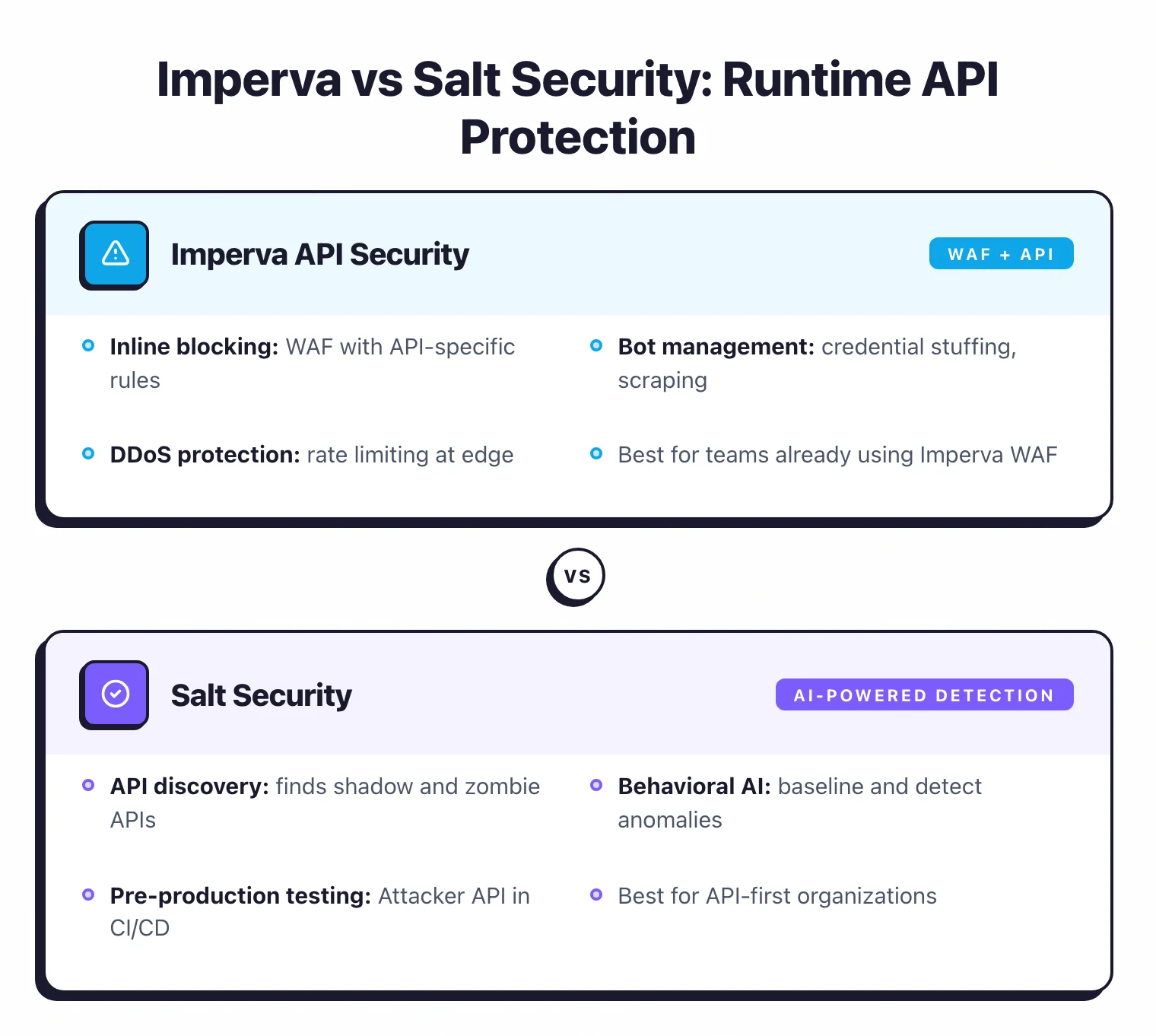
- Both platforms use ML-based behavioral analysis to discover shadow APIs and detect BOLA attacks, but Imperva bundles WAF and bot protection natively while Salt operates as a standalone API security platform.
