Is Arachni discontinued? Effectively yes. Arachni’s last release (v1.6.1.3) shipped in May 2022, and no new releases or security patches have been published since. Teams looking for open-source DAST should migrate to OWASP ZAP, Nuclei, or Wapiti.
Is Arachni Discontinued?
In practice, yes. Arachni’s last public release — v1.6.1.3 in May 2022 — is years out of date. The original maintainers have redirected their effort into Ecsypno Codename SCNR, a commercial successor, so no new releases, dependency bumps, or security patches have shipped since. The scanner’s Ruby runtime and browser cluster are no longer keeping pace with modern web applications.
If you were relying on Arachni, migrate off it. For open-source DAST, OWASP ZAP is the direct replacement — full-featured GUI, REST API, and CI/CD integration. Nuclei is a faster, template-based option that works well in pipelines. Wapiti is a lightweight Python scanner in the same spirit as Arachni and is still actively maintained.
Arachni was a Ruby-based web application security scanner framework. It automated vulnerability detection for XSS, SQL injection, code injection, file inclusion, and other common web vulnerabilities.
Its last release was v1.6.1.3 in May 2022 and the project is no longer actively maintained.
The original developers replaced Arachni with Ecsypno Codename SCNR, a commercial product.
What Arachni did
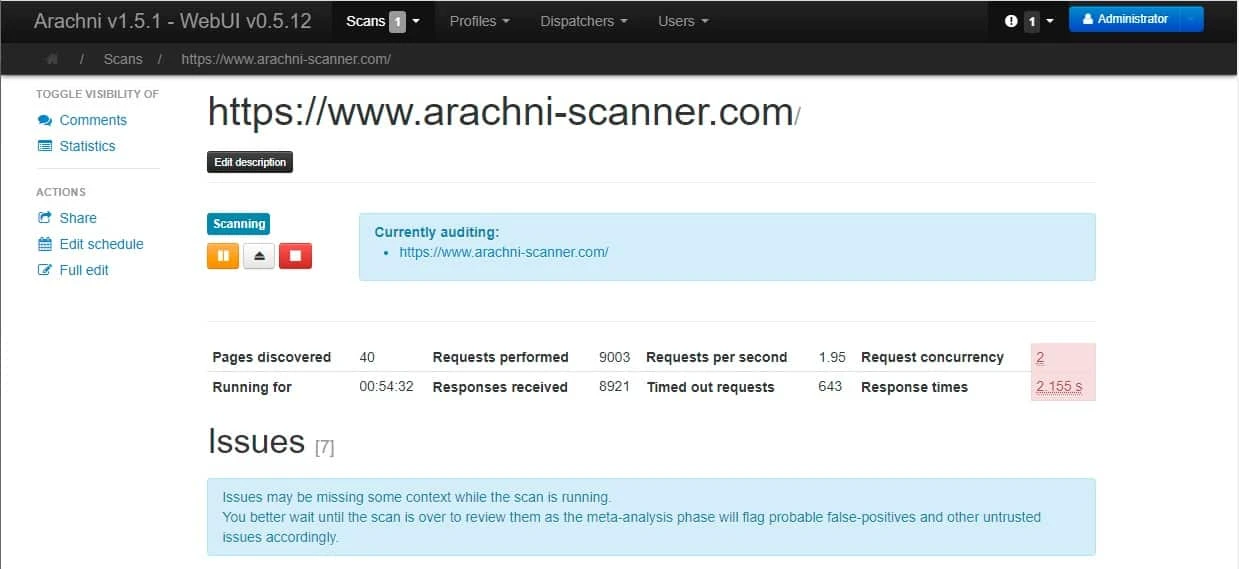
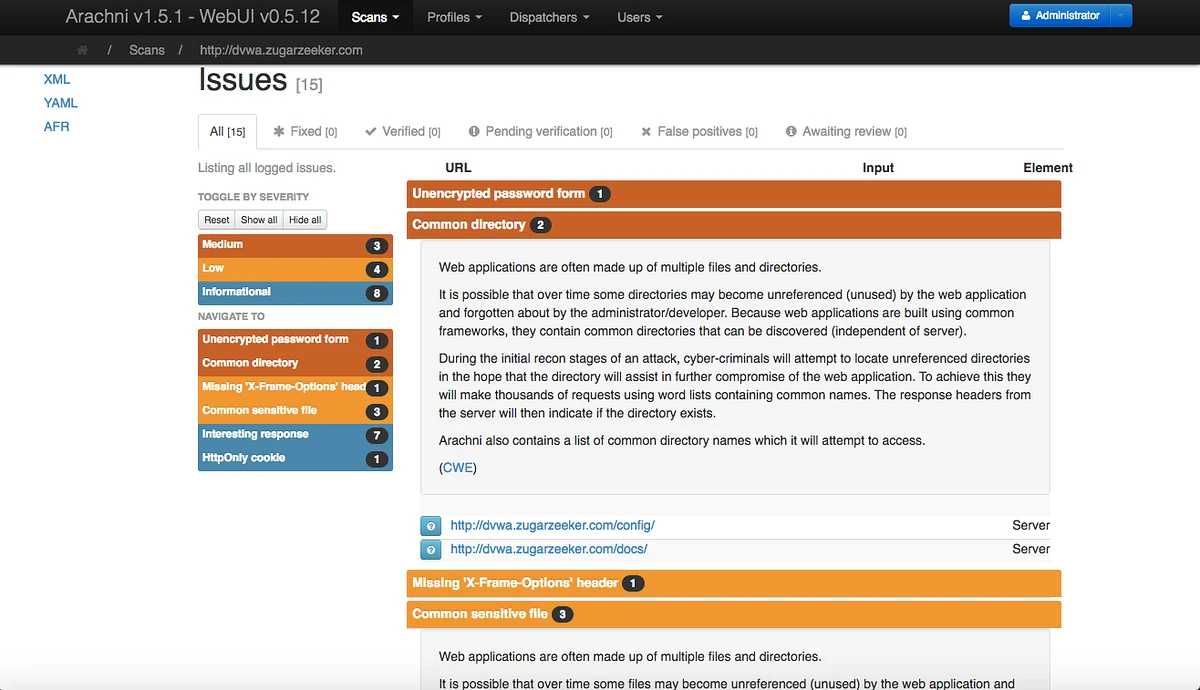
Arachni crawled web applications, identified inputs, and fuzzed them with attack payloads covering categories listed in the OWASP Top 10. The scanner ran as a command-line tool, web UI, or via REST API for integration with other tools.
