- Salt Security discovers shadow APIs through traffic analysis, cloud connectors, external surface scanning, and GitHub scanning; 42Crunch requires OpenAPI specifications as the foundation.
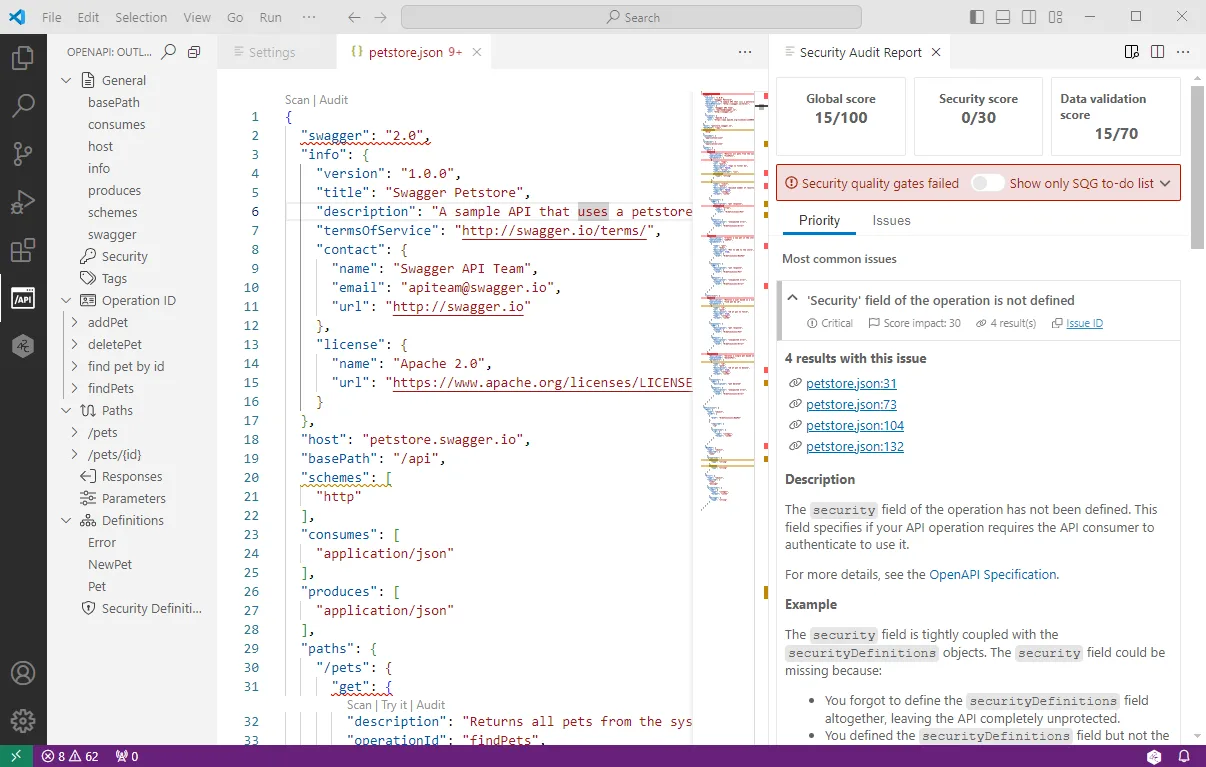
- 42Crunch IDE extensions have 2M+ downloads and run 300+ security checks with 0-100 scoring; Salt Security has no IDE integration and is designed for security teams, not developers.
- Salt's behavioral ML detects logic-based attacks (BOLA, credential stuffing, data exfiltration) that 42Crunch's contract-based firewall cannot catch with valid request structures.
- 42Crunch's micro API firewall enforces a positive security model inline; Salt operates out-of-band via traffic mirroring with zero latency but no native blocking.
- Salt maps posture against PCI DSS, HIPAA, GDPR, SOC 2, NIST, CMMC, and FedRAMP; 42Crunch provides per-API contract compliance through its audit-scan-enforce pipeline.
