Black Duck Software is an enterprise software composition analysis (SCA) platform for managing open-source security, license compliance, and code quality risks. As of April 2026, it operates as an independent company after the Synopsys Software Integrity Group spinoff on October 1, 2024.
The platform scans source code, binaries, and containers to identify open-source components, map known vulnerabilities, and flag license obligations.
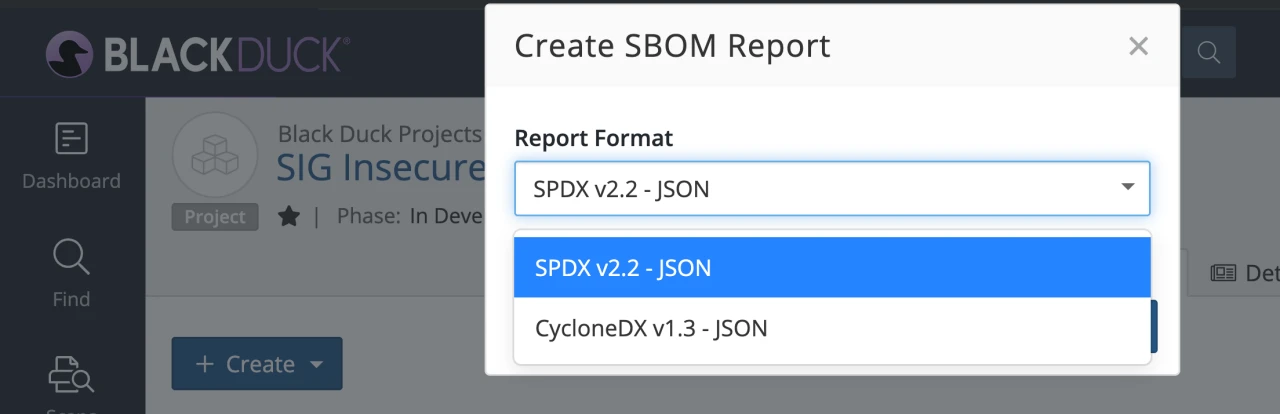
Thousands of organizations use it, mostly in regulated industries that need auditable SBOMs and license compliance reporting.
The Black Duck KnowledgeBase indexes over 10 million open-source projects and 8.7 million unique components from more than 57,700 forges and repositories. Proprietary Black Duck Security Advisories (BDSAs) add vulnerability intelligence that goes beyond public databases like the NVD.
Companies in healthcare, finance, and defense use it for SBOM generation and license compliance .
The Synopsys 2024 OSSRA report found that 53% of audited codebases contained license conflicts, which is the kind of number that keeps Black Duck on enterprise shortlists.
- Category: Software Composition Analysis (SCA) / license compliance
- Owner: Independent company since October 1, 2024; majority-owned by Clearlake Capital and Francisco Partners (formerly Synopsys Software Integrity Group)
- CEO: Jason Schmitt
- Headquarters: Burlington, Massachusetts
- Main products: Black Duck SCA (self-hosted) and Black Duck Polaris Platform (SaaS)
- Target customers: Regulated enterprises, M&A due diligence, commercial software vendors
- Free tier: None (commercial only)
What is Black Duck?
Black Duck is a commercial software composition analysis (SCA) platform that scans source code, binaries, and containers to inventory open-source components, map them to known vulnerabilities, and track license obligations. Black Duck Software has operated the platform as an independent company since its October 1, 2024 spinoff from Synopsys.
Each component is then checked against vulnerability databases and the organization’s policy rules for acceptable licenses.
What are Black Duck’s key features?
