Apiiro is an ASPM platform that uses Deep Code Analysis (DCA) and a proprietary Risk Graph to understand code behavior and prioritize risk from code to runtime. Unlike traditional SAST tools that scan for known vulnerability patterns in source code, Apiiro flags material changes that shift risk even when no scanner fires an alert — because it understands what the code does, not just what it looks like.
Apiiro raised $135M in total funding, including a $100M Series B in 2022 led by General Catalyst. Customers include USAA, BlackRock, Shell, SoFi, Cloudera, and Equinix.
What is Apiiro?
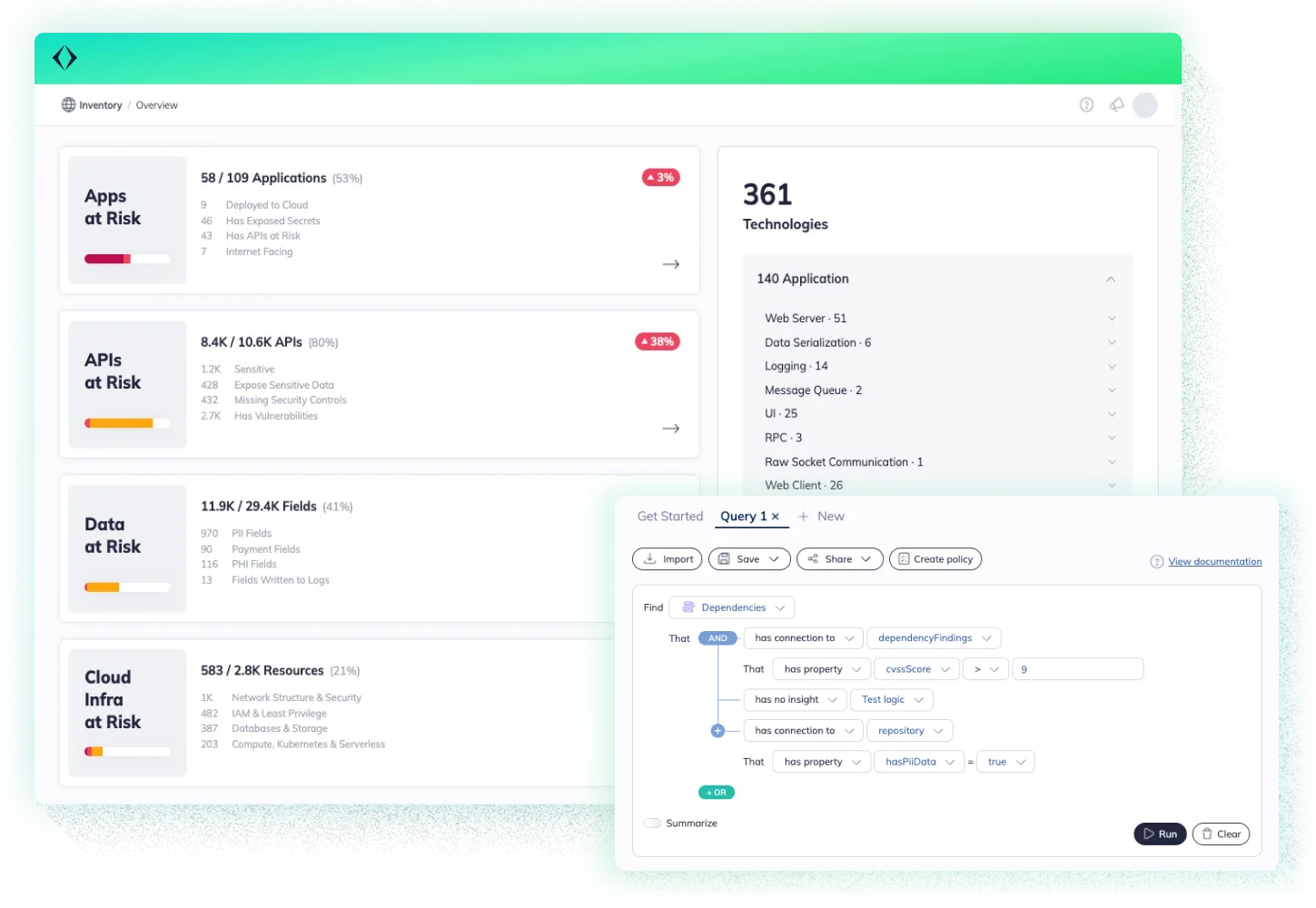
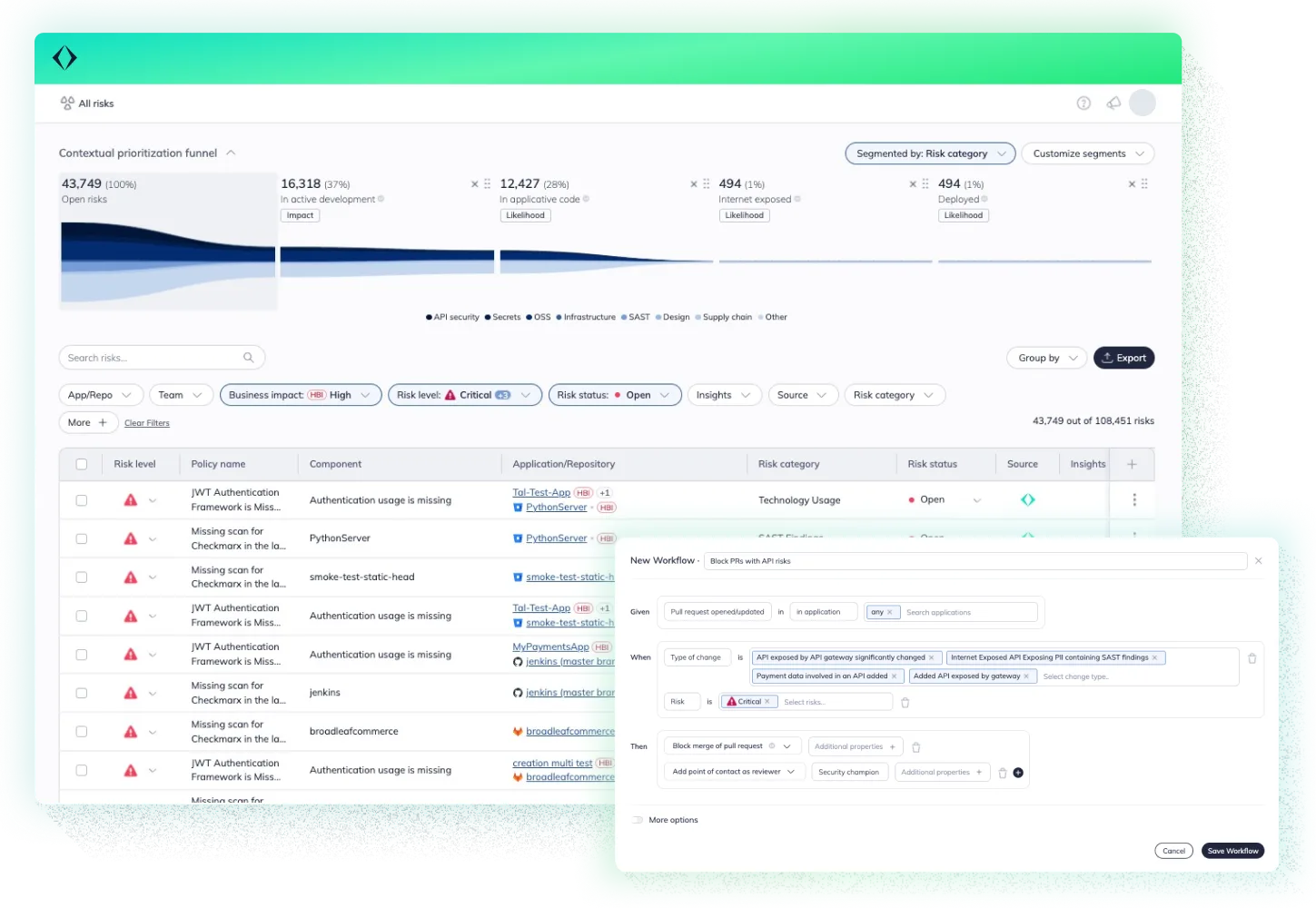
Apiiro is a risk-based ASPM platform that sits on top of existing security scanners and uses code intelligence to separate real risk from noise. It splits the development lifecycle into three phases:
Apiiro is tool-agnostic — it aggregates findings from whatever SAST, DAST, and SCA tools you already run, then layers Risk Graph context on top to determine which findings actually matter based on reachability, business criticality, and internet exposure. It does not replace your existing scanners; it makes them more useful.