Which Is Better: Salt Security or 42Crunch?
This is the full head-to-head comparison of Salt Security and 42Crunch. Salt Security is better for runtime API discovery and behavioral threat detection in production; 42Crunch is better for shift-left API security driven by OpenAPI specifications and contract enforcement. The two platforms are complementary — many teams run both across the API lifecycle.
Both protect APIs, but they approach the problem from opposite ends of the development lifecycle.
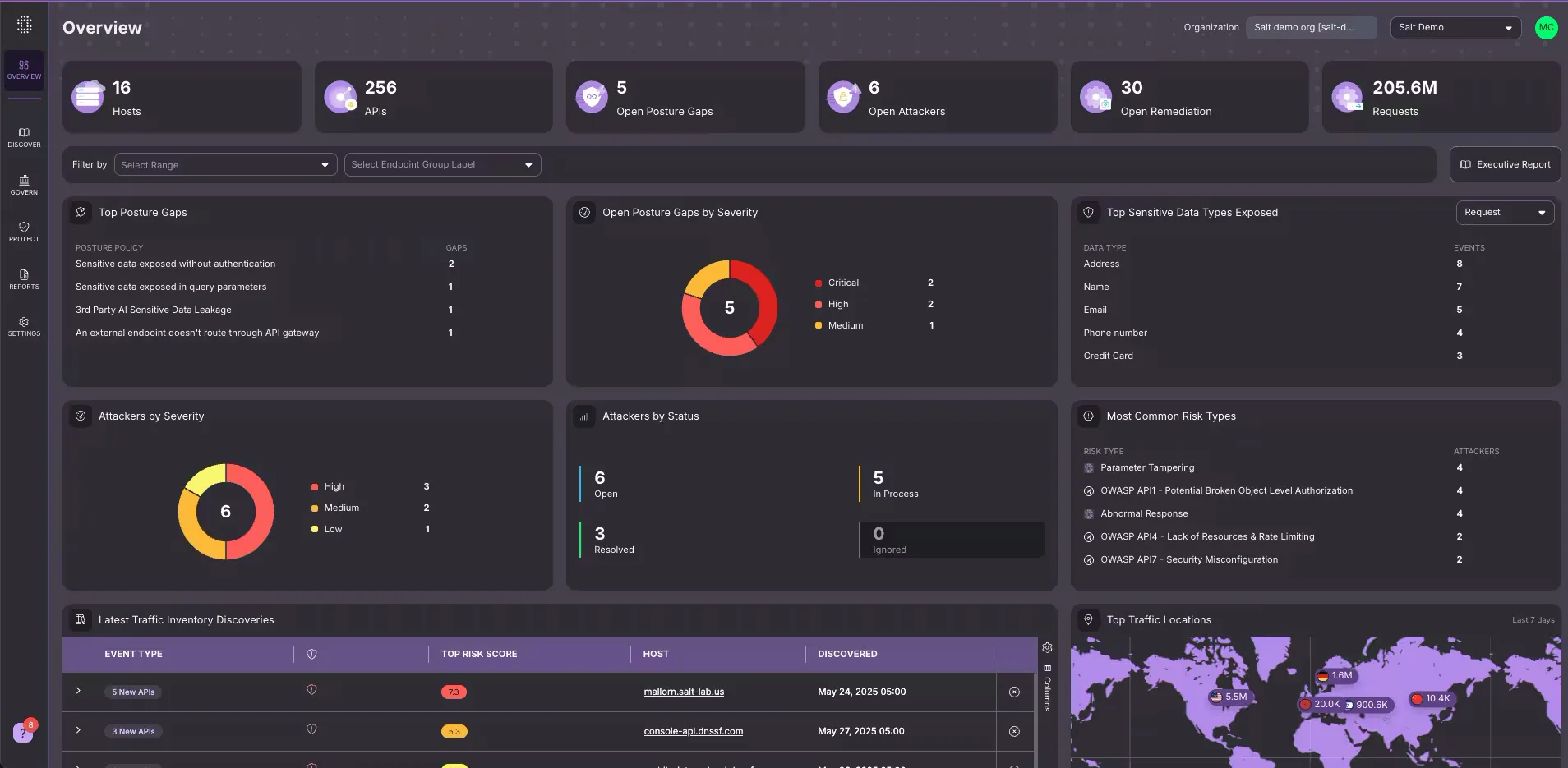
Salt Security is a runtime API protection platform. It discovers APIs you did not know existed by analyzing live traffic, cloud environments, and your external attack surface.