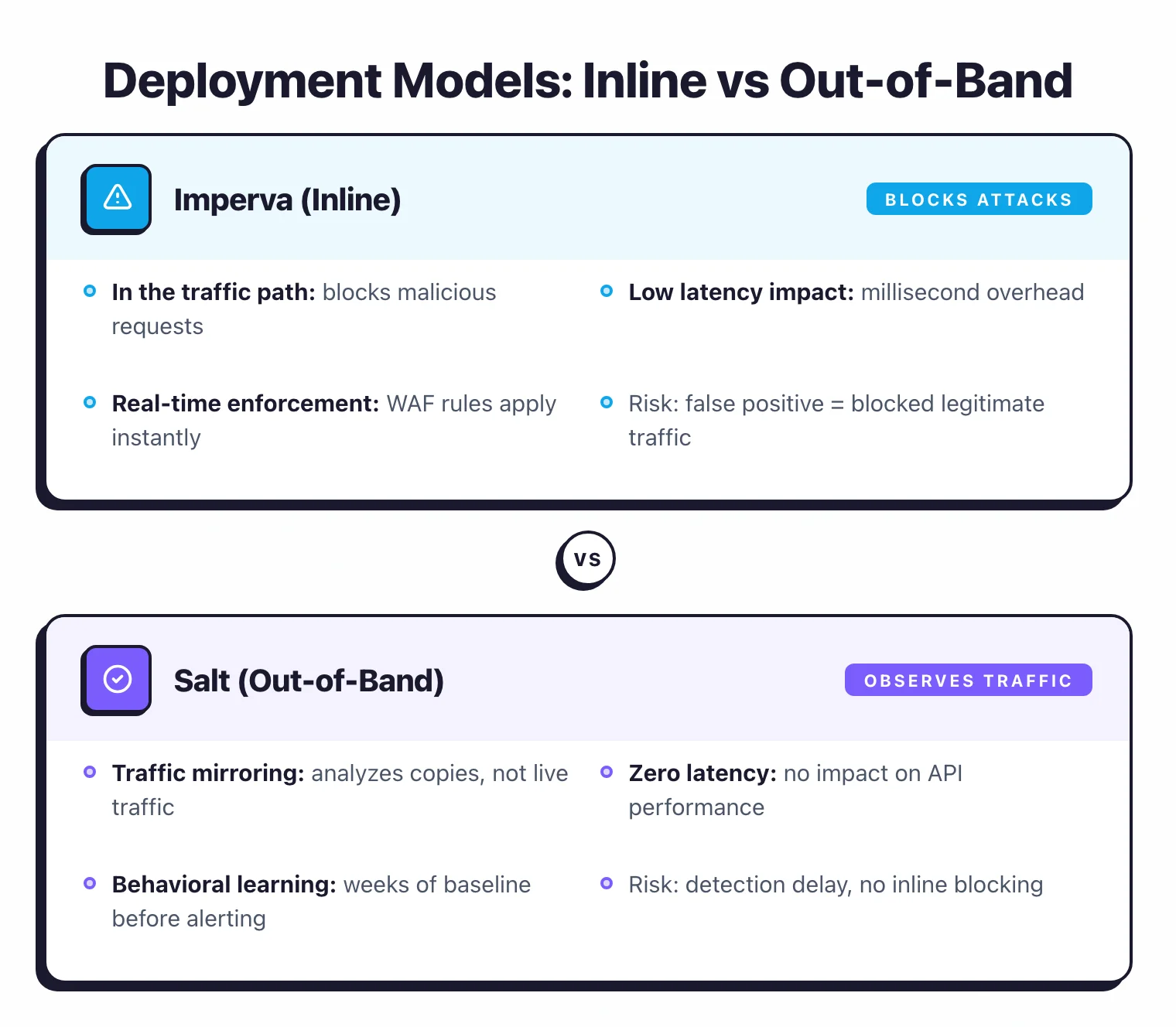
- Salt Security deploys agentlessly via traffic mirroring with zero latency impact; Imperva offers both agent-based (sidecar) and agentless options with inline blocking through its Cloud WAF.
- Salt leads in agentic AI security with MCP Protect, Agentic AI Governance, and GitHub Connect for MCP server discovery; Imperva announced MCP security gateway capabilities for 2026 as part of Thales AI Security Fabric.
- Salt's Policy Hub ships with ~100 pre-loaded posture rules mapping to PCI DSS, HIPAA, GDPR, SOC 2, NIST, and FedRAMP; Imperva focuses posture governance through schema enforcement and WAF policy integration.
- Imperva is backed by Thales Group ($3.6B acquisition) with 5,800+ cybersecurity experts; Salt Security has raised $281M in funding at a $1.4B valuation and reports $75M in annual revenue.
Which Is Better: Imperva API Security or Salt Security?
Imperva API Security is the better choice for organizations that want unified application security with inline blocking under one vendor, while Salt Security is better for teams that need dedicated API security with deep discovery, compliance mapping, and production-ready agentic AI protection.