Written in Ruby, it used a browser cluster to render JavaScript-heavy applications and detect client-side vulnerabilities. The plugin architecture allowed custom checks and export formats.
Why Arachni was archived
Active development effectively stopped after v1.6.1.3 in May 2022. The maintainers launched Ecsypno Codename SCNR as the commercial successor and stopped updating the open-source version.
No security patches, dependency updates, or compatibility fixes have been released since v1.6.1.3. Running Arachni on modern web applications risks missing vulnerabilities or failing to complete scans due to outdated browser engines.
Do not use Arachni for new projects. The codebase has not been updated since May 2022.
Modern web frameworks, authentication methods, and JavaScript patterns have evolved beyond Arachni’s capabilities. Use actively maintained scanners like ZAP or Nuclei instead.
Alternatives to Arachni
For open-source DAST tools, OWASP ZAP offers active scanning, manual testing, and API automation. It detects OWASP Top 10 vulnerabilities and integrates into CI/CD pipelines through Docker, CLI, and GitHub Actions.
Nuclei provides fast, template-based vulnerability scanning. The community maintains 7000+ templates for known vulnerabilities, misconfigurations, and CVEs. Nuclei works well in pipelines for targeted checks.
For commercial web application scanning with automated crawling and JavaScript support, Burp Suite Professional and Invicti offer comprehensive solutions with active development.
Browse other DAST tools for current web application security scanning options, or check the free DAST tools guide for open-source alternatives that cost nothing to run.