Once it maps your API landscape, behavioral ML baselines normal traffic patterns and flags anomalies that indicate attacks like BOLA exploitation, credential stuffing, or data exfiltration.
Salt works after deployment — its strength is finding and protecting APIs in production.
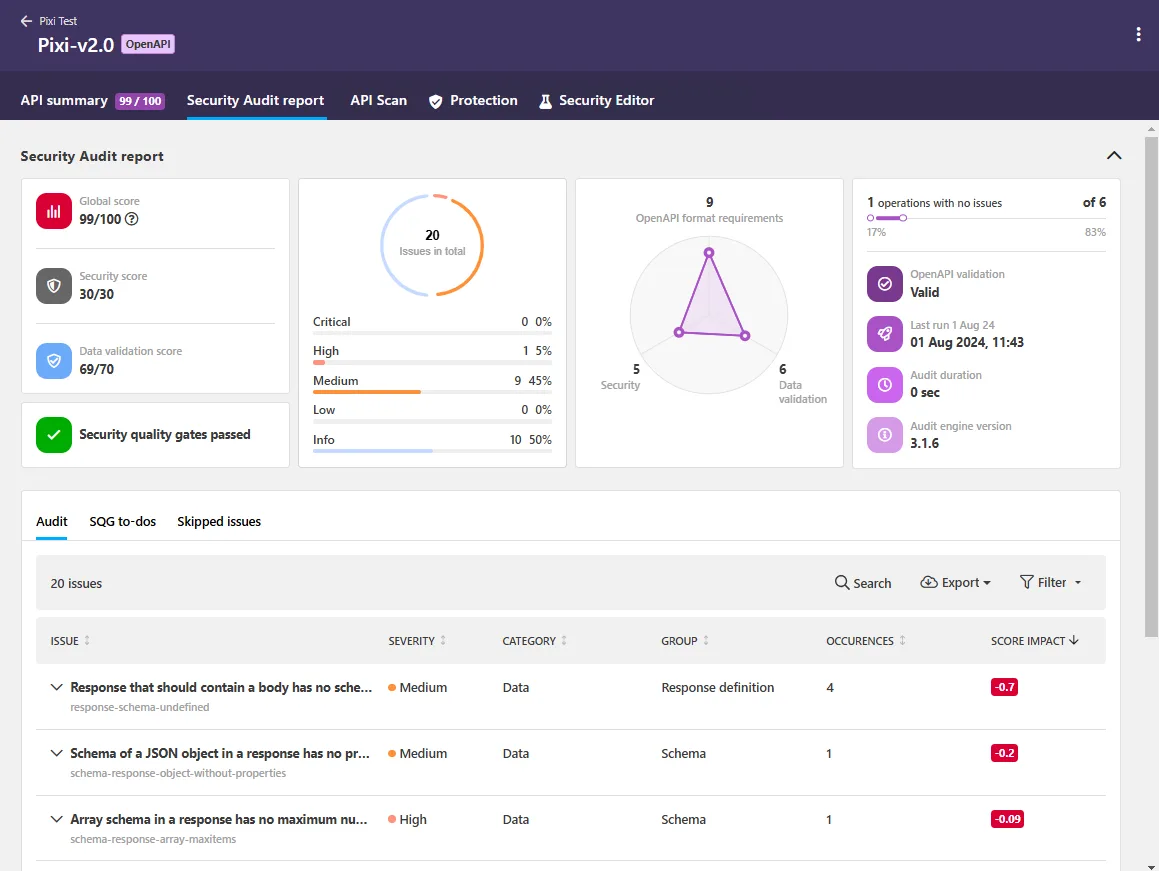
42Crunch is a shift-left API security platform. It starts with the OpenAPI specification itself, running 300+ security checks against the definition before any code ships.
