solution for software applications, it has gained traction in the AI security space as organizations deploy AI agents that need granular permission controls. When an AI agent interacts with external tools through MCP (Model Context Protocol), Cerbos determines which tools that agent — and the user behind it — is actually allowed to use.
The project has over 4,300 GitHub stars and SDKs for eight programming languages. The latest release is v0.51.0 (February 2026). The core PDP is open-source under Apache 2.0, with commercial products (Cerbos Hub, Cerbos Synapse) adding centralized management and data enrichment capabilities.
What is Cerbos?
Authorization in traditional applications is already complicated — roles, attributes, contextual conditions, and compliance requirements create a tangled web of access control logic scattered across codebases. AI agents amplify this problem: an agent acting on behalf of a user should inherit that user’s permissions, but the execution happens through tool calls and API chains that existing authorization systems were not designed to handle.
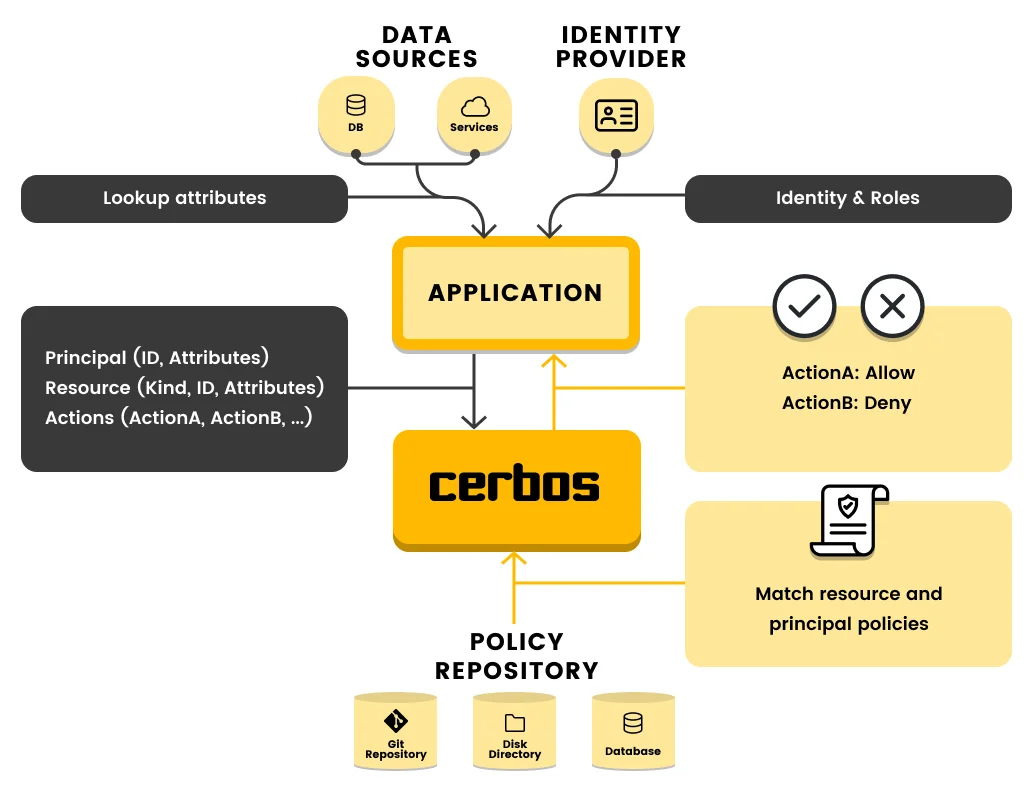
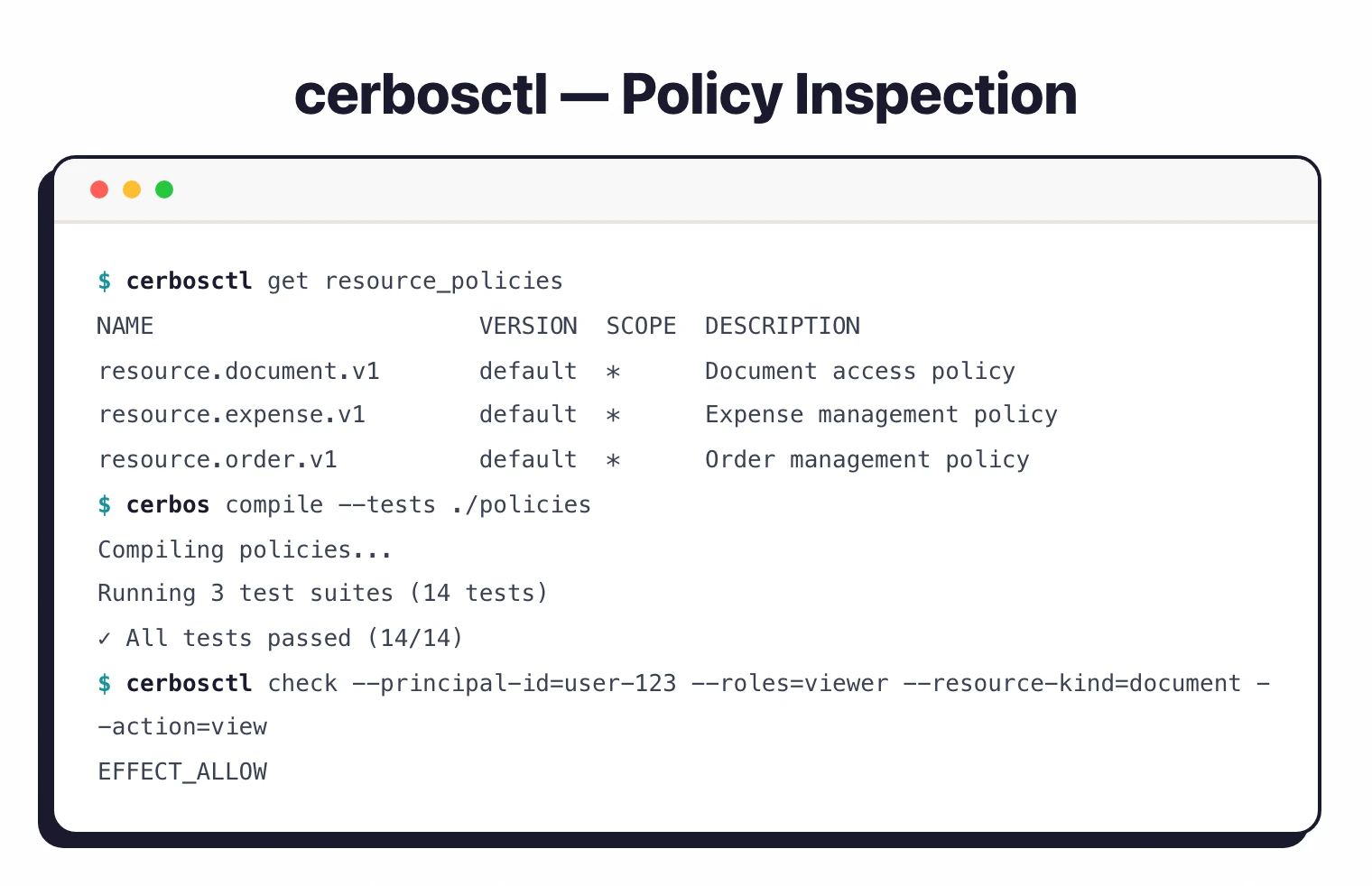
