ArmorCode is an AI-powered ASPM platform that ingests findings from 320+ security tools and correlates them into one prioritized backlog. The platform has processed over 40 billion findings and was named a Leader in the IDC MarketScape: Worldwide ASPM 2025 Vendor Assessment. Founded in 2020 and headquartered in Palo Alto, California, it supports security teams managing vulnerabilities across application, cloud, and infrastructure tooling.
Founded in 2020 and headquartered in Palo Alto, California, ArmorCode was named a Leader in the IDC MarketScape: Worldwide ASPM 2025 Vendor Assessment released in September 2025. Public customers include Shutterfly, Johnson Controls, NetApp, Athena Health, S&P Global, and The Motley Fool.
Notable results: Shutterfly reduced vulnerability remediation from 240 days to 7 days. NetApp consolidated findings from 30+ security tools into a single prioritized view.
- Category: Application Security Posture Management (ASPM)
- Founded: 2020
- Headquarters: Palo Alto, California
- CEO & co-founder: Nikhil Gupta
- Funding: $81M total across seed ($11M), Series A ($14M, Nov 2022), Series B ($40M, Dec 2023), and strategic round ($16M, March 2026)
- Named customers: Shutterfly, NetApp, Johnson Controls, Athena Health, S&P Global, The Motley Fool
- Target buyer: Fortune 1000 CISOs and AppSec leaders with multi-vendor scanner sprawl
- Analyst recognition: Leader, IDC MarketScape for ASPM (September 2025)
What is ArmorCode?
ArmorCode is an AI-powered ASPM platform that consolidates findings from the scanners a security team already owns. It does not scan source code itself. It sits downstream of SAST, DAST, SCA, CSPM, and container tools and turns their output into one prioritized backlog.
The platform solves three problems in that order:
The core problem ArmorCode solves is tool sprawl. Organizations running dozens of security scanners end up with millions of findings, many overlapping and most missing business context.
ArmorCode deduplicates, correlates, and ranks them so teams can focus on what actually matters.
Key features
AI correlation engine
The correlation engine goes past simple deduplication. It uses machine learning to spot relationships between findings across different tools and asset types.