Imperva API Security bundles API security with WAF, bot protection, and DDoS mitigation. Salt Security is a standalone API security platform with broader API discovery and leading MCP/AI agent security capabilities.
Imperva API Security takes a unified platform approach. It combines ML-powered API discovery, schema enforcement, runtime BOLA detection, and automated threat mitigation, all connected to Imperva’s Cloud WAF, Advanced Bot Protection, and DDoS mitigation. Thales acquired Imperva for $3.6 billion in December 2023, backing the platform with 5,800+ security professionals across 68 countries.
Salt Security focuses exclusively on API security through the Salt Illuminate platform. Unlike Imperva, Salt discovers shadow and zombie APIs through four distinct methods: cloud connectors, external surface scanning, live traffic analysis, and GitHub repository scanning. Salt uses behavioral ML to detect logic-based attacks like BOLA, credential stuffing, and data exfiltration.
Salt has raised $281M in total funding at a $1.4 billion valuation and leads the market in agentic AI security with production-ready MCP Protect, Agentic AI Governance, and Ask Pepper AI capabilities. Salt is also recognized as a KuppingerCole Overall Leader in API Security and Management (2025).
If you need a consolidated application security stack with WAF, bot protection, and API security under one vendor, Imperva is the stronger choice. If you need a dedicated API security platform with deep discovery, compliance mapping, and agentic AI protection capabilities, Salt Security is the stronger choice.
What Are the Key Differences?
| Feature | Imperva API Security | Salt Security |
|---|---|---|
| Vendor | Thales Group (acquired Imperva Dec 2023) | Salt Security (independent, founded 2016) |
| Total Funding / Backing | $3.6B acquisition by Thales | $281M raised, $1.4B valuation |
| Platform Scope | API security + WAF + bot protection + DDoS | Dedicated API security platform |
| API Discovery | ML-based traffic analysis (agent/agentless) | Cloud connectors + surface scanning + traffic analysis + GitHub scanning |
| BOLA Detection | Yes, with inline blocking via Cloud WAF | Yes, behavioral ML with out-of-band detection |
| Schema Enforcement | Built-in schema validation and runtime enforcement | Posture rules check for misconfigurations and overexposure |
| Bot Protection | Integrated Advanced Bot Protection | No native bot protection |
| Compliance Mapping | Via WAF policies and schema enforcement | ~100 pre-loaded rules (PCI DSS, HIPAA, GDPR, SOC 2, NIST, CMMC, FedRAMP) |
| AI Agent / MCP Security | MCP security gateway planned for mid-2026 | MCP Protect, Agentic AI Governance, GitHub Connect, AG-SPM/AG-DR (March 2026) |
| Conversational AI Assistant | Not announced | Ask Pepper AI (natural language investigation) |
| Deployment Model | Cloud-managed, self-managed, agent-based, agentless | Cloud SaaS, hybrid (on-prem Hybrid Server), agentless |
| Inline Blocking | Yes (via Cloud WAF integration) | No (out-of-band via traffic mirroring) |
| Request Latency Impact | Minimal (inline inspection) | Zero (out-of-band) |
| Kubernetes Support | Sidecar sniffer for containerized environments | Container and Kubernetes deployment supported |
| API Gateway Integrations | Kong, MuleSoft, Azure APIM, Apigee, Imperva WAF Gateway | Kong, Apigee, MuleSoft, NGINX, Istio, F5 |
| SIEM/SOAR Integration | Splunk, Datadog, and others | Splunk, CrowdStrike, Microsoft Sentinel, Jira, Slack |
| Sensitive Data Tracking | PII and payment data classification | PII, PHI, payment data, custom patterns |
Both platforms detect broken object-level authorization (BOLA — OWASP API1:2023), the canonical #1 risk on the OWASP API Top 10. Imperva’s ML engine flags BOLA against WAF traffic patterns and the API Detection and Response (ADR) module’s behavioral baselines per endpoint; Salt’s behavioral baseline flags BOLA against learned per-user access norms across a longer training window. Different traditions, similar OWASP API Top 10 coverage — the gap shows up in detection latency and false-positive rates rather than category coverage. Salt’s behavioral models typically need 30 days of representative traffic before BOLA detection stabilizes; Imperva’s ADR ramps faster because it inherits anomaly signals from the underlying WAF.
Imperva API Security vs Salt Security: How Do They Compare?
Platform Philosophy
Imperva and Salt Security represent two fundamentally different approaches to API security: platform consolidation versus dedicated specialization. Imperva bundles API security into a broader application security stack, while Salt treats API security as a standalone discipline.
