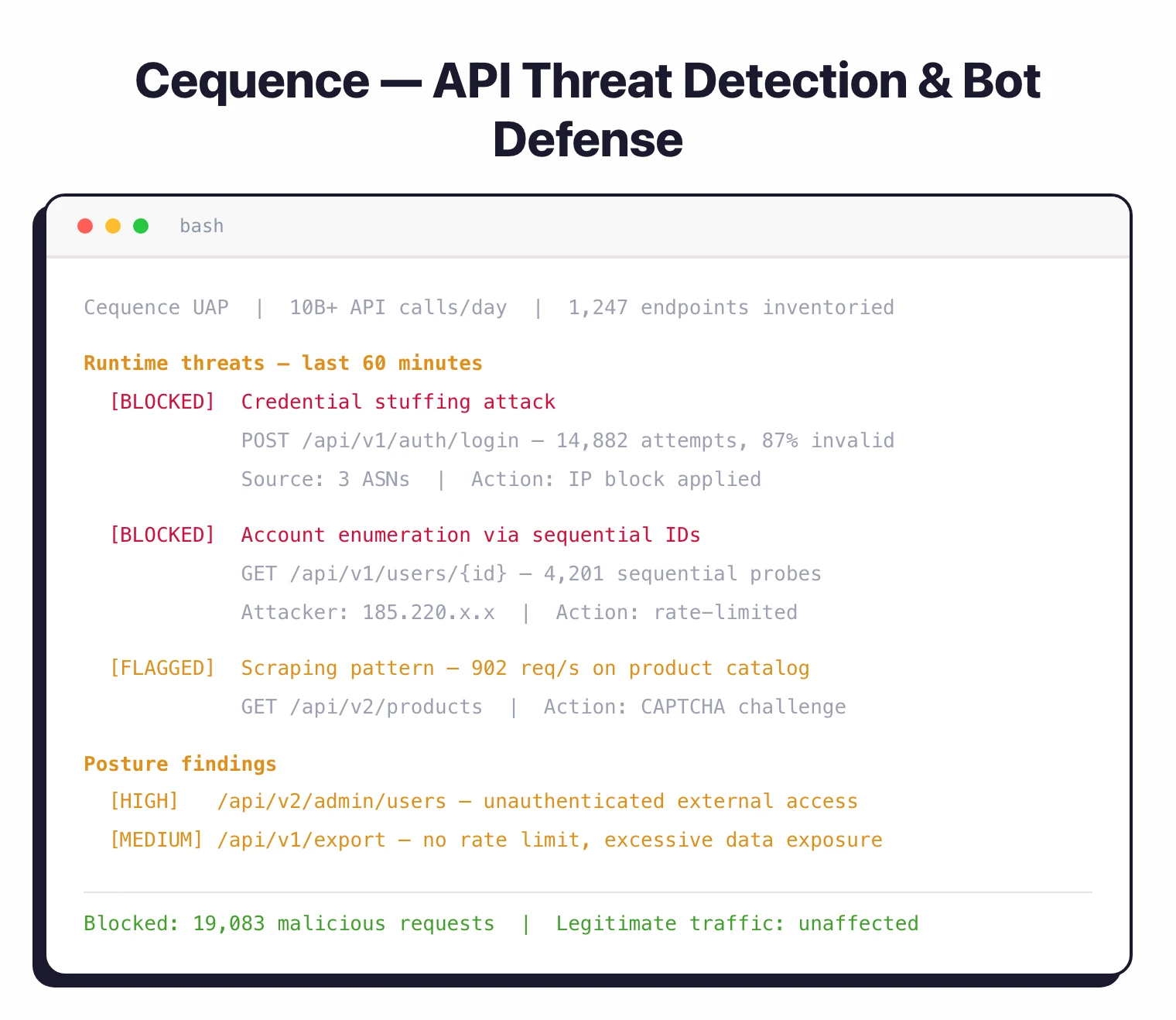
Cequence Security is a unified API security tools platform that discovers, tests, and defends APIs — and unlike most behavioral runtime peers like Salt Security , it blocks malicious traffic natively without requiring a separate WAF or API gateway to enforce decisions.
The platform processes over 10 billion API interactions daily for Fortune 500 financial institutions, retailers, telecom providers, and healthcare organizations.
Founded in 2014 and headquartered in Santa Clara, California, Cequence was named a Leader in the 2025 KuppingerCole Leadership Compass for API Security and ranked #128 on the Deloitte Technology Fast 500. The company also contributes to the Verizon Data Breach Investigations Report (2023, 2024, and 2025 editions) and was recognized as a Leader and Outperformer in the GigaOm API Security Radar.
What is Cequence Security?
Cequence is an API security platform built around a core distinction: it blocks attacks natively, inline, rather than detecting them and forwarding alerts to a separate enforcement system. Most competitors — including tools focused on API discovery and posture — stop at detection. Cequence deploys a reverse proxy called Defender that intercepts and drops malicious requests in real time, cutting the gap between detection and mitigation to zero.
Three pillars structure how it works:
Cequence also offers CQ Prime, a managed threat research team that maintains what the company describes as the largest database of malicious behaviors and known-bad infrastructure.