A SQL injection in application code, a misconfigured database in your cloud environment, and an exposed API endpoint can all trace back to the same root cause. ArmorCode surfaces these connections automatically.

Adaptive risk scoring
Risk scores adjust to your specific environment. The platform factors in exploitability data from threat intelligence feeds, business criticality of affected assets, internet exposure, and compensating controls.
Two critical CVEs do not automatically get the same priority if one sits behind a WAF in an internal app and the other is in a public-facing payment service.
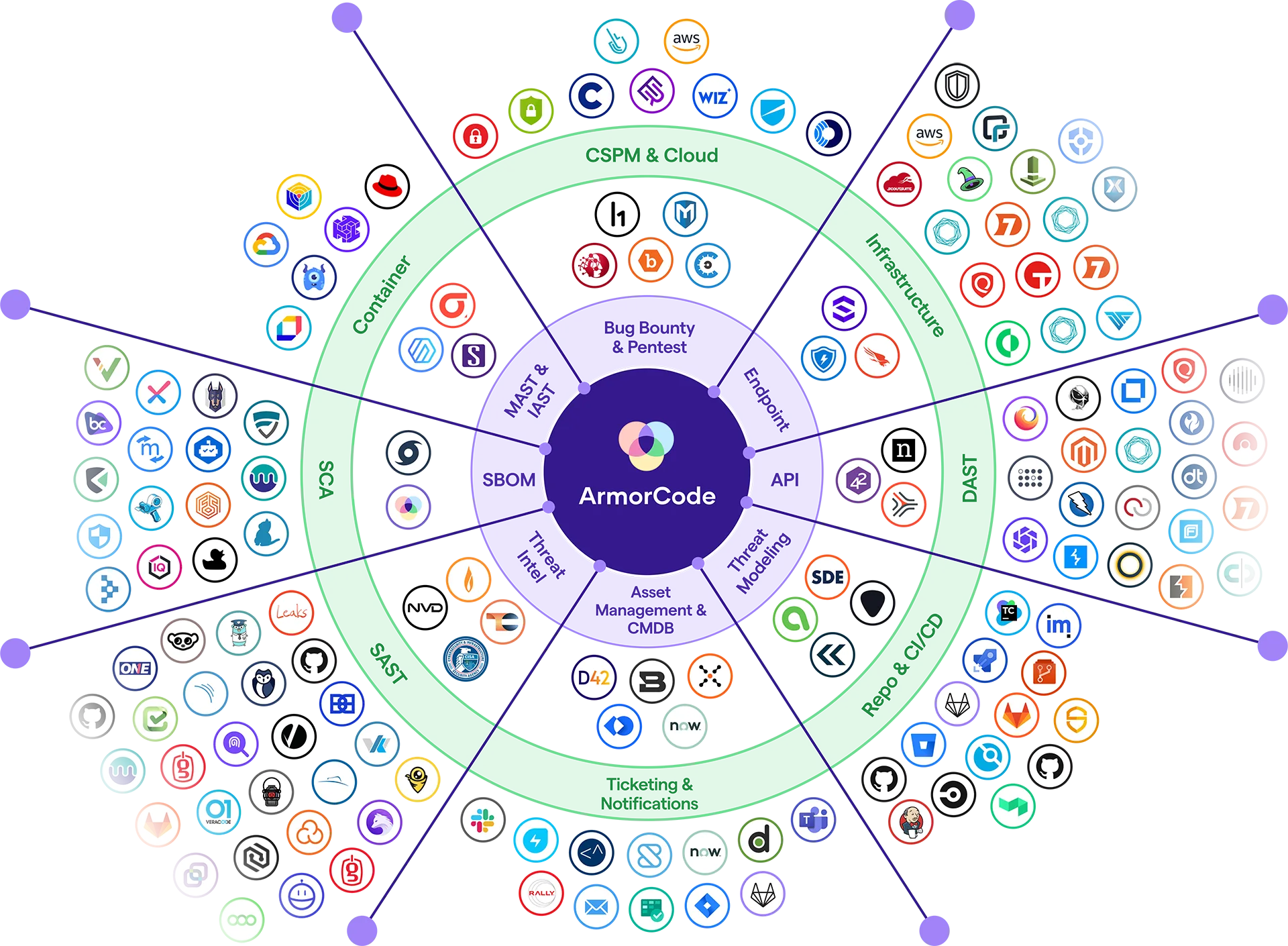
320+ integrations
ArmorCode connects to essentially every security tool on the market:
| Category | Examples |
|---|---|
| SAST | Checkmarx, Fortify, SonarQube, Coverity, Veracode, Snyk Code, CodeQL |
| DAST | Burp Suite, OWASP ZAP, Invicti, Acunetix, StackHawk |
| SCA | Snyk, Black Duck, Dependency-Check, Sonatype, Mend |
| CSPM | Wiz, Prisma Cloud, AWS Security Hub, Microsoft Defender |
| Containers | Trivy, Aqua, Sysdig, Docker Scout, Amazon Inspector |
| IaC | Checkov, KICS, Bridgecrew, Snyk IaC |
| Secrets | GitGuardian, Gitleaks, HashiCorp Vault Radar |
| Ticketing | Jira, ServiceNow, Azure Boards, GitHub Issues |
SBOM and supply chain security
ArmorCode generates and maintains Software Bills of Materials, tracking component inventory across your applications. This covers EU Cyber Resilience Act mandates and helps teams respond quickly when new vulnerabilities hit components in their software supply chain.
Additional capabilities
| Capability | Details |
|---|---|
| Penetration testing management | Track manual pentest findings through assignment, remediation, and verification in the same platform as automated results |
| No-code automation | Visual workflow builder for routing, escalation, and notification rules without writing code |
| Compliance reporting | Pre-built reports for SOC 2, ISO 27001, PCI DSS, and EU Cyber Resilience Act |
| Executive dashboards | Risk posture trends, MTTR tracking, and team performance metrics |
Integrations
Getting started
ArmorCode pricing
ArmorCode does not publish public pricing as of April 2026. Quotes are sales-led and scale with the number of connected scanners, applications under management, user seats, and whether Anya AI or premium modules are included.