Imperva’s pitch is reducing tool sprawl. Instead of deploying separate products for WAF, bot protection, DDoS mitigation, and API security, you get all of these under one platform with shared threat intelligence.
When Imperva’s API security engine detects a BOLA attack, it can trigger blocking rules in the Cloud WAF immediately, no integration plumbing required. This tight coupling between detection and enforcement is Imperva’s core differentiator.
Salt Security’s pitch is API security depth. By focusing exclusively on APIs, Salt has built specialized capabilities that broader platforms have not matched, particularly in API discovery breadth, posture governance, and agentic AI security. Salt treats API security as a distinct discipline that requires purpose-built tooling rather than an extension of WAF or perimeter defense.
The trade-off is real. Imperva customers get a simpler vendor relationship and tighter integration across the security stack. Salt customers get deeper API-specific functionality at the cost of deploying and managing a separate platform alongside their existing WAF and bot protection tools.
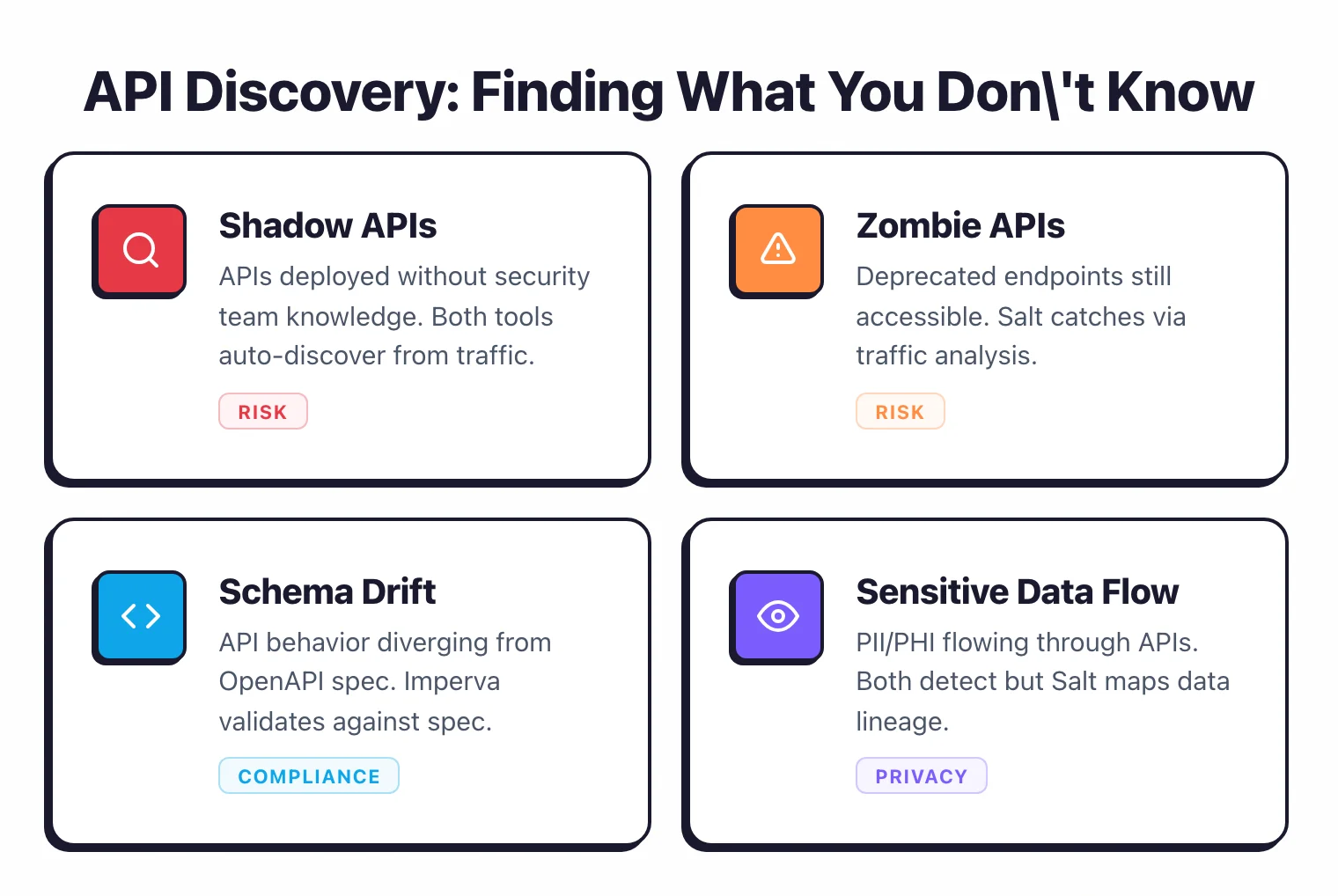
API Discovery
Both platforms discover shadow, zombie, and undocumented APIs using ML-based traffic analysis, but Salt uses four discovery channels compared to Imperva’s two.