Key features
Deep Code Analysis
Deep Code Analysis builds an abstract representation of how code actually behaves, not just what it looks like syntactically.
It traces data flows across function and service boundaries, spots business logic patterns (authentication, payment processing, PII handling), and flags behavioral changes even when the diff looks minor.
Material Change Detection separates high-risk changes from routine refactoring. A rename that touches 200 files won’t trigger the same response as a 3-line change to your authentication flow.
Traditional SAST scans for known vulnerability patterns in source code. Apiiro’s DCA understands code behavior and flags material changes that shift risk, even when no vulnerability pattern matches.
A new API endpoint that exposes PII gets flagged based on what it does, not because it matches a regex.
Risk Graph
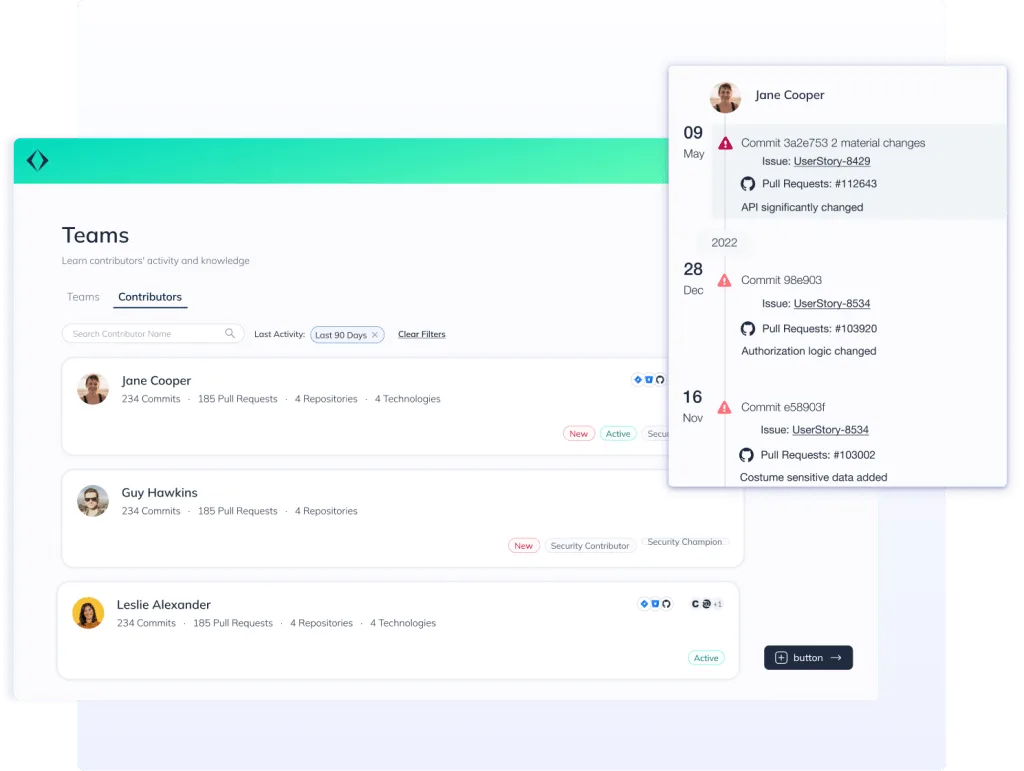
The Risk Graph is Apiiro’s queryable knowledge graph that connects code, infrastructure, and people with business context. It ties together code (repositories, branches, commits, functions, data flows), infrastructure (build pipelines, deployment targets, runtime environments), and people (developers, reviewers, approvers) with business context like data sensitivity and internet exposure.