Cerbos solves this by centralizing all authorization decisions in a single policy engine. Applications, APIs, and AI agents send authorization requests (who wants to do what, on which resource, with what context), and Cerbos returns a decision based on YAML policies. The engine is stateless, so it scales horizontally without shared state or session management.
Key Features
| Feature | Details |
|---|---|
| Decision Latency | Sub-1ms policy evaluation |
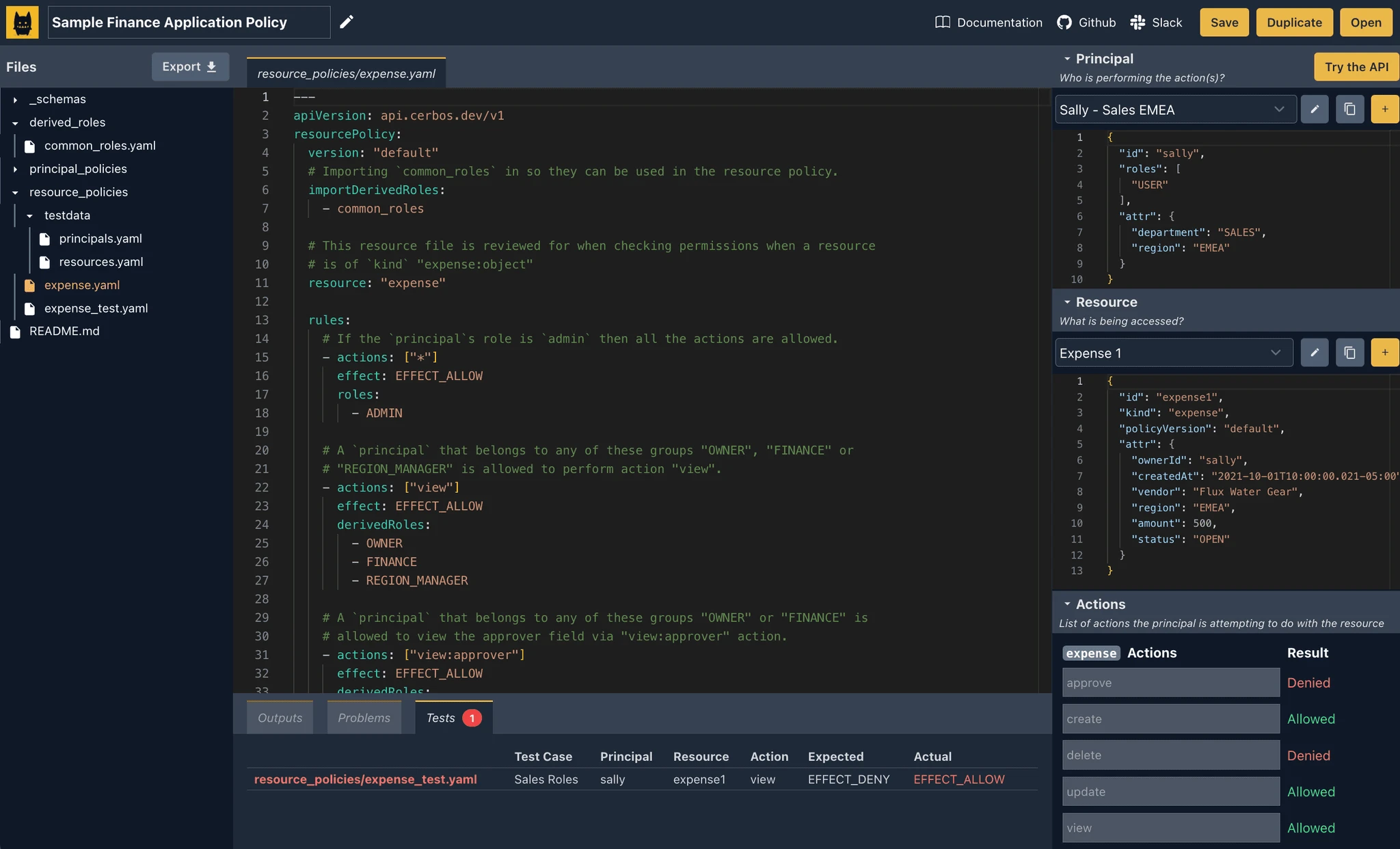
| Policy Format | Human-readable YAML with Git-ops management |
| Access Models | RBAC, ABAC, PBAC (Permission-Based Access Control) |
| Derived Roles | Dynamic role assignment based on contextual conditions |
| APIs | CheckResources and PlanResources endpoints |
| Language SDKs | Go, Java, JavaScript, Python, .NET, PHP, Ruby, Rust |
| AI Authorization | Agent permissions, MCP server tool control, RAG pipeline access |
| Deployment | Kubernetes (sidecar or service), Lambda, containers, edge, air-gapped, on-premise, WebAssembly |
| Compliance | SOC 2, SOC 3, HIPAA, ISO 27001, FedRAMP, GDPR, PCI DSS |
| Latest Release | v0.51.0 (February 2026) |
| Audit Logging | Structured decision logs with policy version lineage |
| Technology | Written in Go (93.4% of codebase), stateless architecture |
How authorization works
Cerbos operates on three core elements: principals (users, applications, or agents requesting access), actions (specific operations like create, read, update, delete), and resources (protected objects with attributes). Every authorization request includes these three elements plus optional context.
The PDP evaluates the request against matching policies and returns an ALLOW or DENY decision. Because the engine is stateless, it can run as a sidecar in Kubernetes, a standalone service, or even inside a Lambda function — scaling independently of the application it protects.
AI agent and MCP authorization
When an AI agent operates through MCP, it calls tools on behalf of a user. Without authorization controls, the agent has access to every tool the MCP server exposes — regardless of whether the user behind the agent should have that access.
Cerbos sits between the agent’s tool request and execution. The MCP server sends the agent’s identity, the requested tool, and the user’s context to Cerbos.
The policy engine evaluates whether that combination is authorized, and the MCP server only exposes the permitted tools. This approach means permissions are enforced consistently whether a human or an AI agent makes the request.