Based on public procurement signals and ArmorCode’s enterprise positioning, the platform targets Fortune 1000 budgets rather than startup ones. Expect a multi-year commercial agreement similar in shape to Snyk Enterprise, Wiz, or other enterprise security platforms.
If budget is the gating constraint, DefectDojo is the free open-source alternative most teams evaluate as a counterweight. For teams that need a commercial ASPM at a smaller footprint, Aikido is worth a look before committing to the ArmorCode sales motion.
How ArmorCode correlates and scores findings
The core technical problem ASPM platforms solve is this: the same vulnerability shows up across a SAST scanner, a container scanner, and a CSPM tool with three different titles, three different severities, and three different finding IDs. Without correlation, the triage queue is 80% duplicates. ArmorCode handles this in two stages.
The first stage is deterministic deduplication. Findings carry normalized identifiers (CWE, CVE, package coordinates, rule ID, file path and line range) that ArmorCode hashes into a fingerprint. Two raw findings with the same fingerprint collapse into one finding record with multiple source references, so you see “SQLi in checkout-service/OrderDao.java:142, reported by Checkmarx, Snyk Code, and Veracode” instead of three separate tickets.
The second stage is contextual risk scoring, branded as Adaptive Risk Scoring. It takes the deduplicated finding and layers on exploitability signals (CISA KEV membership, EPSS-style exploit probability, public exploit availability), exposure signals (is the affected asset internet-reachable, does it process PCI/PII data, what compensating controls sit in front of it), and business-criticality tags that you set on the asset in ArmorCode’s asset graph. The score moves when the underlying signals move. A CVE that enters CISA KEV next week auto-escalates findings tied to it without a rescan.
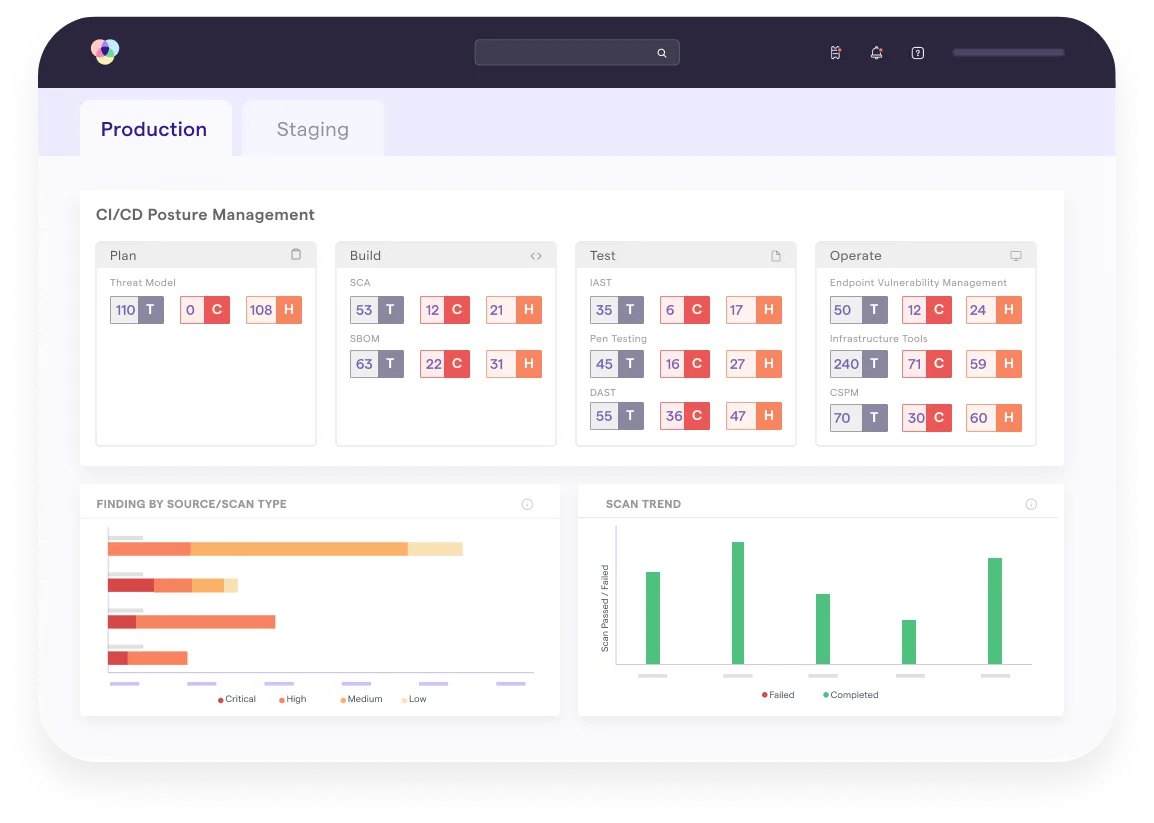
In practice this is what separates ASPM from a shared Jira board. A team I talked to running 12 scanners typically sees a 60–80% reduction in open finding count after correlation lands. The top of the priority queue stops looking like “whichever scanner ran last.”