Supported ecosystems
| Ecosystem | Package managers |
|---|---|
| Java | Maven, Gradle, Ant, sbt |
| JavaScript | npm, yarn, pnpm, Bower |
| Python | pip, Poetry, Pipenv, Conda |
| Go | Go modules |
| C/C++ | Conan, vcpkg, CMake |
| Ruby | Bundler |
| PHP | Composer |
| .NET | NuGet |
| Swift/Objective-C | CocoaPods, Swift PM, Carthage |
| Kotlin | Gradle, Maven |
| Rust | Cargo |
| Scala | sbt, Maven |
| Containers | Docker, OCI |
| Binaries | JAR, DLL, EXE, firmware |
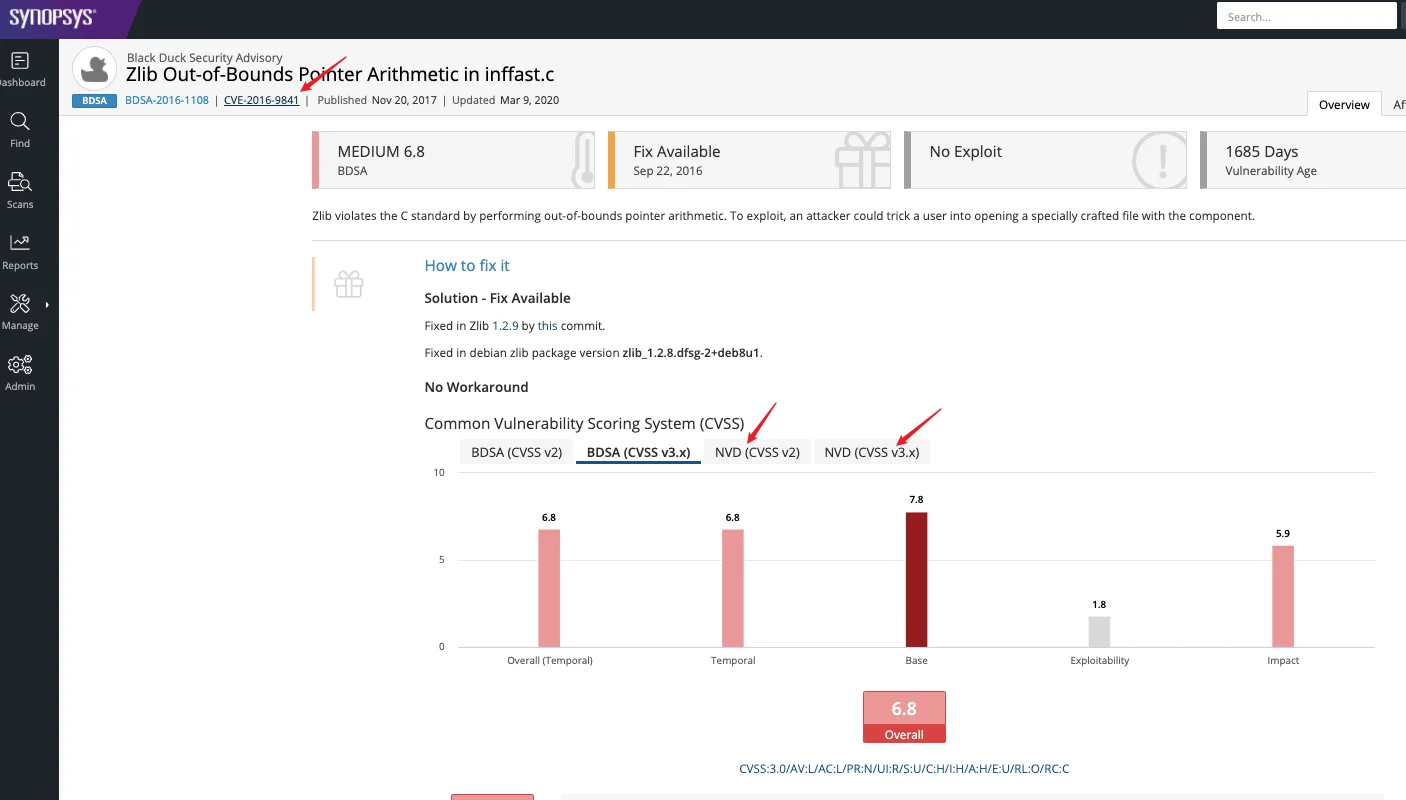
Black Duck Security Advisories (BDSAs)
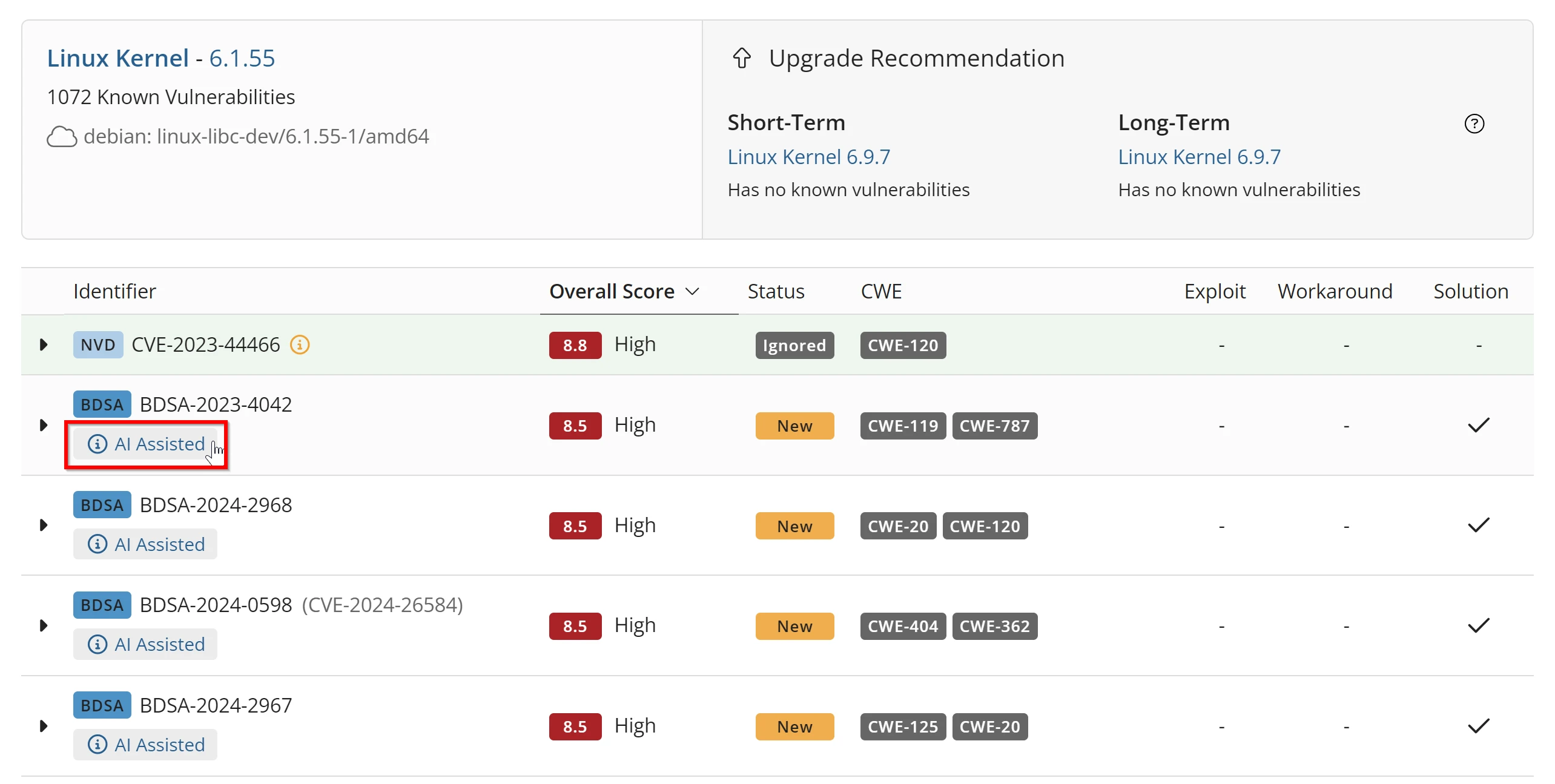
The security research team curates advisories that often land before NVD entries are published.
Each BDSA flags whether known exploits exist in the wild, suggests an upgrade path that avoids breaking changes, and scores severity against real-world risk. You can also add custom vulnerability entries for internal findings.
