The OWASP Top 10 is the most widely referenced list of critical web application security risks, published by the Open Web Application Security Project based on vulnerability data from over 500,000 applications. This guide maps each OWASP Top 10 category to the specific SAST, DAST, SCA, and IAST tools that detect it, with a coverage matrix showing where automated scanning is strong and where manual review is still required.
What this guide covers
The OWASP Top 10 is the most widely referenced list of web application security risks. Published by the Open Web Application Security Project, it ranks the ten most critical risks based on data from hundreds of organizations and thousands of applications.
The current version was published in 2021 and reflects vulnerability data from over 500,000 applications. Most organizations treat it as the baseline for what their application security testing should catch.

Whether you are building a secure SDLC program or evaluating SAST, DAST, or SCA tools, the OWASP Top 10 is the starting point.
This guide maps each OWASP Top 10 item to the application security tool categories that detect it, with specific tool recommendations from our reviews of 215+ tools across 11 categories.
Which tools detect each OWASP Top 10 risk?
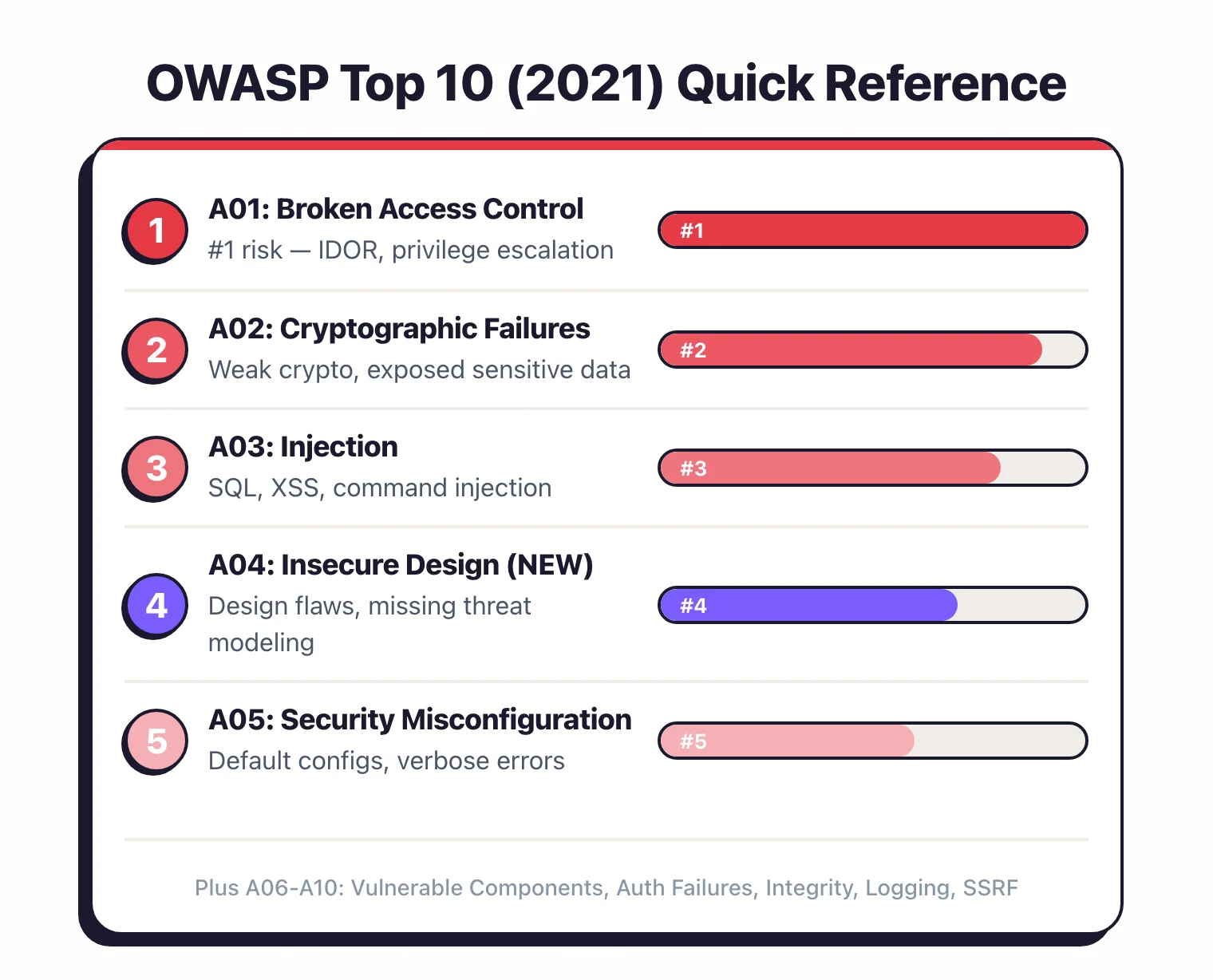
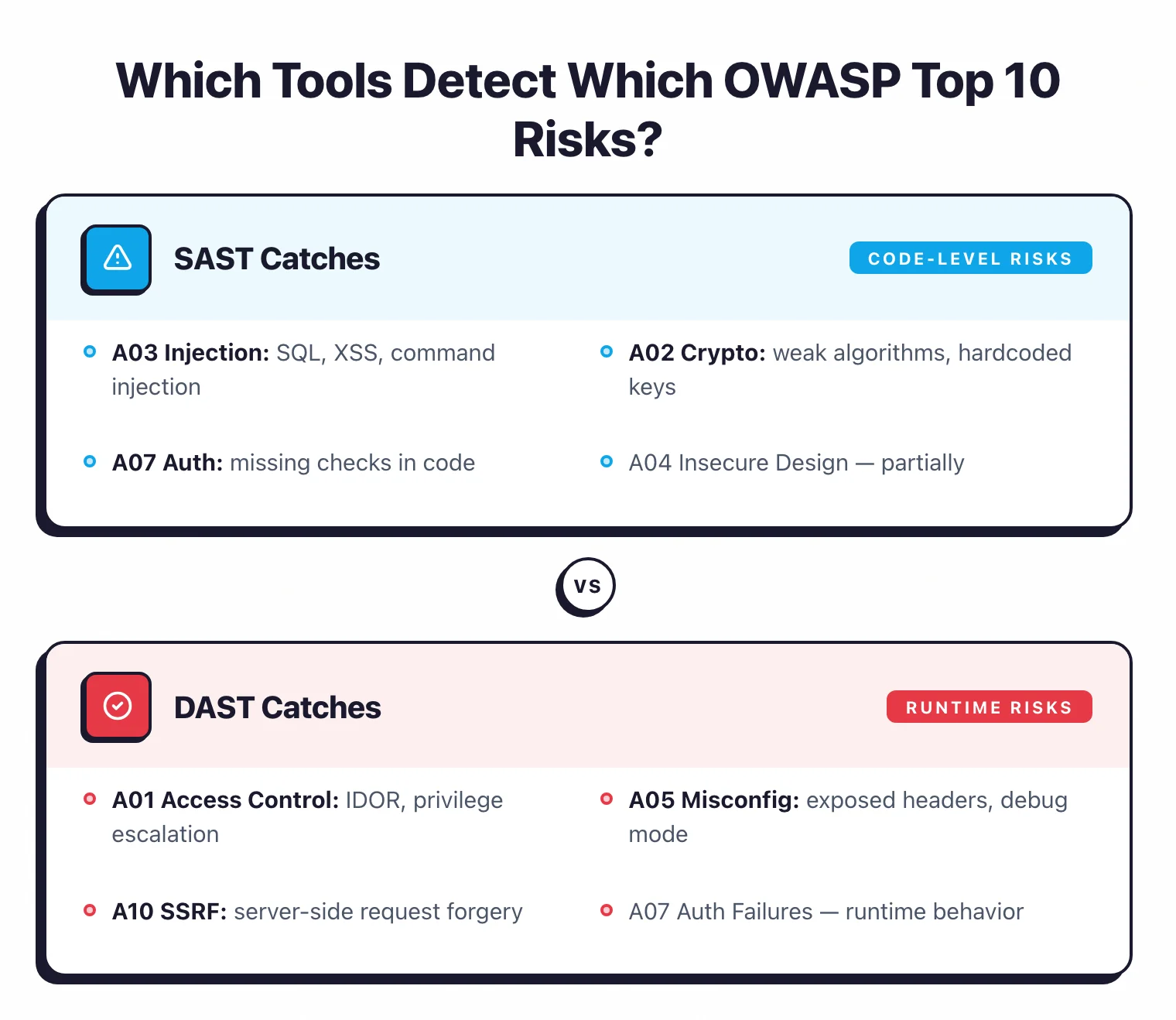
This matrix shows which tool categories provide meaningful detection for each OWASP Top 10 risk. “Strong” means the category is built to find this class of vulnerability. “Partial” means it catches some instances but not all.