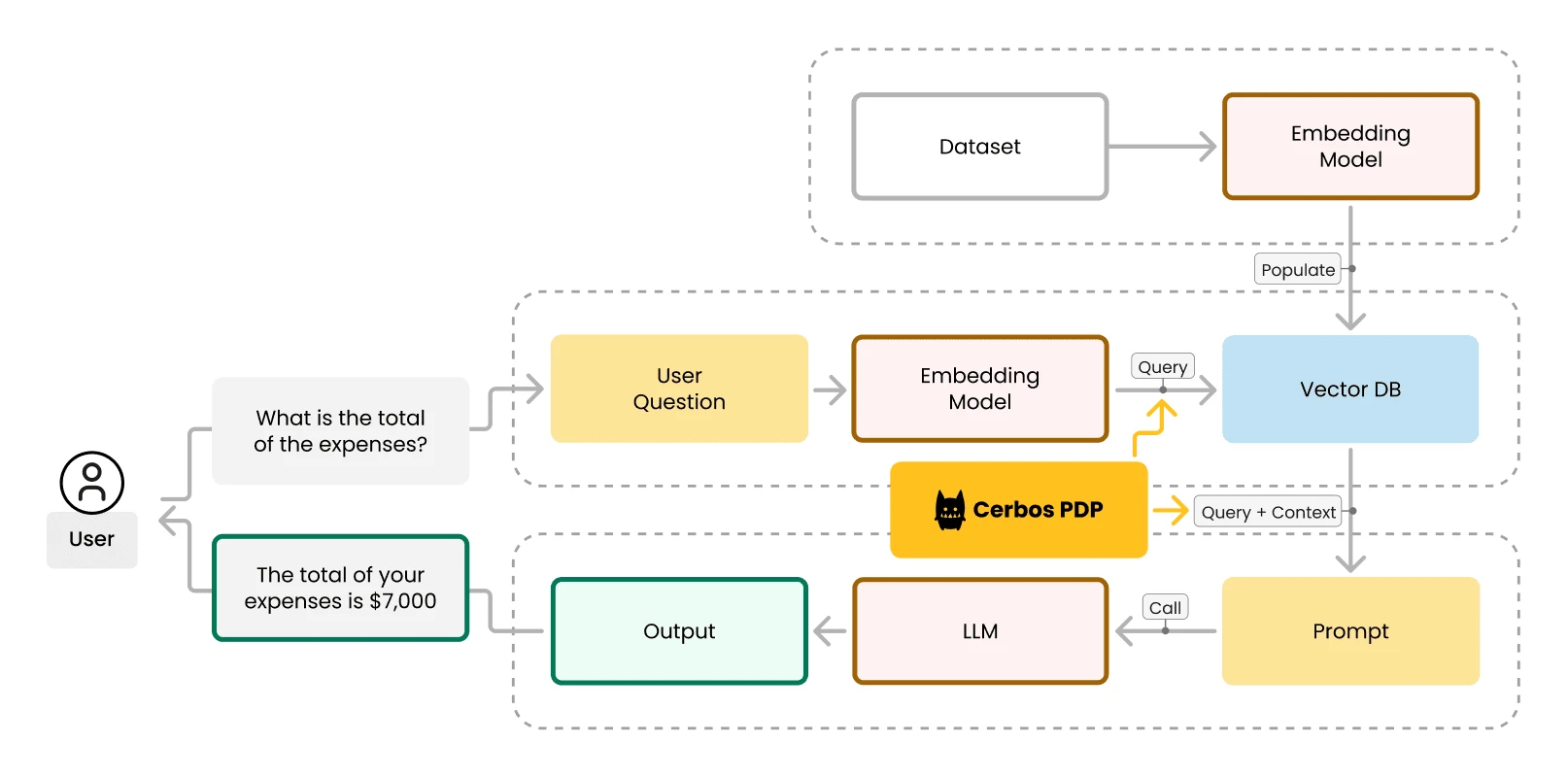
For RAG (Retrieval-Augmented Generation) pipelines, Cerbos controls which documents an agent can retrieve from vector stores (Pinecone, Weaviate, Chroma, Qdrant), ensuring that AI responses only draw from data the requesting user is authorized to access.
Commercial offerings
Cerbos Hub is the centralized control plane for policy authoring, testing, versioning, and distribution. It adds visual policy editing, automated testing, and multi-environment deployment management on top of the open-source PDP.
Cerbos Synapse enriches authorization requests by automatically fetching identity, resource, and relationship data from external systems — eliminating the need for applications to assemble context before making authorization calls.
Identity provider integrations
Cerbos integrates with major identity and DevOps platforms:
Getting Started
When to use Cerbos
Ideal for teams that need to control what AI agents and MCP-connected tools can do, based on the identity of the user the agent represents. While tools like MCP-Scan detect vulnerabilities in MCP server configurations, Cerbos solves a different problem: ensuring that even a perfectly secure MCP server only exposes the right tools to the right users.
The authorization engine is also valuable beyond AI use cases — any application that needs to decouple access control from business logic benefits from a centralized policy decision point. The AI agent authorization capabilities are an extension of the same core engine.
For a broader overview of AI security tools, see the AI security tools guide. For vulnerability scanning of MCP servers (rather than authorization), see MCP-Scan. For full governance of agentic AI systems including runtime inspection, consider Cisco DefenseClaw.