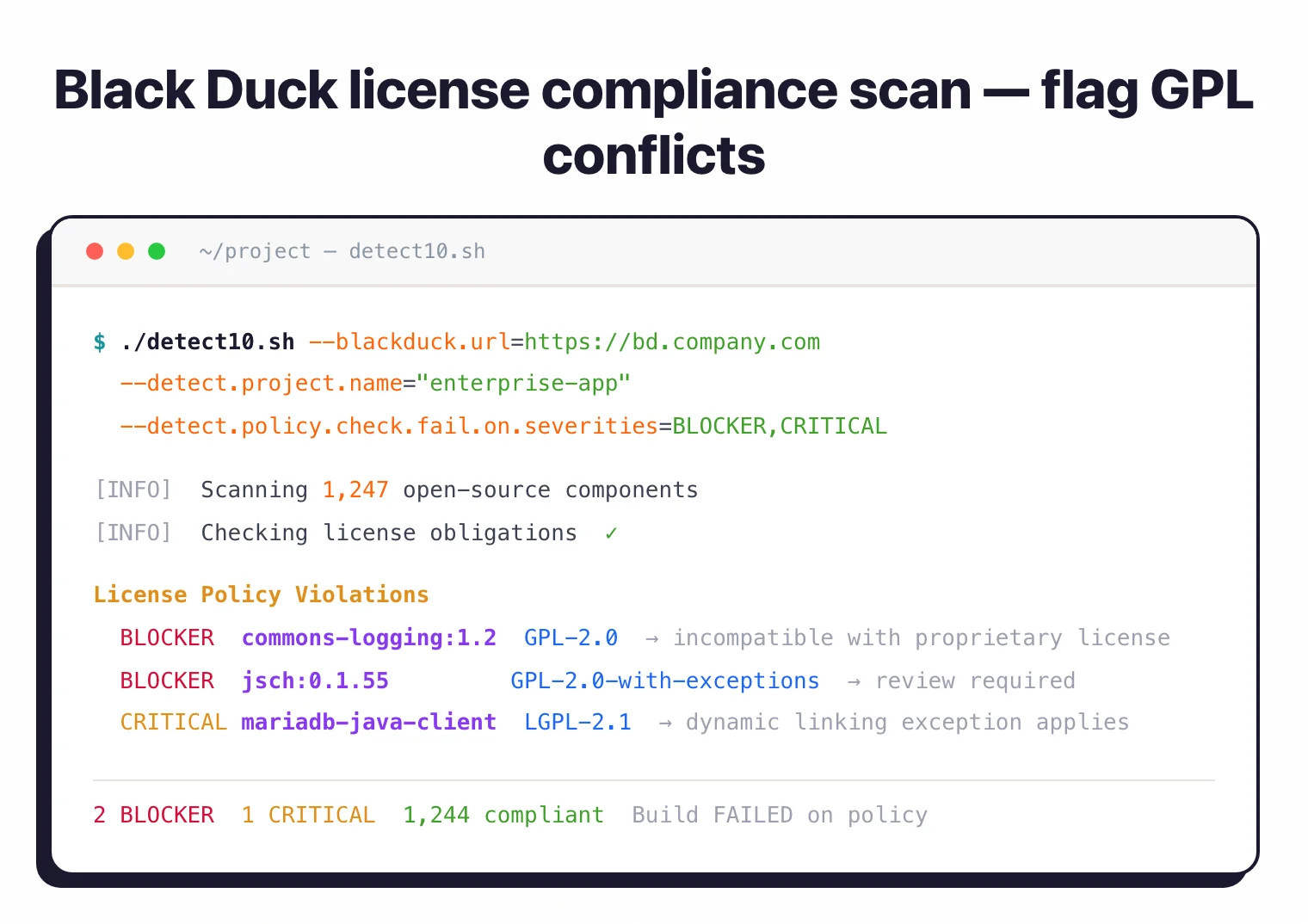
License compliance
License compliance is the part of Black Duck that competing SCA tools have the hardest time matching.
The platform identifies license types across your portfolio, flags conflicts (GPL components in proprietary software, for example), and generates attribution reports.
Custom policies let you define acceptable licenses per project or across the organization. Dual-licensed components are tracked with their commercial alternatives.
Container and binary analysis
Black Duck goes beyond source code.
It analyzes Docker images and OCI containers, scans compiled binaries without source access, and identifies components in firmware and embedded systems.
This matters for organizations that receive third-party software or need to verify what actually ships to production.
Black Duck Assist (AI)
Black Duck Assist uses AI to generate issue summaries, code analysis, and fix suggestions.
