Calico is an open-source Kubernetes CNI plugin and network security platform that handles pod-to-pod networking and network policy enforcement in a single solution.
Created and maintained by Tigera, it is the most widely adopted Kubernetes networking solution, powering over 8 million nodes daily across 166 countries. 7.1k GitHub stars, latest version v3.31.4 (February 2026).
Unlike tools that only scan images or check configurations, Calico operates at the network layer — controlling which pods can talk to each other, encrypting traffic between nodes with WireGuard, and enforcing microsegmentation policies that follow workloads across clusters.
Overview
Calico provides two core capabilities in one platform: Kubernetes networking (routing pod traffic) and network security (controlling what traffic is allowed). This dual role sets Calico apart from pure security tools — it is both the network fabric and the policy enforcement engine.
The project offers a pluggable data plane architecture. Teams can choose between:
| Data Plane | Best For |
|---|---|
| eBPF | High-performance environments, source IP preservation |
| Standard Linux (nftables/iptables) | Maximum compatibility, proven stability |
| Windows HNS | Mixed Linux/Windows Kubernetes clusters |
| VPP | Telco and high-throughput edge workloads |
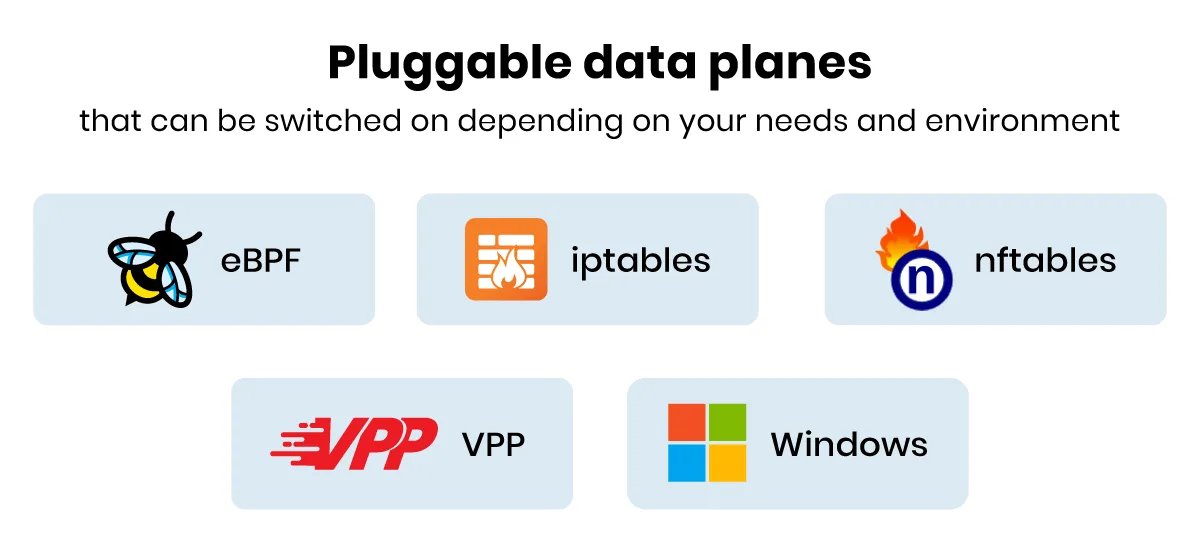
This flexibility lets Calico run everywhere from single-node development clusters to production environments at companies like AT&T, Discover, Merck, and ServiceNow.
| Feature | Details |
|---|---|
| Deployment model | Self-managed (Open Source, Enterprise) or SaaS (Calico Cloud) |
| Data planes | eBPF, standard Linux (nftables/iptables), Windows HNS, VPP |
| Encryption | WireGuard (pod-to-pod), ~73% throughput on 5Gbps with eBPF |
| Policy types | Kubernetes NetworkPolicy, GlobalNetworkPolicy, tiered policies |
| Routing | BGP peering, VXLAN, IP-in-IP, cross-subnet optimization |
| IP support | Dual-stack IPv4/IPv6 |
| OS support | Linux, Windows |
| Compliance | PCI DSS, SOC 2, GDPR, HIPAA (Enterprise/Cloud) |
| Adoption | 8M+ nodes daily, 1M+ clusters, 166 countries |
| GitHub | 7.1k stars, Apache 2.0 |
What are Calico’s key features?