The conformance scanner tests live APIs against the documented contract. The micro API firewall then enforces that contract in production, blocking any request that falls outside the spec. 42Crunch works before and during deployment — its strength is making sure APIs are built correctly from design through runtime.
Pick Salt Security when API discovery and runtime threat detection are your priority. Pick 42Crunch when API specification quality and contract enforcement matter most.
What Are the Key Differences?
| Feature | Salt Security | 42Crunch |
|---|---|---|
| License | Commercial | Commercial (free tier available) |
| Primary Focus | Runtime API discovery & protection | Shift-left API spec security & contract enforcement |
| API Discovery | Traffic analysis, cloud connectors, external surface scan, GitHub scan | API discovery (spec-focused) |
| OpenAPI Spec Auditing | No | Yes (300+ checks, 0-100 scoring) |
| Conformance Testing | No | Yes (dynamic testing against OpenAPI contract) |
| Runtime Protection | Behavioral ML threat detection | Micro API firewall (positive security model) |
| Attack Detection | BOLA, credential stuffing, data exfiltration, account takeover, injection | Blocks non-conforming requests (schema violations, injection) |
| Detection Approach | Behavioral anomaly detection | Contract enforcement (allowlist-based) |
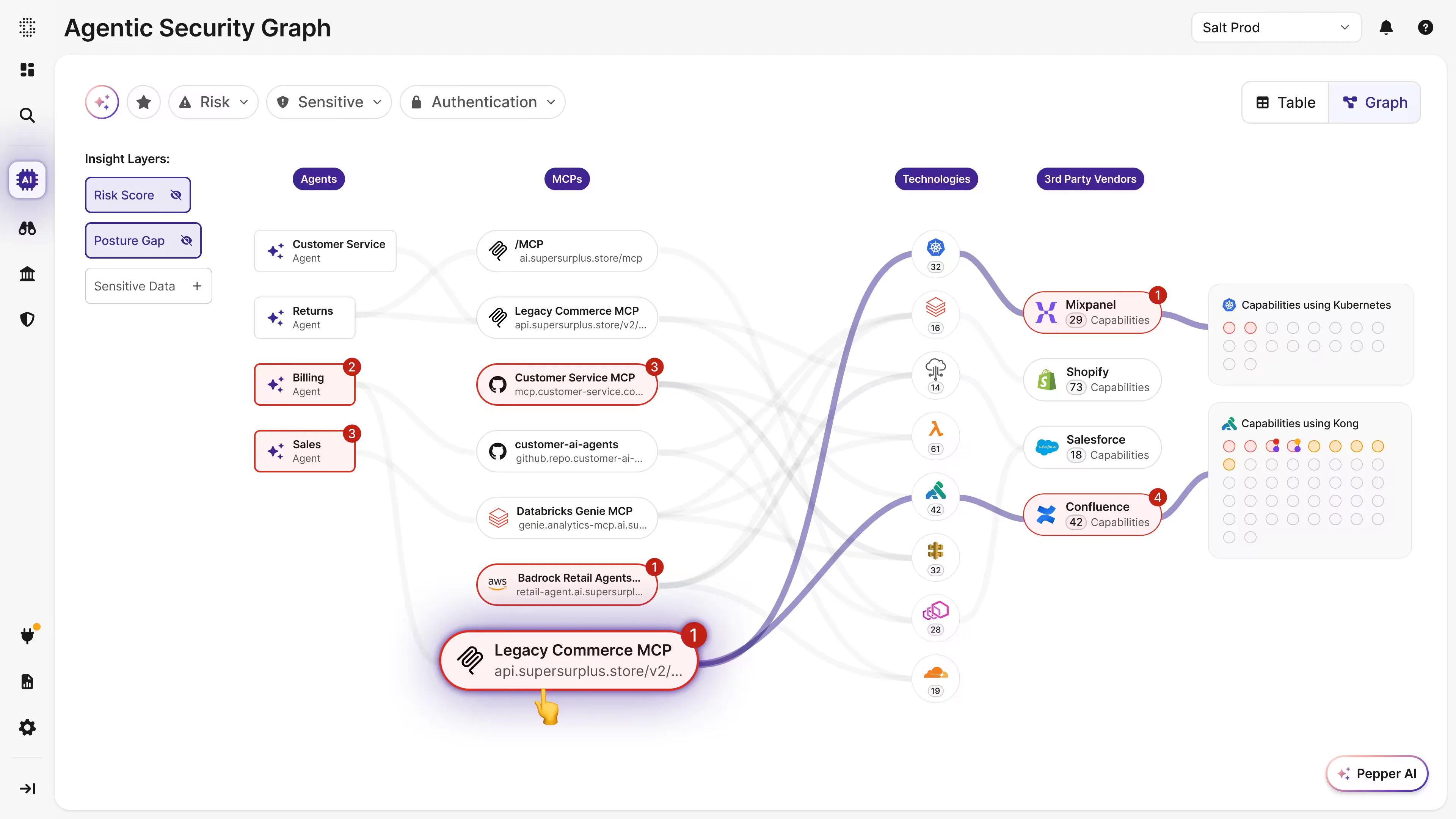
| AI/MCP Security | MCP Protect, Agentic AI Governance, GitHub Connect | No |
| IDE Integration | No | VS Code, JetBrains (19+ IDEs), Eclipse (2M+ downloads) |
| CI/CD Integration | Limited | GitHub Actions, GitLab, Azure Pipelines, Jenkins, Bitbucket, Bamboo, Tekton |
