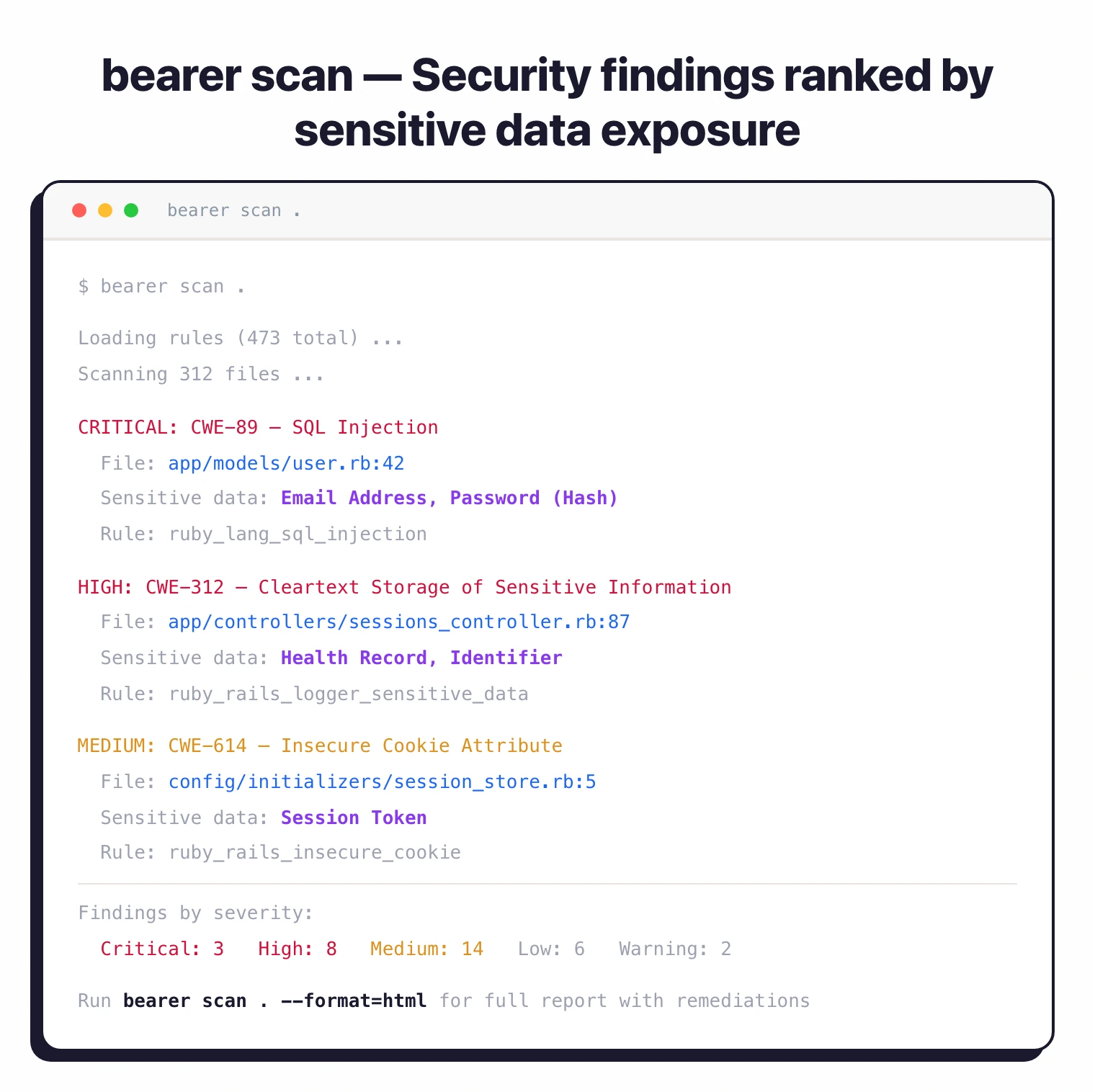
Bearer is an open-source SAST scanner that prioritizes vulnerabilities based on whether they expose sensitive user data — not just severity scores. It traces how personal, financial, and health information flows through application code, then re-ranks findings so the issues that actually put user data at risk surface first.
The CLI ships with 473 built-in security rules covering the OWASP Top 10 and CWE Top 25, detects 120+ sensitive data types, and supports seven languages: JavaScript, TypeScript, Ruby, Java, Go, Python, and PHP.
