Arnica is a pipelineless SCA platform that delivers security scanning without CI/CD pipeline integration.
Install it as a GitHub or GitLab app and it continuously monitors repositories for vulnerable dependencies, hardcoded secrets, and developer risk patterns.
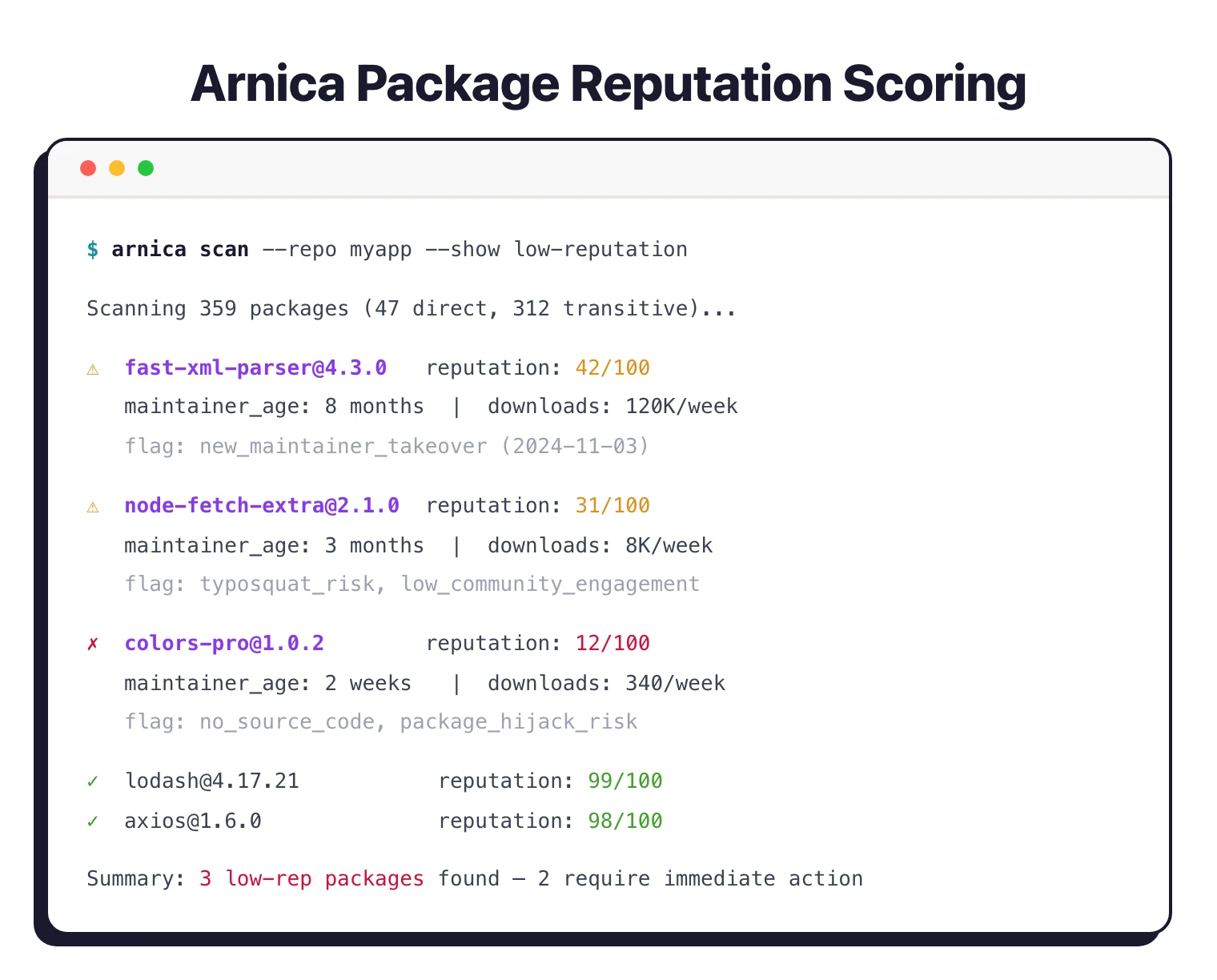
With the Sonatype 2026 State of the Software Supply Chain report framing open-source malware as “a nation-state business model,” Arnica’s package reputation scoring adds a layer of defense that CVE databases alone cannot provide.
Arnica’s package reputation scoring evaluates dependencies beyond CVE databases, factoring in maintainer trustworthiness, download patterns, and community signals. Reachability analysis then filters out vulnerabilities in code paths your application never calls.
What is Arnica?
Traditional SCA tools require pipeline integration, adding complexity and slowing builds. Arnica operates at the repository level instead.