Microsegmentation and Zero Trust
Calico’s network policies enable microsegmentation at the pod level. Instead of broad subnet-based firewall rules, I can define policies that specify exactly which pods, namespaces, and services are allowed to communicate. Labels and selectors keep policies dynamic: they follow workloads as pods scale up, restart, or move across nodes.
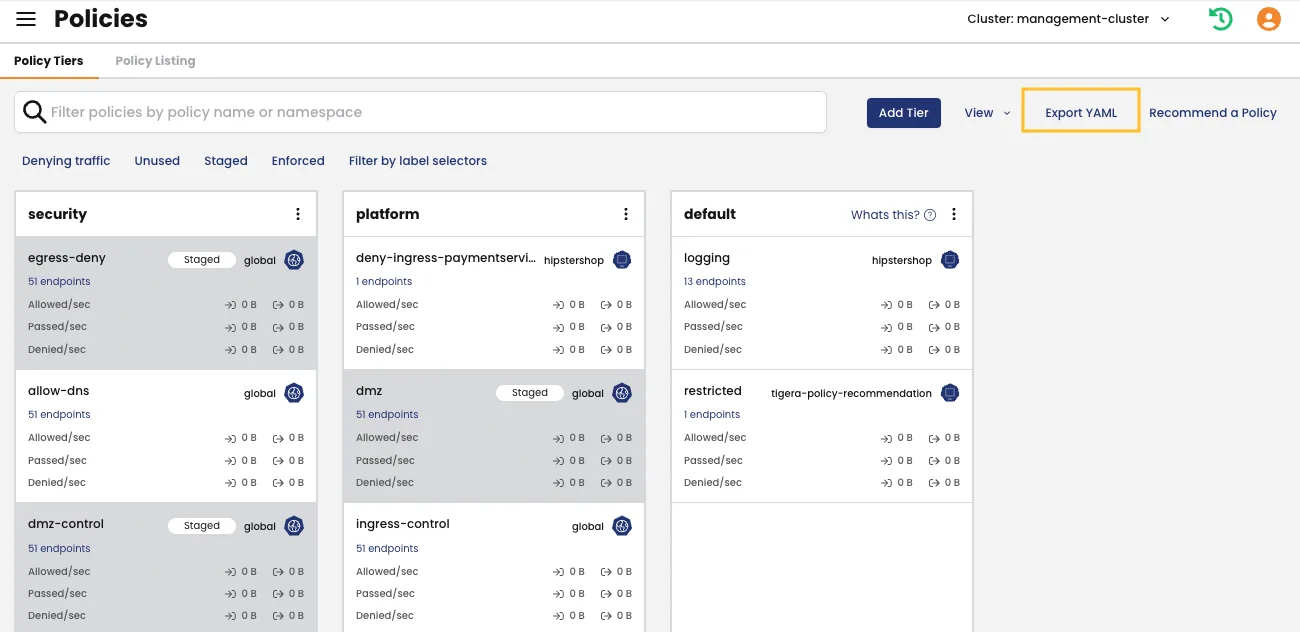
For Zero Trust implementations, Calico supports deny-by-default policies combined with explicit allow rules. Tiered policies (available in Enterprise/Cloud editions) let security teams set non-negotiable baseline policies while giving development teams freedom within those guardrails.
BGP and Non-Overlay Networking
Calico is one of few CNI plugins that supports native BGP peering, which eliminates the overhead of overlay networks like VXLAN. In environments where BGP is available (on-premises data centers, bare-metal clusters), this gives pods routable IP addresses directly on the infrastructure network — reducing latency and simplifying troubleshooting.
For environments that need overlays, Calico supports both VXLAN and IP-in-IP encapsulation with cross-subnet optimization.