Anya, policy-as-code, and workflow automation
Anya is ArmorCode’s agentic AI layer. It accepts natural-language queries like “show me internet-facing critical findings owned by the payments team with no fix committed in 14 days” and returns a structured answer plus drill-down links. It also drafts remediation guidance and summarizes a finding’s blast radius in executive language, which is the piece most security leaders actually use it for when writing board updates.
The more operational half of the platform is the no-code workflow builder. It exposes the triggers you would expect (new finding above severity X, SLA breach imminent, scan status changes) and lets you compose them into routing rules that open Jira or ServiceNow tickets with the right project, assignee, labels, and due date based on asset ownership and severity. SLAs are defined per tuple of criticality, team, and asset class. A critical finding on a PCI asset can carry a 7-day SLA while an internal tool gets 30 days, enforced automatically.
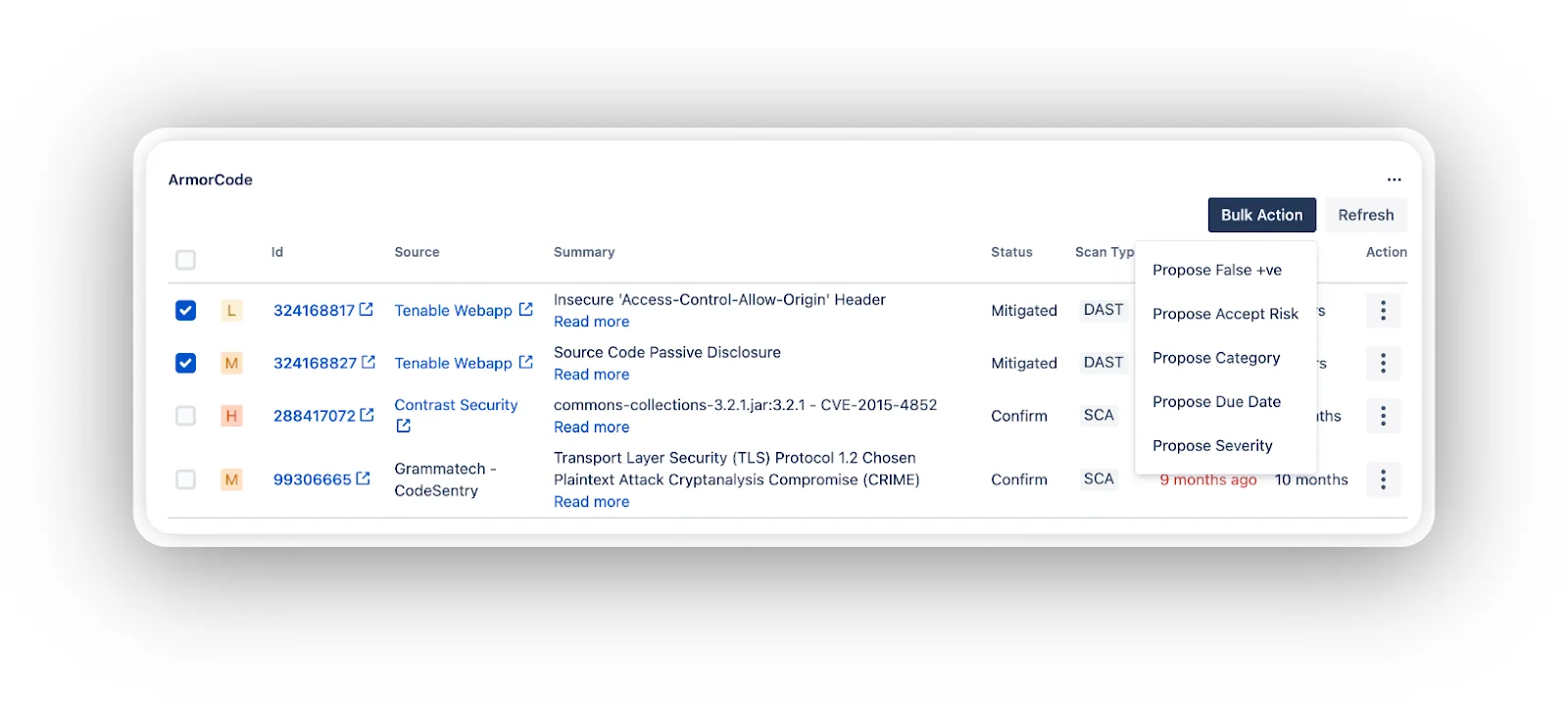
Two workflow capabilities matter for audit preparation specifically. Exceptions (accepted-risk decisions) are first-class records with an owner, expiration date, and justification, not Jira comments that disappear into a backlog. Evidence export bundles finding history, scan artifacts, remediation timestamps, and exception approvals into a single report. That is the kind of artifact a SOC 2 or PCI assessor asks for once and never gets in clean form from a raw Jira export.
The integration surface in practice
ArmorCode’s 320+ integrations is a headline number; the more useful breakdown is which categories the platform covers end-to-end. Per the public integrations catalog on armorcode.com, the coverage spans SAST, SCA, DAST, IAST, MAST, container and IaC scanners, CSPM/CNAPP (Wiz, Prisma Cloud, AWS Security Hub, Microsoft Defender for Cloud, GCP SCC), secrets detection, API security scanners, pentest management, plus ticketing (Jira, ServiceNow, Azure Boards, GitHub/GitLab Issues) and chat (Slack, Teams, PagerDuty).