Once installed as a GitHub App or GitLab integration, it scans continuously in the background with results appearing directly in pull requests.
Key features
Supported platforms and ecosystems
| Category | Coverage |
|---|---|
| SCM platforms | GitHub, GitLab, Bitbucket, Azure DevOps |
| JavaScript | npm, yarn, pnpm |
| Python | pip, Poetry |
| Java | Maven, Gradle |
| Go | Go modules |
| .NET | NuGet |
| Ruby | Bundler |
| Containers | Docker images |
Pipelineless architecture
Arnica connects to your SCM as a native app. No CI/CD changes, no pipeline modifications, no build slowdowns. Results appear in pull requests and the Arnica dashboard.
Package reputation scoring
Beyond CVE scanning, Arnica evaluates packages based on maintainer reputation, account age, download velocity, dependency patterns, and community engagement. New packages from unknown maintainers get lower scores, flagging supply chain risks before any vulnerability is disclosed.
Reachability analysis
Arnica traces code paths to determine whether vulnerable functions are reachable from your application entry points. A vulnerable function buried in dead code scores lower than one called directly from your API handlers.
Hardcoded secrets detection
Scans for API keys, credentials, tokens, and other secrets committed to repositories. Covers AWS keys, database passwords, JWT secrets, and custom patterns. Historical scanning catches secrets in old commits.
Developer risk profiling
Analyzes developer behavior patterns: commit frequency, code ownership, access patterns, and security violation history. Helps security teams identify where additional training or code review is needed.
Automated remediation
When Arnica finds vulnerabilities with available fixes, it creates pull requests with dependency upgrades including vulnerability details and breaking change warnings.
Transitive dependency analysis
Arnica’s SBOM inventory walks the full dependency graph rather than stopping at direct imports. Transitive packages inherit their own CVE, license, and reputation signals, so a vulnerable library pulled in two levels deep still shows up in the risk view.
Dependency update automation
Arnica creates automated pull requests for upgradeable dependencies and overlaps with Dependabot- and Renovate-style workflows. Each PR carries the CVE and breaking-change context from the same scan — teams using Arnica as the primary SCA typically turn Dependabot off to avoid duplicate update PRs on the same repo.
Installation
Arnica installs as a native app on your source code platform:
GitHub Setup
- Navigate to GitHub Marketplace: Arnica
- Click “Install” and select repositories to monitor
- Authorize requested permissions
- Configure in the Arnica dashboard
GitLab Setup
- Log into Arnica and navigate to Integrations
- Select GitLab and authorize OAuth access
- Choose groups and projects to monitor
- Enable desired scanning features
Local Testing