Multi-Cluster and Hybrid Support
Calico works across EKS, GKE, AKS, OpenShift, RKE, k3s, and self-managed Kubernetes clusters. It runs on Linux and Windows nodes, and supports dual-stack IPv4/IPv6 networking. The commercial editions add multi-cluster management for federated policy enforcement across environments.
When should you use Calico?
Platform engineering teams use Calico as the default CNI across all Kubernetes clusters, standardizing on one networking and security solution rather than managing separate tools for routing and policy.
Security teams implement microsegmentation and Zero Trust networking through Calico’s tiered policies, enforcing baseline security rules across all namespaces without requiring changes from application developers.
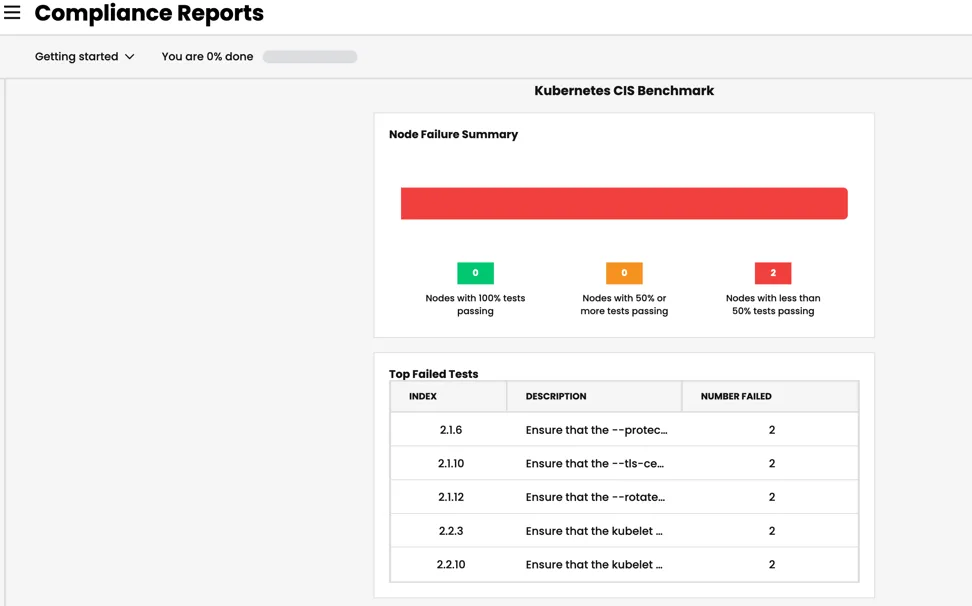
Compliance-driven organizations use Calico Enterprise or Calico Cloud for continuous compliance monitoring against PCI DSS, SOC 2, GDPR, and HIPAA frameworks, with audit trails and reporting built into the platform.
Hybrid and multi-cloud deployments rely on Calico’s consistent networking model across cloud providers and on-premises infrastructure, using BGP peering to connect environments without overlay overhead.
How does Calico compare to Cilium and Antrea?
The Kubernetes CNI shortlist almost always comes down to three projects. Here’s how I see them in practice.
Cilium is the eBPF-native challenger. It was built around eBPF from day one, ships Hubble for L3-L7 flow observability, and has stronger Layer 7 policy semantics for HTTP, gRPC, and Kafka. The trade-off is sharper kernel-version requirements and a steeper operational learning curve when something goes wrong in the eBPF data path.
Antrea is the VMware-backed CNI built on Open vSwitch (OVS). It is the natural pick for VMware Tanzu and NSX-T-heavy estates because it integrates with the vSphere networking stack. Outside of that ecosystem its community footprint is much smaller than Calico’s or Cilium’s.