| Compliance Frameworks | PCI DSS, HIPAA, GDPR, SOC 2, NIST, CMMC, FedRAMP | Contract-based compliance enforcement |
| Sensitive Data Tracking | PII, PHI, payment data in API traffic | Data validation via OpenAPI schema checks |
| Deployment Model | Cloud SaaS or on-prem, agentless | SaaS platform + sidecar firewall |
| Gateway Integrations | Kong, Apigee, MuleSoft, NGINX, Istio | Platform-level integration |
| Founded | 2016 | 2016 |
| Backed By | Venture-backed (Palo Alto HQ) | Adara Ventures, Energy Impact Partners ($17M Series A) |
The two platforms detect broken object-level authorization (BOLA — OWASP API1:2023) through opposing traditions. Salt’s behavioral baseline flags BOLA from runtime traffic patterns that deviate from learned per-user norms; 42Crunch’s contract-conformance engine flags BOLA from API requests that violate the OAS-declared authorization model. Same OWASP category, different evidence. The runtime-vs-design-time split is not just architectural — it shows up directly in how each platform reasons about the same OWASP API Top 10 risk.
Salt Security vs 42Crunch: How Do They Compare?
API Discovery
This is Salt Security’s strongest differentiator. Salt discovers APIs through four simultaneous channels: Salt Connect pulls metadata from cloud accounts and gateways like Kong, Apigee, and MuleSoft.
Salt Surface scans your external attack surface from an adversary’s perspective. Traffic analysis identifies undocumented endpoints, including shadow APIs and deprecated-but-still-active zombie APIs.
GitHub Connect scans source code repositories for API endpoints and MCP servers before deployment. According to Salt Security research, roughly 30% of APIs go undiscovered by CDN-based tools alone.