| OWASP Top 10 Risk | SAST | DAST | SCA | IAST | RASP | IaC |
|---|---|---|---|---|---|---|
| A01: Broken Access Control | Partial | Strong | - | Strong | Strong | - |
| A02: Cryptographic Failures | Strong | Partial | Partial | Partial | - | Partial |
| A03: Injection | Strong | Strong | - | Strong | Strong | - |
| A04: Insecure Design | - | - | - | - | - | - |
| A05: Security Misconfiguration | Partial | Strong | - | Partial | - | Strong |
| A06: Vulnerable Components | - | - | Strong | - | - | Partial |
| A07: Authentication Failures | Partial | Strong | - | Strong | Strong | - |
| A08: Integrity Failures | Partial | - | Strong | - | - | Partial |
| A09: Logging Failures | Partial | - | - | Partial | - | - |
| A10: SSRF | Strong | Strong | - | Strong | Strong | - |
The bottom line: no single tool category covers all ten risks. You need at least SAST + DAST + SCA for broad coverage.
Adding IAST gives you runtime visibility that fills several remaining gaps. For production-time protection, RASP tools block exploitation attempts in real time.
Teams managing multiple tool outputs should consider an ASPM platform to correlate findings across categories.
Pick your next step
I want SAST tools that detect OWASP Top 10
Browse reviewed SAST scanners that catch injection (A03), crypto failures (A02), and SSRF (A10) in source code before deploy.
→Get a SAST head-to-head
Gitleaks vs TruffleHog benchmark for secret scanning — the A02 cryptographic-failure side of the matrix above.
→All AppSec tools
The full directory of reviewed application security tools across SAST, DAST, SCA, IAST, RASP, and IaC categories.