Calico is the broadest-deployment option of the three: dual data plane (eBPF or standard Linux), native BGP peering for non-overlay routing, the only mature Windows node support, and the largest production install base. The honest trade-off is that Cilium’s L7 policy engine and Hubble observability are more advanced for greenfield clusters on modern kernels.
| Pick | If your priority is |
|---|---|
| Calico | Hybrid Linux+Windows clusters, BGP-native data centers, broadest distro support, mature Kubernetes NetworkPolicy + GlobalNetworkPolicy, compliance reporting via Enterprise/Cloud |
| Cilium | eBPF-first design, Hubble L3-L7 observability, Layer 7 policy for HTTP/gRPC/Kafka, greenfield cloud-native deployments on modern kernels |
| Antrea | VMware Tanzu / NSX-T integration, OVS familiarity, vSphere-aligned networking |
| Default cloud CNI | Single-cloud lock-in is fine and you do not need network policy beyond the basic Kubernetes API |
All three integrate with OPA Gatekeeper for admission-time policy enforcement, so the CNI choice does not lock you out of cluster-wide policy automation.
What does Calico integrate with?
Calico ships as the default or supported CNI on every major Kubernetes distribution: Amazon EKS, Azure AKS, Google GKE (optional), Red Hat OpenShift, Rancher RKE/RKE2, SUSE Rancher, k3s, and bare-metal kubeadm clusters. Operators install it via the Tigera operator (Helm chart or kubectl manifest), which keeps lifecycle management consistent across environments.
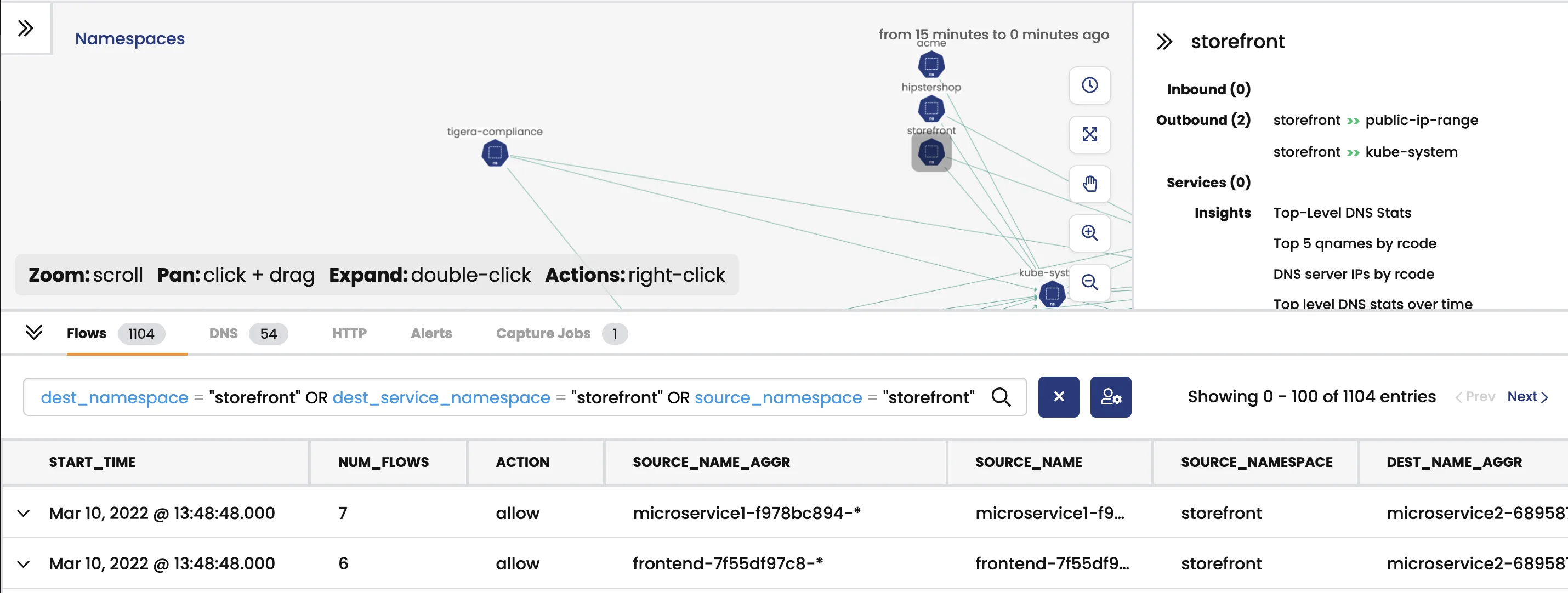
Observability hooks integrate with Prometheus, Grafana, Elasticsearch, Fluentd, and the commercial Dynamic Service Graph for flow visualization. Policy automation works with OPA Gatekeeper and Kyverno — both can manage Calico GlobalNetworkPolicy resources alongside standard admission rules. Calico also coexists with service meshes (Istio, Linkerd) at the L4 layer, while the mesh handles L7 concerns. For runtime threat detection on top of network policy, Falco plugs in cleanly at the kernel level.