You can query it in natural language:
| Query | What it returns |
|---|---|
| “Changes to PII handling code in the last 30 days” | All commits touching sensitive data flows, with authors and review status |
| “Path from this CVE to internet-exposed endpoints” | Dependency chain showing if the vulnerable code is reachable from production |
| “Unreviewed commits to authentication modules” | Commits to auth code that bypassed code review, ranked by risk |
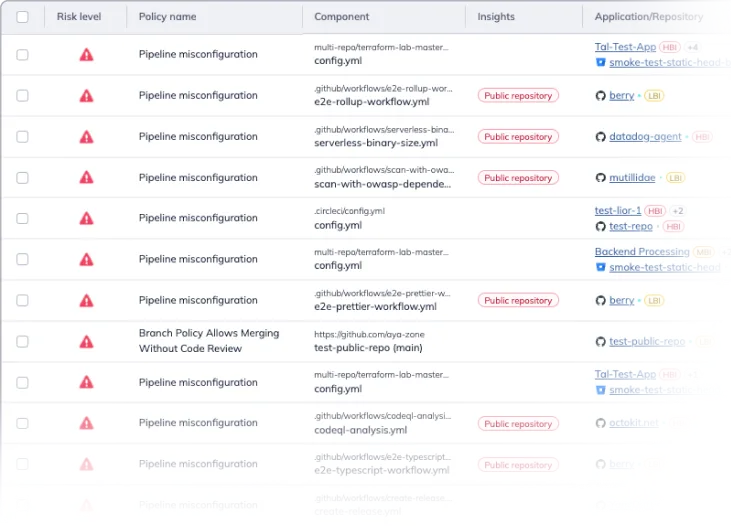
Software supply chain security
Apiiro extends standard SBOM with its XBOM (eXtended Software Bill of Materials), which adds behavioral analysis on top of dependency inventory. Where a standard SBOM lists what packages are present, XBOM detects suspicious changes in dependency updates and flags dependency confusion risks. Specific capabilities include:
- Transitive dependency mapping across the full dependency tree
- Behavioral analysis of dependency updates (detecting suspicious changes)
- Dependency confusion risk detection
- License compliance tracking
- SBOM generation and maintenance
AI agents
Apiiro’s Guardian Agent addresses a gap that traditional AppSec tools miss entirely: insecure code generated by AI coding assistants. It intercepts developer prompts sent to tools like GitHub Copilot or Cursor and injects security context, threat models, and compliance policies before any code is generated. The result is that insecure patterns are blocked at the prompt layer rather than caught in a scan after the fact. AutoFix agents handle remediation across the design, code, and delivery phases.
Integrations

Getting started
When to use Apiiro
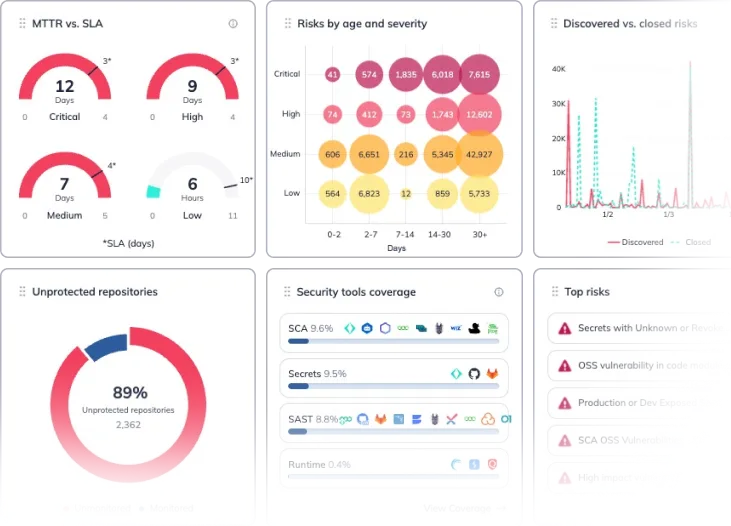
Apiiro is built for enterprises already drowning in scanner findings who need risk-based prioritization, not more alerts. If you’re tracking code risk over time, managing complex supply chains, or need compliance evidence across the development lifecycle, that’s where Apiiro earns its keep.
The difference between Apiiro and a standalone ASPM tool is code intelligence depth. Most ASPM platforms aggregate findings and apply static metadata (severity, asset criticality) to prioritize. Apiiro uses Deep Code Analysis to understand behavioral changes in the code itself, so prioritization reflects actual risk rather than scanner severity scores.
Pricing requires a sales conversation. Median annual contract: $55,000 (range: $14,000–$87,000)
Smaller teams with simple codebases where manual review still works, or organizations that need scanning capabilities rather than aggregation, should look at tools like Aikido or Jit instead.
Frequently Asked Questions
What is Apiiro?
How does Apiiro's Risk Graph work?
What is Deep Code Analysis?
Does Apiiro replace existing security scanners?
What is Apiiro's Guardian Agent?
* Pricing data from Vendr — anonymized contract values from real buyer transactions.