42Crunch added API discovery capabilities, but its core model assumes you already have OpenAPI definitions or are willing to create them.
The API Contract Generator helps by converting Postman Collections and HAR files into OpenAPI specs, which is a practical path for teams with undocumented APIs.
Still, 42Crunch does not perform traffic-based or external surface discovery the way Salt does.
If you suspect your actual API count is larger than what your documentation or gateway shows, Salt’s multi-source discovery approach addresses that gap directly. If your APIs are well-documented and the challenge is making sure those definitions are secure, 42Crunch’s spec-first approach is more relevant.
Design-Time vs Runtime Security
The fundamental philosophical difference between these two platforms comes down to when security gets applied.
42Crunch embeds security into the development process. A developer writes or updates an OpenAPI spec, and the IDE extension immediately runs 300+ checks — scoring the definition from 0 to 100 across security definitions and data validation.
Issues get flagged with quick-fix suggestions before a pull request is opened. In CI/CD, the audit action gates merges based on minimum score thresholds.
The conformance scanner then tests the running API against the spec to verify the implementation matches the contract. This is textbook shift-left: catch problems when they are cheapest to fix.
Salt Security operates after APIs are deployed. It watches live traffic, learns what normal behavior looks like over days and weeks, and then flags deviations that match attacker patterns.
This catches problems that no amount of pre-deployment testing can find — real attackers probing for BOLA vulnerabilities, gradual data scraping campaigns, or credential stuffing across multiple endpoints.
Runtime context reveals threats that static analysis and conformance testing simply cannot predict.
Neither approach replaces the other. 42Crunch prevents insecure APIs from reaching production. Salt Security catches threats that emerge after production deployment.
Attack Detection and Runtime Protection
Salt Security detects attacks through behavioral analysis. Its ML engine baselines normal API traffic patterns and identifies anomalies that indicate attacker intent.
This covers logic-based attacks that WAFs routinely miss: BOLA/IDOR exploitation, slow credential stuffing, systematic data exfiltration, account takeover via session manipulation, and API abuse patterns.
Salt operates out-of-band by analyzing mirrored traffic, so it adds zero latency to the request path.
The tradeoff is that detection is not inline blocking — Salt alerts and provides attack timelines rather than dropping malicious requests in real time.
42Crunch’s micro API firewall takes the opposite approach. It sits inline as a sidecar proxy and enforces the OpenAPI contract on every transaction.
The firewall uses a positive security model — it builds an allowlist from the API definition and blocks anything that falls outside it.
A request with an unexpected parameter, a response with an undeclared field, or a call to an undocumented endpoint all get rejected. This stops injection attacks, schema violations, and data leakage by definition.
The tradeoff is that it only blocks what the OpenAPI spec defines as invalid.
Logic-based attacks that use valid request structures (like BOLA, where the attacker sends a legitimate-looking request with someone else’s object ID) can pass through if the spec does not enforce object-level authorization rules.
Salt is stronger against behavioral and logic-based attacks. 42Crunch is stronger against contract violations and structural attacks.
Developer Experience and Shift-Left Integration
42Crunch has a clear lead in developer tooling. Its IDE extensions — over 2 million downloads across VS Code, JetBrains, and Eclipse — put API security directly in the editor.
Developers see audit scores, severity-tagged issues, and one-click fixes while writing OpenAPI definitions. The freemium tier works without an account, lowering the barrier to adoption.
CI/CD integration covers GitHub Actions, GitLab, Azure Pipelines, Jenkins, Bitbucket, Bamboo, and Tekton with SARIF output for code scanning dashboards.
Salt Security is not a developer tool in the same sense. It is a security platform that connects to cloud infrastructure and analyzes production traffic.
The primary users are security teams, not developers. Salt integrates with SIEM and SOAR platforms (Splunk, CrowdStrike, Microsoft Sentinel) and ticketing tools (Jira, Slack) rather than IDEs and CI pipelines.