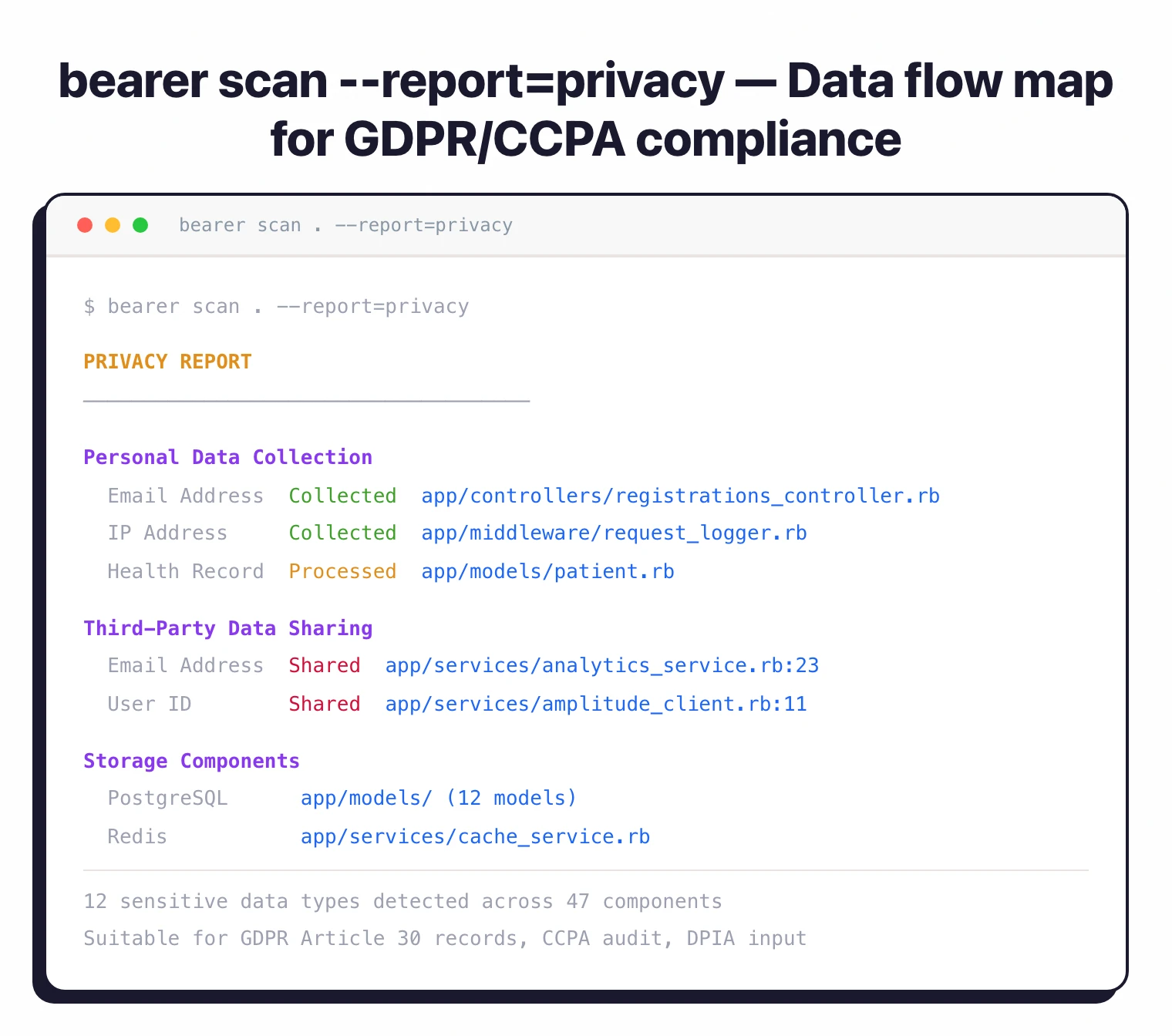
It also generates privacy reports alongside security findings — the only open-source SAST tool that does both.
Cycode acquired Bearer in April 2024. The CLI remains free under the Elastic License v2 (ELv2). Bearer Pro, available through the Cycode ASPM platform, adds cross-file and interprocedural analysis with support for additional languages including C#, Kotlin, and Elixir.
What is Bearer?
Bearer is a static application security testing (SAST) tool that scans source code for security vulnerabilities and privacy risks.
It differs from conventional SAST scanners by adding a sensitive data context layer: instead of treating every finding equally, Bearer identifies 120+ sensitive data types (PII, PHI, financial records) and traces how they flow through the application.
Findings that expose real user data get ranked higher than those affecting non-sensitive variables.
The scanner produces three report types from a single command. The security report covers vulnerabilities with CWE mappings and remediation guidance.
The privacy report maps how sensitive data gets collected, processed, and stored across the codebase — directly useful for GDPR, CCPA, and DPIA compliance audits. The data flow report provides a detailed breakdown for building data catalogs.
How does Bearer’s data flow analysis work?
Bearer’s core differentiator is sensitive data flow tracking. The scanner identifies where sensitive data enters the application (user input, API calls, database queries), traces how it moves through functions, and flags where it ends up (logs, external APIs, storage).
That data flow map is what powers both the security prioritization and the privacy reports.
The free CLI performs single-file data flow analysis. Bearer Pro, available through the Cycode ASPM platform, adds cross-file and interprocedural analysis — tracing data flows across function and file boundaries. On the OWASP Java Benchmark, Bearer Pro scored 76% with a false positive rate below 2%.
What security vulnerabilities does Bearer detect?