→A01: Broken Access Control
Users acting outside their intended permissions: accessing other users’ data, modifying access rights, bypassing access checks. This was #5 in 2017 and moved to #1 in 2021.
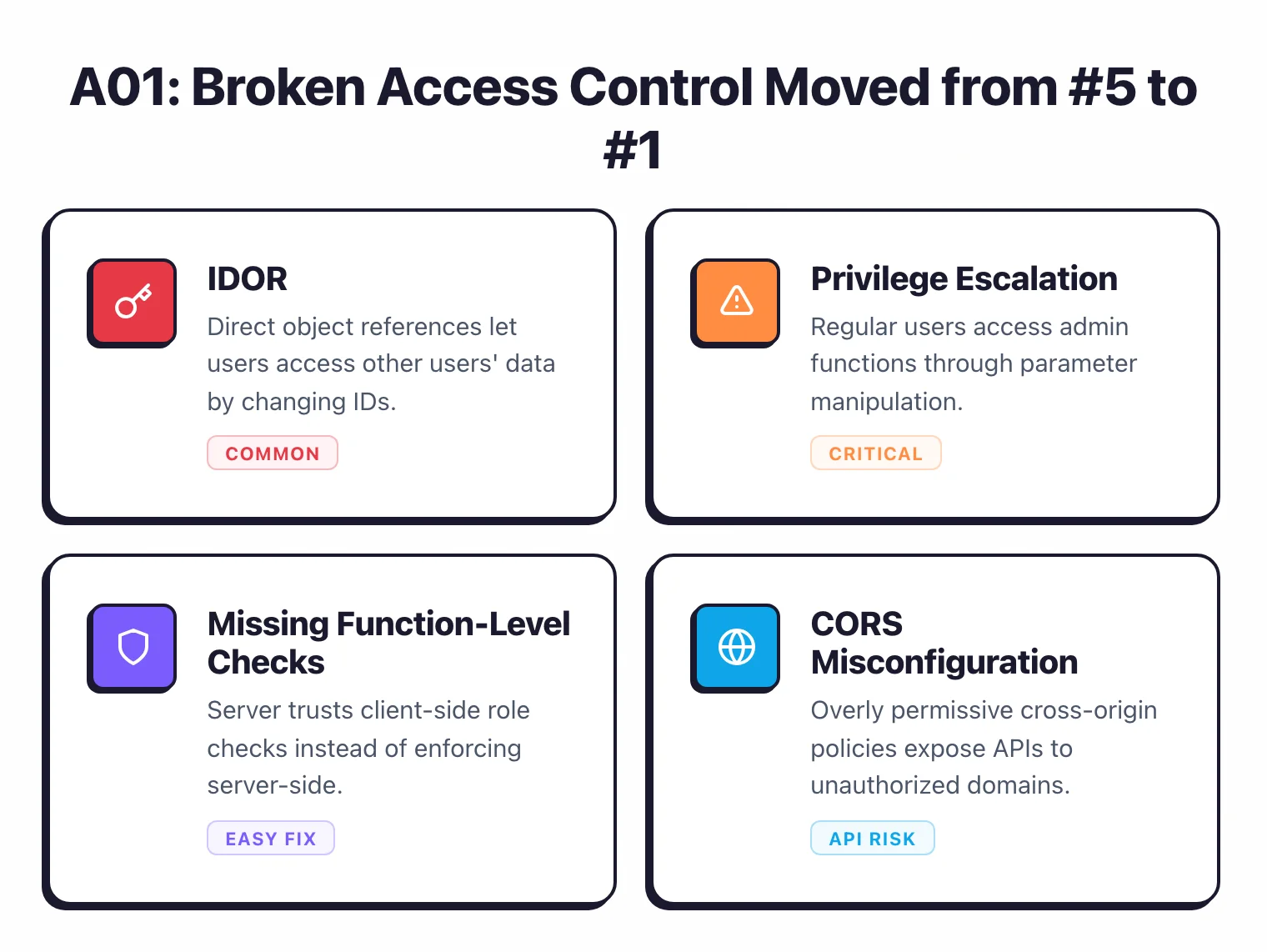
In the OWASP data set, 94% of applications were tested for broken access control CWEs, and it had the most total occurrences of any category with over 318,000 instances.
Access control is business logic, which makes it hard to test automatically. A tool can see that an endpoint returns data, but it has no way to know whether this user should see that data without understanding the authorization model.
Which tools detect it
DAST tools are your primary automated defense. They test for insecure direct object references (IDOR) by manipulating request parameters and checking if the application returns unauthorized data.
- Burp Suite - The Autorize extension specifically tests for access control bypasses
- ZAP - Access control testing via the Access Control Testing add-on
- Invicti - Automated access control checks with proof-based scanning
- Nuclei - Community templates for common IDOR patterns
IAST tools instrument the application at runtime and can observe authorization checks (or their absence) as requests are processed.
- Contrast Security - Detects missing access control checks in real time
- Seeker IAST - Monitors authorization patterns during testing
RASP tools block unauthorized access attempts in production, acting as a safety net.
- Contrast Protect - Runtime blocking of access control violations
- Imperva RASP - Application-level access enforcement
SAST tools provide limited but useful coverage here by detecting hardcoded roles, missing authorization annotations, and absent access control checks in common frameworks.