Imperva discovers APIs through agent-based and agentless monitoring. The agent-based approach uses a lightweight sidecar in Kubernetes environments for deep application-level visibility.
The agentless approach monitors network-layer traffic. Both methods feed discovered APIs into a centralized inventory with risk classification and sensitive data tagging.
Salt Security combines four discovery channels into one platform. Salt Connect pulls API metadata from cloud environments (AWS, Azure, GCP) and API gateways (Kong, Apigee, MuleSoft).
Salt Surface scans the external attack surface from an adversary’s perspective. Live traffic analysis identifies undocumented endpoints in real time. GitHub Connect (launched November 2025) scans source code repositories to find shadow APIs and MCP servers before they reach production.
Salt’s multi-channel approach gives it broader discovery coverage, especially for organizations with APIs scattered across multiple cloud accounts, gateways, and code repositories. Imperva’s discovery is effective but relies primarily on traffic analysis rather than combining it with external scanning and code-level discovery.
Threat Detection and Response
Both platforms detect BOLA attacks and other behavioral threats using ML-based traffic analysis. The key difference is the response model: Imperva blocks inline with zero delay, while Salt detects out-of-band with zero latency impact.
Imperva operates inline through its Cloud WAF. When the API security engine identifies a BOLA attempt or other malicious API traffic, it can block the request in real time before it reaches the backend service.
This inline enforcement extends to schema validation: malformed requests that violate the API’s OpenAPI definition are rejected at the edge. The system combines behavioral and rule-based engines, with anomalies scored and endpoints flagged for immediate action.
Salt Security operates out-of-band via traffic mirroring. It analyzes API traffic without sitting in the request path, which means zero added latency. Salt baselines normal API behavior over days and weeks, then flags deviations that match attacker patterns: slow credential stuffing, gradual data scraping, BOLA exploitation, and account takeover attempts.
Because Salt does not sit inline, it cannot natively block malicious requests. Instead, it sends alerts and integrates with WAFs and API gateways for enforcement.
For organizations that need immediate automated blocking, Imperva’s inline model is the stronger choice. For organizations that prioritize zero-latency monitoring and are comfortable routing blocking through existing WAF or gateway infrastructure, Salt’s out-of-band approach works well.
Compliance and Posture Governance
Salt Security has a clear advantage over Imperva in structured compliance mapping. The Policy Hub ships with nearly 100 pre-loaded posture rules organized by compliance framework: PCI DSS, HIPAA, GDPR, SOC 2, NIST, CMMC, and FedRAMP.
Each rule triggers a posture gap when violated, grouped by severity (Critical, High, Medium). Teams can create custom posture rules and export reports for auditors directly from the dashboard.
Imperva approaches posture governance through schema enforcement and WAF policy integration. It checks API definitions for missing authentication parameters, weak validation rules, and security anti-patterns.
Runtime enforcement applies schema protection to block malformed requests. This is effective for ensuring APIs conform to their specifications, but it does not provide the same breadth of framework-mapped compliance rules that Salt offers.
If compliance mapping across multiple regulatory frameworks is a priority, especially for organizations in financial services, healthcare, or government, Salt’s Policy Hub provides more structured, auditor-ready output. If your compliance needs center on API contract enforcement and WAF policy adherence, Imperva’s schema-driven approach covers the basics.
Agentic AI and MCP Security
Salt Security has moved ahead of both Imperva and the broader market here. Throughout 2025 and into 2026, Salt released a series of agentic AI security features that no other API security vendor has matched:
- MCP Protect discovers and monitors all Model Context Protocol (MCP) server interactions with AI agents in runtime, maps hidden API connections, and assesses data exposure risk.
- Agentic AI Governance ships with out-of-the-box security controls that enforce safe AI agent behavior in MCP and Agent-to-Agent (A2A) environments.
- GitHub Connect identifies risky MCP servers in source code repositories before they deploy to production.
- Agentic Security Platform (launched March 2026) adds Agentic Security Posture Management (AG-SPM) and Agentic Detection and Response (AG-DR) for continuous governance and real-time abuse detection across LLMs, MCP servers, and APIs.
Imperva, through Thales, has announced its own agentic AI security direction. The Thales AI Security Fabric (announced in late 2025) includes Imperva AI Application Security with plans for an MCP security gateway, data leakage prevention, and runtime access control. These capabilities are expected to become generally available in mid-2026.