Bearer ships with 473 built-in security rules covering the OWASP Top 10, CWE Top 25, and language-specific patterns. The rules detect:
- SQL injection and NoSQL injection
- Cross-site scripting (XSS)
- Path traversal and file inclusion
- Insecure cryptography and hashing
- Hardcoded secrets and credentials
- Insecure HTTP configurations
- Broken access control
- Server-side request forgery (SSRF)
Each finding includes a description, severity rating (Critical, High, Medium, Low, Warning), CWE mapping, and remediation guidance.
What makes Bearer different: findings get re-ranked based on sensitive data exposure. A SQL injection that leaks user emails surfaces above one that exposes a non-sensitive counter variable.
Under the hood, Bearer combines rule-based pattern matching for CWEs with cross-file dataflow in source code. The 473 rules implement OWASP Top 10 and CWE Top 25 patterns; the dataflow engine traces sensitive data from source to sink and re-ranks findings by exposure rather than just severity.
How does Bearer generate privacy reports?
The privacy scanner detects 120+ sensitive data types in the codebase — emails, passwords, IP addresses, health records, financial data, biometric identifiers — and maps how each type flows through the application.
The output is a structured report that compliance teams can use during data protection audits for GDPR, CCPA, HIPAA, or DPIA assessments.
It runs alongside the security scan. One bearer scan command produces both security findings and privacy analysis. The separate --report=privacy flag generates the privacy-focused output, while --report=dataflow produces a detailed data flow breakdown suitable for building data catalogs.
Does Bearer detect secrets?
Bearer includes a secret detection mode powered by the Gitleaks engine. It catches hardcoded API keys, tokens, passwords, and credentials.
It covers common patterns without needing a separate scanner, though dedicated tools like GitGuardian or TruffleHog offer deeper coverage with historical commit scanning and real-time monitoring.
How do you install and run Bearer?
Bearer scans a typical codebase in 20 seconds to a few minutes depending on project size. Here is how to get started:
brew install bearer/tap/bearer), install script, Docker, or grab the binary from GitHub
.bearer scan . in your project directory. You get a prioritized security report in the terminal with findings ranked by sensitive data exposure.bearer scan . --report=privacy produces a data flow map showing how sensitive data gets collected, processed, and stored.bearer scan . --format=sarif outputs SARIF, which works with GitHub Code Scanning, GitLab SAST, and similar platforms. Bearer also supports diff-scanning for pull requests.What languages does Bearer support?
Bearer CLI (free) and Bearer Pro (Cycode) support different language sets:
| Language | Bearer CLI (Free) | Bearer Pro (Cycode) | Framework Coverage |
|---|---|---|---|
| JavaScript | Yes | Yes | Express, Fastify, Node.js |
| TypeScript | Yes | Yes | Same as JS + TS-specific patterns |
| Ruby | Yes | Yes | Rails, general Ruby |
| Java | Yes | Yes + cross-file | Spring, Jakarta, general Java |
| Go | Yes | Yes | Standard library, common frameworks |
| Python | Yes | Yes + cross-file | Django, Flask, general Python |
| PHP | Yes | Yes | Laravel, Symfony, general PHP |
| C# | — | Yes + cross-file (alpha) | .NET, ASP.NET |
| Kotlin | — | Yes | Android, Spring |
| Elixir | — | Yes | Phoenix, general Elixir |
| VB.Net | — | Yes | .NET |
What happened after Cycode acquired Bearer?
Cycode announced the acquisition in March 2024 and closed the deal on April 30, 2024 . Bearer’s scanning engine, privacy analysis capabilities, and engineering team all moved to Cycode.
The latest release is v2.0.1 (February 2026), showing continued active development.
The CLI stayed open source under ELv2. Cycode released it as part of their Cygives developer initiative, which also includes open-source tools like Raven and Cimon.
Bearer Pro — adding cross-file analysis, interprocedural tracing, and additional language support (C#, Kotlin, Elixir, VB.Net) — is only available through the Cycode ASPM platform.
When should you use Bearer?
Bearer makes the most sense for teams whose applications handle personal data, health records, or financial information.
The data-centric prioritization means developers spend less time wading through hundreds of generic findings to reach the ones that actually put user data at risk.
It also pairs well with other SAST tools. Running Semgrep for broad rule coverage and Bearer specifically for its privacy reports is a practical combination — no other open-source SAST scanner generates compliance-ready privacy reports.
How does Bearer compare to alternatives?
| Feature | Bearer CLI | Semgrep CE | SonarQube CE |
|---|---|---|---|
| License | ELv2 | LGPL-2.1 | LGPL-3.0 |
| Languages | 7 | 30+ | 17 |
| Security rules | 473 | 3,000+ community | 5,000+ |
| Data flow prioritization | Yes (sensitive data) | No | No |
| Privacy reports | Yes | No | No |
| Secret detection | Yes (Gitleaks) | Pro only | No |
| Cross-file analysis | Pro only | Pro only | Yes |
| SARIF output | Yes | Yes | Via plugin |
Bearer’s advantage is narrow but deep: sensitive data flow tracking and privacy reporting. If you need broader language coverage, Semgrep or SonarQube support more ecosystems. If you’re already on the Cycode ASPM platform, Bearer Pro gives you cross-file analysis, additional languages, and centralized findings management.