The goal is to cut triage time by giving engineers the context they would otherwise research by hand.
Setup
curl -O https://detect.blackduck.com/detect10.sh && chmod +x detect10.sh./detect10.sh --blackduck.url=https://your-server.com --blackduck.api.token=$TOKEN --detect.project.name="my-app"Black Duck Detect CLI
The primary integration method uses the Black Duck Detect CLI tool:
# Download and run Synopsys Detect
curl -O https://detect.blackduck.com/detect10.sh
chmod +x detect10.sh
# Run a scan
./detect10.sh \
--blackduck.url=https://your-blackduck-server.com \
--blackduck.api.token=$BLACKDUCK_API_TOKEN \
--detect.project.name="my-application" \
--detect.project.version.name="1.0.0"
Configuration Options
Create a application-blackduck.yml for reusable configuration:
blackduck:
url: https://your-blackduck-server.com
api:
token: ${BLACKDUCK_API_TOKEN}
detect:
project:
name: my-application
version:
name: ${BUILD_VERSION}
policy:
check:
fail:
on:
severities: BLOCKER,CRITICAL
risk:
report:
pdf: true
What does Black Duck integrate with?
GitHub Actions
name: Black Duck SCA
on:
push:
branches: [main]
pull_request:
branches: [main]
jobs:
blackduck-scan:
runs-on: ubuntu-latest
steps:
- name: Checkout code
uses: actions/checkout@v4
- name: Set up Java
uses: actions/setup-java@v4
with:
distribution: 'temurin'
java-version: '17'
- name: Run Black Duck Scan
uses: blackduck-inc/black-duck-security-scan@v2
with:
blackduck-url: ${{ secrets.BLACKDUCK_URL }}
blackduck-token: ${{ secrets.BLACKDUCK_API_TOKEN }}
blackduck-scan-full: true
blackduck-scan-failure-severities: 'BLOCKER,CRITICAL'
- name: Upload SBOM
if: always()
uses: actions/upload-artifact@v4
with:
name: sbom
path: '**/blackduck-sbom.*'
GitLab CI
stages:
- security
blackduck-scan:
stage: security
image: openjdk:17-slim
variables:
DETECT_LATEST_RELEASE_VERSION: "10"
script:
- apt-get update && apt-get install -y curl bash
- curl -O https://detect.blackduck.com/detect10.sh
- chmod +x detect10.sh
- ./detect10.sh
--blackduck.url=$BLACKDUCK_URL
--blackduck.api.token=$BLACKDUCK_API_TOKEN
--detect.project.name=$CI_PROJECT_NAME
--detect.project.version.name=$CI_COMMIT_REF_NAME
--detect.policy.check.fail.on.severities=BLOCKER,CRITICAL
--detect.risk.report.pdf=true
artifacts:
paths:
- "**/blackduck*.pdf"
expire_in: 30 days
rules:
- if: $CI_PIPELINE_SOURCE == "merge_request_event"
- if: $CI_COMMIT_BRANCH == $CI_DEFAULT_BRANCH
Jenkins Pipeline
pipeline {
agent any
environment {
BLACKDUCK_URL = credentials('blackduck-url')
BLACKDUCK_API_TOKEN = credentials('blackduck-api-token')
}
stages {
stage('Black Duck Scan') {
steps {
detect detectProperties: '''
--detect.project.name=${JOB_NAME}
--detect.project.version.name=${BUILD_NUMBER}
--detect.policy.check.fail.on.severities=BLOCKER,CRITICAL
'''
}
}
}
post {
always {
archiveArtifacts artifacts: '**/blackduck*.pdf', allowEmptyArchive: true
}
}
}
Black Duck deployment options
Black Duck ships in two deployment models: Black Duck SCA (self-hosted) and the Black Duck Polaris Platform (SaaS). The right choice usually comes down to data residency rules and how much operational overhead a security team can absorb.
Black Duck SCA (self-hosted). The traditional deployment. Installs on Linux or Kubernetes, typically on-premise or in a private VPC (legacy install scripts still reference the original bd-hub naming). Teams in finance, defense, and healthcare almost always pick this one because code metadata never leaves their network boundary.