For organizations already deploying AI agents and MCP servers, Salt has production-ready tooling today. Imperva’s roadmap signals competitive capabilities, but they are not yet generally available.
Deployment and Architecture
Both platforms support cloud and on-premises deployment, but their architectures differ in important ways. Imperva offers more deployment models, while Salt’s agentless approach is simpler to deploy with zero latency impact.
Imperva offers three deployment models: cloud-managed through the Imperva Cloud WAF console, self-managed via a local management console (API Security Anywhere), and hybrid configurations combining both. Within each model, teams choose between agent-based deployment (lightweight Kubernetes sidecars for application-level visibility) or agentless monitoring at the network layer. The self-managed option launched in 2024 for organizations that cannot send API traffic to an external cloud.
Salt Security deploys agentlessly by default. It connects to cloud environments, API gateways, and traffic sources through mirroring, with no inline components required.
For organizations that need on-premises data processing, the Hybrid Server handles API traffic locally, keeping sensitive data within the customer’s environment and transmitting only aggregated metadata and malicious events to the Salt cloud. Salt claims the Hybrid Server supports up to 9 billion API calls monthly.
Salt Illuminate, launched in June 2025, also introduced self-service onboarding that reduces deployment time from months to minutes. Connect your cloud accounts and the platform begins mapping APIs within minutes.
Imperva’s deployment options are broader. The agent-based option gives deeper application-level visibility that agentless monitoring cannot match. Salt’s agentless-first approach is simpler to deploy and maintains zero latency, but it sacrifices the depth of inline inspection.
Ecosystem and Integration
Imperva’s biggest integration advantage is internal. Because API security is part of the broader Imperva platform, it shares threat intelligence with Imperva WAF, Bot Protection, RASP, and DDoS mitigation natively.
Security events from one product inform protection in another without requiring external integrations. The platform also integrates with Kong, MuleSoft, Azure APIM, Apigee, Splunk, and Datadog.
Salt Security integrates with a broader set of external platforms. On the gateway side: Kong, Apigee, MuleSoft, NGINX, Istio, Akamai, Cloudflare, and F5. On the cloud side: AWS, Azure, GCP, and Kubernetes.
On the SIEM/SOAR side: Splunk, CrowdStrike, Microsoft Sentinel, Jira, and Slack. Salt also integrates with GitHub for code-level API and MCP server discovery.
If you are already an Imperva or Thales customer, the internal integration story is strong: one vendor, shared intelligence, unified console. If you run a mixed security stack and need flexibility in how your API security platform connects to existing tools, Salt’s broader integration catalog gives you more options.
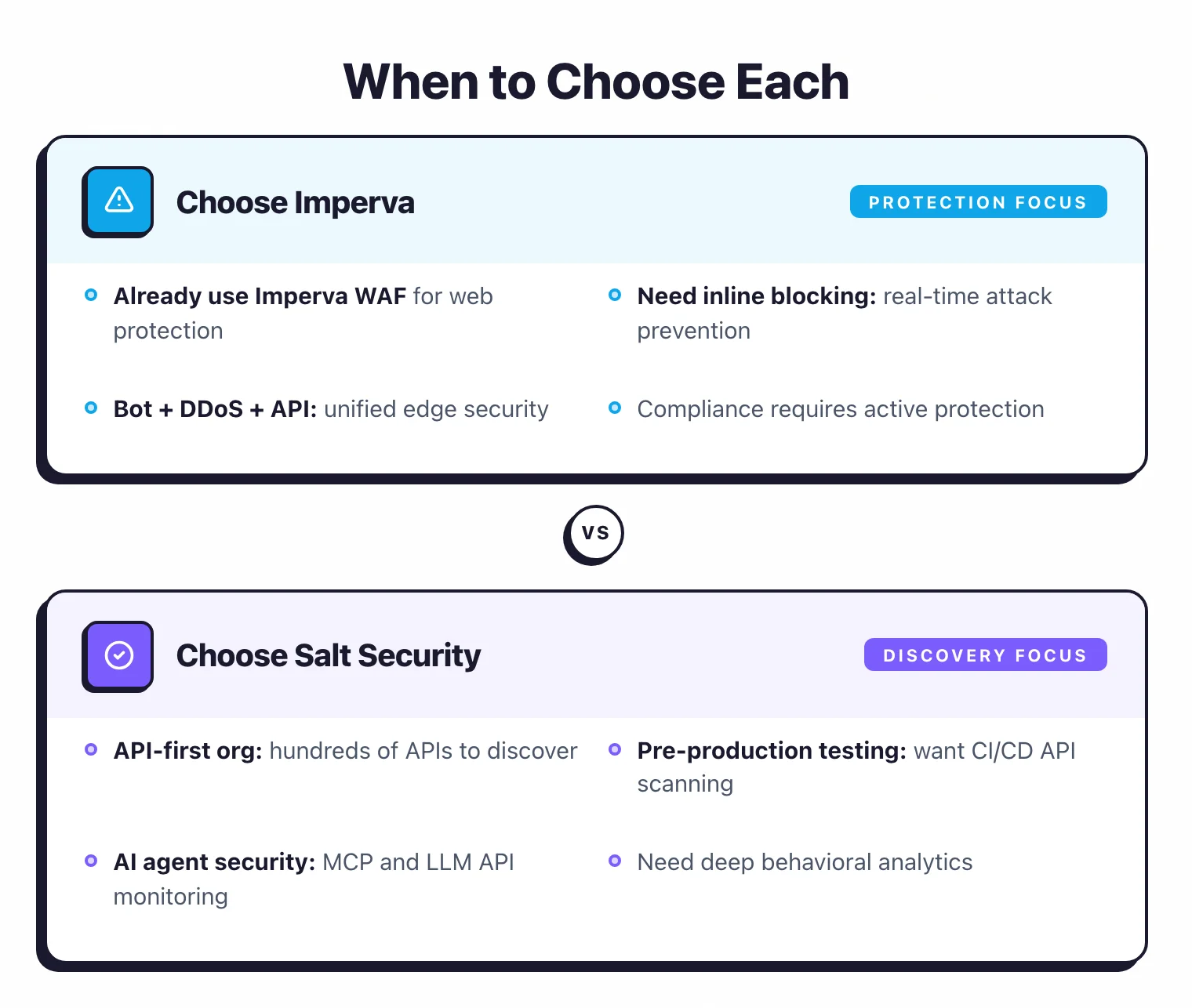
When Should You Choose Imperva API Security?
Choose Imperva API Security if:
- You want a consolidated application security platform with WAF, bot protection, DDoS, and API security under one vendor
- Inline blocking of malicious API traffic is a requirement, not just detection and alerting
- You are already an Imperva or Thales customer and want shared threat intelligence across products
- Your organization needs a vendor backed by a large, established cybersecurity company with global presence
- Schema enforcement and runtime API contract validation are central to your API security strategy
- You prefer agent-based deployment options for deep application-level visibility in Kubernetes environments
The procurement signal that consistently favors Imperva is an existing Imperva WAF, RASP, or bot protection footprint. The API Security module attaches to the Cloud Application Security platform under the same enterprise agreement, which lowers the incremental cost compared to adding a standalone API security vendor and removes the integration overhead of correlating signals across two unrelated products. Following the December 2023 Thales acquisition, Imperva sits inside Thales’s broader cybersecurity portfolio with 5,800+ security professionals across 68 countries, which adds weight to RFPs in regulated industries — particularly financial services, government, and healthcare — where vendor stability and global support presence are part of the selection criteria. The flip side of that integration story is that Imperva expects most deployments to run alongside the Imperva WAF or another Imperva enforcement plane, so teams without the existing footprint usually weigh Salt or another pure-play before committing.
When Should You Choose Salt Security?
Choose Salt Security if:
- API security is a standalone priority that needs dedicated tooling rather than an add-on to a WAF platform
- You need the broadest API discovery coverage, combining cloud connectors, external surface scanning, traffic analysis, and code repository scanning
- Compliance mapping against PCI DSS, HIPAA, GDPR, SOC 2, NIST, or FedRAMP is a requirement, with auditor-ready reporting
- You are deploying AI agents and MCP servers and need production-ready security tooling for agentic AI workflows today
- Zero-latency, agentless deployment is important, with no inline components in the request path
- You want a conversational AI assistant (Ask Pepper AI) for natural-language investigation of API security posture
For organizations that want both broad platform coverage and deep API-specific capabilities, running Imperva for WAF and bot protection alongside Salt for dedicated API security is a viable architecture — though it adds vendor complexity and cost. Salt’s agentless, out-of-band deployment makes it straightforward to layer alongside an existing Imperva WAF without architectural conflicts. Buyers comparing Salt against more than one vendor should also look at the Salt Security vs 42Crunch comparison for the contract-first axis, and the Salt Security alternatives page for the broader peer set.
For the full list of API protection options, see the API security tools comparison on AppSec Santa.