For supply-chain work the platform ingests SBOMs in CycloneDX and SPDX and re-evaluates them continuously against new CVEs, which is the mechanism behind its EU Cyber Resilience Act story. CI/CD hooks cover GitHub Actions, GitLab CI, Jenkins, Azure DevOps, and Bitbucket Pipelines, so findings from a PR scan land in the same taxonomy as nightly scheduled scans instead of living in a separate build log.
Two gaps worth naming honestly. Runtime protection tools (RASP, eBPF runtime) are not the center of gravity here. ArmorCode correlates their findings when they feed data in, but the platform is built around pre-production and posture signals. The platform supports multi-tenant data segregation for MSSPs and holding companies, but the operational story for running ArmorCode across fully air-gapped networks is sales-led rather than self-serve.
When to use ArmorCode
ArmorCode fits organizations that already run multiple security scanners and need a platform to make sense of the output. If you are managing dozens of tools producing overlapping findings, struggling with alert fatigue, or need unified reporting across application, cloud, and infrastructure security, ArmorCode handles that at enterprise scale.
Strengths:
- Widest native integration library in ASPM (320+ tools)
- Anya agentic AI for natural-language security queries and correlation
- Recognized as a Leader in the IDC MarketScape for ASPM (September 2025)
- Proven enterprise customer outcomes (Shutterfly 240→7 days)
- No-code automation for routing and escalation workflows
Limitations:
- Commercial only, no free tier. For free alternatives, use DefectDojo
- Enterprise sales motion is not a fit for startups or teams with a handful of scanners
- Does not scan code itself; you still need SAST, DAST, SCA, and CSPM tools feeding in
Smaller teams with fewer than 50 applications or limited security tool investments should consider lighter-weight options. Aikido covers aggregation at smaller scale without the enterprise overhead; DefectDojo covers it for free if you have the operations capacity.