GitHub Connect scans repositories for shadow APIs, but the overall workflow is security-team-centric rather than developer-centric.
Teams that want API security embedded in the development process from day one will find 42Crunch’s IDE and CI/CD integrations more immediately useful. Teams that need centralized API visibility and runtime protection across a large environment will find Salt’s security-operations approach more relevant.
Compliance and Posture Management
According to Salt Security, the platform ships with nearly 100 pre-loaded posture rules mapped to PCI DSS, HIPAA, GDPR, SOC 2, NIST, CMMC, and FedRAMP.
The Policy Hub evaluates every discovered API against these rules and surfaces posture gaps grouped by severity. Custom rules can be added, and reports can be exported for auditors.
Salt’s approach to compliance is broad — it covers the API landscape at the organizational level and measures posture across frameworks.
42Crunch approaches compliance through contract enforcement. The audit score reflects how well an API’s OpenAPI definition adheres to security best practices.
The conformance scan verifies that the implementation matches the contract. The firewall enforces the contract at runtime.
If your compliance requirement is “all APIs must have documented, tested, and enforced security controls,” 42Crunch provides verifiable evidence at each stage.
The coverage is narrower than Salt’s framework-by-framework mapping, but deeper at the individual API level.
For broad organizational compliance reporting across multiple frameworks, Salt provides more out-of-the-box coverage. For proving that each individual API meets its documented security contract, 42Crunch’s audit-scan-enforce pipeline generates stronger per-API evidence.
When Should You Choose Salt Security?
Choose Salt Security if:
- API discovery is a primary concern — you need to find shadow, zombie, and undocumented APIs across cloud environments
- Runtime threat detection for logic-based attacks (BOLA, credential stuffing, data exfiltration) is a requirement
- You need compliance posture management mapped to PCI DSS, HIPAA, GDPR, SOC 2, NIST, or FedRAMP
- Your organization is adopting agentic AI and needs visibility into MCP server interactions
- You want agentless deployment that analyzes traffic without adding latency or requiring architecture changes
- The security team (not developers) will be the primary users of the platform
The buyer profile that consistently favors Salt is the runtime-first organization with already-deployed APIs that you cannot easily contract-front. Behavioral-detection-mature SOC teams get more out of Salt than out of contract-first tools because the behavioral baseline picks up logic-based attacks (BOLA, credential stuffing, account takeover) that sit outside any spec definition. Large API estates with limited developer capacity for OpenAPI authoring also tend to land on Salt — when the spec coverage is incomplete or stale, Salt’s traffic-derived inventory still works. The same logic applies to organizations that have weighed the broader peer set against Salt; my Salt Security alternatives page covers that landscape, and the Imperva API Security vs Salt Security comparison covers the WAF-extension axis specifically.
When Should You Choose 42Crunch?
Choose 42Crunch if:
- Your APIs have OpenAPI specifications and you want automated security scoring in the IDE and CI/CD pipeline
- Shift-left API security is the goal — catching issues during design and build, not just at runtime
- You need a runtime firewall that enforces the API contract using a positive security model
- Developer adoption matters — IDE extensions with 2M+ downloads and a free tier lower the barrier
- CI/CD gating based on API security audit scores is part of your pipeline requirements
- You want a single platform that connects spec auditing, conformance testing, and runtime enforcement through the same OpenAPI definition
For many organizations, Salt Security and 42Crunch are complementary rather than competing. 42Crunch secures the API lifecycle from design through deployment.
Salt Security secures the API landscape after deployment with discovery and behavioral threat detection. Running both provides coverage that neither delivers alone.
AppSec Santa maintains detailed reviews of all tools mentioned here. For more options, browse the API security tools category, or read the API security testing guide for a deeper look at how contract-first and runtime testing methodologies compare.
Salt Security vs 42Crunch pricing
Both Salt and 42Crunch use a contact-sales model for the commercial product, but the surrounding free-tier story differs and the cost axes diverge.