Imperva API Security vs Salt Security pricing
Both Imperva and Salt use a contact-sales model rather than publishing a public rate card, so any quote depends on the API estate, deployment topology, and module mix.
Imperva API Security is typically procured as part of the Cloud Application Security suite, alongside Imperva Cloud WAF, Advanced Bot Protection, RASP, and DDoS. Existing Imperva customers see the API Security module attach to the existing contract rather than land as a new platform line item, which usually lowers the incremental cost. Greenfield buyers procure the full Cloud Application Security bundle, with cost driven by API call volume, the number of monitored entry points, and which adjacent modules (WAF, Bot, RASP) are included. Following the December 2023 Thales acquisition, the procurement motion still runs through Imperva’s enterprise sales organization rather than a Thales-branded rate card.
Salt Security is sold as a pure-play API Security platform with tiers organized around Discovery, Posture, and Protection (plus newer add-ons for MCP Protect and Agentic AI Governance). The salt.security pricing page directs prospects to a contact-sales flow, with cost driven by API call volume across the monitored estate, the deployment model (cloud SaaS vs hybrid SaaS with on-prem Sensors), and which Illuminate modules are in scope. A free external attack surface scan is available through Salt Surface as a no-commit entry point ahead of the formal procurement cycle.
The procurement difference matters more than the absolute numbers. Imperva’s pricing inherits the broader enterprise platform context — easier to add to an existing master agreement, harder to evaluate in isolation. Salt’s pricing is API-focused — easier to scope when the buyer needs to defend a standalone budget line, harder to consolidate across other security purchases. Both vendors run 30–60 day procurement cycles for new buyers.
Imperva API vs Salt Security FAQ
Did Thales’ acquisition of Imperva change the API Security product? Operationally, no. Thales acquired Imperva in December 2023 for $3.6 billion, and the Imperva brand and product line have continued under Thales’s cybersecurity division. The API Security module receives ongoing development, the existing customers kept their contracts, and the procurement motion still runs through Imperva’s enterprise sales team rather than a Thales-branded route. The acquisition expanded the combined cybersecurity portfolio to 5,800+ security professionals across 68 countries, which mostly shows up in RFP weight rather than day-to-day product changes.
Is Salt purely API-focused or part of a broader platform? Pure-play API. Salt does not bundle a WAF, DDoS, or bot management product alongside the API security platform. The Illuminate engine focuses on API discovery, posture governance, behavioral threat detection, and AI-agent and MCP security. Most Salt customers run an existing WAF (often Imperva, Cloudflare, or Akamai) alongside Salt for the inline enforcement that Salt’s detection-only model does not provide.
Which has better OWASP API Top 10 coverage? Both cover all 10 risk categories from the OWASP API Security Top 10 (2023 edition) through runtime detection. The differences live in the underlying tradition: Imperva’s coverage inherits ML signals from the WAF traffic stream and the API Detection and Response module’s per-endpoint baselines; Salt’s coverage runs against a longer learned per-user behavioral baseline that needs around 30 days of representative traffic to stabilize. Both detect BOLA, broken authentication, excessive data exposure, and the rest, but Imperva’s depth is stronger on schema enforcement and Salt’s depth is stronger on logic-based BOLA detection across long traffic windows.
Can I run Imperva API Security without the WAF? Most deployments include the WAF. Imperva’s commercial model and platform integration assume the API Security module sits alongside the Imperva Cloud WAF or another Imperva enforcement plane, and full functionality (inline blocking, shared threat intelligence, bot integration) depends on that broader stack. Self-managed deployments without the WAF are technically possible but uncommon and usually push buyers toward a pure-play vendor like Salt.
How do migration costs compare between the two? Migrating from Imperva API Security to Salt typically means standing up Salt’s agentless deployment alongside the existing Imperva stack, validating the discovery and behavioral baselines for 30 days, then either decommissioning the Imperva API Security module (keeping Imperva WAF) or splitting traffic between the two during a transition window. Migrating from Salt to Imperva is more involved if Imperva’s WAF is not already in place, since Imperva expects the API Security module to sit alongside it. Most organizations that switch end up running both for at least one renewal cycle to avoid coverage gaps.
Frequently Asked Questions
What is the main difference between Imperva API Security and Salt Security?
Which is better for API discovery: Imperva or Salt Security?
Can Imperva API Security and Salt Security detect BOLA attacks?
Which platform is better for securing AI agents and MCP servers?
Do Imperva API Security and Salt Security support on-premises deployment?
Which tool has better compliance mapping for API security?

Founder, AppSec Santa
Years in application security. Reviews and compares 215 AppSec tools across 12 categories to help teams pick the right solution. More about me →