Black Duck Polaris Platform (SaaS). The vendor-managed multi-tenant offering. Faster to stand up and removes the upgrade burden. Fits mid-market teams that would rather not run Java on Kubernetes.
Both deployments share the same KnowledgeBase, BDSA feed, and scanning engines. Feature parity is close enough that migration in either direction is mostly a data-export exercise.
How much does Black Duck cost?
Black Duck does not publish public pricing as of 2026. Quotes are sales-led and scale with the number of projects scanned, number of user seats, and deployment model (self-hosted Black Duck SCA or Black Duck Polaris Platform SaaS).
Public procurement records and aggregated buyer data point to annual contracts in the five- to six-figure range for mid-sized organizations. A tier comparable to Snyk Enterprise or FOSSA Enterprise is a reasonable starting assumption.
If cost is the main constraint and you only need CVE detection, a free tool like OWASP Dependency-Check or Grype handles the vulnerability half of the job without the license compliance or binary scanning.
BDSA vs NVD: why the advisory feed is the product
Black Duck Security Advisories (BDSAs) typically publish ahead of NVD enrichment for the same CVE, and some advisories never get a matching NVD entry at all.
The KnowledgeBase sits behind Black Duck, but the feature I care about is the Black Duck Security Advisory (BDSA) feed. Advisories are curated by the Cybersecurity Research Center (CyRC) and typically land in the KnowledgeBase well before the same CVE gets enriched in the NVD.
Black Duck publishes its own lead-time figures in the “Demonstrating the value of Black Duck Security Advisories” guide. Most BDSAs ship with full severity, impact, and exploitability detail ahead of the corresponding NVD-analyzed CVE, and a meaningful share of advisories never get a matching NVD entry at all (Black Duck, 2025 ). The specific per-quarter lead-time numbers live inside the gated PDF, so I am deliberately not citing them here; the directional claim (BDSAs lead NVD, often by weeks to months on high/critical findings) is what the public page stands behind.