How much does Calico cost?
Calico is available in three tiers:
| Tier | Model | Key Additions |
|---|---|---|
| Calico Open Source | Free (Apache 2.0) | Networking, network policy, eBPF, WireGuard, BGP |
| Calico Enterprise | Commercial (self-managed) | Dynamic Service Graph, compliance reporting, tiered policies, threat feeds, egress controls |
| Calico Cloud | SaaS (starts at $0.025/vCPU-hour) | Fully managed, AI assistant, multi-cluster management |
Calico Cloud also offers a free tier for single-cluster environments, providing observability dashboards, policy recommendations, and staged policy previews at no cost. Enterprise pricing requires contacting Tigera directly.
Pro tip: Platform engineering and DevOps teams standardizing Kubernetes networking and network security across multiple clusters. Calico makes the most sense when you need one solution for both pod networking (CNI) and network policy enforcement, especially in hybrid environments with mixed Linux/Windows nodes or on-premises BGP requirements.
How do I get started with Calico?
Install Calico as your CNI plugin. Deploy using the Tigera operator via Helm chart or kubectl manifest. Works with new or existing Kubernetes clusters on any distribution.
Configure your data plane. Choose between eBPF (for performance), standard Linux (for compatibility), or Windows HNS (for mixed-OS clusters). Enable WireGuard encryption if you need on-the-wire pod traffic security.
Define network policies. Start with Calico’s Kubernetes NetworkPolicy support, then extend with GlobalNetworkPolicy CRDs for cluster-wide rules. Use label selectors to target workloads dynamically.
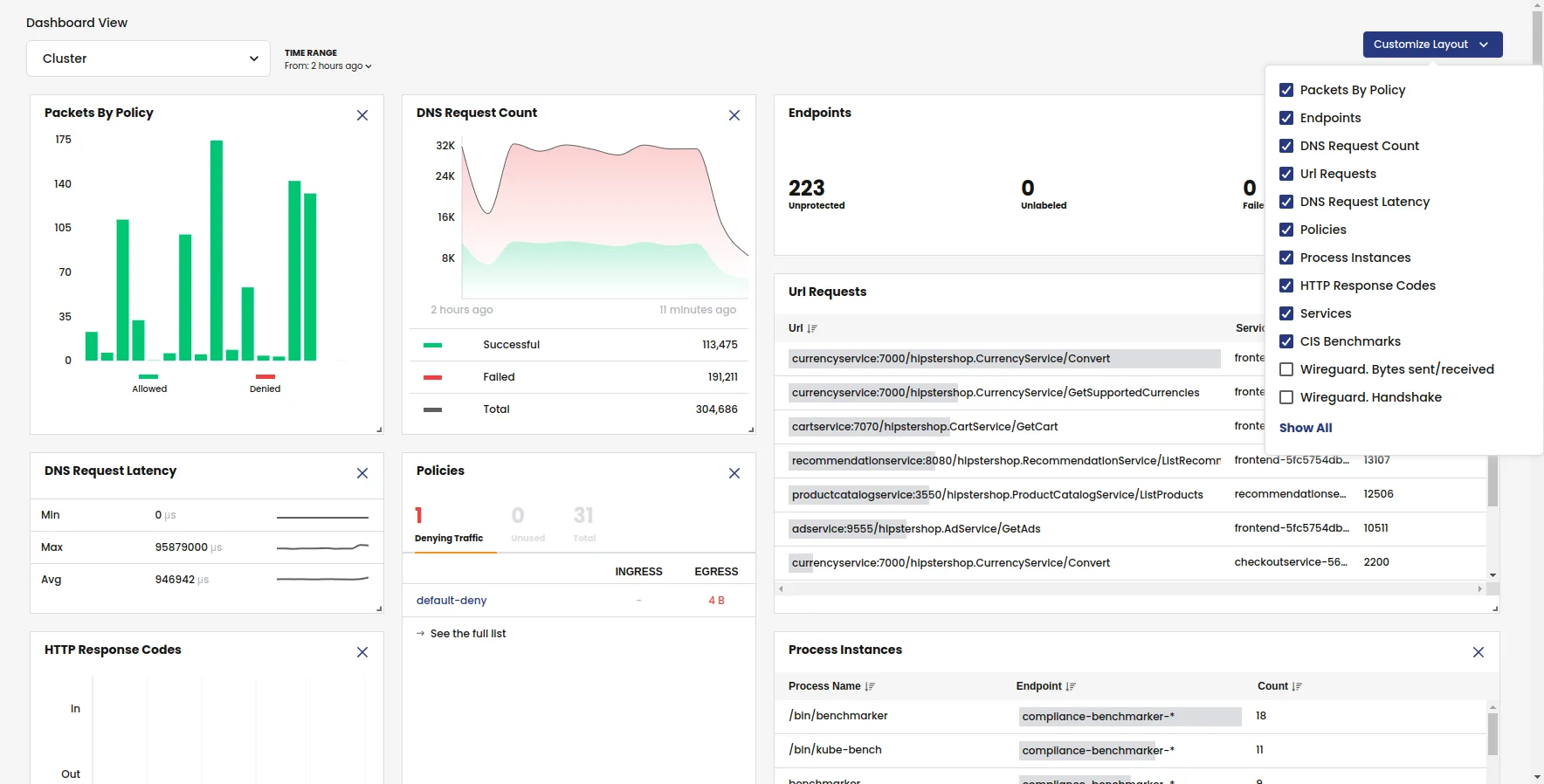
Visualize traffic (commercial). Calico Enterprise and Calico Cloud provide Dynamic Service Graph to visualize actual traffic flows between workloads, identify unprotected communication paths, and get policy recommendations.
Strengths & Limitations
Strengths:
- Most widely deployed Kubernetes CNI — 8M+ nodes, 1M+ clusters globally
- Multiple data plane options (eBPF, Linux, Windows, VPP) for different requirements