Salt Security is sold as a pure-play API Security platform with tiers built around Discovery, Posture, and Protection (plus newer add-ons for MCP Protect and Agentic AI Governance). The salt.security pricing page directs prospects to a contact-sales flow, and Salt has no free tier for the commercial platform — the free entry point is the Salt Surface external attack surface scan, which does not unlock the broader Illuminate platform. Cost scales with API call volume across the monitored estate, the deployment model (cloud SaaS vs hybrid SaaS with on-prem Sensors), and which Illuminate modules are in scope.
42Crunch publishes free IDE extensions for VS Code and IntelliJ that have been adopted by 1.6 million-plus developers, on top of a paid SaaS Platform with an on-prem option for enterprise deployments. The free IDE tier covers OpenAPI auditing inside the developer’s editor, while the commercial product layers conformance scanning, the runtime micro API firewall, and platform-level integrations on top. Cost scales with API count and the number of environments the platform protects.
The cost-axis difference matters when sizing the buy. Salt’s pricing follows traffic volume — higher-volume APIs cost more — while 42Crunch’s pricing follows API count and environment count, which suits organizations with many lower-volume APIs. The free-tier gap (none for Salt, IDE for 42Crunch) also shifts the procurement story: 42Crunch can land bottom-up through individual developers, while Salt usually lands top-down through the security team.
Salt Security vs 42Crunch FAQ
Salt or 42Crunch — which is better for shift-left teams? 42Crunch. The platform’s design-time model is native to a shift-left motion: OpenAPI auditing in the IDE, contract conformance scanning in CI, and runtime contract enforcement through the micro API firewall, all anchored to the same spec. Salt is runtime-only by design, with shift-left coverage available only through integrations rather than as a first-class capability. If the security work has to happen before deployment, 42Crunch is the right pick.
Which is better for runtime API security? Salt. The behavioral runtime model is the entire product, and the platform’s BOLA, credential stuffing, and account takeover detection runs against learned per-user norms with no spec dependency. 42Crunch has runtime functionality through the micro API firewall, but it is contract-conformance enforcement rather than behavioral threat detection — different intent, different evidence model. Pick Salt when the requirement is detecting attacks the spec did not anticipate.
Can I use both together? Yes, and many organizations do. The two platforms cover different lifecycle stages — 42Crunch handles design-time, build-time, and contract enforcement; Salt handles runtime discovery, behavioral detection, and posture governance after deployment. Running both eliminates the gap between “the spec is correct” (42Crunch) and “the actual traffic matches reality” (Salt), and the operational overhead is manageable because the two platforms address different workflows.
Does either cover OWASP API Top 10? Both. Salt covers the full 2023 list through behavioral detection on live traffic; 42Crunch covers the same list through contract conformance and runtime enforcement against the OAS-declared model. The differences live in the detection tradition: Salt’s evidence is traffic-derived behavioral deviations, 42Crunch’s evidence is spec violations. Both tokenize broken object-level authorization (BOLA — OWASP API1:2023) as the canonical #1 risk.
Which is more enterprise-ready? Parallel maturity. Both vendors were founded in 2016, both serve enterprise customers, and both appear in Gartner’s API security coverage. Salt’s enterprise depth shows up in compliance mapping (PCI DSS, HIPAA, GDPR, SOC 2, NIST, CMMC, FedRAMP) and the behavioral-detection breadth. 42Crunch’s enterprise depth shows up in the audit-scan-enforce pipeline and the developer adoption that comes with the free IDE extensions. Different enterprise-readiness profiles, not a clear winner.
Frequently Asked Questions
Is Salt Security or 42Crunch better for API security?
Can I use Salt Security and 42Crunch together?
Which tool is better for API discovery?
Does 42Crunch require OpenAPI specifications?
Which tool handles compliance better?

Founder, AppSec Santa
Years in application security. Reviews and compares 215 AppSec tools across 12 categories to help teams pick the right solution. More about me →