The gap is not a vendor talking point. Imtiaz, Thorn, and Williams found large disagreements in what commercial SCA tools report for the same dependency set, with NVD-only feeds missing a meaningful portion of exploitable issues surfaced by curated feeds (Imtiaz et al., 2021 ).
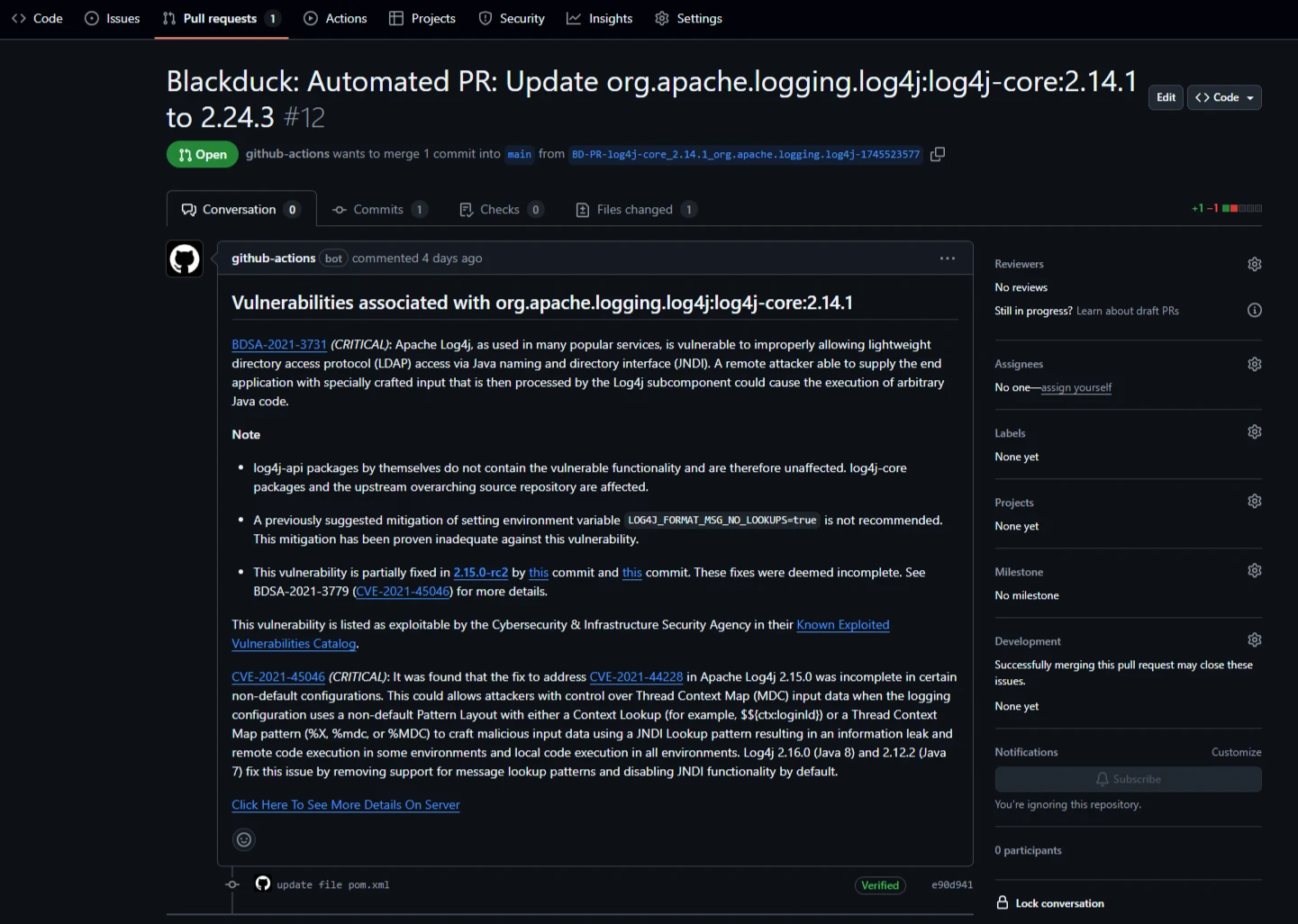
For a compliance-heavy shop where the security team must answer “when did you know?” to an auditor, the earlier timestamp on a BDSA is the defensible paper trail. Each advisory also ships a recommended upgrade path that avoids known breaking changes, which is the part Black Duck tooling actually uses to drive fix PRs and policy gates.
Binary Analysis (Protecode) is the real moat
Black Duck Binary Analysis (BDBA) scans shipped artifacts — ELF, Mach-O, Windows EXE/DLL, firmware images, and container layers — without requiring source code or a build manifest.
Most SCA tools need a manifest or lockfile. BDBA, which still carries the Protecode lineage from the 2017 acquisition, runs across Intel, ARM, PowerPC, MIPS, SPARC, PA-RISC, and AVR32 architectures, and also handles Java classes and Android DEX files (Black Duck BDBA docs ). Matching combines string extraction, metadata fingerprints, and fuzzy checksumming against the KnowledgeBase, so a vendor-supplied DLL or a stripped IoT firmware blob still resolves to concrete components and versions.
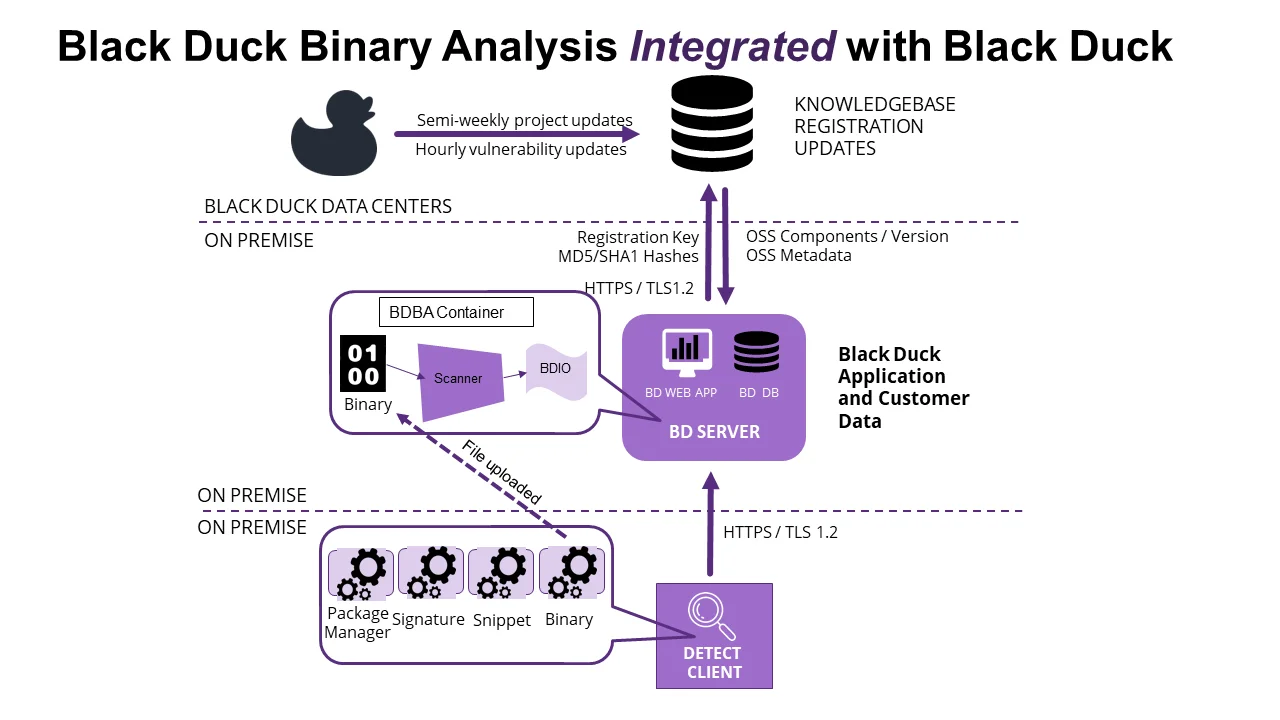
This is the reason Black Duck shows up in M&A due diligence, third-party risk reviews, and regulated-device portfolios. If the target has compiled artifacts but no buildable source, FOSSA and Snyk Open Source have almost nothing to scan. BDBA also flags embedded secrets and over-permissioned mobile manifests during the same pass, which matters for FDA, RED, and CRA submissions that need a component inventory for binaries the vendor did not build.
Academic work on binary SCA (Jiang et al.’s BinaryAI at ICSE 2024) confirms that fuzzy source-to-binary matching with a large curated index still beats pure learned approaches on recall for real-world dependency identification (Jiang et al., 2024 ). Black Duck’s index is exactly that: a KnowledgeBase of 10M+ OSS projects built up over two decades, which is hard to replicate from scratch.