- Native BGP support eliminates overlay overhead in data center environments
- WireGuard encryption adds transport-layer security with minimal performance cost
- Tiered policies enable centralized security governance without blocking developer autonomy
- Free tier of Calico Cloud provides observability without commercial commitment
Limitations:
- eBPF dataplane was added after initial design (unlike Cilium’s eBPF-first architecture) — some eBPF features lag behind Cilium
- Layer 7 (application-layer) policy enforcement is limited compared to Cilium’s HTTP/gRPC-aware policies
- No built-in observability tool equivalent to Cilium’s Hubble (commercial Service Graph fills this gap)
- Calico Open Source lacks compliance reporting, threat feeds, and centralized multi-cluster management
- Windows support covers networking but not all security features available on Linux
Two more honest trade-offs worth knowing before standardizing on Calico.
The eBPF data plane is faster but harder to debug. On older kernels (RHEL 7, Ubuntu 18.04), eBPF features are limited or unavailable, and the standard Linux data plane (iptables/nftables) is still the right call. Iptables is verbose but tcpdump and traditional tooling work the way operators expect — eBPF requires bpftool and a different mental model. For teams without eBPF experience, sticking with the standard data plane until you actually hit a throughput bottleneck is a reasonable default.
Calico Open Source omits commercial features that some compliance programs assume by default: there is no built-in compliance reporting (PCI, SOC 2), no DNS-aware policy, no centralized multi-cluster policy management, and no threat feeds. Those live in Calico Enterprise and Calico Cloud. If a CISO asks for evidence-grade audit reports out of the box, the open-source tier alone will not satisfy the requirement.
For a broader view of Kubernetes and container security options, see the container security tools category page. Calico pairs well with runtime security tools like Falco for kernel-level threat detection and image scanners like Trivy for pre-deployment vulnerability scanning.