A02: Cryptographic Failures
Failures related to cryptography that expose sensitive data: weak algorithms (MD5, SHA1 for passwords), hardcoded keys and secrets, missing encryption for data in transit or at rest, improper certificate validation. Previously called “Sensitive Data Exposure” in the 2017 list.
Which tools detect it
SAST tools are the strongest category for catching cryptographic issues in source code.
- Semgrep - Rules for weak crypto, hardcoded secrets, insecure TLS configurations
- Checkmarx - Deep analysis of cryptographic API usage across 35+ languages
- SonarQube - Built-in rules for weak hashing, insecure random number generation
- Bandit - Python-specific checks for insecure crypto usage
- Fortify - Broad crypto vulnerability detection
DAST tools catch exposed data in transit: missing HTTPS, weak TLS versions, certificate issues.
- Invicti - TLS configuration analysis, mixed content detection
- ZAP - SSL/TLS scanning, cookie security flags
- Nikto - Server-level crypto misconfiguration checks
SCA tools can also flag libraries with known cryptographic vulnerabilities.
A03: Injection
Untrusted data sent to an interpreter as part of a command or query. SQL injection, NoSQL injection, OS command injection, LDAP injection, and cross-site scripting (XSS) all fall here.

Injection dropped from #1 (2017) to #3 (2021) as frameworks with built-in protections became standard.
Which tools detect it
This vulnerability class has the broadest tool coverage of any OWASP item. Nearly every scanning category can detect some form of injection.
SAST tools trace data flow from user input to dangerous sinks (database queries, system commands, HTML output).
- Checkmarx - Strong taint analysis for injection paths
- Veracode Static Analysis - Binary-level analysis catches injection in compiled code
- Semgrep - Pattern-based rules for common injection patterns
- Fortify - Data flow analysis across function boundaries
- Snyk Code - Real-time injection detection in IDEs
DAST tools actively probe running applications with injection payloads.
- Burp Suite - Active scanner with thorough injection testing
- ZAP - Active and passive injection scanning
- Invicti - Proof-based injection verification with confirmed exploitation
- Nuclei - Community templates for injection testing
- Acunetix - DeepScan technology for JavaScript-heavy applications
IAST tools observe injection in real time by watching how the application processes tainted data.
- Contrast Security - Detects injection at the point of exploitation
- Seeker IAST - Runtime injection monitoring
RASP tools block injection attempts in production.
- Contrast Protect - Blocks SQLi and XSS at runtime
- Imperva RASP - Virtual patching for injection vulnerabilities
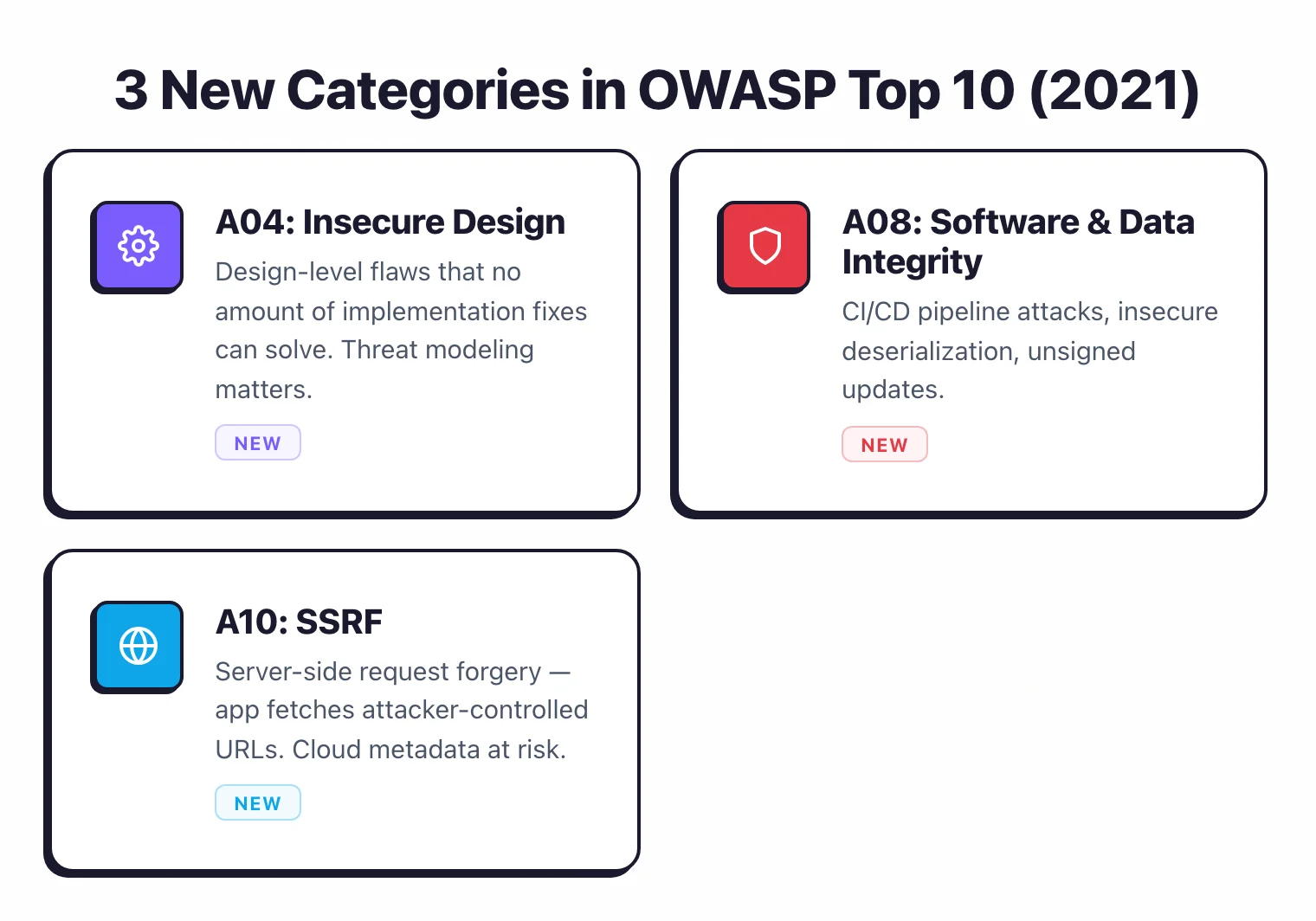
A04: Insecure Design
New in 2021. This covers flaws in the design and architecture of an application, not implementation bugs.