For a head-to-head with the more developer-oriented alternative, see the dedicated Black Duck vs Snyk comparison .
License obligations beyond SPDX identifiers
Where most SCA tools stop at reporting an SPDX identifier, Black Duck’s license engine models copyleft contamination, tracks dual-licensed components, and evaluates compatibility across transitive dependency chains.
The license engine is the other piece that stays hard to copy. It covers the long tail of non-SPDX and custom licenses that show up in older OSS, alongside standard SPDX identifiers.
The obligation layer is where this pays off. An AGPL component linked into a SaaS product, a GPL-2.0 dependency pulled into a proprietary SDK, or a Commons Clause rider on an otherwise permissive package each triggers a distinct obligation with different legal exposure. Black Duck surfaces those as policy violations with attribution reports and notice files generated per release, which is the artifact outside counsel actually asks for in an open-source audit.
That depth is why Black Duck still wins bake-offs against lighter SCA tools in commercial-software-vendor procurement, even when the buyer already has a vulnerability scanner they like.
When to use Black Duck
Black Duck fits enterprises with large open-source portfolios where license compliance carries real legal consequences. The typical buyer is in healthcare, finance, or defense, doing M&A due diligence, or shipping commercial products built on top of open-source components.
Strengths:
- KnowledgeBase with 10M+ projects and 8.7M+ unique components from 57,700+ forges
- BDSAs provide earlier vulnerability intelligence than NVD
- Deep license compliance with attribution report generation
- Container and binary scanning beyond source code
- Two decades of enterprise deployments in regulated industries
Limitations:
- Commercial only, no free tier. For free alternatives, use OWASP Dependency-Check or Grype
- Heavier setup compared to developer-first tools like Snyk
- No automated fix PRs (pair with Renovate for dependency updates)