Arnica primarily operates through its GitHub/GitLab app integration. For local testing and CI/CD workflows, use Arnica’s webhook-based triggers or the dashboard API. See the Arnica documentation for current integration options.
Configuration
Configure Arnica behavior through the dashboard or repository config file:
# .arnica.yml in repository root
version: 1
sca:
enabled: true
severity_threshold: high
ignore_dev_dependencies: true
ignore:
- package: lodash
version: "<4.17.21"
reason: "Mitigated by input validation"
expires: 2026-06-01
secrets:
enabled: true
custom_patterns:
- name: internal-api-key
pattern: 'INTERNAL_[A-Z0-9]{32}'
ignore_paths:
- "**/*.test.js"
- "docs/**"
remediation:
auto_pr: true
pr_assignees:
- security-team
require_approval: true
Pull Request Integration
Arnica adds security context directly to pull requests:
## Arnica Security Analysis
### Dependencies Changed
| Package | Old Version | New Version | Risk |
|---------|-------------|-------------|------|
| axios | 0.21.1 | 1.6.0 | Low |
| lodash | 4.17.15 | 4.17.21 | Fixed CVE-2021-23337 |
### New Vulnerabilities: 0
### Secrets Detected: 0
### Package Reputation
- axios@1.6.0: High reputation (98/100)
- lodash@4.17.21: High reputation (99/100)
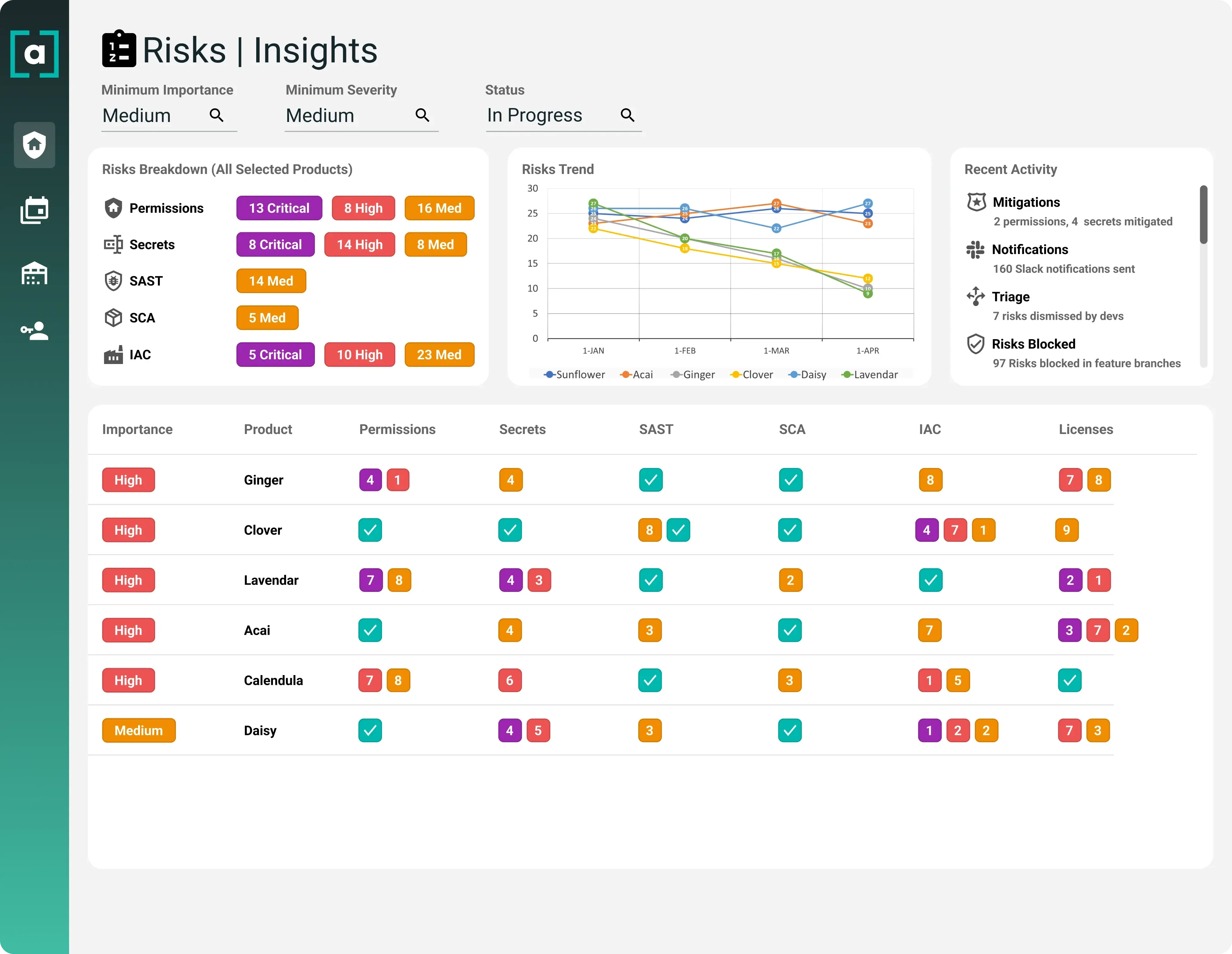
Dashboard Features
The Arnica dashboard provides:
Portfolio Overview
├── Total Repositories: 47
├── Critical Vulnerabilities: 3
├── High Vulnerabilities: 12
├── Secrets Found: 2
└── Average Package Reputation: 87/100
Risk Trends
├── Vulnerabilities over time
├── Developer risk scores
├── Remediation velocity
└── Coverage metrics
Developer Analytics
├── Code ownership mapping
├── Commit patterns
├── Security violation trends
└── Training recommendations
API Integration
Arnica provides a REST API for authenticated customers to retrieve vulnerability data, package reputation scores, and trigger scans programmatically. API access and documentation are available through the Arnica dashboard after onboarding.
SBOM generation and license compliance
Arnica maintains a rolling SBOM inventory per repository and per organization as part of its always-on SCA scan. Exports are available in CycloneDX format alongside CSV and PDF summaries — the CycloneDX output covers direct and transitive components with license, version, and package-reputation signals attached.
License compliance runs off the same inventory. Arnica automatically identifies every dependency license, surfaces conflicts against an organization-level policy (for example, no GPL-3.0 in a commercial closed-source service), and flags newly introduced licenses in pull requests.
The compliance-reporting views on arnica.io/solutions/compliance-security-reporting use the same data to show license posture and unresolved violations across the whole portfolio, which is usually what legal and procurement teams need at audit time rather than per-repo SBOM downloads.
Setup
When to use Arnica
Arnica fits teams that want security scanning without pipeline complexity, and that care about supply chain risk beyond known CVEs.