Missing security controls, business logic flaws, failure to think through attack scenarios.
Which tools detect it
Automated tools have almost no coverage here. This is a human problem.
Insecure design means the application was built without adequate threat modeling. No scanner can detect that a password reset flow lacks rate limiting if nobody specified rate limiting in the design.
No SAST tool can flag that an e-commerce checkout allows negative quantities if the business logic was never defined.
What actually helps:
- Threat modeling during the design phase (tools like Microsoft Threat Modeling Tool, OWASP Threat Dragon)
- Security architecture reviews before implementation starts
- Abuse case testing where QA specifically tries to misuse features
- Security champions on development teams who think about threat patterns
Some ASPM tools like ArmorCode, Apiiro, and Invicti ASPM provide risk scoring that can flag applications lacking security controls, but this is a proxy indicator, not direct detection.
A05: Security Misconfiguration
Insecure defaults, incomplete configurations, open cloud storage, misconfigured HTTP headers, verbose error messages, unnecessary services left enabled. This was #6 in 2017 and moved to #5 in 2021.
Which tools detect it
DAST tools are well suited for finding misconfigurations in deployed applications.
- Invicti - Checks server headers, TLS configuration, error handling
- ZAP - Passive scanning for misconfigured headers, cookies, CORS
- Nikto - Server-level misconfiguration detection
- Nuclei - Thousands of templates for common misconfigurations
IaC Security tools catch misconfigurations before deployment by scanning infrastructure code.
- Checkov - Terraform, CloudFormation, Kubernetes policy checks
- Trivy - Container and IaC misconfiguration scanning
- Terrascan - Multi-cloud infrastructure policy enforcement
- KICS - Broad IaC misconfiguration detection
- Snyk IaC - IaC scanning integrated with Snyk platform
SAST tools offer partial coverage for application-level misconfigurations like debug modes, verbose logging, and insecure framework settings.
A06: Vulnerable and Outdated Components
Using libraries, frameworks, or OS packages with known vulnerabilities. Also covers components that are no longer maintained or running outdated versions.
Which tools detect it
SCA tools exist specifically for this risk. This is the one OWASP Top 10 category where a single tool category provides near-complete coverage.
- Snyk Open Source - Real-time dependency scanning with fix PRs
- Trivy - Container image and filesystem SCA (31,700 GitHub stars)
- Grype - Fast vulnerability matching against SBOM
- OWASP Dependency-Check - Mature, Java-focused SCA
- Renovate - Automated dependency updates (20,700 GitHub stars)
- Dependabot - GitHub-native dependency updates
- Mend SCA - Commercial SCA with license compliance
- Veracode SCA - SCA integrated with Veracode platform
- Sonatype Lifecycle - Policy-driven component governance
See our full SCA tools category for all 23 options.
A07: Identification and Authentication Failures
Weaknesses in authentication and session management: weak passwords, credential stuffing exposure, improper session handling, missing multi-factor authentication. Previously called “Broken Authentication” in the 2017 list.
Which tools detect it
DAST tools actively test authentication mechanisms in running applications.
- Burp Suite - Session management testing, authentication bypass checks
- ZAP - Authentication and session management scanning
- Invicti - Login flow analysis and session security testing
- Acunetix - Automated authentication testing
IAST and RASP tools monitor authentication flows at runtime.
- Contrast Security - Detects insecure session management in real time
- Imperva RASP - Runtime protection against credential attacks
SAST tools provide partial coverage by catching hardcoded credentials, weak password validation logic, and insecure session configuration in code.
A08: Software and Data Integrity Failures
New in 2021. Covers code and infrastructure that fails to protect against integrity violations: insecure CI/CD pipelines, auto-update mechanisms without integrity verification, and insecure deserialization (which had its own category in 2017).
Which tools detect it
SCA tools verify that dependencies have not been tampered with and detect dependency confusion attacks.
- Socket - Supply chain attack detection, malicious package identification
- Snyk Open Source - Dependency integrity checks
- Sonatype Lifecycle - Component authenticity verification
SAST tools detect insecure deserialization patterns in code.
- Checkmarx - Deserialization vulnerability detection
- Fortify - Insecure deserialization analysis
- Semgrep - Custom rules for deserialization patterns
IaC tools can verify CI/CD pipeline security configurations.