What are Cequence Security’s key features?
| Feature | Details |
|---|---|
| Deployment | SaaS, on-premises, hybrid. Deploys in as little as 15 minutes |
| Certifications | SOC 2 Type II, ISO 27001, PCI DSS 3.2 |
| Traffic capacity | 10B+ daily API interactions |
| Architecture | Kubernetes-based, flexible scaling |
Native Inline Blocking
Cequence deploys as a reverse proxy (called Defender) inline with your API traffic. This lets it block malicious requests in real time instead of sending alerts to a separate enforcement system.

Blocking policies are granular:
- Block known malicious IPs and fingerprints immediately
- Rate limit suspicious traffic while allowing legitimate requests
- Geo-fence requests by geographic origin
- Serve fake responses to deceive and slow down attackers
- Flag traffic for analysis without blocking
The Defender adds roughly 8-10 milliseconds of latency per request-response transaction in inline mode. For environments where inline deployment isn’t feasible, the Sensor component operates out-of-band by analyzing mirrored traffic with zero latency impact.
Behavioral Fingerprinting
Behavioral fingerprinting is a detection technique that identifies clients by how they interact with APIs over time — not just their IP address or user agent. Cequence builds these fingerprints continuously, which lets it catch attackers who:
- Rotate through thousands of IP addresses
- Mimic legitimate browser characteristics
- Distribute attacks across many sessions
- Use residential proxies to appear as normal users
Fingerprints incorporate request timing patterns, API call sequences, device characteristics, and interaction behaviors that are difficult to fake. The ML engine classifies threats by industry-specific patterns: telecom CPNI enumeration, retail inventory abuse, and financial services fraud each have distinct detection models.
The same behavioral analytics flag broken object-level authorization (BOLA — OWASP API1:2023) by detecting per-user access patterns that deviate from established role boundaries, even on undocumented endpoints. This BOLA / broken authorization testing capability runs continuously against live traffic rather than as a scheduled scan, so abuse of object-level identifiers shows up in the same fingerprint stream as credential stuffing and content scraping.
Bot Management
Cequence handles automated threats across web, mobile, and API channels from a single product rather than treating bot management as a bolt-on:
- Credential stuffing — Detects and blocks attempts to test stolen username/password combinations
- Account takeover — Identifies unauthorized access to legitimate accounts
- Inventory hoarding — Prevents bots from holding items in shopping carts during flash sales
- Content scraping — Stops automated harvesting of pricing, product, or proprietary data
- Fake account creation — Blocks automated registration of fraudulent accounts
- Gift card and loyalty abuse — Detects fraudulent redemption schemes
No client-side JavaScript or SDK is required. Detection operates at the network level, so it catches API and headless traffic that browser-based bot detection misses entirely.

API Discovery and Inventory
Cequence discovers APIs using both inside-out (traffic analysis) and outside-in (external scanning) methods. It picks up:
- Endpoint URLs, methods, and response schemas
- Authentication mechanisms in use
- PII and sensitive data types (with ML-based detection that distinguishes between data formats globally)
- Shadow APIs outside official documentation
- API gateways, infrastructure components, and cloud hosting providers
A Flow Graph view maps out API call paths and dependencies, which helps when hunting for rogue endpoints or unexpected data flows.
AI Gateway
The AI Gateway is a newer product that makes enterprise applications accessible to AI agents through the Model Context Protocol (MCP).

It works by translating MCP requests from AI agents into application-native API calls. Three steps to deploy:
- Connect applications via existing APIs or OpenAPI/Swagger specifications
- Configure authentication (passthrough or OAuth 2.0 identity providers)
- Deploy the MCP server (fully managed cloud or self-managed via Helm Chart)
The AI Gateway includes a Trusted MCP Registry that transforms official APIs into MCP-compatible endpoints. This avoids the risk of rogue MCP servers.
Organizations can optionally enable Cequence’s full UAP protection on the gateway with a single toggle.

WAAP
Cequence’s Web Application and API Protection bundles four capabilities into a single SaaS deployment:
- API Security — Discovery, testing, and runtime protection
- Bot Management — Behavioral detection and mitigation
- WAF — OWASP Top 10 coverage, Log4j and Java deserialization pattern matching
- DDoS Protection — Layer 3/4/7 mitigation with 99.99% availability SLA
Running from a single SaaS tenant rather than chaining separate products, it avoids the latency penalty of routing traffic through multiple hops.
How to use Cequence Security
Cequence’s deployment model gives me four onboarding choices, and the order I have seen work best mirrors the platform-agnostic story.
- Pick the deployment shape. Out-of-band Sensor against mirrored traffic adds zero latency and is the safest first step; inline Defender as a reverse proxy is the right choice once policies are tuned and blocking decisions are trusted. Hybrid splits the two so critical endpoints get inline enforcement while the rest stays passive.
- Discover and inventory APIs through Sentinel. The discovery engine runs continuously across internal, external, and third-party APIs, builds the Flow Graph, and surfaces shadow endpoints, schema drift, and PII exposure. Leave it running for at least one representative traffic window before tightening rules.