Strengths:
- Zero pipeline changes required
- Package reputation scoring catches risks before CVEs exist
- Reachability analysis reduces false positives
- Secrets detection included
- Developer behavior analytics
Limitations:
- Advanced features require paid plans
- Smaller ecosystem compared to Snyk or Checkmarx
- Pipelineless approach may not fit teams wanting build-blocking gates
- Developer profiling may raise privacy concerns
How it compares:
| vs. | Key difference |
|---|---|
| Snyk Open Source | Snyk integrates into CI/CD pipelines with automated fix PRs. Arnica is pipelineless with package reputation scoring. |
| Socket | Socket focuses on behavioral analysis for supply chain threats. Arnica adds developer risk profiling and pipelineless architecture. |
| GitGuardian | GitGuardian leads in secrets detection. Arnica combines SCA, secrets, and developer analytics in a single pipelineless platform. |
Further reading: What is SCA? | Supply Chain Attacks Guide
Arnica pricing
Arnica publishes per-identity pricing at arnica.io/pricing, where an identity is any user or service account that committed code or had PR activity in the last 90 days.
Free — $0 per identity. Covers SCA, SAST and IaC, secrets scanning, SBOM inventory, license and package-reputation signals, weekly risk ingestion, and the full user and asset inventory. No maximum identity count is listed.
Core Business — $300 per identity per year on annual billing, $360 on monthly. Adds real-time risk ingestion, merge-blocking policies on pull requests, ChatOps notifications to Slack and Teams, inline PR risk identification, and automated issue management.
Core Enterprise — $600 per identity per year on annual billing, $720 on monthly. Adds advanced RBAC, SAML provisioning, zero-day campaigns, API access, on-prem deployment, and dynamic backlog management. Image Scanning, AI SAST, and the Agentic Rules Enforcer are listed as priced add-ons on top of Enterprise.
Re-check the pricing page before budgeting — Arnica has adjusted tiers before and may again.
Arnica alternatives
Arnica sits at the intersection of pipelineless SCA, secrets detection, and developer-risk analytics. The closest alternatives each cover a subset of that scope differently.
Snyk Open Source
Snyk Open Source is the most common CI-integrated SCA comparison. Snyk has broader language coverage, a mature free tier, and a deeper automated-fix-PR workflow inside the pipeline. Arnica wins when teams want to avoid CI changes entirely and value package-reputation scoring above CVE-only triage.
Socket
Socket focuses on behavioral analysis of npm and PyPI packages at PR time — typosquats, install scripts, obfuscated code. Socket goes deeper on malicious-package detection in those two ecosystems. Arnica is broader (SCA + secrets + developer risk + six ecosystems) but less deep on npm/PyPI behavior.
Endor Labs
Endor Labs leads on function-level call-graph reachability to cut CVE noise. Arnica’s reachability analysis is lighter; Endor fits larger engineering orgs that want to prove exploitability before triaging.
Mend SCA
Mend SCA ships the Renovate-powered dependency-update engine behind most enterprise automation. Teams that want SCA plus the most mature update-automation layer pick Mend; teams that want SCA plus secrets and developer analytics in one pipelineless app pick Arnica.
For the broader landscape, see the SCA tools overview and what SCA does.
Arnica FAQ
How is pipelineless SCA different from CI-integrated SCA?
CI-integrated SCA tools run inside a pipeline step — findings appear on the build that triggers them, and historical vulnerabilities are only surfaced when a build happens to re-run. Arnica connects to the SCM as a GitHub, GitLab, Bitbucket, or Azure DevOps app instead, so scanning runs continuously against the repository state regardless of whether a build is active.
What ecosystems does Arnica support?
Arnica covers JavaScript (npm, yarn, pnpm), Python (pip, Poetry), Java (Maven, Gradle), Go modules, .NET (NuGet), Ruby (Bundler), and container images. The supported-ecosystem list is maintained in the Arnica documentation.
Does Arnica replace Dependabot or Renovate?
Yes, for teams that want a single SCA + update-automation source. Arnica creates remediation PRs using its own scan data, so running it alongside Dependabot or Renovate typically produces duplicate update PRs on the same repo. Most teams turn the others off once Arnica is authoritative.
What permissions does the GitHub App need?
Read access to source is required for scanning. Write access is opt-in and gated per capability — PR comments, automated fix PRs, and automated permission provisioning each map to separate permissions, documented on the Arnica GitHub App permissions page.
What data leaves the repository?
Arnica processes code metadata and dependency manifests in its SaaS backend. Source-code snippets that Arnica captures for secrets detection and remediation context are covered by its commercial SaaS terms — teams with stricter boundaries can use the on-prem deployment listed on the Core Enterprise tier.