A09: Security Logging and Monitoring Failures
Insufficient logging, detection, monitoring, and active response. Without proper logging, breaches go undetected. Was #10 in 2017, moved up to #9 in 2021.
Which tools detect it
This category has the weakest automated tool coverage of any OWASP item. Most scanners simply do not evaluate whether an application logs security events correctly.
SAST tools provide limited detection by checking for missing logging calls around security-sensitive operations (authentication, authorization, input validation).
IAST tools can observe whether the application generates appropriate log entries during security testing.
What actually helps:
- SIEM (Security Information and Event Management) solutions
- Application Performance Monitoring (APM) tools
- Log aggregation platforms (ELK Stack, Datadog, Splunk)
- Manual code reviews focused on security logging completeness
A10: Server-Side Request Forgery (SSRF)
SSRF happens when a web application fetches a remote resource without validating the user-supplied URL.
Attackers use this to force the application to make requests to internal services, cloud metadata APIs, or other places it should not be talking to.
New to the OWASP Top 10 in 2021, added based on the community survey.
Which tools detect it
SAST tools trace user-controlled data into URL-building and HTTP-request functions.
- Semgrep - SSRF rules for common HTTP client libraries
- Checkmarx - Data flow analysis for URL manipulation
- Snyk Code - SSRF pattern detection
- Fortify - Taint analysis for SSRF paths
DAST tools probe applications with payloads designed to trigger SSRF.
- Burp Suite - Burp Collaborator for out-of-band SSRF detection
- ZAP - SSRF scanning with OAST (Out-of-band Application Security Testing)
- Invicti - Proof-based SSRF verification
- Nuclei - SSRF templates targeting common patterns
IAST and RASP tools observe or block SSRF at runtime.
- Contrast Security - Real-time SSRF detection and blocking
How do you build complete OWASP Top 10 coverage?
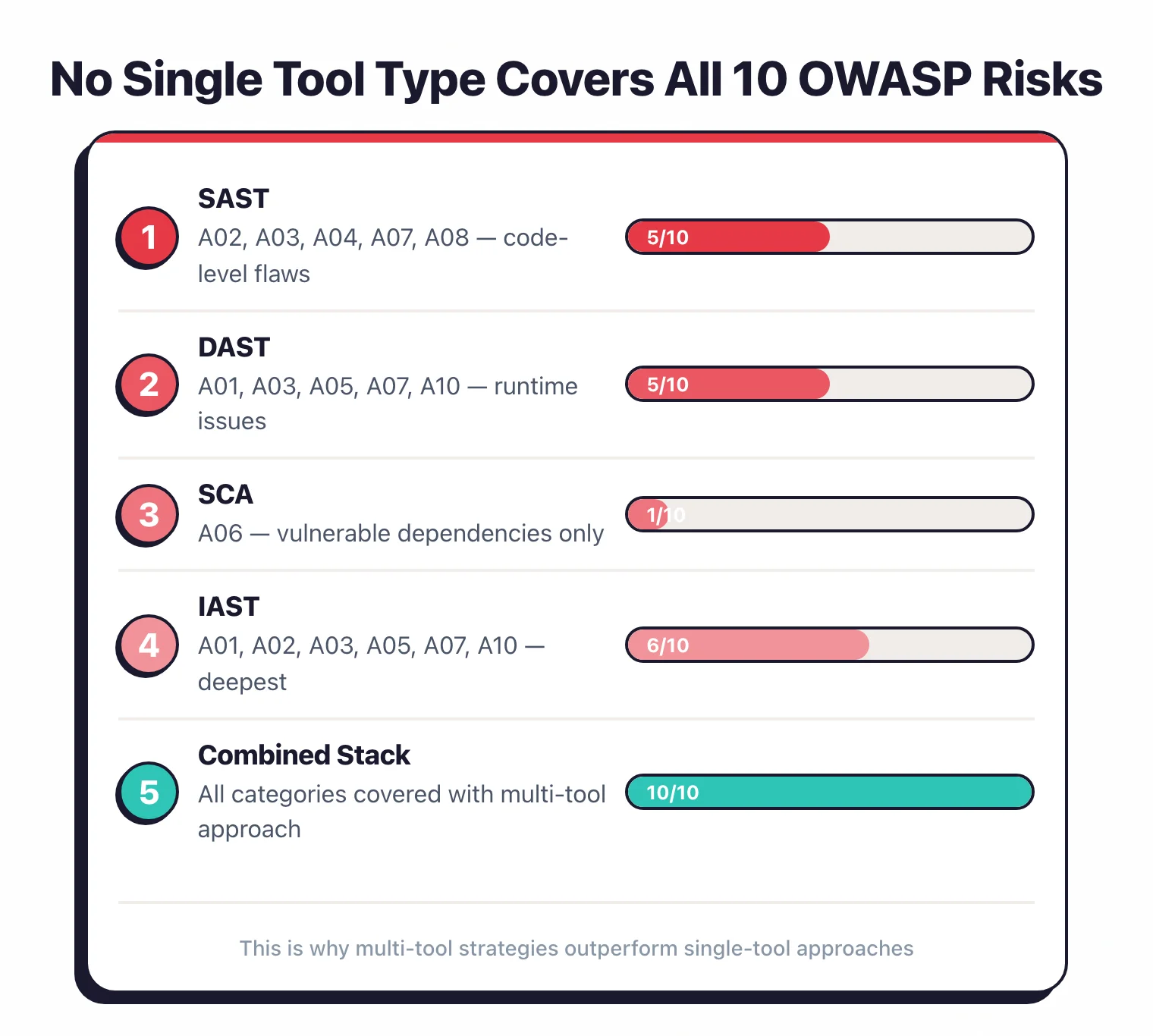
Using the coverage matrix above, here is how to build layered detection across the OWASP Top 10.