- Configure Spartan policies for posture. This is where compliance baselines (PCI DSS, GDPR, DORA) and OWASP API Top 10 conformance checks attach to the discovered inventory. Rules are user-configurable without code, and policies inherit from environment defaults so multi-tenant deployments stay manageable.
- Tune business-logic-abuse detections against your own traffic baseline. CQ Prime’s threat models cover credential stuffing, inventory hoarding, scraping, and account takeover out of the box; the per-customer tuning step lowers false positives by anchoring detections in your traffic mix rather than industry averages.
- Push alerts and blocking events into the SOC stack. Native connectors send to Splunk, Datadog, Slack, ServiceNow, Jira, and PagerDuty so the security and platform teams see the same signal that drives blocking decisions.
What does Cequence Security integrate with?
Cequence integrates with API gateways, CDNs, cloud providers, WAFs, and observability platforms.
Events also push to ServiceNow, Jira, Slack, and PagerDuty for ticketing and alerting workflows.
Deployment Options
Cequence supports three deployment models:
Inline (Active): Deploy the Defender as a reverse proxy for real-time blocking. Recommended for production APIs where immediate mitigation matters.
Out-of-Band (Passive): Analyze mirrored traffic through the Sensor component. Zero latency impact. Good as a first step before going inline, or when inline isn’t an option.
Hybrid: Inline on critical APIs, traffic mirroring on everything else. Gives full visibility while limiting inline deployment to high-priority endpoints.
All three options work across SaaS, on-premises (Kubernetes-based), and hybrid environments.
How do I get started with Cequence Security?
Cequence says deployment can finish in as little as 15 minutes. The CQ Prime team also offers managed services for organizations that want help with onboarding and ongoing threat monitoring.
Customer Results
Cequence counts Fortune 500 companies across financial services, retail, telecom, and healthcare among its customers. A few published results:
- Ulta Beauty — Blocked 85.9 million malicious requests during a fragrance inventory scraping attack, with 17 million blocked at the attack’s peak. The company reported $80,000 in savings across infrastructure and loss prevention.
- Poshmark — Achieved 80-90% automatic bot blocking with reduced account takeover incidents.
- T-Mobile — Deployed Cequence to discover and inventory APIs across a large-scale infrastructure, uncovering over 4,600 active endpoints and multiple sensitive data exposure issues during the initial proof of concept.
According to Cequence, its protection extends to 4 billion user accounts and 1 in 15 mobile users worldwide.
When to Use Cequence Security
Cequence is built for organizations that need to actually block API attacks, not just detect them.
It works well when you:
- Need real-time blocking without depending on a separate WAF
- Face credential stuffing, inventory hoarding, or scraping attacks at scale
- Handle sensitive financial, healthcare, or customer data through APIs
- Want a single platform for API security and bot management rather than two separate products
- Process high-volume API traffic across multiple gateways and cloud providers
Consider alternatives if:
- You only need API discovery and testing without runtime protection — tools like 42Crunch focus on that
- Budget constraints favor open-source options
- Your API traffic volume doesn’t justify enterprise tooling
- You prefer a detection-only approach with your existing WAF handling enforcement
How much does Cequence Security cost?
Cequence does not publish price lists for the Unified API Protection platform. Procurement runs through enterprise sales for all three product lines — Spartan (API security and bot defense), Sentinel (API discovery and inventory), and the WAAP bundle that pulls in WAF and DDoS — and the cequence.com pricing page directs prospects to a contact-sales flow rather than a public rate card.
Three signals usually move the quote: API call volume across the monitored estate, the deployment model (inline Defender, out-of-band Sensor, or hybrid), and which modules are in scope (Spartan plus Sentinel, the AI Gateway add-on, or the full WAAP bundle). Larger Fortune 500 deployments tend to negotiate annual contracts with optional CQ Prime managed-service hours layered on top. Onboarding usually closes in a 30–60 day procurement cycle for new buyers, with a passive-mirror POC running first to size the eventual production deployment.
What are alternatives to Cequence Security?
Cequence sits at the unusual intersection of API security and ML-driven bot defense, so the closest alternatives split by which axis you weight more.
- Salt Security is the obvious behavioral-runtime peer. It runs continuous detection against live API traffic without leaning on inline blocking, which makes it the default choice when the WAF stays in place and Cequence’s native enforcement is not a fit.
- Akamai API Security , formerly Noname Security , pairs Noname’s discovery engine with Akamai’s edge. Pick it when the buying signal is multi-CDN coverage rather than ML bot defense.
- Wallarm bundles WAAP heritage with API discovery and runtime detection. It is the better fit when the WAF replacement and the API security purchase land in the same budget cycle.
- HUMAN Security is the specialist on the bot-defense axis only — no full API security platform — and competes for the credential-stuffing and account-takeover slice of Cequence’s footprint.
- Imperva API Security extends an established WAF platform with API discovery and runtime checks, which suits existing Imperva customers consolidating into a single vendor.
The buying signal that consistently favors Cequence is needing real-time blocking for business-logic abuse — credential stuffing, inventory hoarding, scraping — across high-volume API traffic without standing up a separate WAF rule set.