Minimum viable stack (3 tool categories)
- SAST - Covers A02, A03, A10 strongly; partial coverage for A01, A05, A07, A08, A09
- DAST - Covers A01, A03, A05, A07, A10 strongly; partial coverage for A02
- SCA - Covers A06, A08 strongly
This three-layer approach provides meaningful detection for 8 of 10 OWASP categories. A04 (Insecure Design) and A09 (Logging Failures) remain largely manual.
Recommended tool combinations
Free stack: Semgrep CE + ZAP + Trivy
Mid-market stack: Snyk Code + Snyk Open Source + StackHawk
Enterprise stack: Checkmarx One + Invicti + Contrast Security
For a deeper look at how these tool categories work together across the development lifecycle, see the Secure SDLC guide. AppSec Santa’s application security tools page provides reviews across all categories referenced in this matrix.
Which Tools Detect Each OWASP Top 10 Vulnerability?
The table below maps each OWASP Top 10 category to the specific tools that provide detection. Every tool listed here has been reviewed on AppSec Santa.
For tool categories where automated detection is weak, we note the manual practices that fill the gap.
| OWASP Category | Primary Tools | Tool Category |
|---|---|---|
| A01: Broken Access Control | ZAP, Burp Suite, Invicti, Contrast Security | DAST, IAST |
| A02: Cryptographic Failures | Semgrep, SonarQube, Checkmarx, Bandit | SAST |
| A03: Injection | Semgrep, Bandit, ZAP, Nuclei, Burp Suite | SAST, DAST |
| A04: Insecure Design | Threat modeling, security architecture review | Manual |
| A05: Security Misconfiguration | Checkov, KICS, Trivy, ZAP, Nuclei | IaC Security, DAST |
| A06: Vulnerable Components | Trivy, Grype, Snyk Open Source, FOSSA | SCA |
| A07: Auth Failures | Burp Suite, ZAP, Invicti, Contrast Security | DAST, IAST |
| A08: Integrity Failures | Syft, Dependency-Track, Snyk Open Source, Checkov | SCA, IaC Security |
| A09: Logging Failures | Falco, runtime monitoring, SIEM integration | RASP, Manual |
| A10: SSRF | ZAP, Burp Suite, Nuclei, Semgrep | DAST, SAST |
A01: Broken Access Control — Tool Recommendations
Broken access control is the #1 web application security risk according to the 2021 OWASP data set, with the most total occurrences of any category across over 318,000 instances.
Detection requires tools that can test authorization boundaries at runtime. DAST tools like ZAP and Burp Suite test for insecure direct object references by manipulating request parameters and verifying whether the application returns unauthorized data. Invicti automates proof-based scanning that confirms access control bypasses without false positives.
On the IAST side, Contrast Security instruments the application to observe authorization checks as requests flow through the code, catching missing access control enforcement that scanners miss.
SAST tools offer partial coverage by detecting missing authorization annotations in frameworks like Spring Security and Django. For production protection, RASP tools block unauthorized access attempts in real time.
A02: Cryptographic Failures — Tool Recommendations
Cryptographic failures encompass weak algorithms, hardcoded secrets, missing encryption, and improper certificate validation. SAST tools are the strongest category here because they analyze source code for insecure cryptographic patterns before the code ships.
Semgrep provides community-maintained rules that flag weak hashing algorithms like MD5 and SHA1 used for passwords, hardcoded API keys, and insecure TLS configurations. SonarQube includes built-in rules for weak random number generation and deprecated crypto APIs. Checkmarx performs deep analysis of cryptographic API usage across 35+ languages, tracing how keys and secrets flow through the application.
For Python projects specifically, Bandit catches insecure crypto usage patterns like hashlib.md5() calls.
DAST tools complement SAST by verifying encryption in transit: ZAP and Invicti check TLS versions, certificate validity, and mixed content issues on deployed applications.
A03: Injection — Tool Recommendations
Injection has the broadest automated tool coverage of any OWASP Top 10 item.
Both SAST and DAST tools provide strong detection because injection vulnerabilities follow predictable data flow patterns: user input reaches a dangerous sink like a SQL query or OS command without sanitization.
On the SAST side, Semgrep matches injection patterns using lightweight rules that run in seconds, while Bandit covers Python-specific injection risks including SQL injection through string formatting and OS command injection via subprocess.
For runtime testing, ZAP and Nuclei actively probe running applications with injection payloads targeting SQL, XSS, LDAP, and command injection. Burp Suite provides the deepest manual testing capability with its active scanner and intruder tool.
IAST tools like Contrast Security observe injection at the point of exploitation, confirming true positives with near-zero false positive rates.
A04: Insecure Design — Approach
Insecure design cannot be detected by automated scanning tools. It covers architectural flaws, missing security controls, and business logic errors that exist because nobody considered the threat during the design phase.
No scanner can flag that a checkout flow allows negative quantities if the specification never required quantity validation. The primary defenses are threat modeling during design, security architecture reviews before implementation, and abuse case testing during QA.
Some ASPM tools like ArmorCode and Apiiro provide risk scoring that can highlight applications lacking certain security controls, but this is a proxy signal rather than direct detection.
Teams that invest in threat modeling using frameworks like STRIDE or PASTA catch insecure design issues before they become code.
Security champions embedded in development teams help bridge this gap by raising threat patterns during design discussions and sprint planning.
A05: Security Misconfiguration — Tool Recommendations
Security misconfiguration spans insecure defaults, open cloud storage, misconfigured HTTP headers, verbose error messages, and unnecessary services.
Two tool categories share primary responsibility. IaC Security tools catch misconfigurations before deployment by scanning infrastructure-as-code templates: Checkov enforces policies across Terraform, CloudFormation, and Kubernetes manifests.
KICS covers 22+ IaC platforms with over 2,400 queries. Trivy combines container scanning with IaC misconfiguration detection in a single binary.
On the runtime side, DAST tools verify deployed configurations: ZAP passively scans for missing security headers, insecure cookies, and CORS misconfigurations. Nuclei has thousands of community templates targeting specific misconfigurations in web servers, cloud services, and network devices.
Teams should run IaC scans in CI pipelines and DAST scans against staging environments to catch misconfigurations at both layers.
A06: Vulnerable Components — Tool Recommendations
Vulnerable and outdated components represent the one OWASP Top 10 category where a single tool category provides near-complete coverage. SCA tools scan your dependency manifests, lock files, and container images against vulnerability databases like the NVD and GitHub Advisory Database.
Trivy scans container images, filesystems, and git repositories for known CVEs in both OS packages and application dependencies. Grype matches vulnerabilities against software bill of materials (SBOM) generated by Syft, making it ideal for container-heavy workflows.
Snyk Open Source monitors dependencies continuously and generates fix pull requests with version upgrades or patches. FOSSA adds license compliance to vulnerability scanning, important for organizations managing open source risk.
For automated remediation, Renovate and Dependabot create dependency update PRs on a configurable schedule. See our complete SCA tools comparison for all options.
A07: Authentication Failures — Tool Recommendations
Authentication and session management weaknesses require runtime testing because these flaws manifest in how the application handles login flows, session tokens, password policies, and multi-factor authentication.
DAST tools are the primary detection category: Burp Suite tests session management by analyzing cookie attributes, session fixation, and authentication bypass vectors. ZAP includes authentication scanning with support for form-based, JSON-based, and script-based login sequences. Invicti analyzes login flow security and tests for common authentication weaknesses automatically.
On the IAST side, Contrast Security monitors authentication flows at runtime, detecting insecure session configuration, missing secure cookie flags, and weak password hashing as the application processes real requests.
SAST tools provide partial coverage by flagging hardcoded credentials and weak password validation regex patterns in source code.
A08: Software and Data Integrity Failures — Tool Recommendations
This category covers supply chain attacks, insecure CI/CD pipelines, and insecure deserialization. SCA tools and SBOM generators are the primary defense against software supply chain threats.
Syft generates accurate software bills of materials from container images and filesystems, establishing a baseline inventory of what is deployed. Dependency-Track consumes SBOMs and continuously monitors them against new vulnerability disclosures, providing policy-based governance. Snyk Open Source detects dependency confusion attacks and verifies package integrity.
For CI/CD pipeline security, Checkov scans GitHub Actions workflows and pipeline configurations for insecure patterns like untrusted code execution and missing approval gates.
SAST tools like Checkmarx and Semgrep detect insecure deserialization patterns in code, covering the deserialization attack vector that was a standalone OWASP category in 2017.
A09: Security Logging and Monitoring Failures — Tool Recommendations
Logging and monitoring failures have the weakest automated tool coverage of any OWASP Top 10 category.
Most scanning tools do not evaluate whether an application logs security events correctly. Falco fills part of this gap at the runtime layer by monitoring system calls and detecting anomalous behavior in containers and Kubernetes clusters, alerting when unexpected processes execute or sensitive files are accessed.
Some RASP tools like Contrast Protect log security events at the application layer, including blocked attacks and suspicious request patterns.
Beyond tooling, this category requires SIEM platforms (Splunk, Datadog, ELK Stack) to aggregate and correlate security logs, plus application-level instrumentation that explicitly logs authentication events, authorization failures, and input validation exceptions.
Security teams should verify logging coverage through manual code review and penetration testing that specifically checks whether attack attempts generate detectable alerts.
A10: Server-Side Request Forgery — Tool Recommendations
SSRF vulnerabilities allow attackers to force an application to make requests to internal services, cloud metadata endpoints, or other unintended destinations.
Both DAST and SAST tools provide strong detection. ZAP tests for SSRF using out-of-band application security testing (OAST) techniques that detect when the target application makes DNS or HTTP requests to attacker-controlled endpoints.
Burp Suite uses its Collaborator server for the same purpose, catching blind SSRF variants where no response data is returned to the user. Nuclei includes community templates targeting SSRF in common web frameworks, cloud provider metadata endpoints, and internal service discovery.
On the SAST side, Semgrep traces user-controlled data into URL construction and HTTP request functions, flagging potential SSRF before the code is deployed.
IAST tools like Contrast Security observe SSRF at runtime by monitoring outbound HTTP requests from the application.
